The top-five funny school, social media, and IoT hacks | Kaspersky official blog
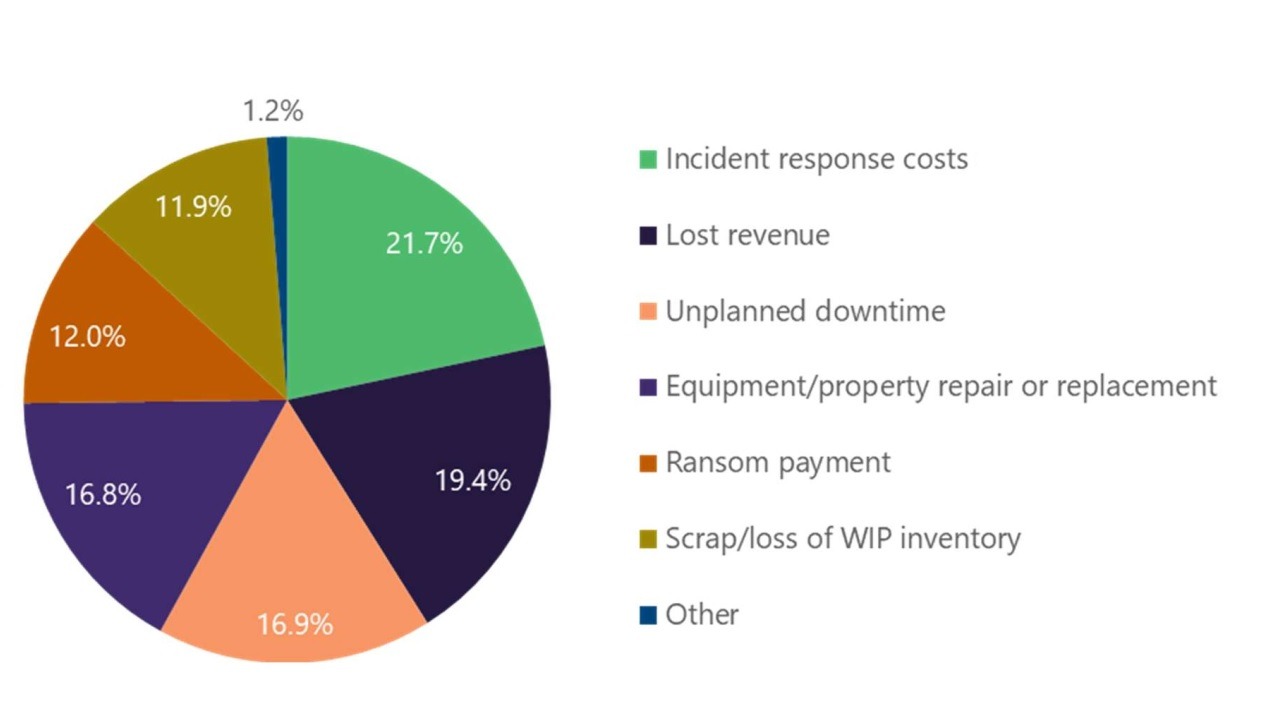
On this here blog of ours we constantly write about all sorts of cyberattacks and their devastating effects — from cryptocurrency theft to personal data leaks. Yet there’s a different category of high-profile hacks: those where the hackers aren’t after money, but instead pull off silly stunts that are mostly harmless enough and just for fun (though some (one in particular — the Ecovacs hack, below) could be more serious than others). Today, we tell you about five of these and discuss the lessons we can learn from them…
“They’re everywhere!” When traffic lights talk to you in the voices of Zuckerberg and Musk
In the spring of 2025, unknown individuals hacked crosswalk buttons on traffic lights across Silicon Valley. These audio-enabled buttons are widely installed on pedestrian signals across the United States. As you might expect, they’re designed for people with visual impairments: their main purpose is to play voice messages that help pedestrians who can’t see well understand when it’s safe to cross the road.
The unknown individuals replaced the standard voice messages on crosswalk buttons in several Silicon Valley towns with their own — featuring AI-generated imitations of the ubiquitous tech-billionaires Mark Zuckerberg and Elon Musk. Videos recorded by local residents show the hacked buttons playing the messages.
In a voice imitating Mark Zuckerberg: “It’s normal to feel uncomfortable or even violated, as we forcefully insert AI into every facet of your conscious experience. I just want to assure you, you don’t need to worry because there’s absolutely nothing you can do to stop it.”
