Chinese APT Gelsemium Deploys ‘Wolfsbane’ Linux Variant
In a sign of the times, a backdoor malware whose ancestors date back to 2005 has morphed to target Linux systems.
darkreading – Read More
In a sign of the times, a backdoor malware whose ancestors date back to 2005 has morphed to target Linux systems.
darkreading – Read More
Federal prosecutors in Los Angeles this week unsealed criminal charges against five men alleged to be members of a hacking group responsible for dozens of cyber intrusions at major U.S. technology companies between 2021 and 2023, including LastPass, MailChimp, Okta, T-Mobile and Twilio.
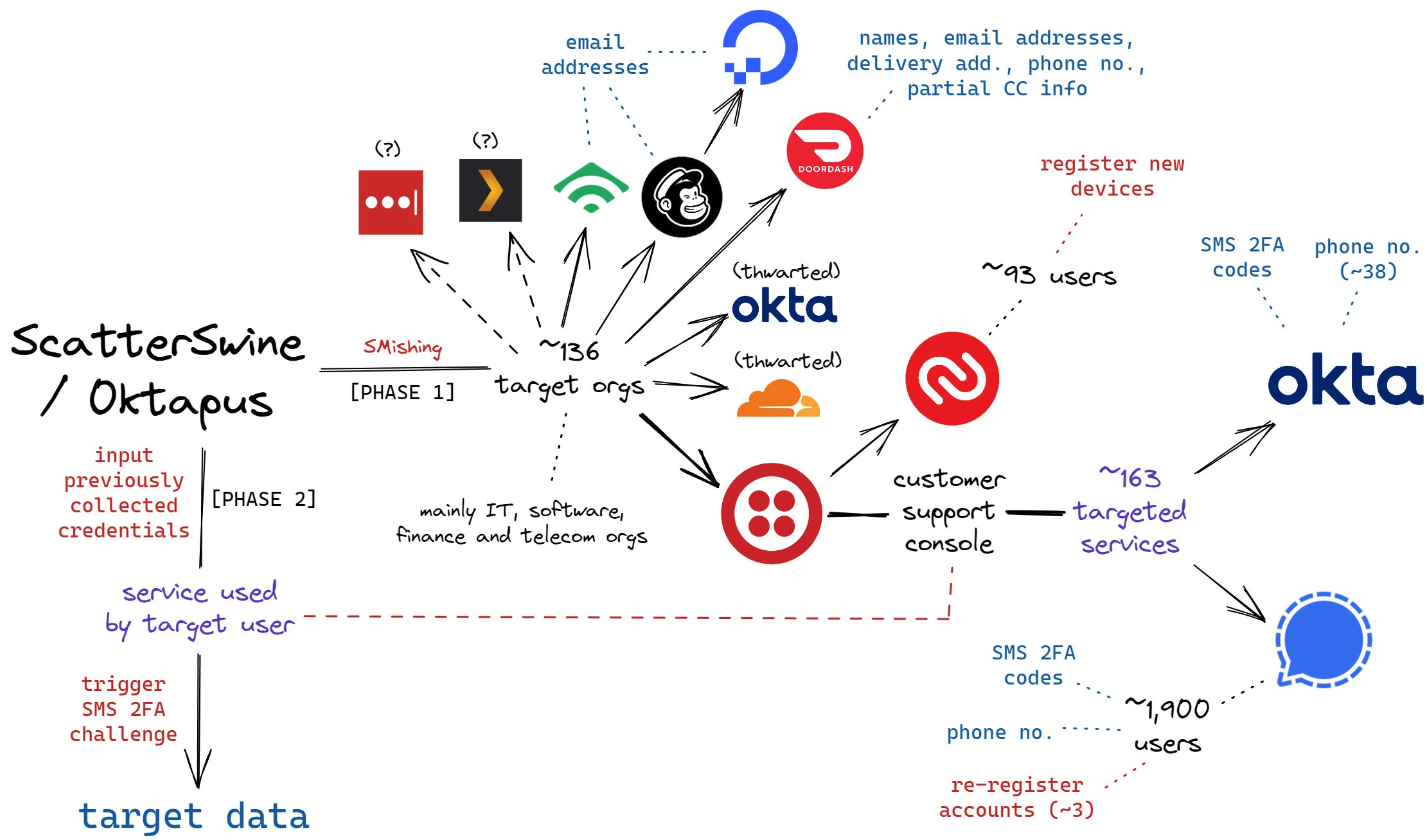
A visual depiction of the attacks by the SMS phishing group known as Scattered Spider, and Oktapus. Image: Amitai Cohen twitter.com/amitaico.
