BTMOB: A stealthy RAT burrowing deep into Android devices
The malware pairs remote access capabilities with ready-made campaign tools, lowering the barrier for full device compromise
WeLiveSecurity – Read More
The malware pairs remote access capabilities with ready-made campaign tools, lowering the barrier for full device compromise
WeLiveSecurity – Read More
May 2026 showed how fast routine business activity can turn into real security exposure. ANY.RUN observed phishing campaigns, fileless malware delivery, credential theft, OTP interception, and remote access abuse targeting organizations across industries.
From fake invitations and banking portals to compromised B2B websites and Word Online lures, the month’s attacks had one thing in common: they were built to look normal long enough to delay detection.
Here are the major attacks from May and what SOC teams should take away from them.
The most important lesson from May’s attacks is that many of these campaigns were designed to hide inside normal business activity long enough to create real exposure.
May’s campaigns were concentrated around the business functions and user groups that attackers can use to reach valuable accounts, financial workflows, and internal systems. For CISOs, this helps show where security reviews, detection coverage, and response playbooks should be prioritized first.
| Target Area | What Attackers Focused On |
|---|---|
| Finance and banking users | Banking login flows, customer account access, and payment-related interactions. |
| Procurement and payroll teams | Employees handling invoices, purchase orders, payroll files, and supplier communication. |
| Corporate email users | Business inboxes, Microsoft 365 accounts, webmail access, and internal communication channels. |
| IT and support workflows | Remote support processes, software installation flows, and admin-adjacent activity. |
| Employees using business websites | Everyday browsing activity on legitimate or familiar-looking websites. |
| SaaS and cloud account users | Accounts connected to business apps, shared data, and company operations. |
| High-exposure industries | Finance, banking, healthcare, manufacturing, technology, education, and government. |
In May, ANY.RUN tracked a fake invitation phishing campaign targeting U.S. organizations. The attack used familiar event-style lures to guide users through what looked like a normal invitation flow. Behind that flow, attackers could move victims toward credential theft, OTP interception, and in some cases remote access tool delivery.
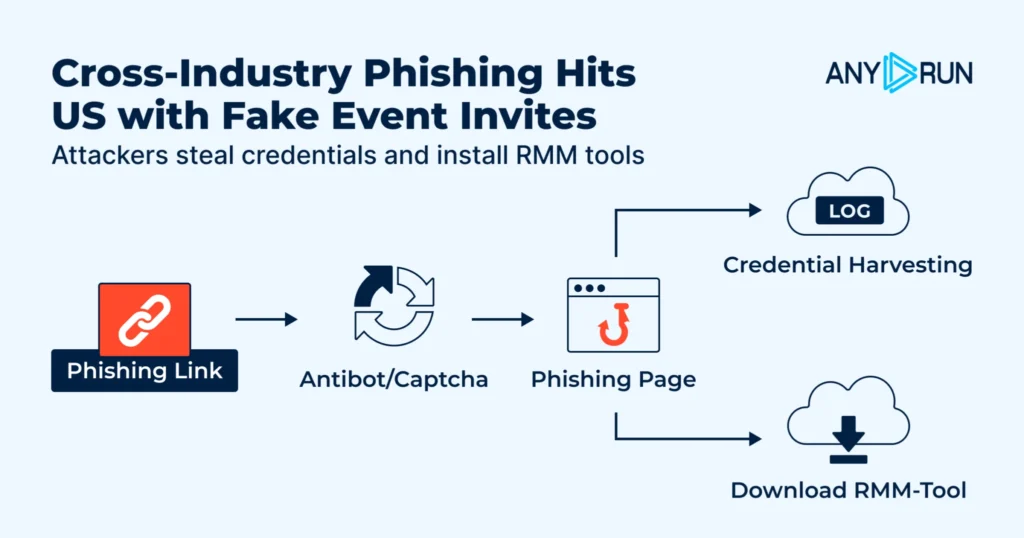
This campaign shows how a simple business interaction can turn into an access incident. The user does not need to open an obviously malicious file or interact with a suspicious-looking page. They only need to follow an invitation that feels familiar. From there, the risk can expand from one employee action to exposed credentials, compromised mailboxes, unauthorized remote access, and wider business exposure.
CISO priority: Security leaders should treat fake invitation flows as more than phishing noise. These attacks test whether the SOC can connect email, browser, identity, and remote access signals fast enough to understand real exposure. ANY.RUN helps teams safely open the full flow, observe credential and OTP collection, identify possible remote access tool delivery, and pivot to related infrastructure before the same campaign reaches more users.
ANY.RUN also analyzed an Agent Tesla campaign targeting enterprises in Latin America. The attack used familiar business-document themes, including purchase orders, invoices, payroll files, and procurement requests, to reach employees who regularly work with external files and supplier communication.
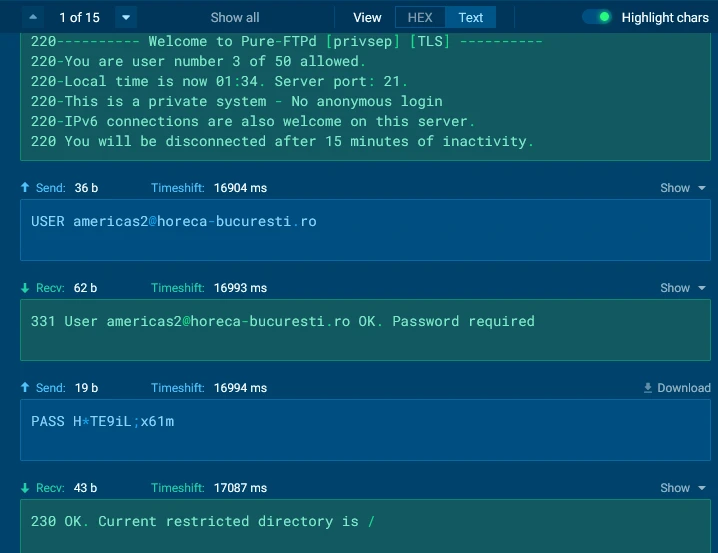
This type of attack goes after the business functions where one stolen credential can quickly create financial and operational exposure. If attackers gain access to email accounts, browser credentials, FTP logins, or other stored data, the risk can move beyond one infected endpoint. It can support BEC, supplier fraud, cloud account compromise, and wider access across company systems.
