Enterprise Plan: Boost SOC Performance, Reduce Business Risks with ANY.RUN
Editor’s note: The current article was originally published on April 10, 2024, and updated on July 15, 2025.
Modern cybersecurity teams face growing pressure: more threats, tighter SLAs, and less time to investigate. The difference between fast containment and a damaging breach often comes down to visibility, collaboration, and control.
ANY.RUN’s Enterprise plan is a complete malware analysis plan built for organizations that can’t afford to miss a threat. It combines interactive sandboxing, robust privacy settings, centralized team management, and flexible integrations.
It provides SOCs with the full picture of every threat, helping them respond quickly and accurately, no matter the size or sector of your organization.
Why Leading Security Teams Choose ANY.RUN’s Enterprise Plan
Enterprise gives security teams all the essentials in a single, unified solution—from threat visibility and secure collaboration to automation and ecosystem integration. With a setup designed to fit into existing workflows, it removes bottlenecks and accelerates decision-making at every stage of investigation.
The results speak for themselves:
- 90% of companies report higher detection rates after adopting ANY.RUN
- 95% say they resolve investigations significantly faster
- 80% of Fortune 100 companies rely on ANY.RUN in their security operations
- Trusted by 15,000+ organizations across finance, telecom, retail, government, and healthcare
ANY.RUN helps teams cut through alert noise, validate threats faster, and stay ahead of what’s coming next.
 Enterprise Plan:
Enterprise Plan:- Is for SOC teams and MSSPs
- Offers all features, including teamwork and Automated Interactivity
- Available for integration via API and SDK
- Covers 5 or more seats
Real-World Success Stories: How Security Teams Win with ANY.RUN Enterprise