The five men, aged 20 to 25, are allegedly members of a hacking conspiracy dubbed “Scattered Spider” and “Oktapus,” which specialized in SMS-based phishing attacks that tricked employees at tech firms into entering their credentials and one-time passcodes at phishing websites.
The targeted SMS scams asked employees to click a link and log in at a website that mimicked their employer’s Okta authentication page. Some SMS phishing messages told employees their VPN credentials were expiring and needed to be changed; other phishing messages advised employees about changes to their upcoming work schedule.
These attacks leveraged newly-registered domains that often included the name of the targeted company, such as twilio-help[.]com and ouryahoo-okta[.]com. The phishing websites were normally kept online for just one or two hours at a time, meaning they were often yanked offline before they could be flagged by anti-phishing and security services.
The phishing kits used for these campaigns featured a hidden Telegram instant message bot that forwarded any submitted credentials in real-time. The bot allowed the attackers to use the phished username, password and one-time code to log in as that employee at the real employer website.
In August 2022, multiple security firms gained access to the server that was receiving data from that Telegram bot, which on several occasions leaked the Telegram ID and handle of its developer, who used the nickname “Joeleoli.”
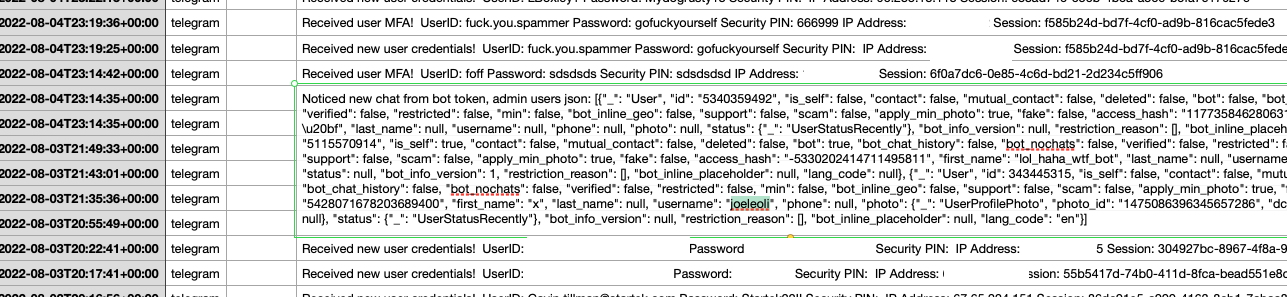
The Telegram username “Joeleoli” can be seen sandwiched between data submitted by people who knew it was a phish, and data phished from actual victims. Click to enlarge.
That Joeleoli moniker registered on the cybercrime forum OGusers in 2018 with the email address joelebruh@gmail.com, which also was used to register accounts at several websites for a Joel Evans from North Carolina. Indeed, prosecutors say Joeleoli’s real name is Joel Martin Evans, and he is a 25-year-old from Jacksonville, North Carolina.
One of Scattered Spider’s first big victims in its 2022 SMS phishing spree was Twilio, a company that provides services for making and receiving text messages and phone calls. The group then used their access to Twilio to attack at least 163 of its customers. According to prosecutors, the group mainly sought to steal cryptocurrency from victim companies and their employees.
“The defendants allegedly preyed on unsuspecting victims in this phishing scheme and used their personal information as a gateway to steal millions in their cryptocurrency accounts,” said Akil Davis, the assistant director in charge of the FBI’s Los Angeles field office.
Many of the hacking group’s phishing domains were registered through the registrar NameCheap, and FBI investigators said records obtained from NameCheap showed the person who managed those phishing websites did so from an Internet address in Scotland. The feds then obtained records from Virgin Media, which showed the address was leased for several months to Tyler Buchanan, a 22-year-old from Dundee, Scotland.