Business risk to reduce: Finance, procurement, and payroll inboxes should be treated as high-risk business entry points. A suspicious invoice or purchase order is not only an attachment problem; it may be the first sign of credential theft that can later support fraud or unauthorized access. With behavior-based sandbox analysis, teams can quickly confirm whether a file executed, what data it tried to collect, and which accounts need immediate protection.
May also showed how legitimate B2B websites can be abused to deliver malware without relying on obvious malicious files. In this activity, attackers used compromised websites and injected scripts to move users toward PowerShell execution, in-memory payload delivery, and outbound C2 communication.
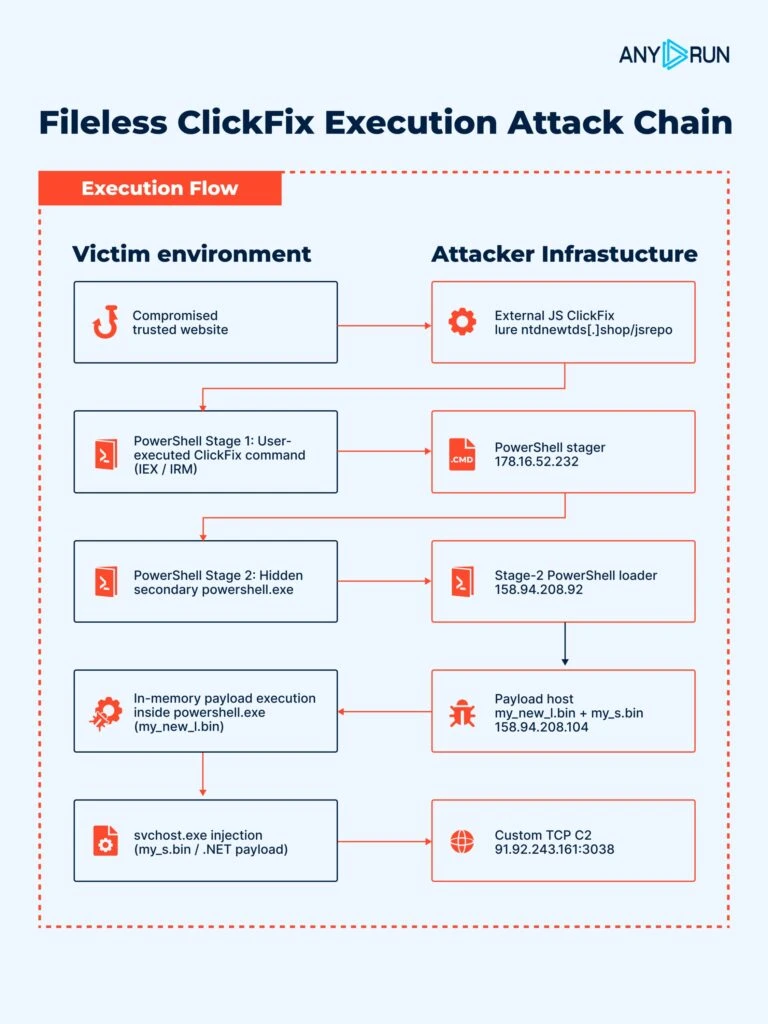
This is dangerous as the attack starts from a place employees may already trust. The website can look legitimate, the traffic may not stand out at first, and the malicious activity becomes clearer only later in the chain. For enterprises, that means a normal browsing session can turn into fileless execution before the SOC has enough evidence to react.
Detection gap to close: This is where reputation-based controls are not enough. A known business website can still become part of the attack chain, and fileless execution may leave fewer obvious artifacts for Tier 1 teams to catch. ANY.RUN gives analysts a way to see what happens after the page loads: script behavior, PowerShell activity, memory execution, process injection, and C2 communication. That turns a suspicious browsing event into a response-ready case.
ANY.RUN tracked a large-scale phishing campaign impersonating a U.S. financial institution. The campaign used a multi-step flow to collect usernames, passwords, OTP codes, and email verification data. Its infrastructure was also highly reusable, with hundreds of related phishing domains already identified.
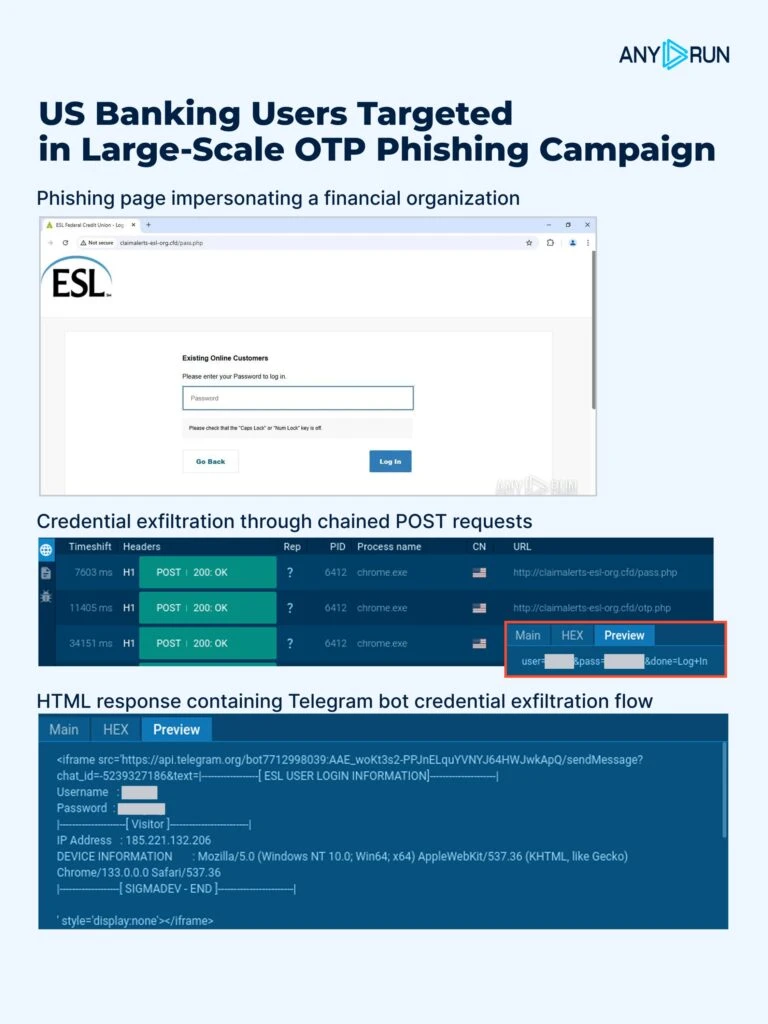
This attack highlights a dangerous shift: MFA does not remove phishing risk when attackers can intercept OTPs in real time. Once users submit credentials and verification codes, attackers can move closer to account takeover, fraud, and unauthorized access before security teams have a clear picture of what happened.