ANY.RUN’s Enterprise plan is trusted by leading organizations to solve real problems, streamline operations, and stay ahead of threats.
From managed security providers to financial institutions, more than 15,000 organizations around the world use Enterprise to improve visibility, accelerate response, and strengthen their security posture.
Expertware Cuts Investigation Time by 50% with ANY.RUN Enterprise
Expertware, a leading European IT consultancy, needed to accelerate investigations, reduce manual overhead, and deliver faster results to clients. With Enterprise, they achieved a 50% reduction in malware investigation turnaround time.
By replacing time-consuming manual setups with interactive sandboxing, Expertware improved visibility into complex threats, streamlined collaboration across their SOC, and scaled operations without adding overhead.
Besides the faster investigation, Expertware achieved:
- Greater SOC efficiency: Interactive analysis and shared reports improved collaboration and reduced rework
- Deeper visibility: Full insight into multi-stage and fileless attacks, from macro execution to C2 communication
- Stronger client outcomes: Faster, clearer reporting helps clients respond before threats escalate
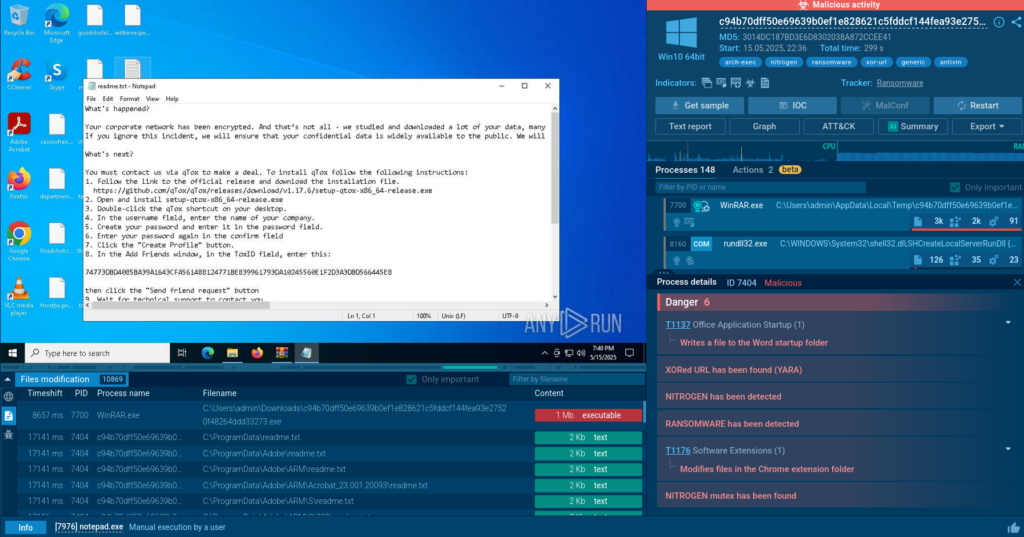
Investment Bank Improves SOC Efficiency and Stops Ransomware with ANY.RUN Enterprise
A Brussels-based investment bank adopted ANY.RUN’s Enterprise plan to overhaul its overloaded cybersecurity operations. Facing constant phishing and ransomware threats, their lean SOC team needed a solution that could speed up investigations, enhance visibility, and reduce manual work.
With ANY.RUN, they replaced slow, manual triage processes with interactive sandboxing and automated analysis, allowing them to detect and contain attacks faster, without adding headcount.
The combination of speed and knowledge allowed us to identify and prevent cyber attacks better than ever before.
Head of Cybersecurity, EU-based investment bank
