Overview
Cyberattacks on a country’s critical infrastructure have become a growing malicious trend globally. The surge in cybercrime threats and its growing impact on national security, businesses, and individuals has led experts to closely examine which regions face the most cyberattacks.
A recent study from the World Cybercrime Index (WCI) compiled by an international team of researchers, shed light on the most targeted countries, ranking them based on the severity of cyberattacks, the skill of the perpetrators, and the professionalism of the cybercriminals involved.
As of 2024, these countries face the highest levels of cybercrime threats, driven by a complex mix of geopolitical factors, technological infrastructure, and economic conditions. This blog explores the top 10 countries that are most impacted by cyberattacks and why they are at the forefront of the global cybersecurity challenge.
10. India: A Victim of Cybercrime Amid Rapid Digitalization
India ranks tenth in the global cybercrime index, experiencing an uptick in cyberattacks due to its rapid digital transformation. The country’s massive online population and growing e-commerce sector make it an appealing target for cybercriminals. Phishing scams, financial fraud, and ransomware attacks are common in India, with both individuals and organizations being affected. The Indian government has been working to bolster cybersecurity, but the increasing maliciousness of cybercriminals presents an ongoing challenge for the country.
Read also: https://cyble.com/resources/research-reports/india-threat-landscape-report-2024/
9. Brazil: A Growing Cybercrime Hotspot in Latin America
Brazil, the largest economy in Latin America, has witnessed a surge in cyberattacks, particularly those targeting its financial sector and government institutions. Brazil’s growing digital economy has made it an attractive target for cybercriminals involved in fraud, data breaches, and ransomware. The WCI places Brazil ninth, citing its vulnerability to cybercrime despite efforts to improve cybersecurity regulations. Cybercriminal groups operating in Brazil often specialize in online fraud, identity theft, and other forms of financial cybercrime.
Read also: https://cyble.com/blog/goatrat-android-banking-trojan-variant-targeting-brazilian-banks/
8. United Kingdom: A Rising Cyberattack Target
The United Kingdom faces major cybersecurity threats, ranking eighth on the WCI. As a major financial and technological hub, the UK is often targeted by both cybercriminals and state-sponsored actors. Ransomware attacks and data breaches have been particularly impactful, with high-profile incidents affecting public and private sector organizations. The UK government has increased its efforts to combat cybercrime, but the country remains a target due to its global standing and the increasing digitization of its economy.
7. North Korea: Cyber Warfare and Financial Theft
North Korea’s cybercriminal activities are well-documented, with the country’s state-sponsored hackers playing a prominent role in cyberwarfare and financial cybercrime. The regime has been linked to several high-profile cyberattacks, including the infamous WannaCry ransomware attack and attacks on South Korean entities.
North Korea’s cyber units, such as Lazarus Group, are involved in stealing funds through cybercrime to finance the country’s regime. Their targets are often financial institutions, cryptocurrency exchanges, and government agencies, making North Korea a critical player in the global cybercrime arena.
6. Romania: A Hotbed for Cybercrime Groups
Romania is a big player in the global cybercrime ecosystem, ranking sixth on the WCI. The country is home to several notorious cybercriminal groups involved in ransomware attacks, data theft, and financial fraud.
Romanian hackers are known for their technical expertise and ability to deploy malware across multiple sectors. The Romanian government has made efforts to crack down on cybercrime, but the country remains a hotbed for cyberattacks on countries worldwide, particularly targeting financial institutions and online businesses.
Read also: https://cyble.com/blog/romania-urges-energy-sector-of-proactive-scanning-amid-lynx-ransomware-threat/
5. Nigeria: A Leading Hub for Cybercrime in Africa
Nigeria has earned a place on the list of the top cyberattack countries due to its increasing involvement in online fraud, scams, and cybercrimes. Known for its widespread involvement in “419” fraud (advance-fee fraud) and cyber scams targeting both individuals and corporations globally, Nigeria’s cybercriminal activities are a growing concern. The country is also home to highly organized cybercrime groups, some of which use cybersecurity tools to launch phishing campaigns and steal sensitive data. The lack of sufficient cybersecurity infrastructure and regulatory enforcement contributes to the persistent cybercrime problem in Nigeria.
4. United States: A Prime Target and Source of Cyberattacks
The United States is not only a major source of cyberattacks but also one of the most heavily targeted nations globally. As the world’s largest economy and a hub for technological innovation, the U.S. faces an array of cyberthreats, from cybercriminals seeking financial gain to nation-state actors pursuing espionage objectives.
The U.S. has witnessed high-profile cyberattacks, including those targeting critical infrastructure, government agencies, and multinational corporations. Ransomware attacks, data breaches, and election interference campaigns are just a few examples of the cybercrimes affecting the U.S., positioning it as one of the countries most impacted by cyberattacks.