For enterprises, the lesson goes beyond one banking-themed campaign. Any organization that relies on login codes, email verification, or user-driven authentication flows needs to understand where those flows can be copied, replayed, or abused.
MSSP priority: The priority is to move from single-alert handling to campaign-level detection. Blocking one domain will not stop an operation built on reusable templates and rotating infrastructure. ANY.RUN Threat Intelligence helps MSSPs connect related phishing pages, infrastructure, and recurring artifacts, so teams can prove whether authentication data was exposed and help clients act before stolen access becomes fraud or account takeover.
Another May attack started with an Outlook email and redirected users to a fake Word Online / OneDrive-style page. Instead of pushing an obvious malware download, the chain moved through software installation stages and eventually led to remote access through ScreenConnect, with additional activity used to hide the installed tools.
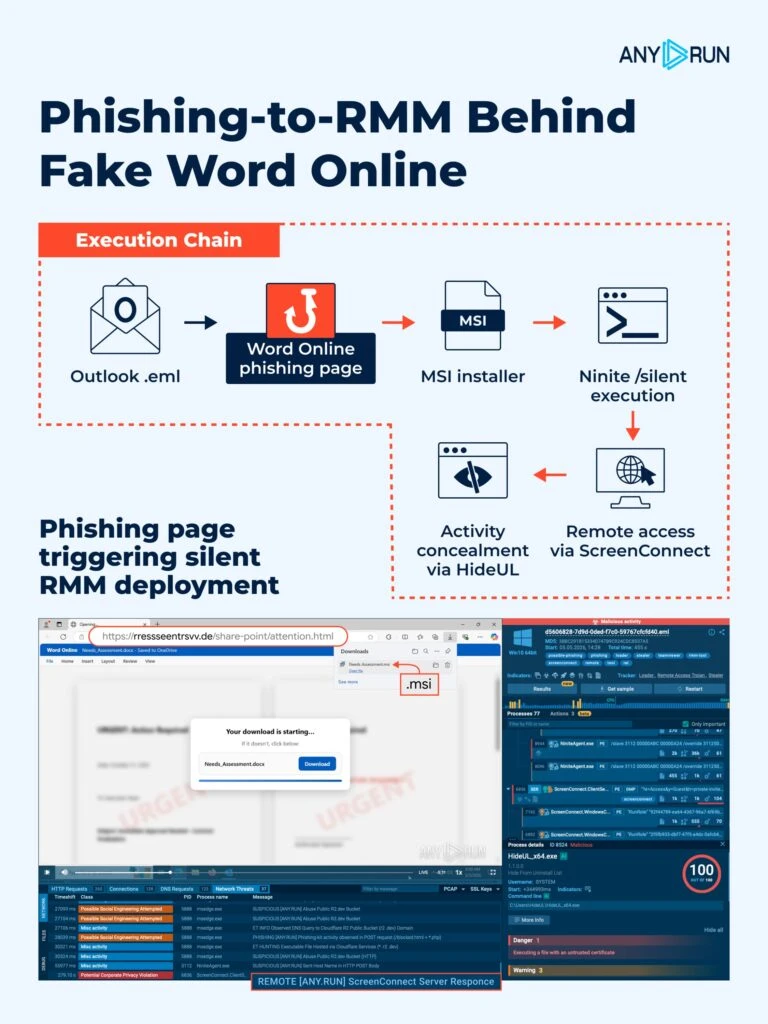
This is the kind of attack that creates real confusion inside security operations. On the surface, the user is trying to open a business document. Deeper in the chain, the attacker is setting up remote access through tools that may look similar to normal IT or support activity.
For MSSPs, this is especially dangerous as one alert may not immediately look like a full compromise. A fake document page, a silent installer, an RMM tool, and concealment activity may appear as separate weak signals unless the team can connect them fast.
Access question for leaders: This attack should push CISOs and MSSPs to ask a harder question: not “Did malware run?” but “Did someone gain hands-on access to the environment?” Remote access abuse is dangerous because it can look close to legitimate IT activity while giving attackers a path back into the network. Teams should expose the full chain from phishing page to installer behavior, RMM deployment, concealment activity, and follow-on access signals to can contain the access path before it becomes persistence.
May also brought attention to BlobPhish, a credential-phishing campaign targeting Microsoft 365, major U.S. financial institutions, and webmail services. Instead of loading a phishing page in the usual way, the attack generated the page directly inside the browser using blob objects, keeping the malicious content in memory.