Key improvements after adopting the Enterprise plan:
- Faster triage and response: Analysts process alerts twice as fast using automated sandbox submissions and interactivity
- Smarter planning and decision-making: Deeper behavioral insights help the team prioritize threats more effectively
- Prevented major ransomware incident: A suspicious supplier email was detonated in the sandbox, revealing ransomware and saving the company from significant financial and reputational damage
ANY.RUN became a central part of their modernized SOC, delivering speed, visibility, and control without increasing complexity.
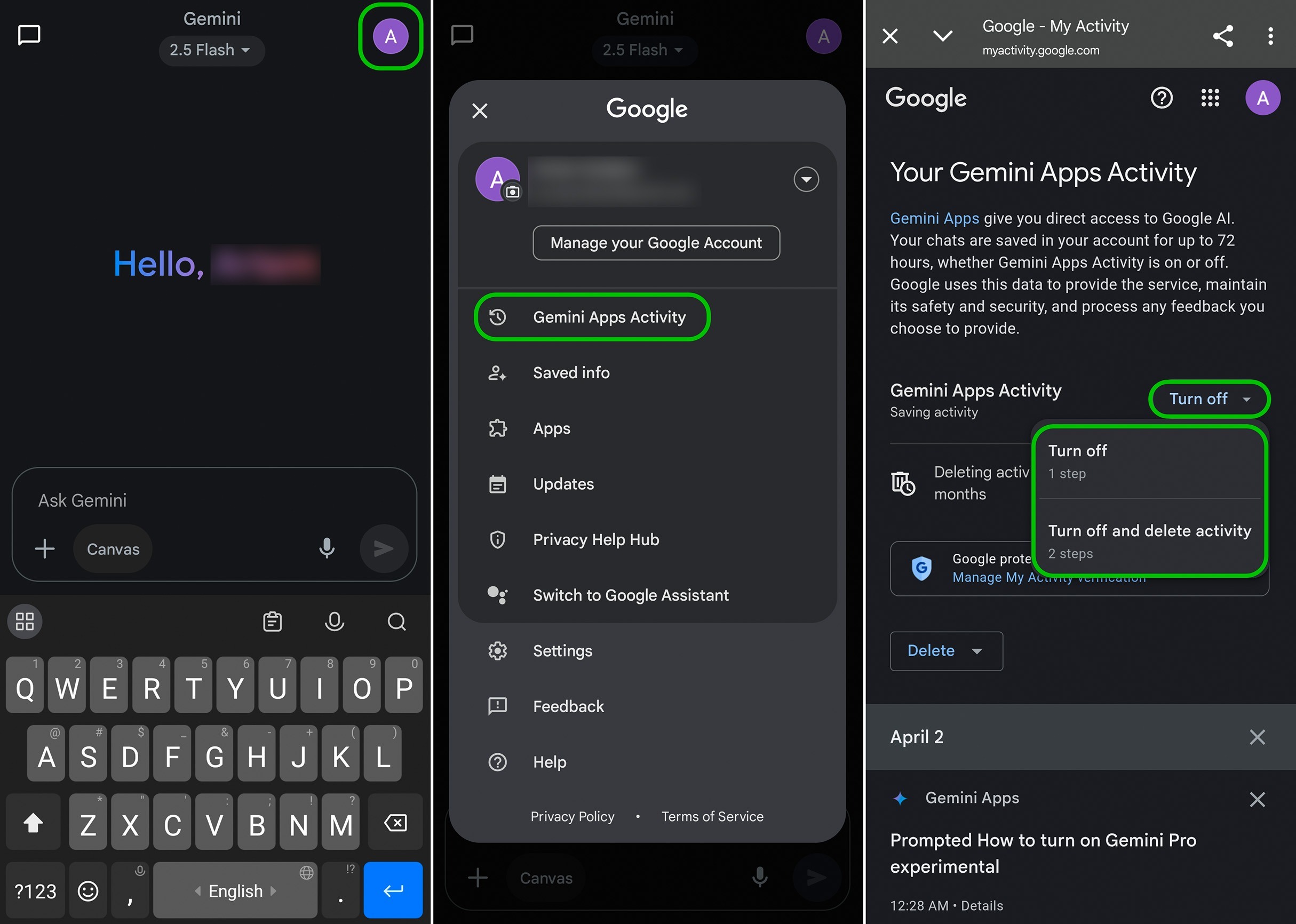
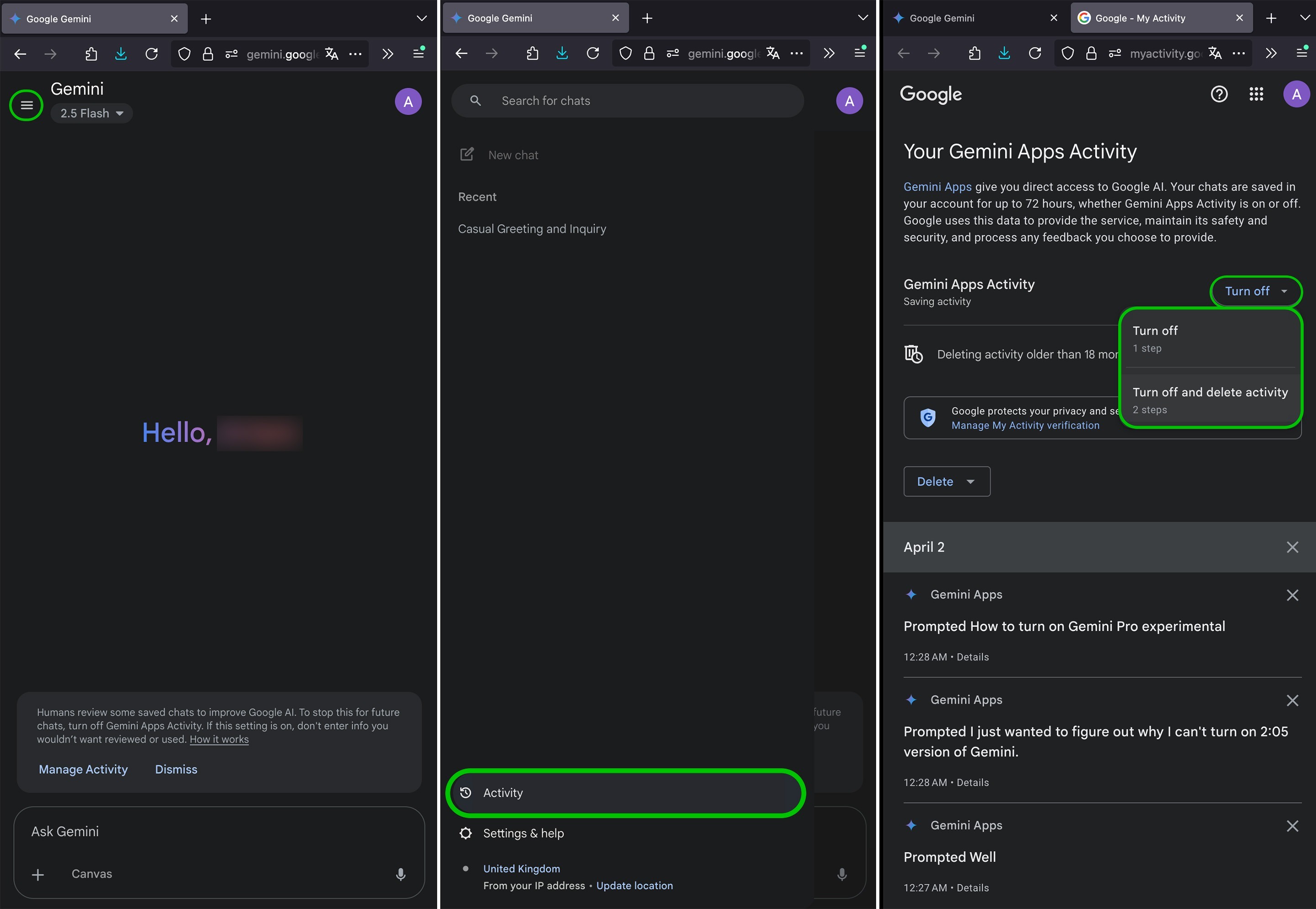
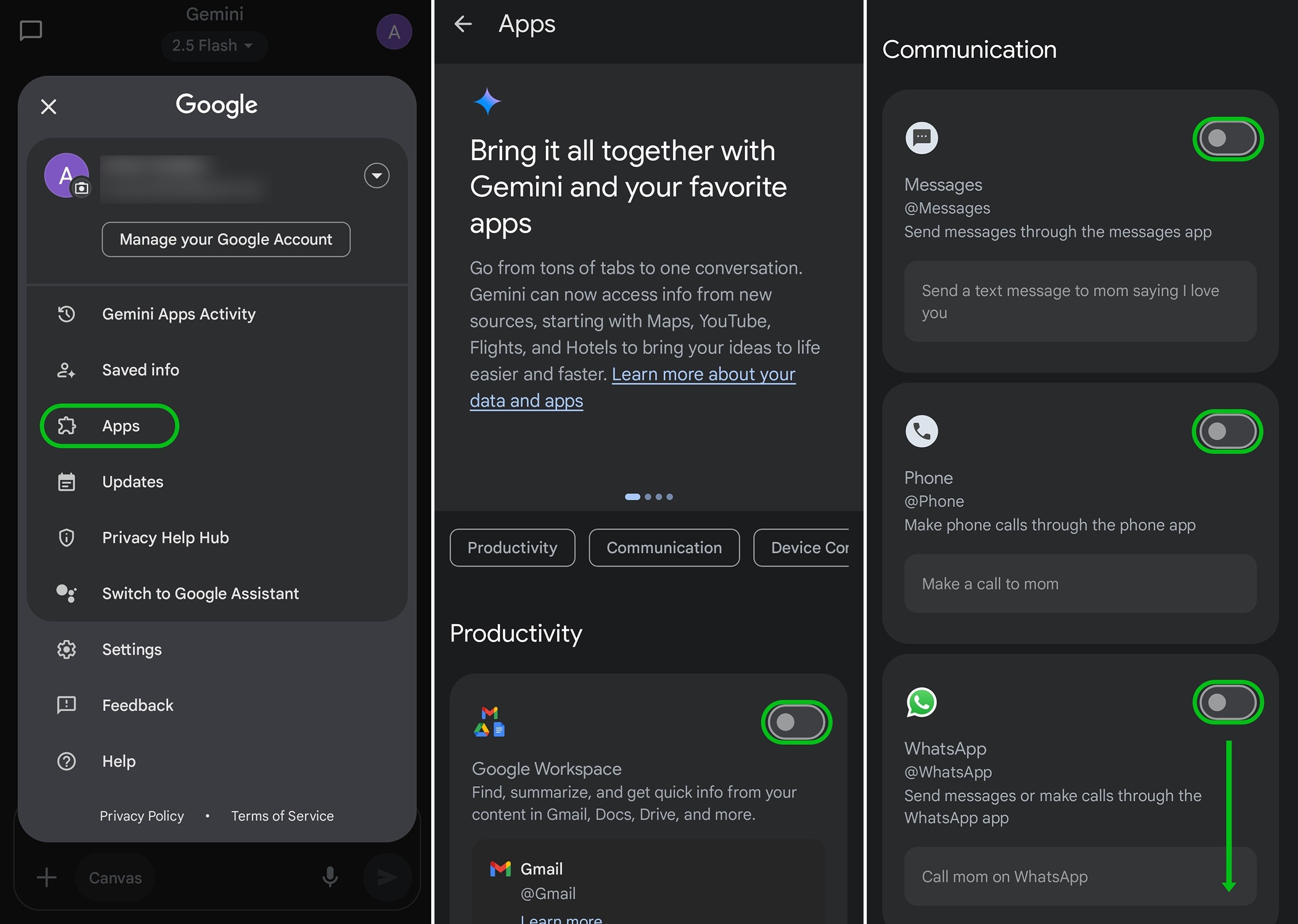
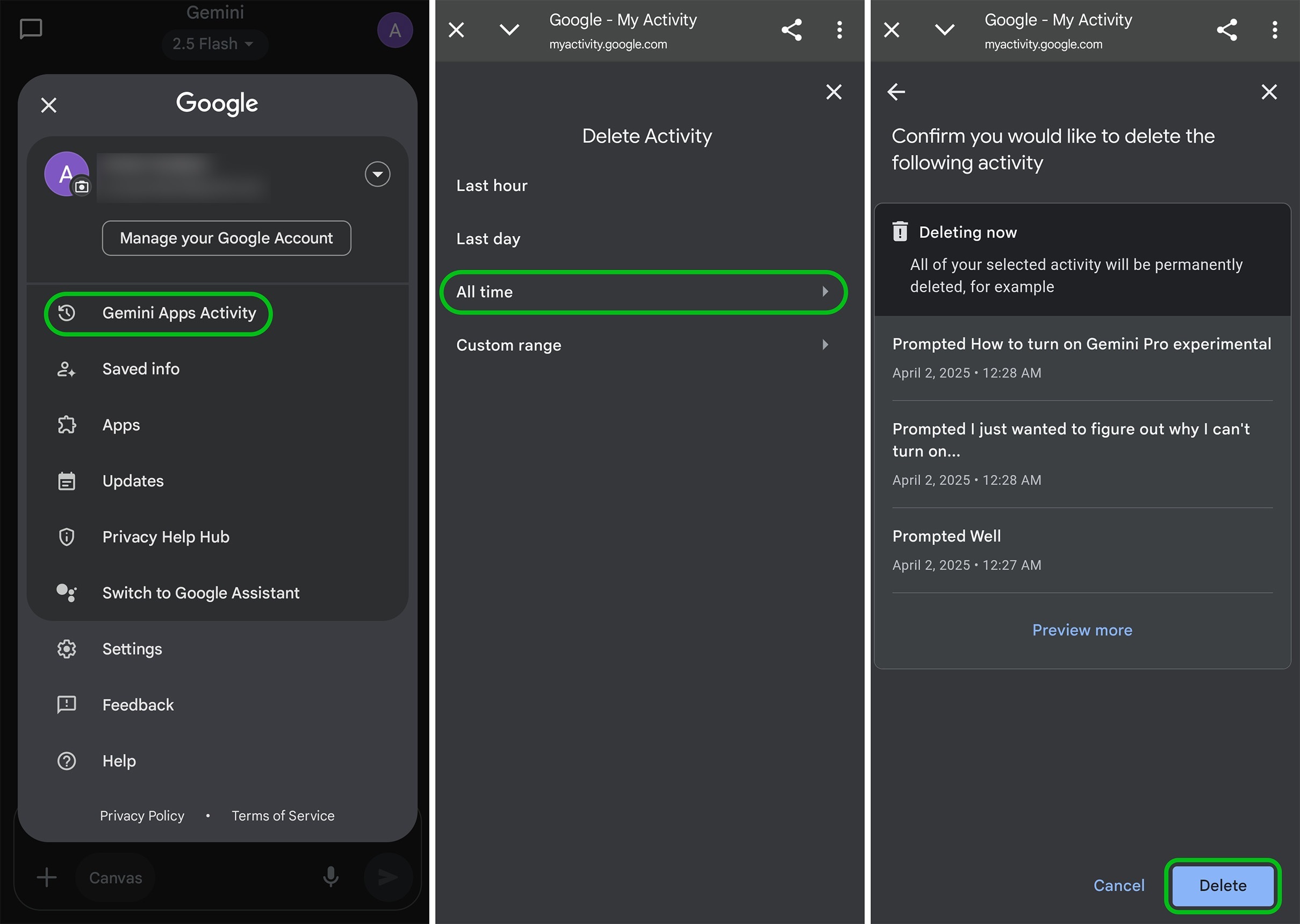
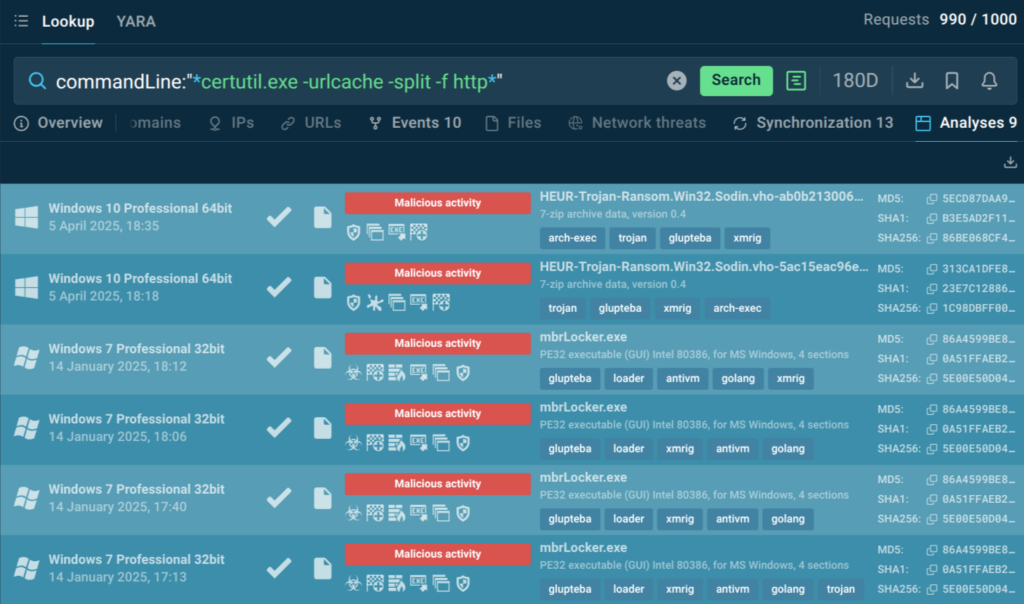
Privacy: Keep Investigations Secure and Under Control
In threat investigations, privacy plays an important role. A single public task launched by mistake can expose sensitive data, damage trust, or break compliance. The Enterprise plan helps your team avoid those risks with flexible private analysis options, role-based visibility controls, and secure access through SSO.
Flexible Private Analysis Quotas
Enterprise customers can choose the model that fits their team structure best:
- Unlimited private analyses per user with a per-user pricing model
- Unlimited users with a per-analysis pricing model
This flexibility makes sure your investigations stay private, without limiting your team’s ability to scale or collaborate.
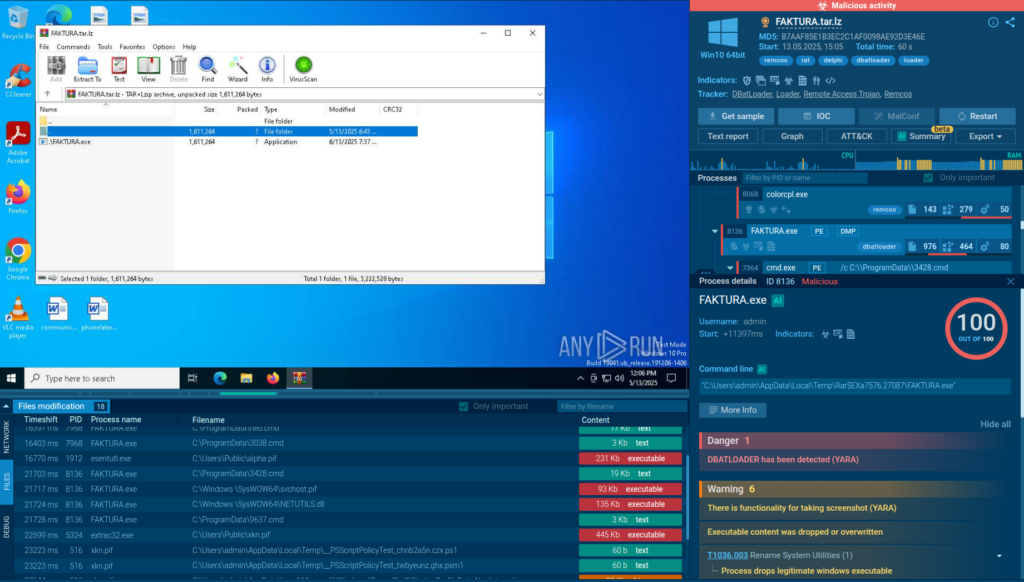
Granular Privacy Controls
You can control each user’s access to the sandbox, including the default privacy level of their analyses; whether tasks are visible only to the user, shared with the team, or accessible via a link. Team masters can define what analysts are allowed to share and ensure sensitive investigations aren’t exposed by mistake.
