How to select the best on-ramp and off-ramp for you?
Choosing the best on-ramp and off-ramp solutions is a key part of navigating the cryptocurrency landscape – to…
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More
Choosing the best on-ramp and off-ramp solutions is a key part of navigating the cryptocurrency landscape – to…
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More
Finastra is investigating a data breach after a hacker claimed the theft of information from an internal file-transfer application.
The post Financial Software Firm Finastra Investigating Data Breach appeared first on SecurityWeek.
SecurityWeek – Read More
Chinese black market operators are openly recruiting government agency insiders, paying them for access to surveillance data and then reselling it online—no questions asked.
Security Latest – Read More
Just like other technologies that have gone before, such as cloud and cybersecurity automation, right now AI lacks maturity.
The post AI – Implementing the Right Technology for the Right Use Case appeared first on SecurityWeek.
SecurityWeek – Read More

The U.S. Department of Agriculture (USDA) has announced the use of Fast IDentity Online (FIDO) protocols, a new solution for phishing-resistant authentication. This shift to FIDO-based multi-factor authentication (MFA) has proven successful in securing USDA systems against credential theft and phishing attacks.
With many seasonal employees and workers in specialized environments, such as laboratories requiring decontamination procedures, USDA cannot fully rely on Personal Identity Verification (PIV) cards, which are typically used for secure authentication across government agencies.
USDA’s workforce includes not only full-time employees but also a large number of seasonal workers who are ineligible for PIV cards. Furthermore, certain USDA staff work in environments, such as bio-containment labs, where standard PIV cards cannot survive the decontamination processes required.
Historically, USDA managed this by providing users with temporary user IDs and passwords. However, as credential phishing attacks became more sophisticated, the USDA found this approach increasingly vulnerable to cyber threats.
USDA identified the need for a secure, phishing-resistant authentication method that would work across a variety of environments and use cases. The agency needed to move beyond passwords and user IDs, adopting a solution that would meet modern cybersecurity standards while accommodating the unique needs of its workforce.
FIDO is a set of open standards designed to provide secure, passwordless authentication. Unlike traditional forms of MFA, which can still be vulnerable to phishing attacks, FIDO leverages public key cryptography to bind credentials to the user’s device. This approach is inherently resistant to phishing attempts because even if a malicious actor attempts to trick users into revealing their credentials, they cannot access the system without the physical device used for authentication.
The USDA’s decision to adopt FIDO was driven by its ability to prevent credential phishing—one of the most common and dangerous threats faced by organizations today. With FIDO, USDA employees can authenticate without passwords, using cryptographic keys stored on secure devices. This approach mitigates the risk posed by increasingly sophisticated credential phishing attacks that exploit the weaknesses of SMS codes, authenticator apps, or even push notifications.
Before transitioning to FIDO, USDA’s Identity, Credential, and Access Management (ICAM) division conducted a thorough review of the agency’s needs. They identified key use cases where employees could not use PIV cards and where traditional MFA methods were insufficient.
These included seasonal workers, employees waiting for PIV cards, and those working in high-security or physically demanding environments where card-based solutions were impractical.
With a centralized identity management system already in place, USDA was well-positioned to implement a FIDO-based solution. The agency used Microsoft Entra ID to integrate FIDO capabilities, allowing them to extend phishing-resistant authentication to core services such as:
The centralization of USDA’s ICAM system under a unified platform allowed for more agile updates, enabling the rapid rollout of FIDO across various IT environments. By focusing on four main enterprise services, USDA was able to significantly reduce its exposure to phishing attacks while meeting the needs of its diverse workforce.
USDA’s adoption of FIDO technology was not just about protecting individual users—it was about addressing a systemic issue of security across the organization. FIDO protocols were integrated with USDA’s existing SSO platform, which serves over 600 internal applications. This integration allowed USDA to enhance the security of both cloud-based and on-premises systems, protecting users from more advanced forms of MFA bypass techniques.