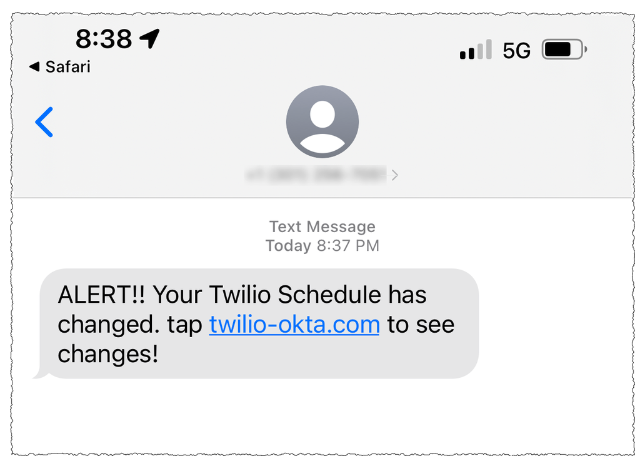
A Scattered Spider phishing lure sent to Twilio employees.
As first reported here in June, Buchanan was arrested in Spain as he tried to board a flight bound for Italy. The Spanish police told local media that Buchanan, who allegedly went by the alias “Tylerb,” at one time possessed Bitcoins worth $27 million.
The government says much of Tylerb’s cryptocurrency wealth was the result of successful SIM-swapping attacks, wherein crooks transfer the target’s phone number to a device they control and intercept any text messages or phone calls sent to the victim — including one-time passcodes for authentication, or password reset links sent via SMS.
According to several SIM-swapping channels on Telegram where Tylerb was known to frequent, rival SIM-swappers hired thugs to invade his home in February 2023. Those accounts state that the intruders assaulted Tylerb’s mother in the home invasion, and that they threatened to burn him with a blowtorch if he didn’t give up the keys to his cryptocurrency wallets. Tylerb was reputed to have fled the United Kingdom after that assault.

A still frame from a video released by the Spanish national police, showing Tyler Buchanan being taken into custody at the airport.
Prosecutors allege Tylerb worked closely on SIM-swapping attacks with Noah Michael Urban, another alleged Scattered Spider member from Palm Coast, Fla. who went by the handles “Sosa,” “Elijah,” and “Kingbob.”
Sosa was known to be a top member of the broader cybercriminal community online known as “The Com,” wherein hackers boast loudly about high-profile exploits and hacks that almost invariably begin with social engineering — tricking people over the phone, email or SMS into giving away credentials that allow remote access to corporate networks.
In January 2024, KrebsOnSecurity broke the news that Urban had been arrested in Florida in connection with multiple SIM-swapping attacks. That story noted that Sosa’s alter ego Kingbob routinely targeted people in the recording industry to steal and share “grails,” a slang term used to describe unreleased music recordings from popular artists.
FBI investigators identified a fourth alleged member of the conspiracy – Ahmed Hossam Eldin Elbadawy, 23, of College Station, Texas — after he used a portion of cryptocurrency funds stolen from a victim company to pay for an account used to register phishing domains.
The indictment unsealed Wednesday alleges Elbadawy controlled a number of cryptocurrency accounts used to receive stolen funds, along with another Texas man — Evans Onyeaka Osiebo, 20, of Dallas.
Members of Scattered Spider are reputed to have been involved in a September 2023 ransomware attack against the MGM Resorts hotel chain that quickly brought multiple MGM casinos to a standstill. In September 2024, KrebsOnSecurity reported that a 17-year-old from the United Kingdom was arrested last year by U.K. police as part of an FBI investigation into the MGM hack.
Evans, Elbadawy, Osiebo and Urban were all charged with one count of conspiracy to commit wire fraud, one count of conspiracy, and one count of aggravated identity theft. Buchanan, who is named as an indicted co-conspirator, was charged with conspiracy to commit wire fraud, conspiracy, wire fraud, and aggravated identity theft.
A Justice Department press release states that if convicted, each defendant would face a statutory maximum sentence of 20 years in federal prison for conspiracy to commit wire fraud, up to five years in federal prison for the conspiracy count, and a mandatory two-year consecutive prison sentence for aggravated identity theft. Buchanan would face up to 20 years in prison for the wire fraud count as well.