In large or distributed teams, one misconfigured setting can lead to accidental data leaks. Granular privacy controls help reduce that risk by enforcing visibility rules at the user level, keeping your analysis environment secure without slowing your team down.
Let us show you how ANY.RUN can help your SOC team – book a call with us 
Single Sign-On (SSO): Simpler Access, Stronger Control
For busy security teams, managing multiple logins can slow things down, and increase risk. With Single Sign-On (SSO) in the Enterprise plan, your team can log in to ANY.RUN using the same credentials they use across the rest of your organization.
That means:
- Fewer login issues and less time wasted on password resets
- Stronger access control, especially as your team grows
- Easier onboarding and offboarding for analysts and contractors
SSO helps your SOC stay efficient and secure, giving every team member fast, reliable access to the sandbox, without extra friction. It also reduces the chance of human error, making it easier to stay compliant with internal policies and external standards.
Automated Interactivity: Streamline Analysis for Faster Response
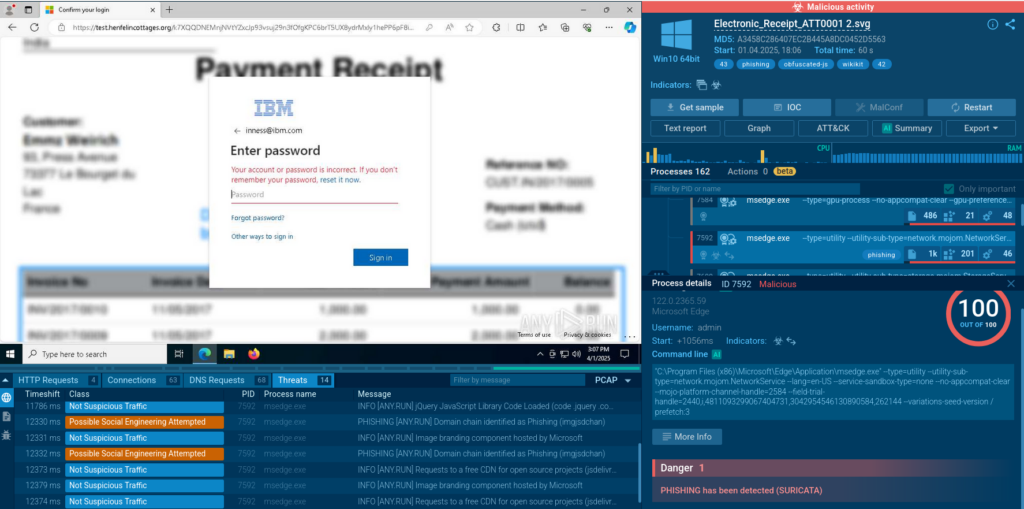
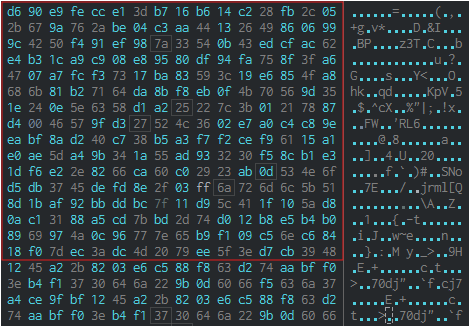
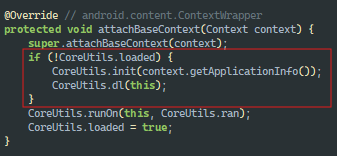
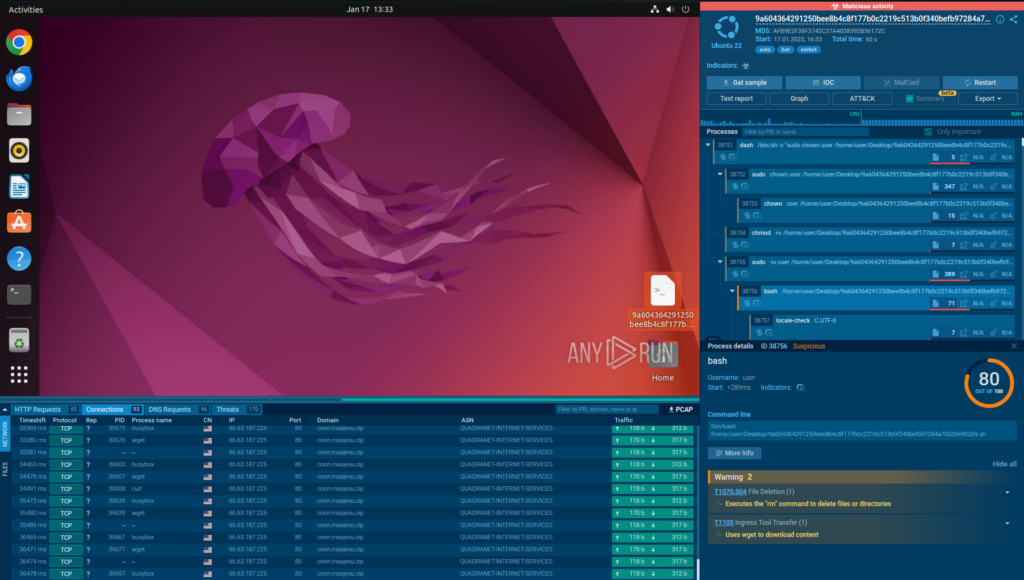
Automated Interactivity, powered by machine learning, enables security teams to automate file/URL analysis by letting the sandbox simulate human actions to outsmart evasion tactics like CAPTCHAs and redirects. Available exclusively in Enterprise plan, it gives a massive boost to SOC efficiency by automating detonation of attacks and accelerating threat detection.
It identifies and detonates malicious content, such as email attachments, payloads inside archives, URLs in QR codes. Thanks to this feature, your SOC team can reduce workload, improve the detection rate and alert processing capabilities, while focusing on critical incidents only.