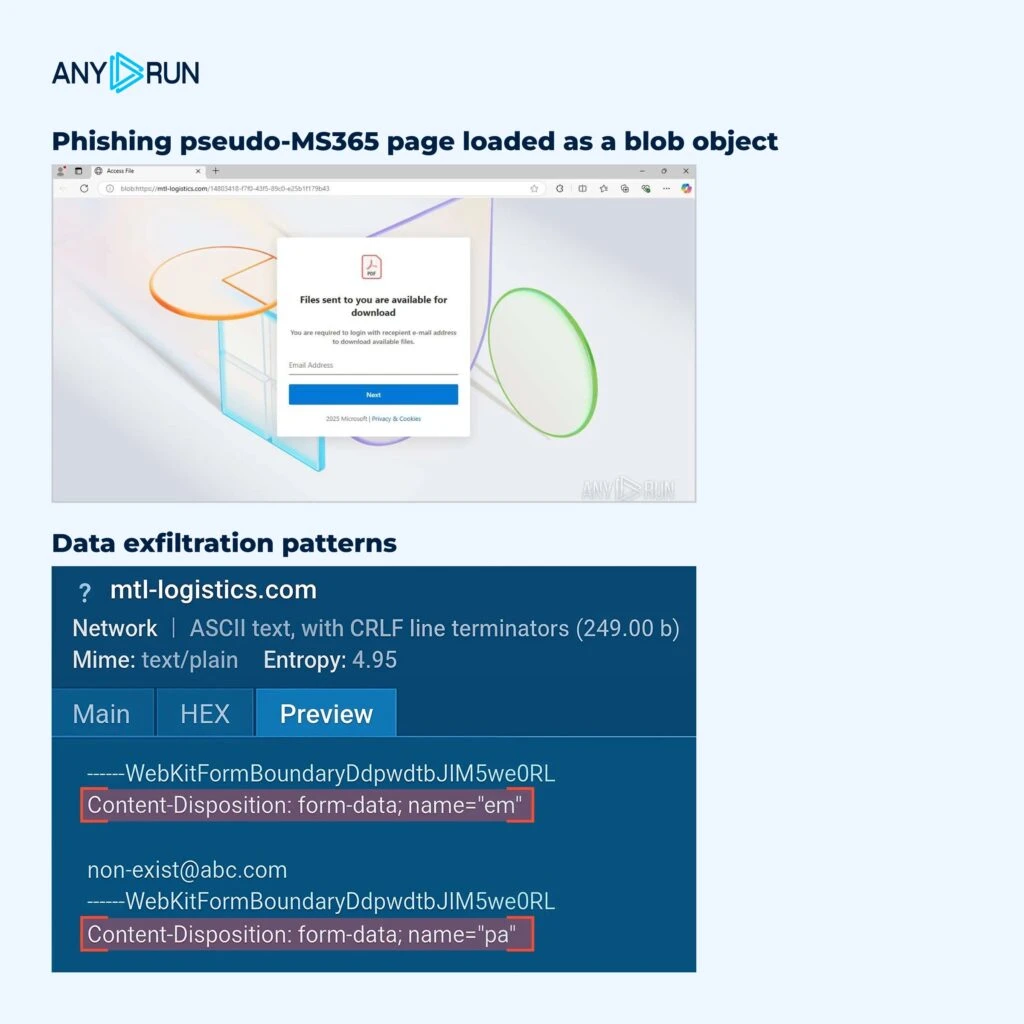
This matters as many phishing defenses still depend on what can be seen in the email, URL, or network request. BlobPhish weakens that visibility. The page can appear after the browser builds it locally, which makes the attack harder to judge using traditional signals alone.
For CISOs, this creates a dangerous gap between what the user experiences and what the security stack can clearly prove. For MSSPs, it raises the investigation burden across clients: teams need to understand not only where the user clicked, but what the browser created after the click.
Visibility gap to close: BlobPhish shows why phishing response cannot stop at URL checks. The real danger is the gap between what the user sees in the browser and what security teams can prove afterward. ANY.RUN allows teams to reproduce the browser-side flow safely, observe how the phishing page is generated, and capture the credential-theft behavior that may not be visible through standard inspection alone. For CISOs and MSSPs, this closes a critical evidence gap before stolen accounts turn into BEC, SaaS compromise, or client-wide exposure.
May’s attacks made one thing clear: the earliest signs of compromise are often hidden inside normal workflows. A user follows an invitation, opens a supplier file, visits a trusted website, enters an OTP, or previews a document, and the SOC may only see scattered signals until the risk has already moved forward.
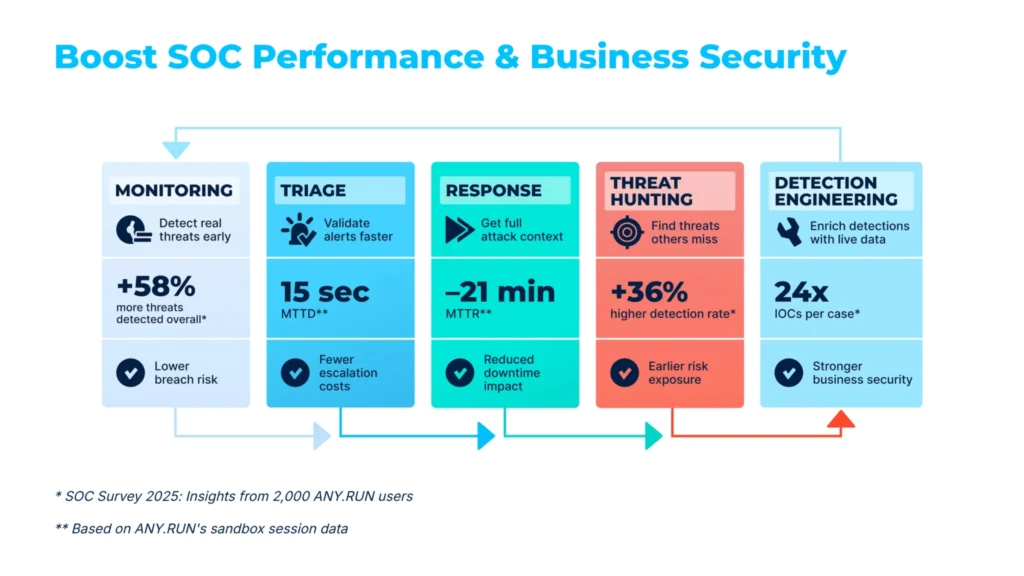
That is where ANY.RUN Enterprise Suite gives security leaders stronger control. Teams get full sandbox functionality, private analyses, multi-platform analysis across Windows, macOS, Linux, and Android, advanced privacy controls, SSO, team management, API access, workspace analytics, and TI Lookup & YARA Premium to validate threats faster and investigate sensitive cases without losing visibility or control.

With these capabilities, enterprise teams can:
ANY.RUN’s 10th-anniversary special offers are available until May 31, making this a timely opportunity for SOCs, MSSPs, and enterprise security teams to expand threat analysis and intelligence capabilities, reduce investigation delays, and respond with more confidence.
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps SOC, MSSP, and enterprise security teams detect threats earlier, and investigate incidents faster.
With its Interactive Sandbox, Threat Intelligence Lookup, TI Feeds, and YARA Search, ANY.RUN gives teams the visibility they need to analyze suspicious files, URLs, scripts, phishing pages, and malware behavior in real time. Security teams can safely observe full attack chains, extract IOCs, investigate related infrastructure, and turn unclear alerts into evidence they can act on.