Further reading:
The redacted complaint against Buchanan (PDF)
Charges against Urban and the other defendants (PDF).
Krebs on Security – Read More
The DOJ proposes tough proposals in its antitrust lawsuit against Google, including selling the Chrome browser, limiting search…
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More
Threat actors exploited two vulnerabilities in Intel-based machines. Google’s Threat Analysis Group discovered the flaws.
Security | TechRepublic – Read More
Law enforcement agencies seized the notorious PopeyeTools cybercrime platform and accused three people of running it.
The Record from Recorded Future News – Read More
Four of the arrested individuals of the cybercriminal gang, known for hacking MGM and Caesars, are American, all of whom could face up to 27 years in prison for the charges against them.
darkreading – Read More

Welcome to this week’s edition of the Threat Source newsletter.
Bidirectional communication is foundational to a well-built team regardless of environment. It’s critical in information security to be able to drive a conversation up the ladder and down and not lose the critical elements. One of the most difficult challenges that cyber security teams face is making sure that everyone that is in a decision-making space is aware of the highly technical challenges that the evolving threat landscape dictates. Navigating the challenges that come in continually evolving the team and it’s tools to defend is often a much greater challenge. I’m going to help you with those conversations. In both directions. By talking about drumming. I know, I don’t have the pro wrestling takes that Jon came to the table with, so you’re going to have to run with me Constant Reader.
I’m going to choose drumming to outline an easy way to identify some complex issues and talk about them in both directions and drumming is a little easier to identify for non-musicians and FAR less contentious than a spicy guitar opinion. Ok, so let’s start with a simple concept.
Sounds difficult. Is difficult.
Sounds difficult. Is easy.
Sounds easy. Is difficult.
Sounds easy. Is easy.
Sounds difficult. Is difficult. This one is easy – Tomas Haake from Meshuggah playing Bleed is a perfect example. Polyrhythms, stamina, speed, interdependence, and complexity. This sounds difficult. It is difficult. Only the criminally insane attempt to learn how to play this song.
Sounds easy. Is easy. Take Phil Rudd and pick any AC/DC song from Back in Black. The perfect example of sounds easy, is easy. Perfectly in the pocket.
Sounds easy. Is difficult. This one is harder and will cause someone to wellackshully and I assure you I do not care. I’m going to give two examples, Jeff Porcaro of Toto playing Rosanna and Vinnie Colaiuta playing Seven Days with Sting. Both of these songs are immensely easy to listen to and don’t seem like there’s anything challenging going on. Until you try to play along, then you cry and examine all the choices you’ve made in life.
Sounds difficult. Is easy. This is going to be a sticky situation, but I’d say that you could throw on anything by Travis Barker and Dave Lombardo. Bring it haters. I’m not saying that they are bad drummers – simply that what they do sounds more difficult than it is.
Ok William, but how does this help me at all?
When you have information security meetings with people in your organization take a second as you look at the agenda, and your conversation in specific, and think about the groupings above and determine what kind of drumming you are hearing. Depending on your environment and team the topics will fall naturally into these categories – it can be patch and vulnerability management, EOL devices that need to be replaced, endpoint detection and response, deciding what traffic is actionable and defining that in your SIEM, forensic analysis, threat hunting, event response, the conversations are as malleable as the threat landscape.
It’s easy to isolate the things in your environment that are very difficult to defend AND take a skilled defender and complex tooling to defend. Those conversations flow with either junior analysts or C-Level executives. This is the “Sounds difficult. Is difficult.” type of conversation. Ditto the “Sounds easy. Is easy.” conversations are easy to have in either direction. The most difficult topics to convey fall into the “Sounds difficult. Is easy.” or “Sounds easy. Is difficult.” In my experience these conversations are usually much easier to deliver in one direction and much more difficult in the other. Jazz guys enjoy the nuance of Colaiuta and can’t wrap their minds around Lombardo while metalheads love him and don’t want to be bothered by ghost notes. By taking a moment to dissect your topic and determine where you are going to run into the “Sounds difficult. Is easy.” or the “Sounds easy. Is difficult.” situation it will allow you to prepare for those more challenging conversations so that you can craft a narrative to best capture the nuance that might be lost in a highly technical conversation with a C-Level exec, or the motivation for waiting for the next financial quarter for new tooling that the analysts really need.