FIDO’s support for hardware-bound authentication methods, like Microsoft’s Windows Hello for Business (WHfB) and FIPS-140 validated security keys, played a pivotal role. These devices are bound to the user’s hardware, making it almost impossible for a hacker to bypass the authentication process without physical access to the device.
Furthermore, USDA utilized its centralized human resources (HR) system as the authoritative source for identity lifecycle management, ensuring that access rights and credentials were appropriately provisioned and de-provisioned. This integration made managing user access more streamlined and secure, particularly as the agency transitioned to more cloud-based services.
USDA’s early adoption of FIDO technology placed them ahead of the curve in implementing phishing-resistant MFA. Their solution aligns with the broader federal initiative outlined in the U.S. government’s Moving the U.S. Government Toward Zero Trust Cybersecurity Principles (M-22-0922), which mandates the transition to phishing-resistant MFA for federal agencies.
By adopting FIDO, USDA not only improved its security posture but also contributed to the federal push for Zero Trust cybersecurity, a model that assumes breaches are inevitable and advocates for continuous monitoring and verification of user access. FIDO, with its strong encryption and device-based authentication, is a critical part of this Zero Trust framework.
USDA’s experience with FIDO offers valuable lessons for other organizations looking to enhance their cybersecurity defenses against phishing and credential theft. The key takeaways from USDA’s implementation include:
The USDA’s adoption of Fast IDentity Online (FIDO) for phishing-resistant multi-factor authentication (MFA) has strengthened its cybersecurity defenses. By using FIDO, USDA has protected its diverse workforce from credential theft and phishing attacks while ensuring secure access to online systems.
The agency’s centralized approach to Identity, Credential, and Access Management (ICAM) and its commitment to incremental improvements have been a key factor to this success. USDA’s implementation not only meets federal cybersecurity requirements but also exemplifies a proactive approach to Zero Trust principles.
The post USDA Implements Phishing-Resistant Multi-Factor Authentication (MFA) with Fast Identity Online (FIDO) appeared first on Cyble.
Blog – Cyble – Read More
Five alleged members of the infamous Scattered Spider cybercrime crew have been indicted in the U.S. for targeting employees of companies across the country using social engineering techniques to harvest credentials and using them to gain unauthorized access to sensitive data and break into crypto accounts to steal digital assets worth millions of dollars.
All of the accused parties have been
The Hacker News – Read More
Exploitation attempts seen for two recently patched Citrix Session Recording vulnerabilities tracked as CVE-2024-8068 and CVE-2024-8069.
The post Exploitation Attempts Target Citrix Session Recording Vulnerabilities appeared first on SecurityWeek.
SecurityWeek – Read More
We’re excited to announce the latest update to Threat Intelligence (TI) Lookup. The enhanced home screen now integrates all techniques and tactics of the MITRE ATT&CK matrix, along with relevant malware samples and signatures.
Let’s dive into how these updates can transform your workflow and help you tackle threats with greater confidence.