In a voice imitating Elon Musk: “You know, they say money can’t buy happiness… I guess that’s true. God knows I’ve tried. But it can buy a Cybertruck and that’s pretty sick, right? F***, I’m so alone.”
Another message in a simulated Musk voice: “You know, people keep saying cancer is bad, but have you tried being a cancer? It’s f****** awesome. Call me Elonoma. Heh-heh-heh.”
The billionaires’ voices were clearly AI-generated, but exactly how the hackers managed to breach the traffic light audio buttons remains unknown. Security experts have noted, however, that default passwords are often used when connecting these kinds of buttons, and nobody bothers to change them after installation.
It looks like no one was hurt by the prank – except maybe the billionaires’ pride.
In Illinois, students learn a key lesson: never forget about Rick
On the last Friday of the 2021 school year, all the TVs and projectors in classrooms across six schools in Cook County, Illinois, turned on by themselves. A message appeared on the screens: “Please remain where you are. An important announcement will be made shortly.” A five-minute countdown timer was displayed below the unsettling message…
Five minutes later, 500 screens simultaneously started showing the famous Rick Astley video for Never Gonna Give You Up. Later that same day, the song played again over the schools’ public address systems.
The hackers behind this surprise pop… classic’s airing were four American students, and what they did was pull off one of the biggest Rickrolls in history that day. A Rickroll is a popular online prank where an unsuspecting user is sent a seemingly important or exciting link, only to be redirected to the video for English singer Rick Astley’s 1987 hit, Never Gonna Give You Up. Rickrolling achieved cult status back in 2007 after spreading on the 4chan imageboard.
Let’s get back to the four students. Their massive Rickroll was a hi-tech twist on a classic American tradition known as the senior prank: basically, a good-natured prank pulled by high-school, college, or university seniors before graduation.
However, the four Illinois students clearly took it to a new level. To pull off their Rickroll, they exploited fairly basic vulnerabilities in the school’s infrastructure. For example, the pranksters gained access to the system controlling hundreds of projectors and TVs across the entire school district because the default usernames and passwords hadn’t been changed after setup.
Similarly, the students were able to log into the schools’ audio public address systems. The person who originally configured the PAs diligently changed the default system password to the one provided as an example in the user manual, which of course was available online. While they were at it, the hacking team discovered an administrator account with “password” used as the password.
It’s worth highlighting just how responsibly the hackers approached the whole operation. Before carrying out the Rickroll, the prankster team prepared a detailed 26-page report, which they sent to the school administrators immediately after the incident. In it, the students thoroughly described their actions and provided recommendations for improving the schools’ cybersecurity. Additionally, once the Rickroll was over, the script they wrote restored the school systems back to their original state.
We always knew: the rise of the machines would begin with robot vacuums
Last year, reports surfaced online about a series of hacks targeting Chinese-made Ecovacs Deebot X2 robot vacuums in cities across the United States. Pranksters assumed control of the robots’ movements and shouted expletives through the built-in speakers. Additionally, they could spy on the owners through the integrated cameras.
The story seemingly had its beginnings at the DEF CON 32 hacker conference, where cybersecurity researchers Dennis Giese and Braelynn Luedtke presented their talk, Reverse engineering and hacking Ecovacs robots. The presentation described vulnerabilities they’d discovered in Ecovacs robot vacuums and lawnmowers, as well as methods for exploiting them. As part of their study, the researchers were able to gain remote access to the built-in microphones and cameras and control the vacuums’ movements. We previously covered their work in detail in our post Ecovacs robot vacuums get hacked.
(By the way, during their presentation at DEF CON, Giese and Luedtke themselves became the target of a hacker prank: a member of the audience managed to take control of the presenter’s clicker and spent several minutes messing with the speakers by randomly flipping through their slides.)
Giese and Luedtke reported their findings to the vendor in a responsible manner. Ecovacs engineers attempted to patch the vulnerabilities, but didn’t have much luck. Several months after the report went out, unknown tech enthusiasts, likely inspired by the study, were able to recreate the techniques described in it to execute a series of attacks on other people’s robot vacuums. For example, in one such attack in California, a robot chased the owner’s dog around the house while shouting obscenities.
The exact number of victims from this series of hacks remains unknown, as it’s plausible that the pranksters didn’t always make their presence obvious — they might have simply observed the vacuum owners’ lives. That, clearly, would have been a very serious infringement of those owners’ privacy – and could in no way be described as mere “fun and games”; neither could this: what if Ecovacs lawnmowers are next?