Trusted by more than 15,000 organizations and 600,000 security professionals worldwide, ANY.RUN supports faster triage, stronger threat visibility, and more confident response across modern SOC workflows.
The post Major Cyber Attacks in May 2026: Fake Invitations, Agent Tesla, BlobPhish, and More appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
Watch out for bogus World Cup websites that mimic official ticket and merchandise flows to steal money and personal data
WeLiveSecurity – Read More
Imagine handing your smartphone over for repair. A couple of days later, you pick it up — and great, it’s working again! But you won’t even realize that your device has been injected with malicious code, allowing attackers to access your smartphone even when it’s locked.
This is the beginning of the story shared by Kaspersky ICS CERT researchers, Alexander Kozlov and Sergey Anufrienko, at the Black Hat Asia 2026 conference. They managed to uncover a vulnerability that flips conventional assumptions about smartphone and IoT security on their head. Its core lies at the very heart of Qualcomm chips.
To grasp the severity of this discovery, we first need to look at how a modern device powered by a Qualcomm chip boots up. Think of it as a fortress with multiple layers of security. Each subsequent layer verifies the pass issued by the previous one. The bedrock foundation — the most trusted layer of them all — is the BootROM, a read-only memory baked directly into the silicon that can’t be modified once it comes off the fab.
The BootROM is the very first thing to run when a device powers on. It verifies the signature of the next bootloader, which in turn verifies the next, building a chain of trust all the way up to the operating system. If an attacker can compromise this chain at the BootROM level, it’s game over: the malicious code will execute before the main operating system even has a chance to load.
This is exactly what attackers can do by exploiting the CVE-2026-25262 vulnerability discovered by Kaspersky ICS CERT researchers.
The research began with a protocol called Sahara. This is a component of Emergency Download Mode (EDL). Manufacturers and service centers use it to revive bricked devices: the phone is connected to a computer via USB, and a special utility program signed by the manufacturer (in this case, Qualcomm) is uploaded to it.
Sahara is implemented directly within the ARM PBL (Primary Boot Loader) — the BootROM itself. This means the protocol runs before any operating system boots, before any user access privileges are checked, and before any security controls are activated. The device simply waits for a USB connection, ready to accept data.
The communication scheme looks simple: the device sends a handshake (HELLO) to the computer, the computer selects the mode, a cycle begins to upload the utility program in chunks, and finally, the device executes the uploaded code. And it was within the verification logic of these very file chunks that the vulnerability was identified.
In technical terms, the bug introduced by the developers is classified as CWE-123: Write-What-Where Condition. This is about as bad as it gets when it comes to flaws in low-level programming. An attacker can write arbitrary data to an arbitrary address in the device memory.
Without diving too deep into the technical weeds, suffice it to say that by exploiting the discovered vulnerability, attackers can gain access to any data on the device, including user-entered passwords, files, contacts, geolocation data, as well as the hardware sensors like the camera and microphone. In certain scenarios, complete control over the device is possible. Just a few minutes of physical access to the device via a cable connection, and the gadget has been compromised. This creates a risk if you hand your smartphone over to a repair shop, pass it to someone else to set up and install apps on, or just leave it unattended.
The CVE-2026-25262 vulnerability affects the following Qualcomm chip series: MDM9x07, MDM9x45, MDM9x65, MSM8909, MSM8916, MSM8952, and SDX50 — every single version released to date, until the vulnerability is patched by the manufacturer.
These are no obsolete museum pieces. The MDM9207, which we used for the bulk of our research, is integrated into modem modules for the internet of things (IoT), industrial equipment, smart home devices, healthcare monitoring systems, logistics trackers, and banking terminals. The MSM8916 powers many budget smartphones, while the SDX50 is used in automotive control units.
The catch is that the attacker needs physical access to the device to pull this off. In the real world, this translates to:
With just a few minutes of physical access to the device an attacker can plant a backdoor so deep inside that standard research tools won’t even detect it in most cases.
Qualcomm was notified of the discovery in March 2025 and confirmed the vulnerability in its chips. To identify it, the vendor reserved CVE-2026-25262, and on April 20, 2026, Kaspersky ICS CERT published technical information on the vulnerability and recommendations for users.
Qualcomm included this vulnerability in its May security bulletin. While fixing already-made devices is fundamentally impossible, the company promised to make all future chips without this vulnerability.
If you currently own a device with an affected chip, use our recommendations below to help mitigate the risk of infection.
If you notice that your gadget with a vulnerable Qualcomm chip starts acting up — overheating when idle, reporting unexpected spikes in network traffic, or exhibiting strange app behavior — you may have fallen victim to this vulnerability. You can wipe the malicious code and reset your device to its baseline state simply by completely cutting its power. This means either pulling the battery or letting it drain all the way to zero until the gadget shuts down entirely. In this case, the malicious code will most likely not persist on the device — during our research, we were unable to confirm that it could achieve persistence in non-volatile memory.
Want to learn more about severe vulnerabilities in Android phones? Check out these posts:
Kaspersky official blog – Read More

Welcome to this week’s edition of the Threat Source newsletter.
“It takes very little to govern good people. Very little. And bad people can’t be governed at all. Or if they could, I never heard of it.” ― Cormac McCarthy, No Country for Old Men
Most of my career has been built on dichotomy: striving to be a supportive teammate while also pushing every boundary in front of me. I’ve often been told to “never do X, only do Y,” but I’ve invariably chosen to do X anyway (even when fraught with peril) to get to the deeper answer. For years, I was told that I should perform in certain ways — instead of in ways that made sense for my brain and way of learning.
I wasn’t governable, but I wasn’t bad. Just … challenging. While Sheriff Ed Tom Bell’s view of good vs. bad is compelling, maybe our careers should be defined as “acquiescent” vs. “challenging.” It’s less of an existential crisis that way.
Over the past few years, I’ve been enjoying the mentoring aspect of my career. One of the things that I love to share with people is that being ungovernable is very challenging early in career; it’snot a favorite of middle management, but it can take you to places that you really want to be (i.e., Talos). The road is going to be longer and much bumpier than your governable cohort, but this is the long con.
The path to Talos was long and arduous, but I’ve learned to make my career choices through the lens of the axiom, “If you’re the smartest person in the room, you’re in the wrong room.” It’s been the only guidepost I’ve needed. I don’t know that it applies to everyone, because everyone is unique, but it absolutely helps me decide what I want to learn, what I want to dive into, who I want to surround myself with.
