OfferUp scammers are out in force: Here’s what you should know
The mobile marketplace app has a growing number of users, but not all of them are genuine. Watch out for these common scams.
WeLiveSecurity – Read More
The mobile marketplace app has a growing number of users, but not all of them are genuine. Watch out for these common scams.
WeLiveSecurity – Read More
Bulletproof hosting providers are abusing the legitimate ISPsystem infrastructure to supply virtual machines to cybercriminals
Categories: Threat Research
Tags: virtual machine, cybercrime, Ransomware, ISPs
Sophos Blogs – Read More

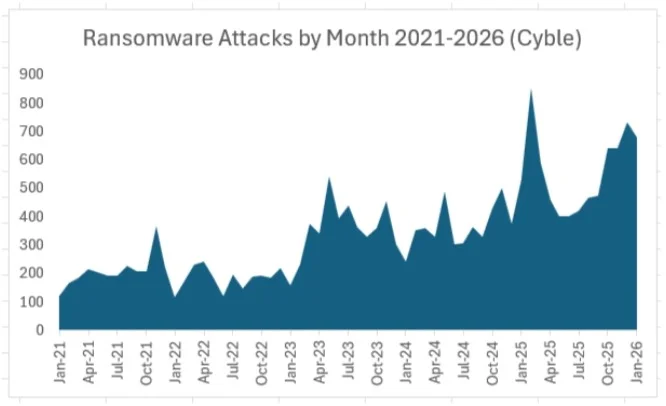
Ransomware groups claimed more than 2,000 attacks in the last three months of 2025 – and they’re starting 2026 at the same elevated pace.
Cyble recorded 2,018 claimed attacks by ransomware groups in the fourth quarter of 2025, an average of just under 673 a month. The threat groups maintained that pace in January 2026, claiming 679 ransomware victims.
By comparison, in the first nine months of 2025, ransomware groups averaged 512 claimed victims a month, so the trend in the last four months has been more than 30% above the previous nine-month period. The chart below shows ransomware attacks by month since 2021.
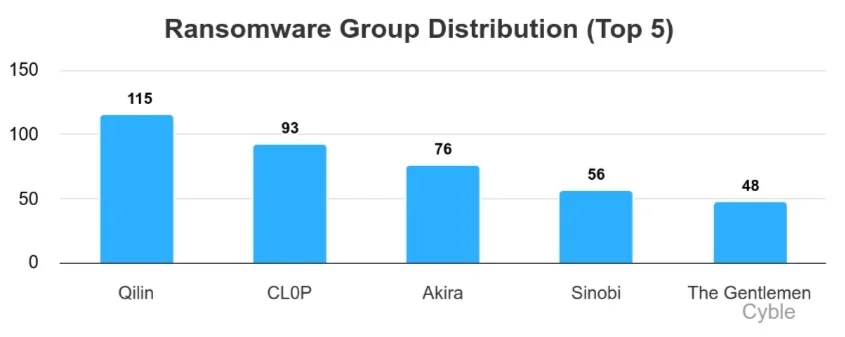
Qilin once again led all ransomware groups, with 115 claimed attacks in January. A resurgent CL0P has claimed scores of victims in the last two weeks, yet as of this writing had provided no technical details on the group’s latest campaign. Akira once again remained among the leaders with 76 claimed victims, while newcomers Sinobi and The Gentlemen rounded out the top five (chart below).
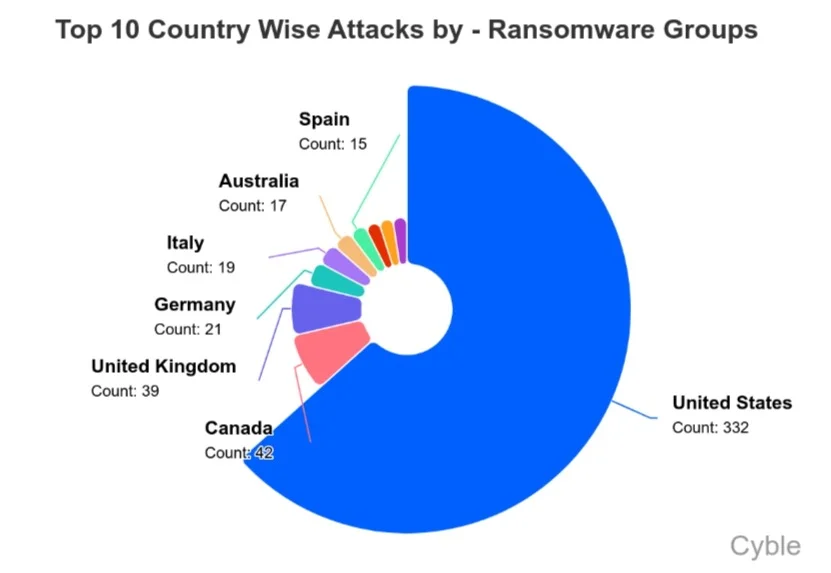
The U.S. once again was the most attacked country by a significant margin, accounting for just under half of all ransomware attacks in January (chart below). The UK and Australia experienced higher-than-usual attack volumes; CL0P’s recent campaign was a factor in both of those increases.