This sandbox has provided features we didn’t have previously and helps to make the team more efficient
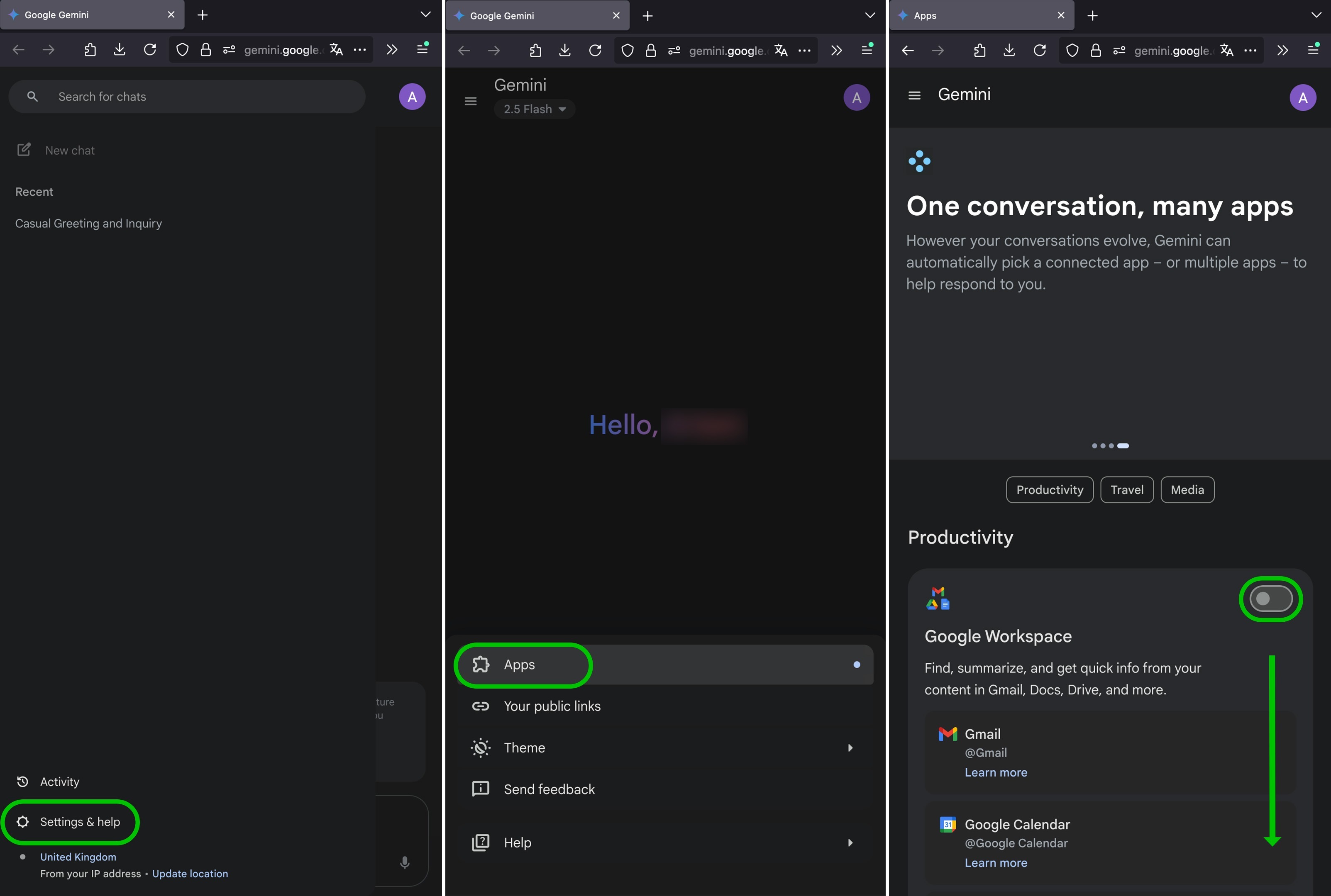
API/SDK: Integrate ANY.RUN for Faster SOC Workflows
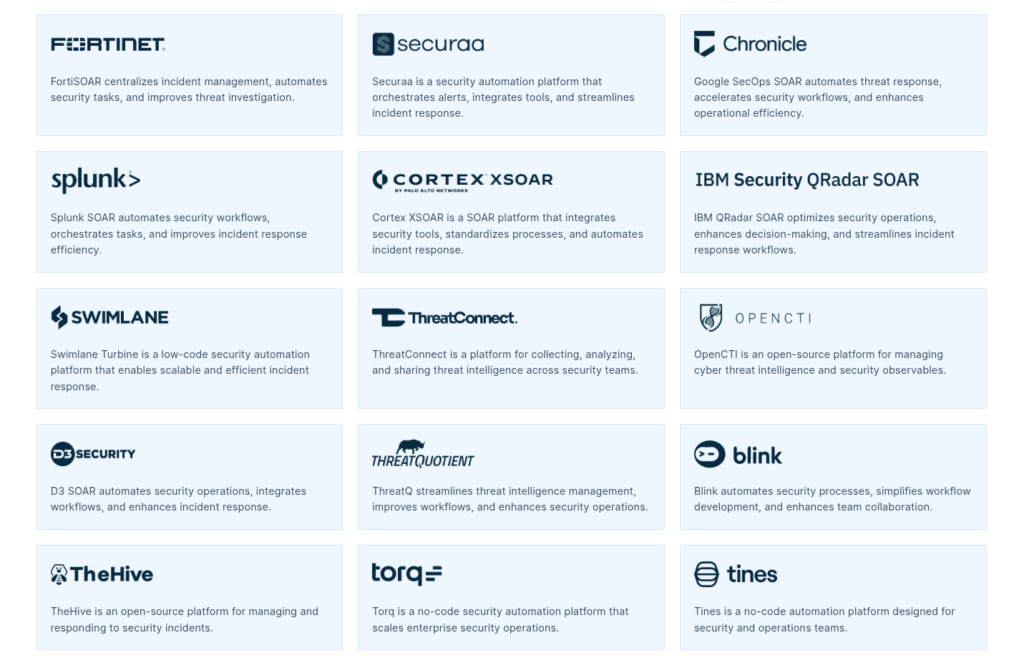
The Enterprise plan gives your team full access to API and SDK integrations, so you can embed ANY.RUN directly into your existing workflows, automate routine tasks, and enrich investigations with real-time behavioral data.
Whether you use a SIEM, SOAR, or case management platform, ANY.RUN connects seamlessly, helping analysts cut down on manual effort and focus on what matters most.
One of our latest integrations is with IBM QRadar SOAR, a popular platform for incident response. With ANY.RUN’s official app, teams can:
- Launch sandbox analyses directly from SOAR playbooks
- Enrich cases with fresh IOCs and behavioral insights
- Automate repetitive tasks to reduce Mean Time to Respond (MTTR)
Setup takes minutes; just plug in your API key and get started.
With integrations like this, ANY.RUN becomes a natural part of your security workflow, helping your team move faster, stay aligned, and act with greater precision.
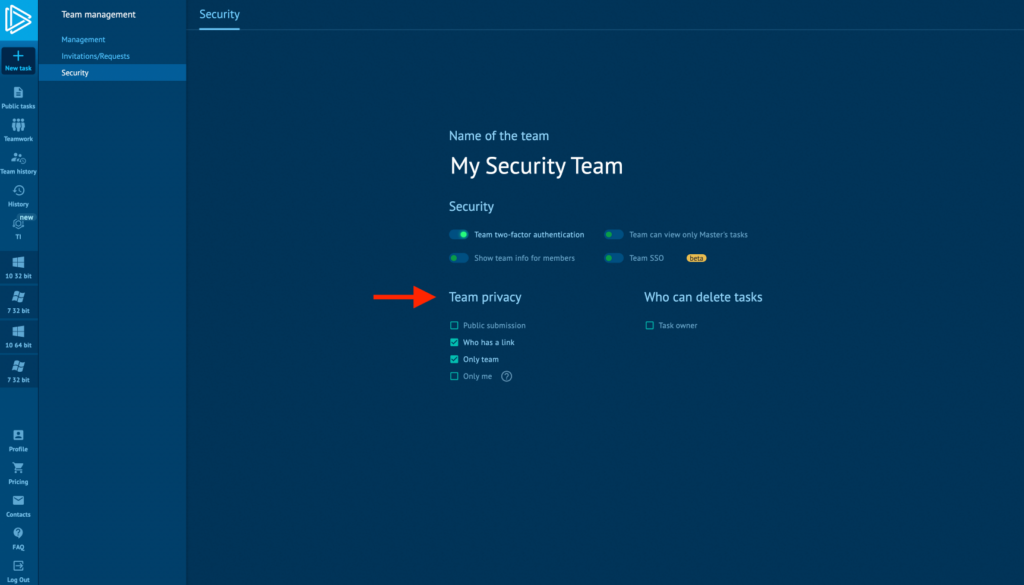
Teamwork: Smarter Collaboration for Analysts
Even the most advanced tools fall short when teams can’t work together effectively. In many SOCs, analysts work in silos, communication breaks down, and duplicated work or missed alerts slow down investigations.

The Teamwork feature in Enterprise makes collaboration seamless, whether your team sits in the same room or operates across time zones. Analysts can join a shared workspace, while team leads assign roles, track progress, and manage licenses, all from one central interface.