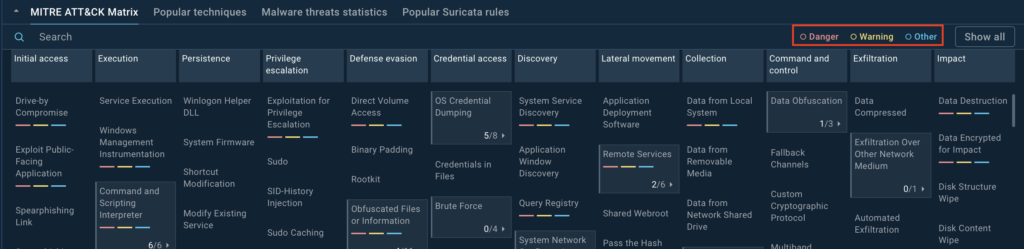
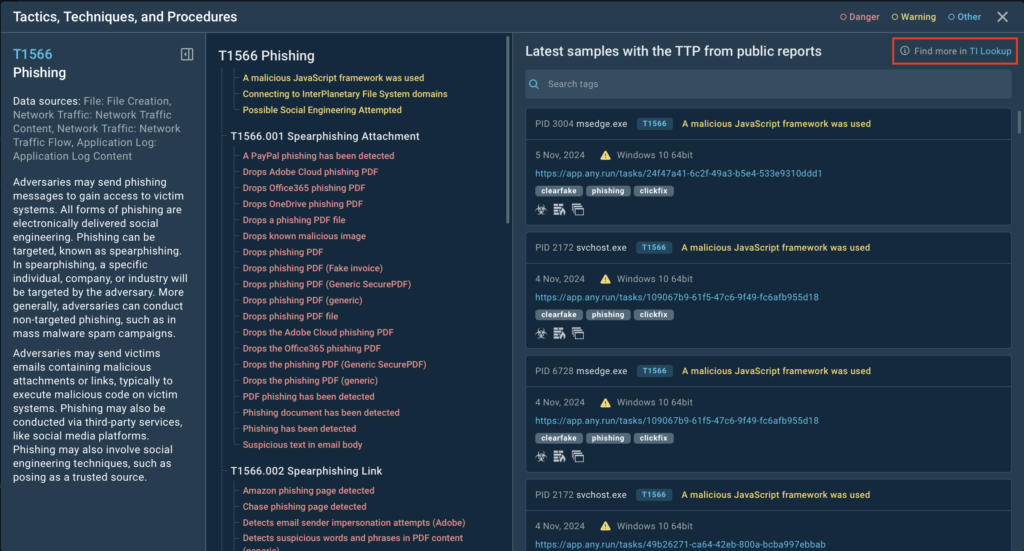
The centerpiece of the updated Threat Intelligence home screen is the MITRE ATT&CK matrix, neatly organizing tactics and techniques into a clear, actionable layout.
But here’s where it gets really exciting: The matrix is interactive and lets you explore actual malware samples tied to each technique. This bridges the gap between theoretical knowledge of attack patterns and practical insights into how those patterns are used in real-world attacks.
The new home screen is designed to be super functional for anyone working with malware, whether you’re a malware analyst, an incident responder, a threat researcher, or just someone curious about how malware operates.
One of the core goals of this redesign was to turn the MITRE ATT&CK classification into a working tool for analysts. Instead of just showcasing popular techniques, the matrix now:
This update takes analysts beyond just understanding the techniques and tactics. It helps them put that knowledge into action.
They can see how specific techniques have been used in real attacks, spot the malware families tied to certain behaviors, and fine-tune their detection rules to better defend against similar threats in the future.
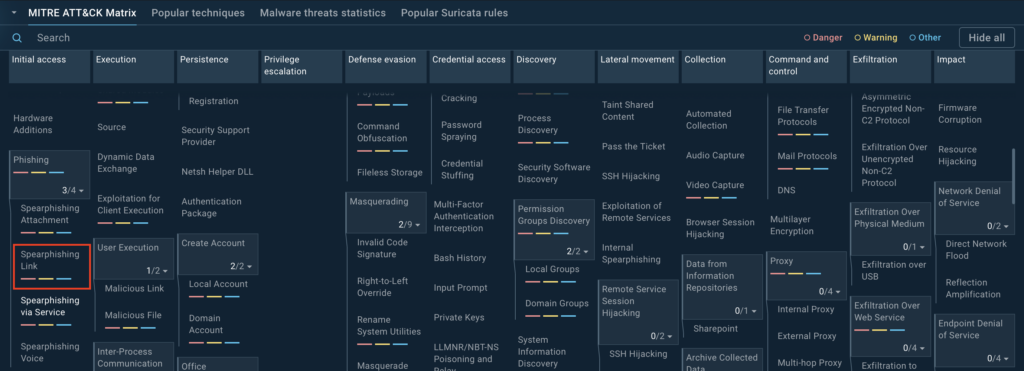
With the new home screen, all techniques and tactics are displayed clearly. Clicking on any technique opens up a wealth of information and analysis samples related to it, including its sub-techniques.