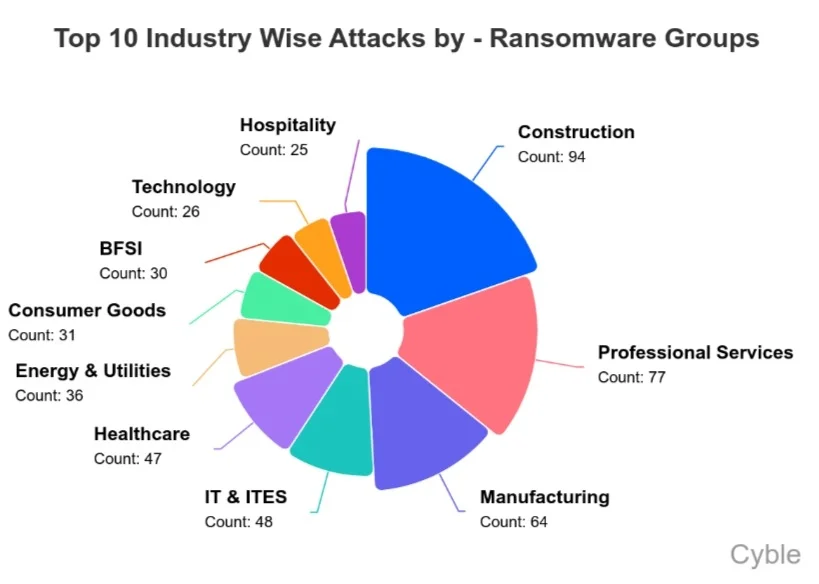
Construction, professional services, and manufacturing continue to lead the sectors hit by ransomware attacks, likely due to opportunistic threat actors targeting vulnerable environments (chart below). The IT industry also remains a frequent target of ransomware groups, likely due to the rich target the sector represents and the potential to pivot into downstream customer environments.
Here are some of the most significant ransomware attacks that occurred in January, several of which had supply chain implications. Additional details will be provided in Cyble’s forthcoming January 2026 Threat Landscape Report, which will be published in the Research Reports section.
As CL0P tends to claim victims in clusters, such as its exploitation of Oracle E-Business Suite flaws that helped drive supply chain attacks to records in October, new campaigns by the group are noteworthy. Among the claimed victims in the latest campaign have been 11 Australia-based companies spanning a broad range of sectors such as IT and IT services, banking and financial services (BFSI), construction, hospitality, professional services, and healthcare.
Other claimed victims have included a U.S.-based IT services and staffing company, a global hotel company, a major media firm, a UK payment processing company, and a Canada-based mining company engaged in platinum group metals production.
The Everest ransomware group claimed responsibility for breaching a major U.S. manufacturer of telecommunications networking equipment and claimed to have exfiltrated 11 GB of data. Everest claims the data includes PDF documents containing sensitive engineering materials, such as electrical schematics, block diagrams, and service subsystem documentation.
Additional directories reportedly contain .brd files, which are printed circuit board (PCB) layout files detailing information critical to hardware manufacturing and replication. The group also shared multiple samples showing internal directories, engineering blueprints, and 3D design-related materials.
The Qilin ransomware group claimed responsibility for breaching a U.S.-based airport authority responsible for managing commercial aviation operations and related services. The group shared 16 data samples as proof-of-compromise. The materials suggest access to financial documents, telehealth-related reports, internal email correspondence, scanned identification documents, non-disclosure agreements (NDAs), and other confidential agreements, suggesting exposure of sensitive administrative and operational information.
The Sinobi ransomware group claimed a breach of an India-based IT services company providing digital transformation, cloud, ERP, and managed services. The threat group alleges the theft of more than 150 GB of data, including contracts, financial records, and customer data. Samples shared by the attackers indicate access to internal infrastructure, including Microsoft Hyper-V servers, multiple virtual machines, backups, and storage volumes.