- Faster coordination across analysts, team leads, and managers
- Clear task ownership and role definitions to avoid confusion or rework
- Real-time supervision for team leads, without disrupting workflow
- Scalable team structure, ready to support fast-growing SOCs
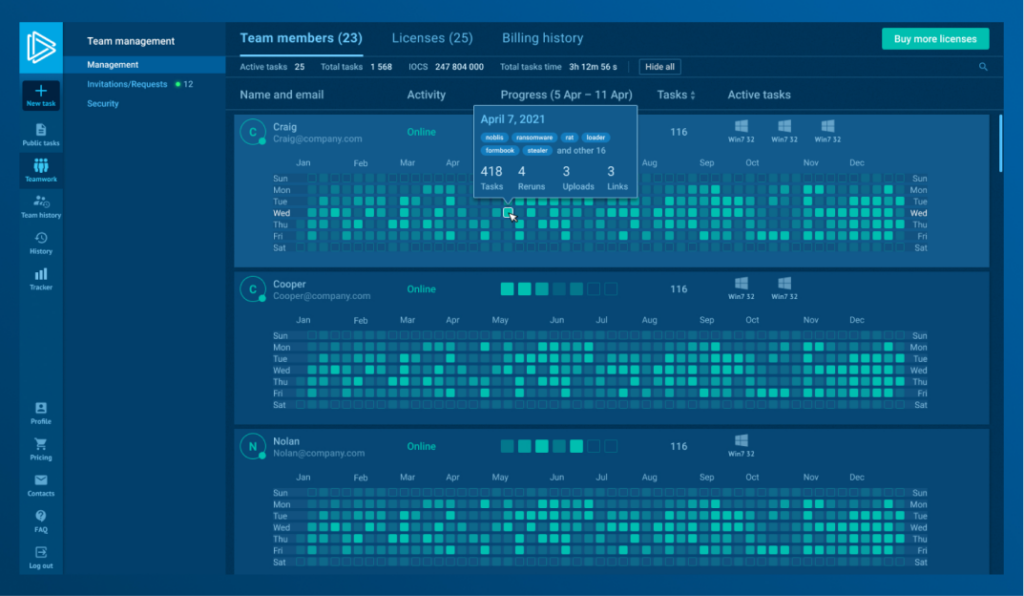
When every analyst knows what to focus on, and team leads can oversee without micromanaging, you reduce delays, avoid duplication, and build a stronger response process.
Other Enterprise-Grade Capabilities for Deeper, More Accurate Investigations
The Enterprise plan gives your analysts the technical depth and flexibility to run more realistic, multi-stage investigations and uncover even the most evasive threats.
- Ensure full sandbox coverage without feature limitations: Enterprise users get access to 100% of sandbox functionality, unlocking every detection layer and configuration option available.
- Investigate advanced malware without time pressure: With 1,200-second VM timeout, your team has the time needed to observe full execution chains, from initial dropper to final payload.
- Reveal location-based behavior and evasion techniques: Use residential proxy and locale selection to simulate real-world environments and detect malware that hides its behavior under generic settings.
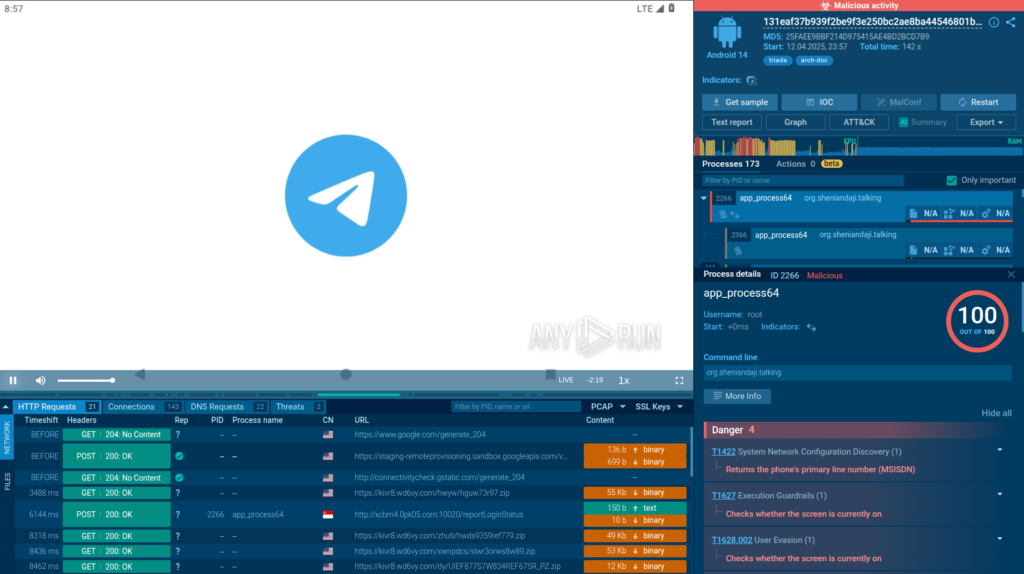
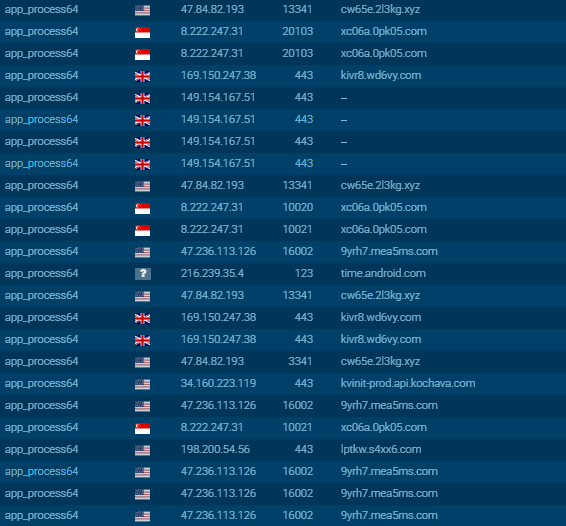
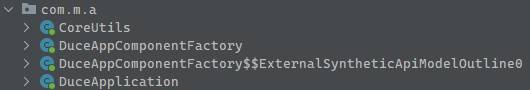
- Analyze threats across real-world environments: Run samples in Windows (11 64-bit, 10 32-bit, and Windows 10 64-bit for Developers, exclusive to Enterprise), Linux, and Android to detect OS-specific behavior and expand coverage across your attack surface.
- Uncover stealthy or delayed malicious actions: Rely on system process monitoring and reboot support to catch techniques that only activate during system events or over time.
- Enable external reporting and automation with precision: Export results using JSON and MISP formats, making it easier to integrate analysis findings into your internal tools or client reporting.
- Support managed services and external collaboration: Work with confidence using a commercial license, built for MSSPs and enterprise security teams with external commitments.
These capabilities make Enterprise more practical for real-world, high-stakes investigations that demand clarity, completeness, and context.
Trusted by Industry Leaders and Backed by the Community
ANY.RUN is consistently rated as a leading solution on major platforms.
- G2 Rating: 4.7/5 → Read Reviews on G2
- Gartner Peer Insights Rating: 4.8/5 → See on Gartner
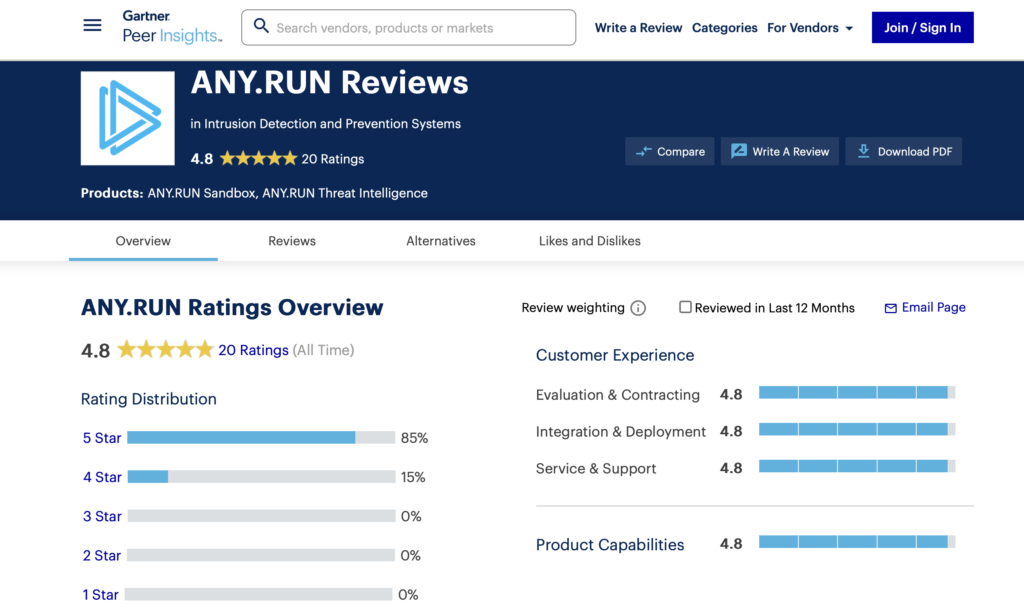
From MSSPs to financial institutions, teams around the world choose ANY.RUN to investigate faster, detect smarter, and simplify their daily workflows. These ratings reflect what thousands of users already know: interactive analysis makes all the difference.
Boost SOC Performance with Real-Time Threat Intelligence
Teams using ANY.RUN’s Interactive Sandbox also utilize advanced Threat Intelligence solutions that help you enrich your security, from detection to prevention.