The secret lies in the last comment — it’s the people. If you continue to search for the smartest people in the room, you’ll find it and when you do, you’ll find that you aren’t ungovernable — rather, you’re understood. Be ungovernable (but kind) in the short term, find new ways to solve problems, think around solutions in new ways, program in different languages, and be the person in the meeting that says, “I think we should do Y instead, and here’s why.”
I suspect that this is the same approach many of you already take in your daily roles when identifying threats vs. benign activity, choosing your pivots in hunting, or deciding the priorities in device replacement. It’s a natural direction for the intellectually curious, so be kind, but ungovernable.
“The future of intelligence must be about search, while the future of ignorance must be about the inability to evaluate information.” ― Patricia Lockwood, No One Is Talking About This
Cisco Talos has recently discovered a commodity BadIIS malware variant fueling a thriving malware-as-a-service (MaaS) ecosystem for Chinese-speaking cybercrime groups. Identifiable by its embedded “demo.pdb” strings, this toolset boasts a multi-year development cycle complete with builder tools and persistence mechanisms. Threat actors are leveraging this robust framework to easily execute malicious search engine optimization (SEO) fraud, hijack server content, and redirect traffic to illicit sites.
This is a highly active, commercially driven malware ecosystem. The author constantly pushes rapid updates to introduce new features and actively evade specific security vendors, making it a persistent headache for defenders. Because this BadIISvariant is sold as a commodity tool, it lowers the barrier to entry for cybercriminals, leading to widespread attacks that silently hijack server traffic without triggering obvious alarms.
Defenders should actively monitor IIS environments for unauthorized traffic redirection, unexpected reverse proxying, or sudden spikes in “503 Service Unavailable” errors. Threat hunting efforts should also target the distinct “demo.pdb” strings and associated Chinese-language folder paths within IIS binaries. Ensure your endpoint detection solutions are updated to catch these reactive evasion tactics, and read the full blog for complete coverage and indicators of compromise (IOCs).
CISA exposes secrets, credentials in “private” repo
A researcher discovered a public GitHub repository belonging to CISA that contained 844MB of sensitive data, including plain-text passwords, authentication tokens, and other secrets. (Dark Reading)
NYC Health + Hospitals says hackers stole medical data and fingerprints, affecting at least 1.8 million people
The breach is particularly sensitive because hackers stole biometric information, including fingerprints and palm prints, which affected individuals have for life and cannot replace. (TechCrunch)
Bug bounty businesses bombarded with AI slop
Companies that pay hackers to find flaws in their software are being inundated with low-quality (often false) reports generated by AI, forcing some to suspend the programs altogether. (Ars Technica)
Four OpenClaw flaws enable data theft, privilege escalation, and persistence
The vulnerabilities, collectively dubbed Claw Chain, can permit an attacker to establish a foothold, expose sensitive data, and plant backdoors. (The Hacker News)
New NGINX vulnerability allows remote attackers to trigger malicious code
A new vulnerability in NGINX JavaScript (njs) allows unauthenticated remote attackers to trigger a heap‑based buffer overflow that can lead to denial‑of‑service and, in some conditions, remote code execution in the NGINX worker process. (Cyber Security News)
TP-Link, Photoshop, OpenVPN, Norton VPN vulnerabilities
Talos’ Vulnerability Discovery & Research team recently disclosed eight vulnerabilities in TP-Link, and one each in Adobe Photoshop, OpenVPN, and Gen Digital’s Norton VPN. The vulnerabilities have been patched by their respective vendors.
Webinar: AI found the problem. Now what?
Experts from Talos and Cisco Security will examine how AI is changing the game for both defenders and well-resourced adversaries, and why the most persistent risks often remain rooted in unpatched legacy systems.
Breaking things to keep them safe with Philippe Laulheret
From his memorable experiment using a green onion to bypass a biometric fingerprint reader to his experience on the frontlines of cybersecurity, Philippe shares the journey that led him to vulnerability research.
SHA256: 9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507
MD5: 2915b3f8b703eb744fc54c81f4a9c67f
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507
Example Filename: VID001.exe
Detection Name: Win.Worm.Coinminer::1201**
SHA256: d87e8d9d43758ce67a8052cb2334b99cc24f9b0437ee44815f360be0b22d835a
MD5: 362498c3e71eeaa066a67e4a3f981d1c
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=d87e8d9d43758ce67a8052cb2334b99cc24f9b0437ee44815f360be0b22d835a
Example Filename: TunMirror.exe
Detection Name: PUA.Win.Tool.Tunmirror::1201
SHA256: 9896a6fcb9bb5ac1ec5297b4a65be3f647589adf7c37b45f3f7466decd6a4a7f
MD5: 38de5b216c33833af710e88f7f64fc98
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=9896a6fcb9bb5ac1ec5297b4a65be3f647589adf7c37b45f3f7466decd6a4a7f
Example Filename: SECOH-QAD.exe
Detection Name: Win.Tool.Procpatcher::1201
SHA256: acd55c44b8b0d66d66defed85ca18082c092f048d3621da827fce593305c11fd
MD5: 0f03f72a92aef6d63eb74e73f8ac201d
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=acd55c44b8b0d66d66defed85ca18082c092f048d3621da827fce593305c11fd
Example Filename: KMSSS.exe
Detection Name: PUA.Win.Tool.Hackkms::1201
SHA256: 96fa6a7714670823c83099ea01d24d6d3ae8fef027f01a4ddac14f123b1c9974
MD5: aac3165ece2959f39ff98334618d10d9
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=96fa6a7714670823c83099ea01d24d6d3ae8fef027f01a4ddac14f123b1c9974
Example Filename: d4aa3e7010220ad1b458fac17039c274_63_Exe.exe
Detection Name: W32.Injector:Gen.21ie.1201
Cisco Talos Blog – Read More
ESET researchers describe new tools and techniques that the Webworm APT group recently added to its arsenal
WeLiveSecurity – Read More
We’ve written time and again about how QR codes are used in phishing schemes. Our secure email gateway solution even includes technology to read these codes — not just from emails, but also from attachments — and check the embedded links. Yet, attackers haven’t given up on trying to send QR codes to their victims. Lately, we’ve increasingly seen them use ASCII art for this purpose — images composed of characters. This seems particularly ironic considering that phishers once tried to evade link scanning by hiding links in images, and now they’re trying to dodge image scanning by going back to text. But with a few twists.