Read also: https://cyble.com/resources/research-reports/us-threat-landscape-report-a-time-of-growing-peril/
3. China: A Major Player in Cyber Espionage
China ranks third in the global cybercrime rankings, largely due to its involvement in large-scale cyber espionage operations. The country has been accused of conducting numerous cyberattacks aimed at stealing intellectual property and accessing sensitive government and corporate data across the globe.
Chinese cybercriminals are notorious for their high level of technical skill and have been linked to various attack methods, including Advanced Persistent Threats (APT). China’s rapid technological growth and its economic prominence have made it both a source and a victim of cyberattacks, making it one of the top cyberattack countries.
2. Ukraine: A Geopolitical Hotspot for Cyberattacks
Ukraine is another country that faces immense cybercrime threats. Since the 2014 annexation of Crimea, Ukraine has been subject to numerous state-sponsored cyberattacks, primarily from Russia. The country has been the target of ransomware attacks and power grid disruptions, making it a prominent example of cyberwarfare in the 21st century.
The WCI ranks Ukraine second due to its vulnerability to cyberattacks, especially amid ongoing political tensions and military conflicts with Russia. Ukrainian government agencies, critical infrastructure, and businesses have been the focus of cyber attackers.
Read also: Hackers Target Ukrainian Army with Fake Military Apps to Siphon Authentication and GPS Data
1. Russia: The Epicenter of Cybercrime
Russia remains the undisputed leader in terms of cybercriminal activity. Ranked number one on the World Cybercrime Index, Russia has been a hub for various cybercrime types, including state-sponsored attacks, ransomware campaigns, and hacking for espionage purposes.
The country’s role in cyberattacks on countries globally, particularly targeting political opponents, is well-documented.
Read also: Russian State Hackers Biggest Cyber Threat to US, UK and EU Elections
The troubling nature of cybercriminal operations in Russia, coupled with their expertise in developing malware, makes the nation a constant threat to others.
Conclusion: The Global Fight Against Cybercrime
As we move into 2025, cyberattacks on countries are increasingly impacting vital sectors like government, finance, and healthcare. Countries such as Russia, Ukraine, China, and the United States are at the forefront of this growing global issue. To combat these threats, governments, organizations, and cybersecurity experts must collaborate to strengthen defenses and proactively monitor cybercriminal activities.
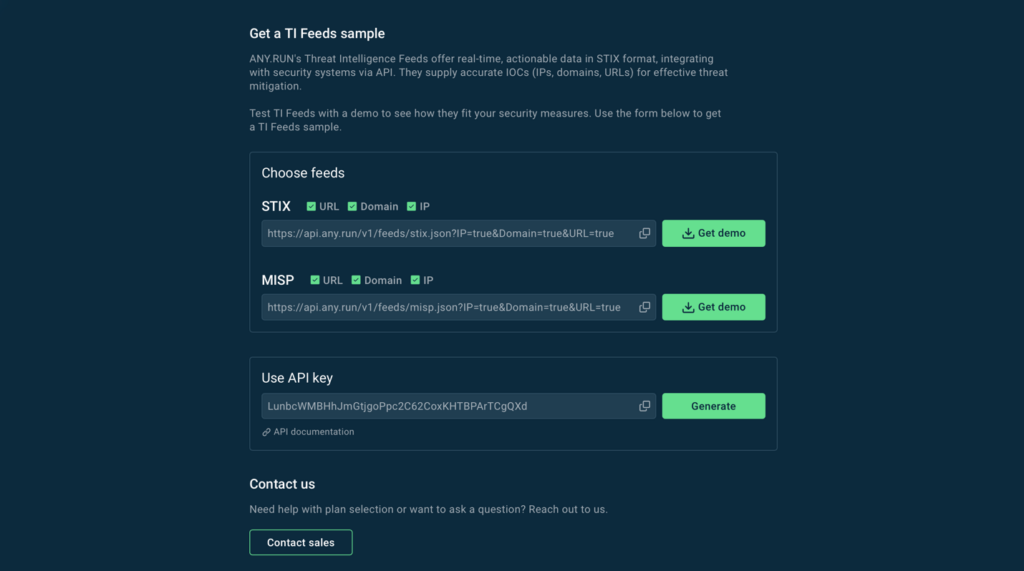
Cyble, a leader in AI-powered cybersecurity, is playing an important role in this effort. Cyble offers multiple threat intelligence platforms that offer real-time monitoring, which processes vast amounts of dark web data and provides actionable insights. By leveraging AI-driven platforms like Cyble, organizations and government sectors can protect their infrastructure and respond to cyberattacks more effectively, helping to ensure a more secure future.
References
The post Russia, Ukraine, China, and More: The Nations at the Center of the Cybercrime Epidemic appeared first on Cyble.
Blog – Cyble –