I’m not going to lie – you can prepare this way and things can still fall on deaf ears, they can still underestimate the lift required because people are fallible but if you prepare just a bit and know your audience you can drag your C-Level into a discussion on polyrhythm and pull your junior analyst up with a little Vinnie Colaiuta and make them all feel like Phil Rudd.
Cisco Talos discovered a new information stealing campaign operated by a Vietnamese-speaking threat actor targeting government and education entities in Europe and Asia. PXA Stealer targets victims’ sensitive information, including credentials for various online accounts, VPN and FTP clients, financial information, browser cookies, and data from gaming software. PXA Stealer also has the capability to decrypt the victim’s browser master password and uses it to steal the stored credentials of various online accounts.
Harvested credentials can allow attackers direct access to your environment without the need to exploit vulnerabilities or face any of your defensive architecture – they can just log in. Cisco Talos Incident Response has observed an increasing number of engagements where this is the case.
Cisco Talos has released several Snort rules and ClamAV signatures to detect and defend against PXA Stealer.
Attackers are continuing to upload hundreds of malicious packages to the open-source node package manager (NPM) repository in an attempt to infect the devices of developers that rely on these libraries. (Ars Tecnica)
Cybersecurity and Infrastructure Security Agency (CISA) has confirmed that it’s director Jen Easterly will step down from her position on President-elect Donald Trump’s Inauguration Day. (Dark Reading)
Palo Alto Networks has released a patch to fix a critical vulnerability in some instances of its firewall management interfaces. PAN observed threat activity exploiting an unauthenticated remote command execution vulnerability against firewall management interfaces. (Bleeping Computer, Dark Reading)
CyberCon Romania (Nov 21-22)
Bucharest, Romania
Martin Lee from Cisco Talos will speak on a panel discussion Maintaining Resilience for a Secure Cyber Infrastructure.
misecCON (Nov. 22)
Lansing, Michigan
Terryn Valikodath from Cisco Talos Incident Response will explore the core of DFIR, where digital forensics becomes detective work and incident response turns into firefighting.
AVAR (Dec 4-6)
Chennai, India
Vanja Svancer and Chetan Raghuprasad from Cisco Talos will both present, Vanja will be discussing Exploring Vulnerable Windows Drivers, while Chetan presents Sweet and Spicy Recipes for Government Agencies by SneakyChef.
SHA 256: c20fbc33680d745ec5ff7022c282a6fe969c6e6c7d77b7cfac34e6c19367cf9a
MD5: 3bc6d86fc4b3262137d8d33713ed6082
Typical Filename: 8c556f0a.dll
Claimed Product: N/A
Detection Name: Gen:Variant.Lazy.605353
SHA 256: bea312ccbc8a912d4322b45ea64d69bb3add4d818fd1eb7723260b11d76a138a
MD5: 200206279107f4a2bb1832e3fcd7d64c
Typical Filename: lsgkozfm.bat
Claimed Product: N/A
Detection Name: Win.Dropper.Scar::tpd
SHA 256: 47ecaab5cd6b26fe18d9759a9392bce81ba379817c53a3a468fe9060a076f8ca
MD5: 71fea034b422e4a17ebb06022532fdde
Typical Filename: VID001.exe
Claimed Product: N/A
Detection Name: RF.Talos.80
SHA 256: 3a2ea65faefdc64d83dd4c06ef617d6ac683f781c093008c8996277732d9bd66
MD5: 8b84d61bf3ffec822e2daf4a3665308c
Typical Filename: RemComSvc.exe
Claimed Product: N/A
Detection Name: W32.3A2EA65FAE-95.SBX.TG
Cisco Talos Blog – Read More
The US Department of Justice has taken down PopeyeTools, a major online marketplace used by cybercriminals to sell…
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More
The company gave details for the first time on its approach to combatting organized criminal networks behind the devastating scams.
Security Latest – Read More
In its latest security report, the parent company of Facebook, Instagram and WhatsApp highlighted its role in fighting scams that originate in crime compounds, primarily in Asia.
The Record from Recorded Future News – Read More