It’s hard to believe today, but there was a time when computers couldn’t display graphics. Consequently, the very first computer images were constructed from text characters. Following the adoption of the standard in 1963, characters from the ASCII (American Standard Code for Information Interchange) set were used for this type of artwork to ensure that images looked the same across different computers. Over time, other text symbols (for example, from the extended Unicode set) began to be used to create images, but the name “ASCII graphics” remained the term used to describe this art form as a whole. There were serious artists working in this medium, the earliest websites were designed with ASCII art, and even the first computer pornography was rendered with text characters.
As image display technology evolved, ASCII art began to fall out of fashion. It saw a major resurgence in the 2000s during the heyday of email spam. Back then, spammers primarily used it because it allowed them to disguise blatant spam keywords that could trigger mail filters, while also placing less load on mail servers than images. Additionally, since many users paid for volume of internet traffic at the time, they often disabled image loading in their email clients. Naturally, at that time, we augmented our email security solutions with technology specifically designed to block ASCII art.
Now, ASCII art has been rediscovered — this time by those looking to bypass technology that recognizes QR codes within images.
Here’s a recent example. The pretext itself is pretty run-of-the-mill: someone has supposedly sent to victim a confidential document via DocuSign, but to open it the recipient needs to scan the QR code in the email to visit a website and enter corporate login credentials.
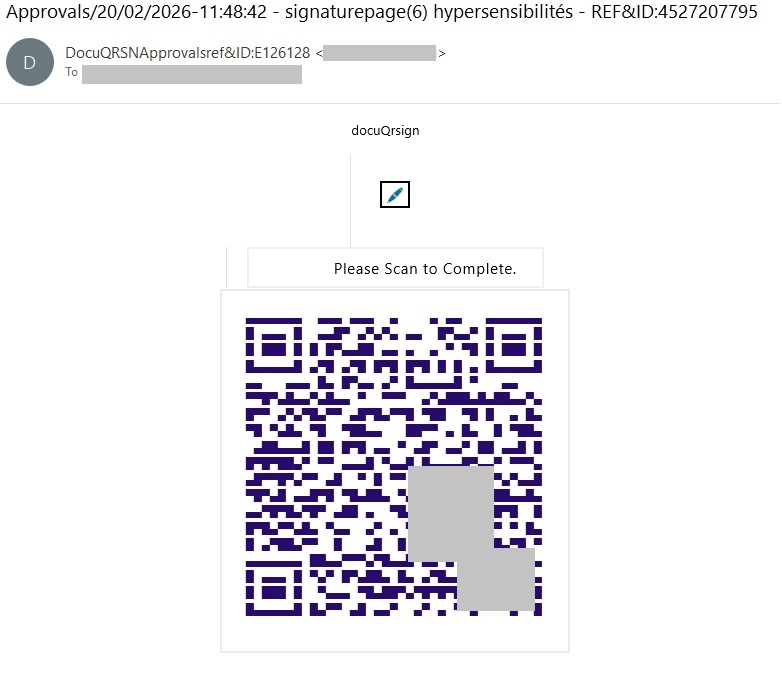
A QR code rendered with unicode characters. We’ve blurred out a portion of the code to prevent the malicious link from being scanned.
Admittedly, the code looks weird. This is primarily because it’s drawn piece-by-piece in pseudo-graphic elements, and even the gaps between the lines can be seen. In reality, there’s no actual image in the e-mail message code; the QR code looks something like this behind the scenes:
As a result, link scanners can’t see the link, and image analysis tools can’t find the URL hidden inside the QR code, so the attackers assume the phishing email is going to reach the victim just fine. Spoiler alert: no, we haven’t forgotten how to block ASCII art.
In theory, there are situations where using a QR code makes sense. It’s a fairly convenient way to share contacts, a link to a mobile app, a map location, or a configuration. In other words, it works well whenever information needs to be delivered specifically to the recipient’s mobile device.
However, someone using a QR code to make you enter corporate credentials on a mobile device is an instant red flag. And when that QR code is generated with ASCII art, it’s clearly a phishing attempt or an effort to lure you to a malicious URL. This trick can only have one purpose — an attempt to bypass security controls.
To prevent phishing emails — whether containing ASCII art or not — from ever reaching employee inboxes, we recommend using a secure email gateway with advanced anti-phishing capabilities. As an additional layer of defense, install security solutions on all endpoints used to access the internet.
Additionally, we recommend regular security awareness training to educate employees on modern phishing tactics. Specifically, to explain that ASCII art in modern emails can be a telltale sign of an attempted phishing attack.
Kaspersky official blog – Read More
Netflix, Apple TV+, Disney+, Hulu, Amazon Prime, YouTube Premium… The average law-abiding family today pays for five to 10 subscriptions just to watch their shows of choice, with the monthly bill easily crossing the hundred-dollar mark. It’s no surprise, then, that social media and online marketplaces are seeing a surge in demand for the “magic boxes” that popped up at the end of 2025: Android-powered TV boxes that promise to unlock thousands of channels and every streaming service subscription-free for a one-time purchase.
Ads for these devices are flooding TikTok and Instagram: smiling influencers unbox the SuperBoxes, plug them into a TV, and browse endlessly through channels. It looks like the ultimate life hack against subscription fatigue, right? In reality, it’s one of the easiest ways to invite a botnet into your home network.
A promotional video on TikTok explaining how great it is when the cheese is free you can just go ahead and cancel all your subscriptions
Stories about malicious TV boxes have surfaced before, but right now, their marketing has reached a truly alarming scale.
At the end of 2025, analysts examined several models of the popular SuperBox device available from major retail stores and online marketplaces. The findings were deeply concerning: immediately upon powering up, the devices began pinging the servers of the Chinese messaging app Tencent QQ, as well as the Grass proxy service — effectively renting out the owner’s internet bandwidth to third parties.
Inside the firmware, researchers discovered applications completely uncharacteristic of a media player: a network scanner, a traffic analyzer, and tools for DNS hijacking. Consequently, the device not only streams pirated content but also scans the local network for other targets (including industrial SCADA interfaces), and stands ready to participate in DDoS attacks. The SuperBoxes were also found to contain folders with the telltale name “secondstage”, a textbook indication of multi-stage malware.