The Rhysida ransomware group claimed responsibility for breaching a U.S. company providing life sciences and biotechnology instrumentation and solutions. According to the threat group, the allegedly stolen data has already been sold, though no information was provided regarding the buyer or the price at which the dataset was advertised.
The victim was listed as directly sold rather than placed under a traditional negotiation or countdown model. Despite this, samples remain accessible and indicate exposure of email correspondence, engineering blueprints, project documentation, and non-disclosure agreements (NDAs), suggesting compromise of both technical and corporate information.
The RansomHouse extortion group claimed responsibility for breaching a China-based electronics manufacturing company providing precision components and assembly services for global technology and automotive manufacturers. As evidence, RansomHouse published documentation indicating access to extensive proprietary engineering and production-related data. The shared materials reference confidential 3D CAD models (STEP/PRT), 2D CAD drawings (DWG/DXF), engineering documentation, printed circuit board (PCB) design data, Gerber files, electrical and layout architecture data, and manufacturing drawings. Notably, the group claims the compromised archives contain data associated with multiple major technology and automotive companies.
INC Ransom claimed responsibility for breaching a Hong Kong–based manufacturer supplying precision components to the global electronics and automotive industries. According to the group, approximately 200 GB of data was allegedly exfiltrated. The claimed dataset reportedly includes client-related information associated with more than a dozen major global brands, plus confidential contracts and project documentation for at least three major IT companies.
The Qilin ransomware group claimed responsibility for breaching a Taiwan-based company operating in the semiconductor and electronics manufacturing sector. According to the group, approximately 275 GB of data was allegedly exfiltrated. Based on the file tree information shared by Qilin, the dataset reportedly consists of 19,822 directories and 177,551 files, suggesting broad access to internal systems.
The Nitrogen ransomware group leaked more than 71 GB of data allegedly stolen from a U.S. company providing engineered components and systems for the automotive industry. According to the threat group, the exposed data includes sensitive corporate and technical information such as CAD drawings, accounts payable and receivable records, invoices, and balance sheet documentation. To substantiate its claims, Nitrogen published selected project blueprints and shared a file tree indicating the alleged theft of approximately 116,180 files, suggesting broad access to internal engineering and financial systems.
The Anubis ransomware group claimed responsibility for breaching an Italian government authority responsible for the management, regulation, and development of regional maritime port operations. According to the group, the compromised data includes incident and safety reports, logistics and operational data, port infrastructure layouts, audit results, internal reports, and business correspondence.
Among new ransomware groups that have emerged recently, Green Blood has launched an onion-based data leak site. While the group has not yet publicly named specific victims, it claims that affected organizations are located in India, Senegal, and Colombia. The group provides TOX ID and email-based communication channels for victim contact. Notably, malware samples associated with Green Blood have been observed in the wild. The ransomware encrypts files using the “.tgbg” extension and drops a ransom note titled “!!!READ_ME_TO_RECOVER_FILES!!!.txt”
A new ransomware-as-a-service (RaaS) operation named DataKeeper has surfaced, promoting an updated affiliate model referred to as CrystalPartnership RaaS. The group claims this approach improves trust by splitting ransom payments directly between the operator’s and affiliate’s Bitcoin addresses at the time of payment, removing reliance on centralized payout handling. DataKeeper is advertised as a Windows-focused ransomware toolkit. The operation claims to use a hybrid encryption scheme combining symmetric file encryption with RSA-4096 key protection, unique per-build identifiers, and TOR-based payment links. Encryption and decryption workflows are tied to a victim-specific ID, with decryption requiring delivery of a key file following payment.
The group emphasizes operational features such as in-memory execution, multithreaded encryption, optional shadow copy removal, network share targeting, and evading security controls.
The threat actor (TA) MonoLock announced a new RaaS operation on the RAMP cybercrime forum (the forum has since been seized by the FBI). MonoLock’s core design is based on Beacon Object Files (BoF), enabling full in-memory execution, reduced payload exposure, and centralized control from a single post-exploitation command-and-control (C2) instance without dropping files.
While BoF usage is common in Windows environments, MonoLock introduced a custom Linux ELF-based BoF loader, derived from the TrustedSec ELFLoader, adding chained execution, command packing, encryption, and in-memory deployment. The group promotes a “Zero Panel” extortion model, explicitly rejecting leak sites and Tor-based negotiation panels.