The updated TI Lookup now includes filtering options for MITRE ATT&CK matrix techniques to help users prioritize threats:
Users can refine their view by choosing to hide or display specific categories using the button next to the labels.
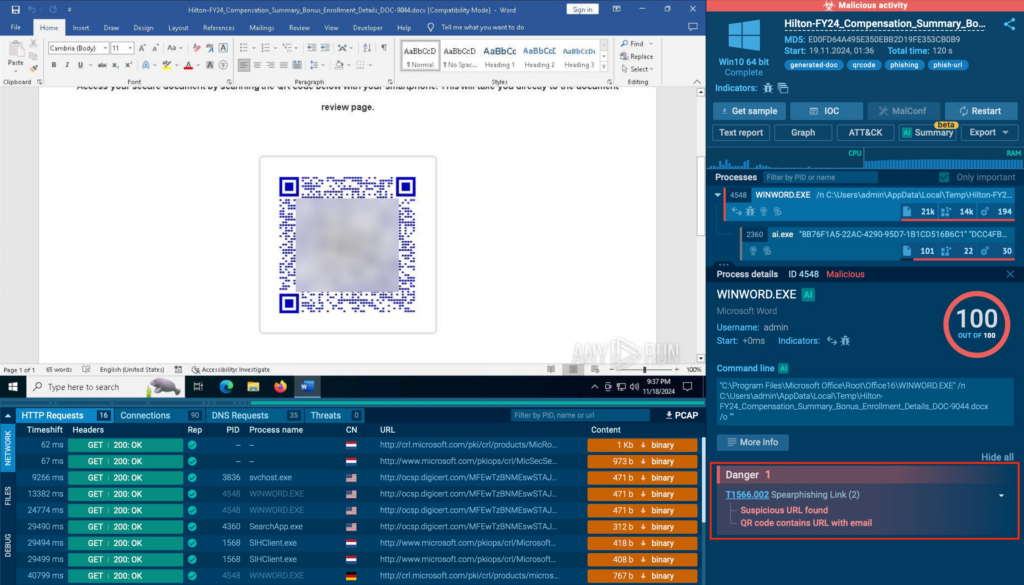
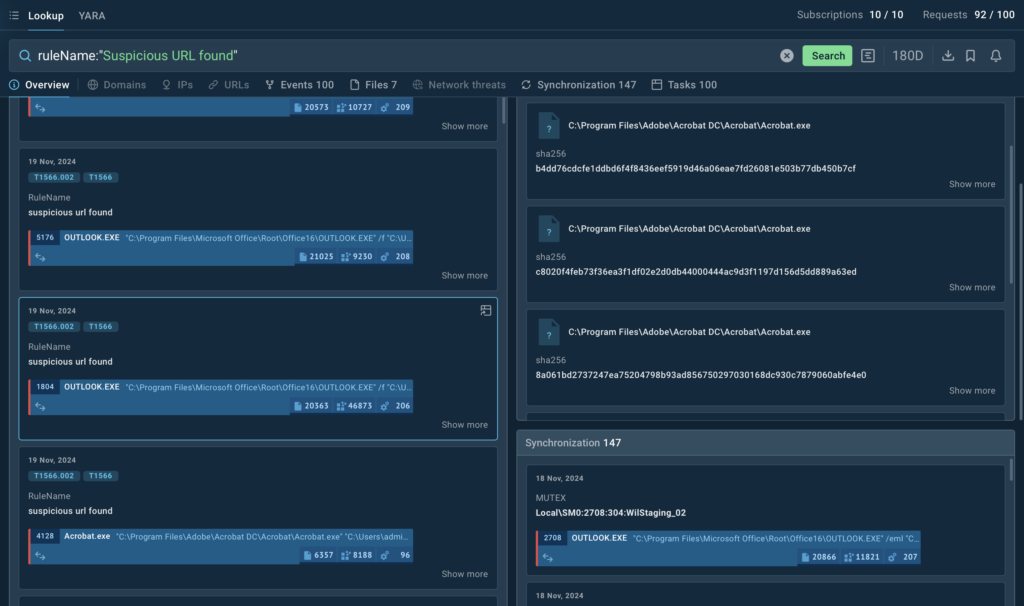
Here’s an example of how the redesigned TI Lookup can be used to explore real-world malware scenarios. Let’s take a closer look at the samples related to spearphishing links.