More recently, in April 2026, the Darknet Diaries podcast featured an interview with a security researcher known by the alias D3ada55, who shared plenty of intriguing details about these boxes — including the fact that they were still openly sold on major platforms like Amazon, Walmart, and Best Buy.
The SuperBox case is far from the only instance where Android devices have been turned into botnet nodes — or sold infected right out of the box. Here’s a look at the most recent cases:
All of these stories share the same origin: the Triada Trojan, first documented by our researchers back in 2016 and dubbed at the time “one of the most advanced mobile Trojans”. Over the past decade it has evolved from a standard piece of malware into a modular backdoor baked directly into firmware during manufacturing.
Manufacturers of cheap TV boxes cut corners on absolutely everything: Google Play Protect certification, firmware audits, and security updates. Many of these devices run on the Android Open Source Project without any security guarantees whatsoever. Somewhere along the supply chain — whether at the factory, through a middleman, or at a distributor — a backdoor gets injected into the firmware image. Our experts suspect that the manufacturer itself might not even be aware of the compromise.
The sheer scale of the infection turns millions of identical boxes into the perfect foundation for a botnet: every compromised device represents a unique IP address that can be rented out to anyone. Botnet operators like Kimwolf monetize this not only through distributed DDoS attacks but also by reselling the bandwidth of infected smart TVs and streaming boxes.
An infected TV box sits right in your living room, connected to your home Wi-Fi. That means it can see smartphones running banking apps, network-attached storage (NAS) units holding family archives, IP cameras, smart locks, work laptops, and any other the devices connected to your Wi-Fi network.
With this kind of beachhead inside your home network, an attacker can intercept unencrypted traffic, spoof DNS requests, scan ports, and hunt for vulnerabilities on neighboring devices. On top of that, they can use your IP address for fraudulent activity. As a result, in the best-case scenario, your IP will end up blacklisted, and legitimate services will start blocking you for suspicious activity; in the worst-case scenario, law enforcement could come knocking on your door.
You should be on alert if a device:
Want to know how else to protect your smart home devices? Read more in our related posts:
Kaspersky official blog – Read More
A complete decoupling from US technology is neither realistic nor necessary, but the changing environment does require nations and companies to reassess their relationships and dependencies
WeLiveSecurity – Read More

Cisco Talos’ Vulnerability Discovery & Research team recently disclosed eight vulnerabilities in TP-Link, and one each in Adobe Photoshop, OpenVPN, and Gen Digital’s Norton VPN.
The vulnerabilities mentioned in this blog post have been patched by their respective vendors, in adherence to Cisco’s third-party vulnerability disclosure policy, except the Norton VPN vulnerability, which was discovered in-use before a patch was available.
For Snort coverage that can detect the exploitation of these vulnerabilities, download the latest rule sets from Snort.org, and our latest Vulnerability Advisories are always posted on Talos Intelligence’s website.
Discovered by Lilith >_> of Cisco Talos.
The TP-Link Archer AX53 is a dual band gigabit Wi-Fi router. Talos has disclosed eight vulnerabilities, as follows:
TALOS-2025-2302 (CVE-2026-30814) is a stack-based buffer overflow vulnerability in the tmpServer opcode 0x436 functionality of Tp-Link AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted set of network packets can lead to arbitrary code execution. An attacker can send packets to trigger this vulnerability.
TALOS-2025-2303 (CVE-2026-30815) is an OS command injection vulnerability in the OpenVPN configuration restore script_security functionality of Tp-Link Archer AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted configuration value can lead to arbitrary command execution. An attacker can upload a malicious file to trigger this vulnerability.
TALOS-2025-2304 (CVE-2026-30816) is an external config control vulnerability in the OpenVPN configuration restore crt.sed functionality of Tp-Link Archer AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted configuration value can lead to arbitrary file reading. An attacker can upload a malicious file to trigger this vulnerability.
TALOS-2025-2305 (CVE-2026-30817) is an external config control vulnerability in the OpenVPN configuration restore route_up functionality of Tp-Link Archer AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted configuration value can lead to arbitrary file reading. An attacker can upload a malicious file to trigger this vulnerability.
TALOS-2025-2306 (CVE-2026-30818) is an OS command injection vulnerability exists in the dnsmasq configuration restore dhcpscript functionality of Tp-Link Archer AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted configuration value can lead to arbitrary command execution. An attacker can upload a malicious file to trigger this vulnerability.
TALOS-2025-2307, TALOS-2025-2308, and TALOS-2025-2309 are OS command injection vulnerabilities in the OpenVPN configuration restore client_disconnect, client_connect, and route_up functionalities of Tp-Link Archer AX53 v1.0 1.3.1 Build 20241120 rel.54901(5553). A specially crafted configuration value can lead to arbitrary command execution. An attacker can upload a malicious file to trigger this vulnerability.
Discovered by KPC of Cisco Talos.
Adobe Photoshop is a popular digital photo manipulation and illustration program with a wide array of features for personal and business use cases.
TALOS-2025-2274 (CVE-2026-34632) is a privilege escalation vulnerability in the installation process of Adobe Photoshop via the Microsoft Store. The vulnerable version of the installer is Photoshop_Set-Up.exe 2.11.0.30. A low-privilege user can replace files during the installation process, which may result in elevation of privileges.
Discovered by Emma Reuter of Cisco ASIG.
OpenVPN is an open source SSL VPN with remote access, site-to-site VPNs, WiFi security, enterprise load balancing, failover, and granular access control features available.
TALOS-2026-2381 (CVE-2026-35058) is a reachable assertion vulnerability in the TLS Crypt v2 Client Key Extraction functionality of OpenVPN 2.6.x and 2.8_git. A specially crafted network packet can lead to a denial of service. An attacker can send a sequence of malicious packets to trigger this vulnerability.
Discovered by KPC of Cisco Talos.
Gen Digital’s Norton VPN client is a proprietary tool for private proxy network information exchange.
TALOS-2025-2276 (CVE-2025-58074) is a privilege escalation vulnerability in the installation process of Norton VPN via the Microsoft Store. A low-privilege user can replace files during the installation process, which may result in deletion of arbitrary files, possibly leading to elevation of privileges.
Cisco Talos Blog – Read More