MonoLock claims that avoiding public extortion infrastructure reduces law enforcement exposure and leverages silence as negotiation pressure, minimizing reputational damage for victims. Affiliates are recruited under a 20% revenue share with a USD $500 registration fee, alongside a limited referral program running from January 11 to March 31.
The persistently high level of ransomware attacks – and the emergence of new ransomware groups eager to compete on features and price – highlight the urgent need for security teams to adopt a defense-in-depth cyber strategy. Cybersecurity best practices that can help build resilience against attacks include:
Cyble’s comprehensive attack surface management solutions can help by scanning network and cloud assets for exposures and prioritizing fixes, in addition to monitoring for leaked credentials and other early warning signs of major cyberattacks.
Additionally, Cyble’s third-party risk intelligence can help organizations carefully vet partners and suppliers, providing an early warning of potential risks.
The post Ransomware Attacks Have Surged 30% Since Q4 2025 appeared first on Cyble.
Cyble – Read More
First month of the year, and we’re starting it off with updates that support faster decisions and more predictable SOC operations.
In January, we introduced a major workflow enhancement with the new ANY.RUN Sandbox integration with MISP, alongside expanded detection coverage across behavior signatures, YARA rules, and Suricata.
Let’s find out what this means for your team.
January brought another solid round of improvements focused on practical SOC workflows: faster alert validation, less manual back-and-forth, and earlier decisions that help stop incidents from growing into bigger problems.
The main highlight of the month was the release of the ANY.RUN Sandbox integration with MISP; an important step for teams that use MISP daily for threat intelligence and investigations.
Most SOC teams spend too much time validating alerts, moving samples between tools, and filling in missing context. When execution evidence is separated from threat intelligence platforms, investigations slow down, MTTR increases, and SLAs come under pressure.
With the ANY.RUN Sandbox integration for MISP, analysts can now bring real execution behavior directly into MISP, turning it from a passive intelligence repository into an active investigation layer.
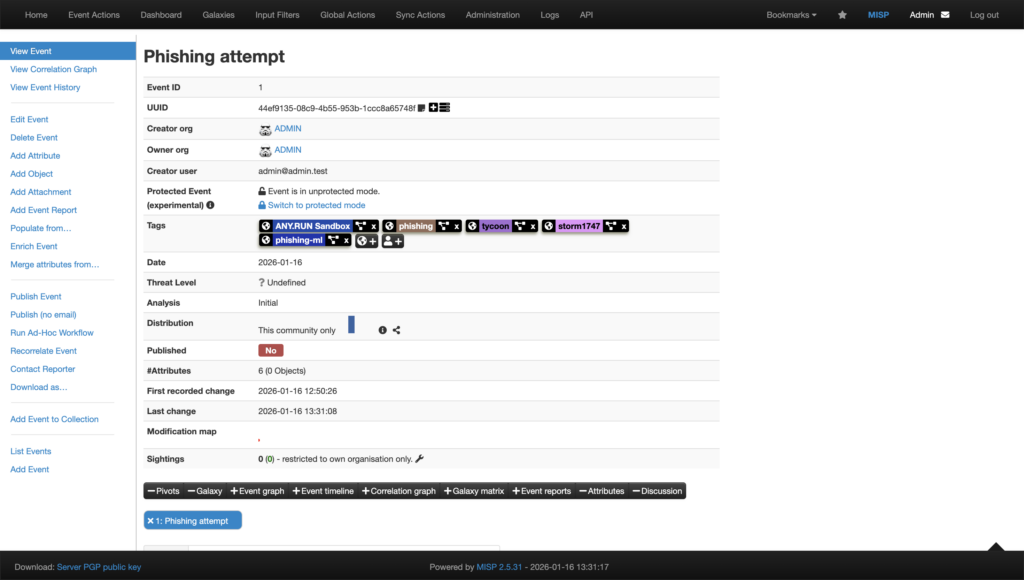
Using native MISP modules, suspicious files and URLs can be sent straight from MISP into the ANY.RUN Sandbox, without any context switching or manual handoffs.
You can easily integrate the modules, using the following links:
Analysis runs automatically using Automated Interactivity. This allows the sandbox to behave like a real user by clicking, opening files, and waiting when needed. This is critical for exposing modern threats that delay execution or hide behind user-driven actions.