In the Initial Access section of the MITRE ATT&CK matrix, you’ll find Phishing (T1566), which includes sub-techniques like spearphishing.
Clicking on Phishing brings up a new tab with detailed information, including:

For example, under the Spearphishing Links sub-technique, you’ll see signatures pulled from actual analysis sessions.
These might include:
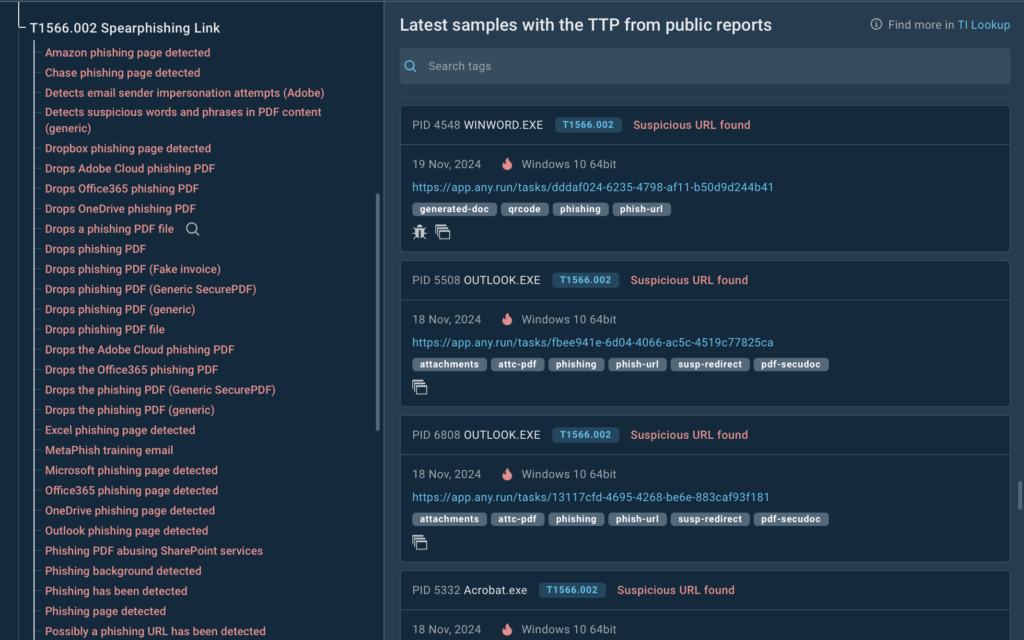
When you select a technique, sub-technique, or a specific signature, the service will show relevant samples along with links to corresponding sandbox sessions where the selected TTP was identified.