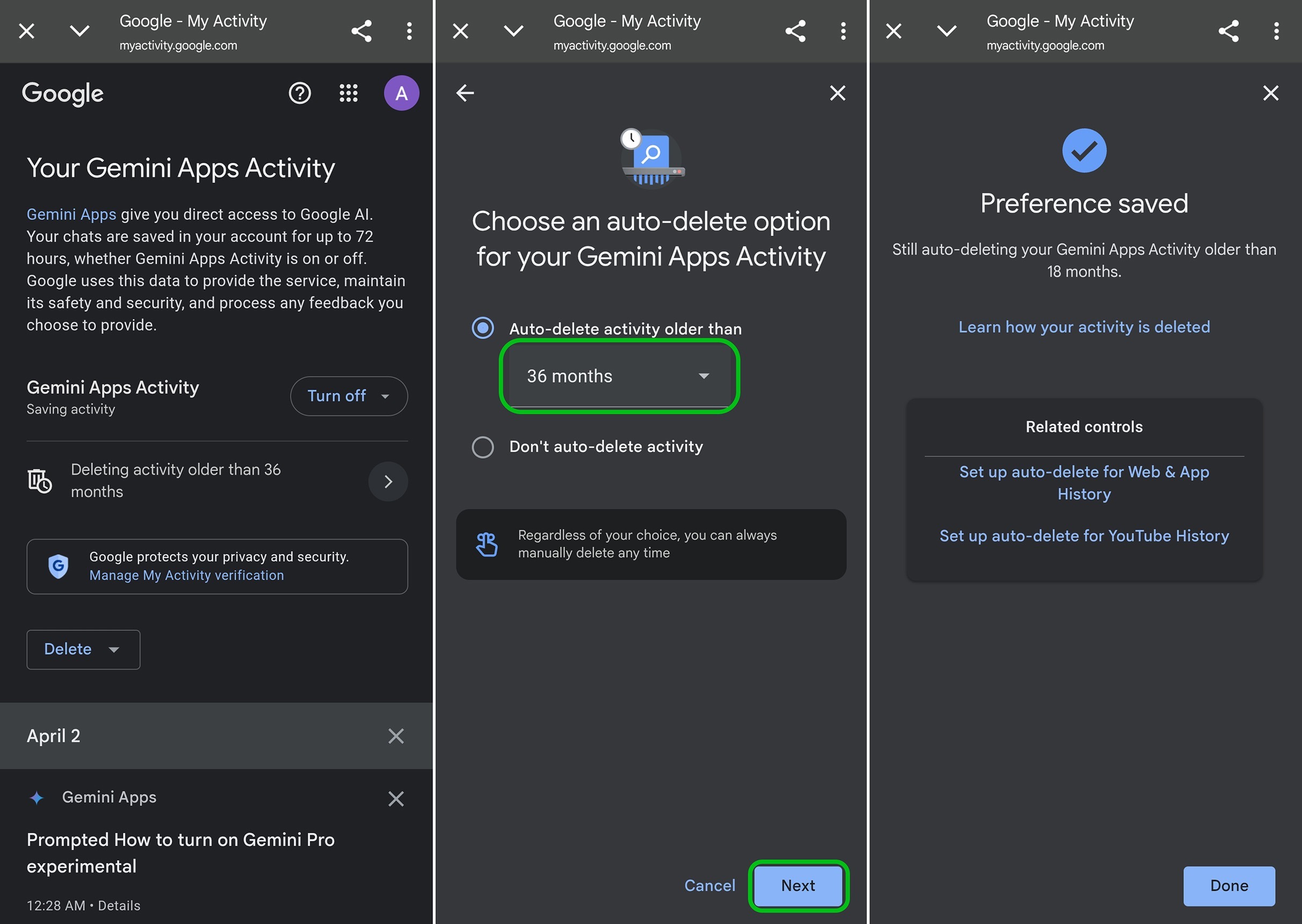
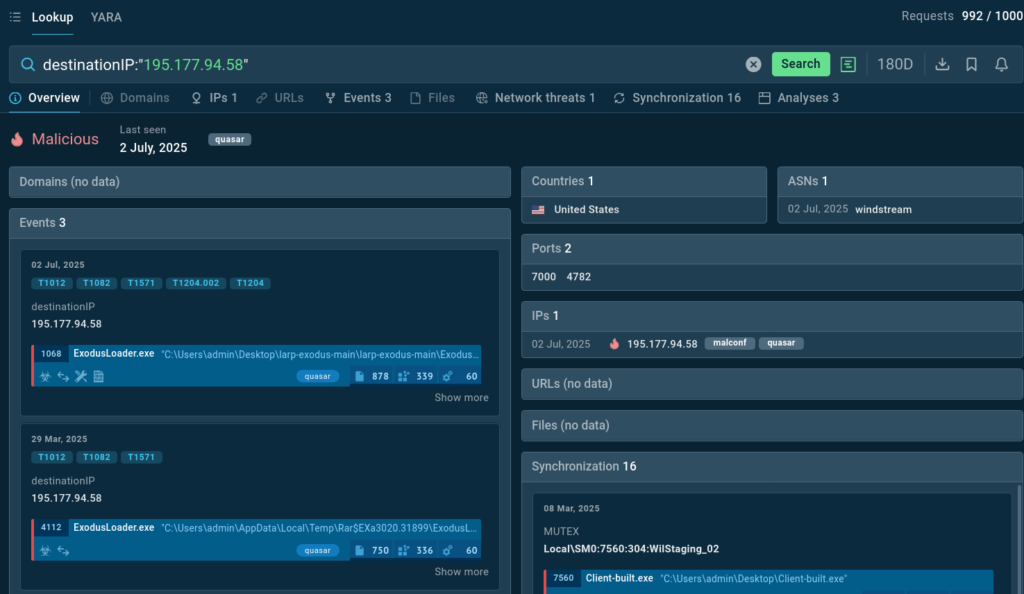
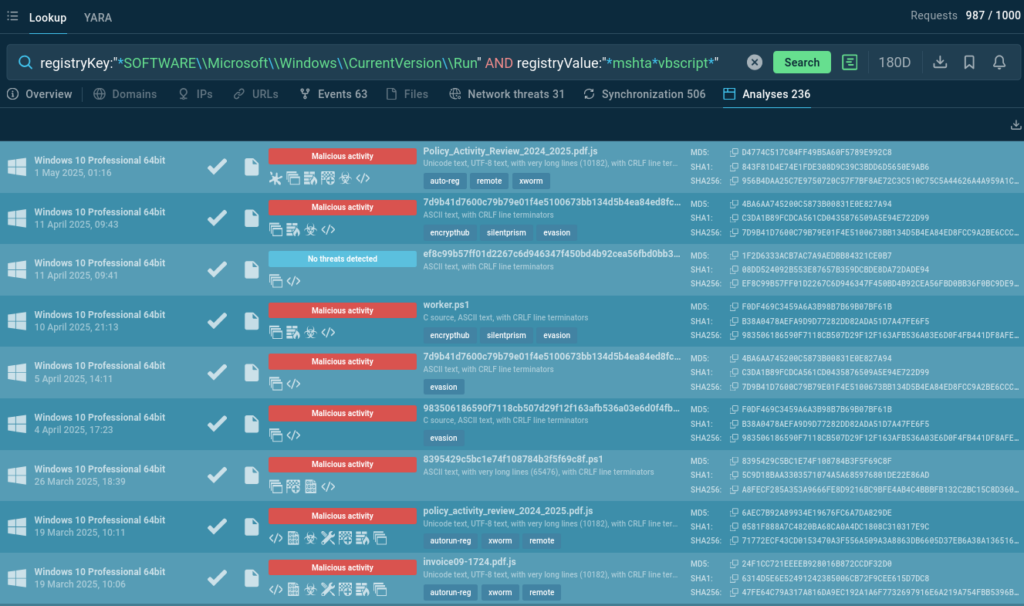
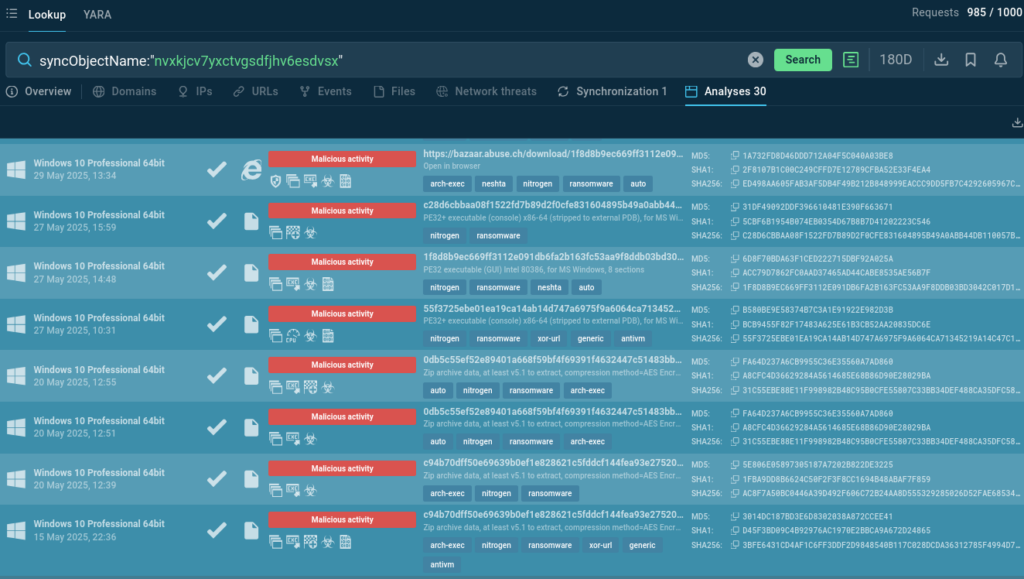
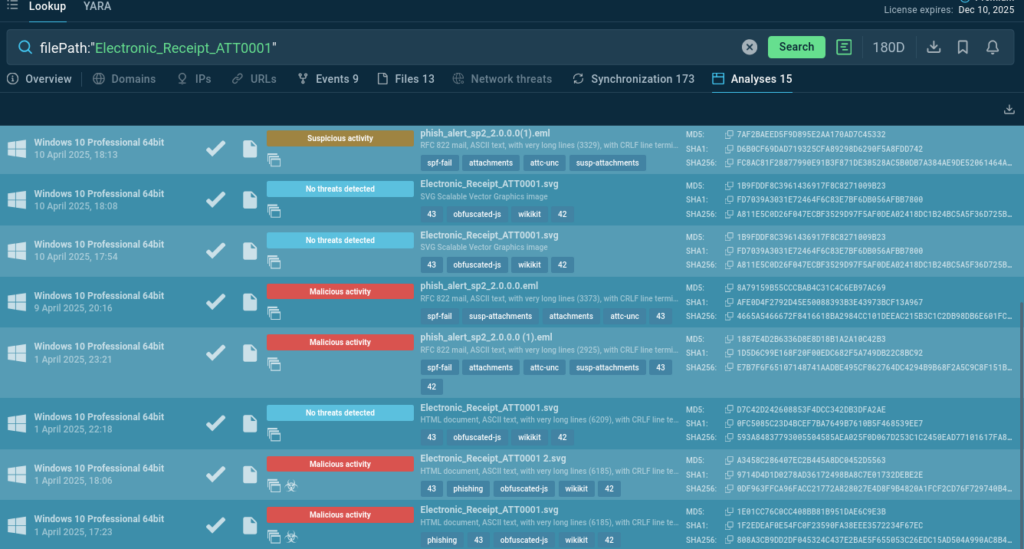
Threat Intelligence Lookup
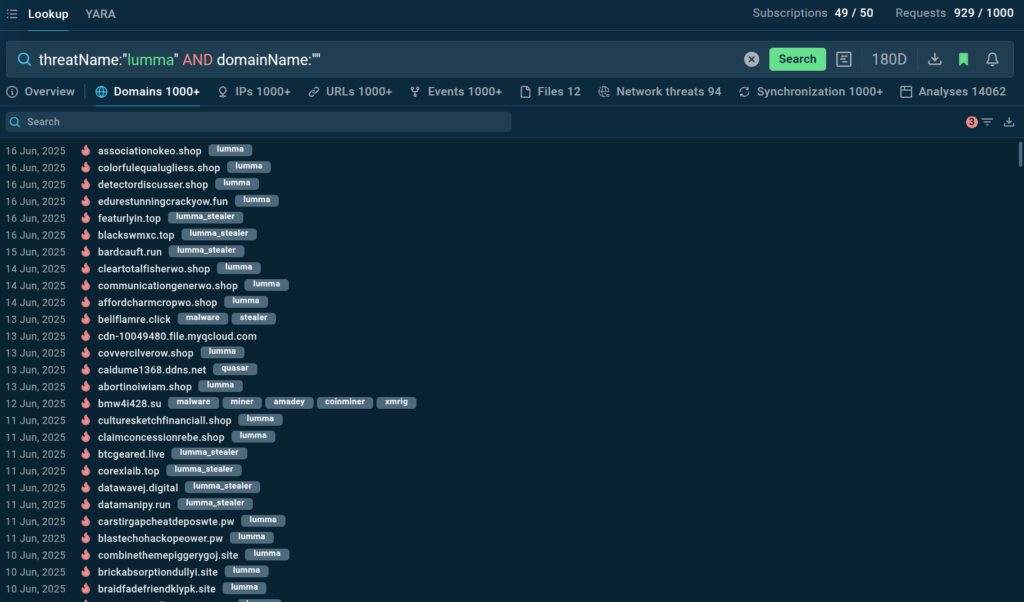
Quickly assess suspicious IPs, domains, hashes, and URLs with real-time context from live sandbox detonations across 15,000 organizations. TI Lookup lets you uses over 40 behavioral and static indicators to help SOC teams make faster decisions, reduce false positives, and respond to threats before they escalate, minimizing business risk and cutting investigation time.
Explore Threat Intelligence Lookup
Threat Intelligence Feeds
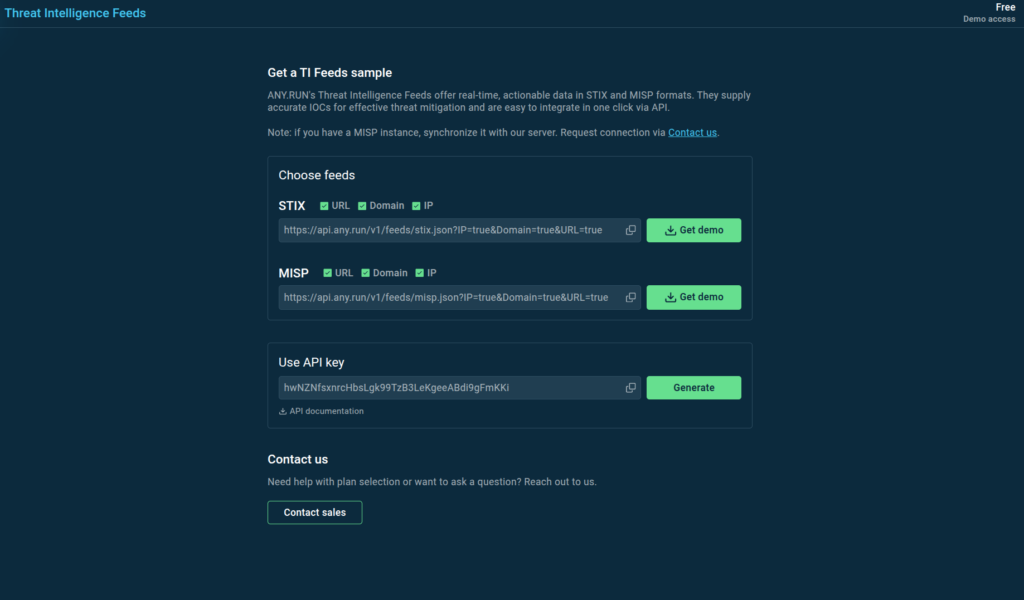
Receive continuously updated network indicators pulled from the latest malware samples analyzed in our sandbox. ANY.RUN’s TI Feeds help you proactively block threats and improve detection rules across your entire security stack.
Explore Threat Intelligence Feeds
About ANY.RUN
Designed to accelerate threat detection and improve response times, ANY.RUN equips teams with interactive malware analysis capabilities and real-time threat intelligence.
ANY.RUN’s cloud-based sandbox supports investigations across Windows, Linux, and Android environments. Combined with Threat Intelligence Lookup and Feeds, our solutions give security teams full behavioral visibility, context-rich IOCs, and automation-ready outputs, all with zero infrastructure overhead.
Ready to see how ANY.RUN’s services can power your SOC?
The post Enterprise Plan: Boost SOC Performance, Reduce Business Risks with ANY.RUN appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More