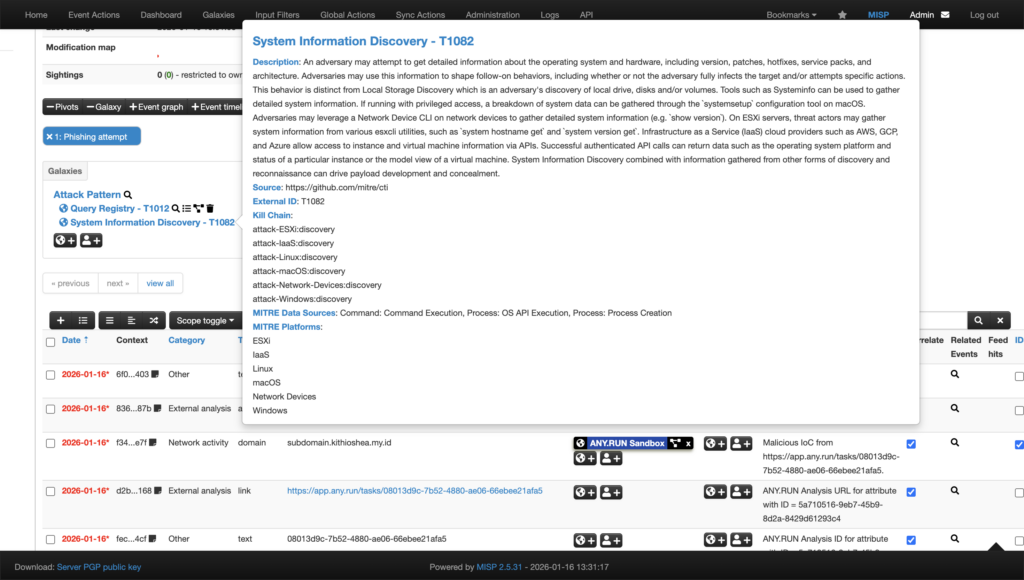
Once execution completes, results are automatically returned to MISP, including, verdict and risk assessment, extracted IOCs, adirect link to the interactive sandbox session, HTML analysis report, mapped MITRE ATT&CK techniques and tactics.
This allows analysts to validate alerts using real behavior, not assumptions, directly inside their existing workflow.
For organizations using MISP as part of daily operations, this integration delivers clear operational gains:

To support proactive coverage at scale, ANY.RUN Threat Intelligence Feeds deliver verified malicious network IOCs from real attacks across 15,000+ organizations, in STIX/TAXII format, ready for use in MISP, SIEM, or SOAR platforms.
Learn more about TI Feeds integration with MISP
In January, our team continued expanding the detection layer across sandbox execution, behavioral analytics, and network visibility, reinforcing ANY.RUN as a unified operational solution for detection, validation, and response.
This month’s updates include:
Together, these updates help security teams move faster from alert to decision, without switching tools or waiting for late-stage indicators.
January’s behavior signature updates focus on early-stage execution signals and hands-on attacker activity, helping teams identify malicious intent before payloads fully deploy or damage occurs.
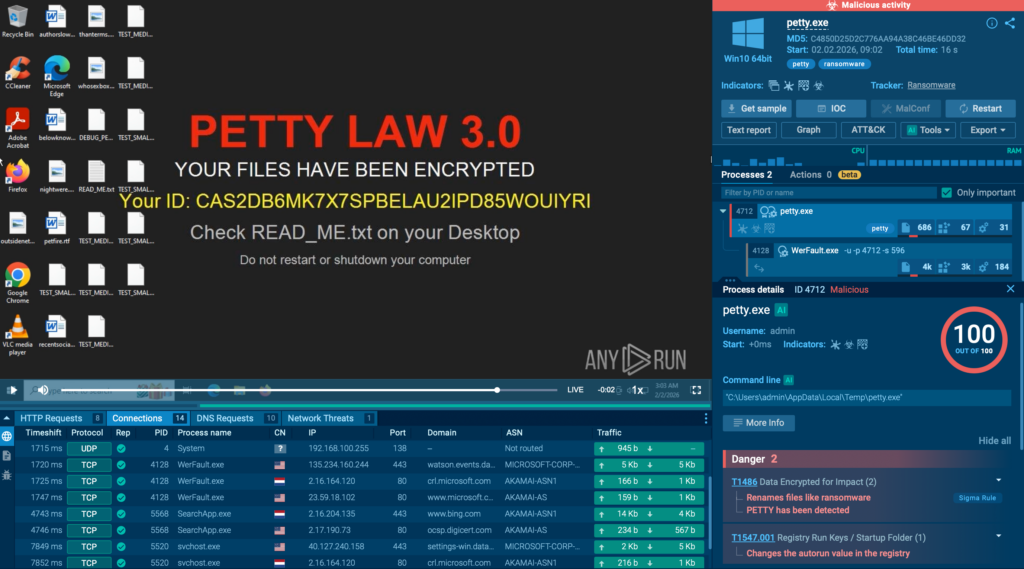
The new detections expand coverage across ransomware families, loaders, stealers, and post-exploitation techniques, with particular attention to abuse of native Windows tooling and suspicious command-line behavior often seen in real-world intrusions.