Lizard Squad “breaking free”: a defacement free redesign of Lenovo’s website
Here’s another playful attack by teenagers, this time targeting Lenovo. A decade ago, the computer manufacturer’s website was hacked. Visitors were redirected to a slideshow featuring photos of bored-looking adolescents, presumably the hackers themselves, all set to the song Breaking Free from Disney’s High School Musical.
Clicking on the slideshow would lead users to the hacking group Lizard Squad’s account on X, which was still known as Twitter at the time. The hackers left a jab at the webmasters in the source code: “The new and improved rebranded Lenovo website featuring Ryan King and Rory Andrew Godfrey”. These two individuals had previously been linked to Lizard Squad.
The attack was orchestrated via DNS hijacking. The hackers altered the DNS records for lenovo.com, causing all users attempting to reach the official company website to be automatically redirected to a fake page controlled by the pranksters.
The attack was apparently a protest against what was seen as the computer vendor’s lax attitude toward security and user protection. Shortly before the defacement, it was revealed that Lenovo had been selling laptops preloaded with Superfish malware. This made users who purchased infected devices potentially vulnerable to data interception and man-in-the-middle attacks. Thus, the hack seems kind of wrong, but at the same time feels justified.
Bring back 2013, when Twitter accounts were hacked for mischief — not crypto scams
These days, when the X account of a high-profile individual or major company gets hacked, it almost invariably leads to some kind of cryptocurrency scam. But it wasn’t always this way. Just a decade ago, popular accounts on what was then still known as Twitter were more often hijacked for giggles than for illicit financial gain.
Take February 2013, for example. Unknown hackers breached Burger King’s Twitter account to post this gem: “We just got sold to McDonalds! Look for McDonalds in a hood near you.”
On top of that, Burger King’s profile picture was swapped out for the McDonald’s logo, and their bio read: “Just got sold to McDonalds because the whopper flopped.” The bio also included the misspelled line “FREDOM IS FAILURE” and a dead link to a press release.
For about an hour, the attackers posted increasingly outrageous messages before Twitter finally suspended the account. Interestingly, Burger King’s arch-rival, McDonald’s, tweeted a message of support — while making sure to clarify they had nothing to do with the breach.
Fast-forward to August 2017, which was when the Ourmine hacking outfit targeted the Twitter account of soccer giant Real Madrid. The hackers used the club’s account to announce that none other than Lionel Messi, who then played for Real Madrid’s fiercest rival, FC Barcelona, was transferring to Real Madrid.
The post quickly racked up 2800 likes and 3100 retweets. Ourmine also posted a series of tweets claiming responsibility for the hack, with one declaring, “Internet security is s*** and we proved that.” It’s hard to argue with that.
A takeaway from the hacks: protect your password from the start
Perhaps the most crucial lesson to learn from these online shenanigans is this: using weak — or even worse, default — passwords is a surefire way to hand control of your device, account, or website to internet pranksters… if you’re lucky. Weak passwords were what tripped up city infrastructure and school administrators, and it’s highly likely that the Twitter account hacks were also linked to a careless approach to password policies.
This blog has frequently discussed how to create strong passwords. But to wrap things up, let’s reiterate a few basic rules of password hygiene:
- Passwords should be at least 16 characters long, or even longer if the website allows it.
- When creating a password, it’s good practice to mix uppercase and lowercase letters, numbers, and special characters.
- It’s best to avoid easily guessable things like common words or dates in your password. And you definitely shouldn’t use the word “password”.
- Ideally, your password should be a random combination of characters.
- Create a new, unique password for each website.
Of course, any user today signs up for dozens, if not hundreds, of online services. So, remembering long and unique passwords for each one isn’t feasible. That’s where Kaspersky Password Manager can help you manage this and protect yourself not just from pranks, but from far more serious consequences.
Additionally, the app automatically checks all your passwords for uniqueness, and helps you create truly strong and random combinations of characters. So, when using Kaspersky Password Manager, you don’t need to keep all those complex rules in mind — the password manager does it all for you. Beyond passwords, Kaspersky Password Manager can store and sync two-factor authentication tokens and passkeys. We recently thoroughly explored this new passwordless technology for accessing websites and services in our complete guide to using passkeys in 2025.
Kaspersky official blog – Read More