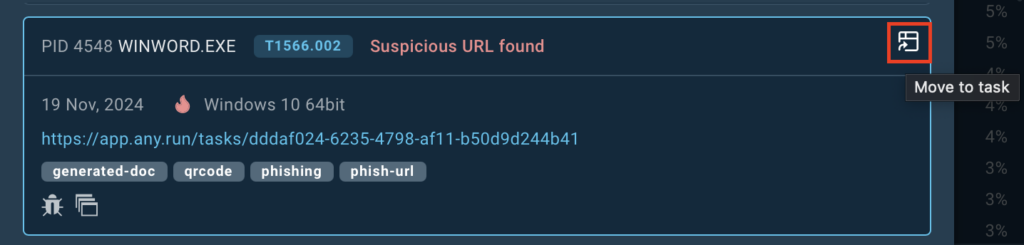
With one click, you can jump into ANY.RUN’s sandbox to observe the behavior of the malware in action and analyze the attack’s overall structure.
If you want to dive deeper and gather Indicators of Compromise (IOCs) for your analysis, there are two ways to do so.
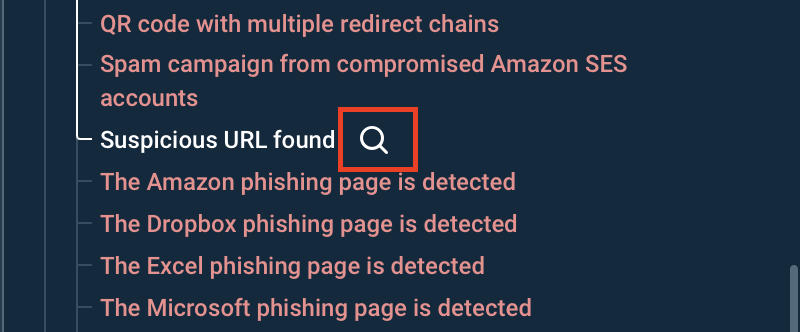
First, you can use the search icon next to each threat to instantly uncover additional details, such as domains, IPs, URLs, files, and other relevant context tied to the selected technique.
Alternatively, by clicking on TI Lookup in the upper-right corner of the tab, you’ll be redirected to the dedicated TI Lookup search page.
Here, you can refine your search and explore a wealth of actionable intelligence. TI Lookup is designed to provide everything an analyst needs in one place, comprehensive data about specific techniques, behavior patterns, malware families, and their associated IOCs, IOBs, and IOAs.
This new workflow not only makes it easier to understand the processes behind a specific technique but also provides the context needed to develop better strategies for combating similar threats.
For instance, by analyzing spearphishing links in-depth, you’ll gain insights into the methods attackers use to trick victims and the types of payloads delivered. Armed with this knowledge, you can:

Whether it’s phishing, persistence techniques, or lateral movement, TI Lookup provides the tools you need to dive deep into the data and make informed decisions. With the redesigned home screen, the service is now even more useful for security analysts and researchers, as it helps them easily find samples where specific TTPs were used.
Ready to see it in action? Head over to Threat Intelligence Lookup and start exploring!
ANY.RUN helps more than 500,000 cybersecurity professionals worldwide. Our interactive sandbox simplifies malware analysis of threats that target both Windows and Linux systems. Our threat intelligence products, TI Lookup, YARA Search and Feeds, help you find IOCs or files to learn more about the threats and respond to incidents faster.
With ANY.RUN you can:
Request free trial of ANY.RUN’s products →
The post Explore MITRE ATT&CK Techniques in Real-World Samples with TI Lookup appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
Google has revealed that its AI-powered fuzzing tool, OSS-Fuzz, has been used to help identify 26 vulnerabilities in various open-source code repositories, including a medium-severity flaw in the OpenSSL cryptographic library.
“These particular vulnerabilities represent a milestone for automated vulnerability finding: each was found with AI, using AI-generated and enhanced fuzz targets,”
The Hacker News – Read More
Threat hunters are warning about an updated version of the Python-based NodeStealer that’s now equipped to extract more information from victims’ Facebook Ads Manager accounts and harvest credit card data stored in web browsers.
“They collect budget details of Facebook Ads Manager accounts of their victims, which might be a gateway for Facebook malvertisement,” Netskope Threat Labs researcher
The Hacker News – Read More