This month, our team added signatures that detect:
Malware and loader execution patterns, such as
Suspicious use of built-in Windows tools, including
Persistence and system modification techniques, such as
Remote access and administrative tools observed in malicious contexts, including
Mutex- and pattern-based detections, including
In January, 4 new YARA rules went live in production, expanding detection and hunting coverage inside ANY.RUN, especially useful when teams need quick classification and reliable pivots during triage.
Highlighted additions include:
These rules help security teams tag and cluster related samples faster, validate whether a file matches known patterns, and speed up investigation workflows without relying on a single indicator type.
Our team deployed 1,897 new Suricata rules to expand network-level visibility into phishing infrastructure, backdoor communication, and stealer-related traffic patterns. These detections help teams identify malicious activity even when payloads are fileless, heavily obfuscated, or delivered through multi-stage web flows.
Highlighted additions include:
ANY.RUN is a core part of modern security operations, helping organizations make faster, more confident decisions across the full investigation lifecycle, from early alert validation to deep analysis and continuous threat awareness.
By exposing real attacker behavior in real time, ANY.RUN adds the context that alerts often lack and keeps detections aligned with how threats actually operate in the wild. This allows SOC teams to reduce noise, shorten response times, and focus effort where it matters most.
Today, more than 600,000 security specialists and 15,000 organizations worldwide rely on ANY.RUN to accelerate triage, limit unnecessary escalations, and stay ahead of fast-moving phishing and malware campaigns
Integrate ANY.RUN’s solution for Tier 1/2/3 in your organization →
The post Release Notes: Workflow Improvements, MISP Integration & 2,000+ New Detections appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More

Cyble Vulnerability Intelligence researchers tracked 1,147 vulnerabilities in the last week, and more than 128 of the disclosed vulnerabilities already have a publicly available Proof-of-Concept (PoC), significantly increasing the likelihood of real-world attacks.
A total of 108 vulnerabilities were rated as critical under the CVSS v3.1 scoring system, while 54 received a critical severity rating based on the newer CVSS v4.0 scoring system.
Below are some of the IT vulnerabilities flagged by Cyble threat intelligence researchers for prioritization by security teams in recent reports to clients.
Cyble’s network of honeypot sensors detected attack attempts on CVE-2025-68613, a critical remote code execution flaw in the n8n open-source workflow automation platform. Workflow expressions supplied by authenticated users could execute in an insufficiently isolated context under the Improper Control of Dynamically-Managed Code Resources flaw, potentially enabling arbitrary code execution with n8n privileges and potential full system compromise. The issue is fixed in versions 1.120.4, 1.121.1, and 1.122.0.
Vulnerabilities generating discussion in open-source communities included CVE-2025-8088, a high-severity path traversal vulnerability in WinRAR that exploits Alternate Data Streams (ADS) in crafted RAR archives. The vulnerability was added to CISA’s Known Exploited Vulnerabilities (KEV) catalog last August, but recent reports reveal that multiple actors, including nation-state adversaries and financially motivated groups, are exploiting the flaw to establish initial access and deploy a diverse array of payloads.
Also under active discussion is CVE-2025-15467, a critical stack buffer overflow in OpenSSL’s CMS (Cryptographic Message Syntax) AuthEnvelopedData parsing when using AEAD ciphers like AES-GCM. OpenSSL 3.6, 3.5, 3.4, 3.3 and 3.0 are vulnerable to the issue, while FIPS modules and OpenSSL 1.1.1 and 1.0.2 are not.
Among the recent additions to CISA’s Known Exploited Vulnerabilities (KEV) catalog were CVE-2026-24858, an authentication bypass vulnerability in Fortinet products; CVE-2025-68645, a Local File Inclusion (LFI) vulnerability in the Webmail Classic UI of Zimbra Collaboration Suite (ZCS); and CVE-2026-1281, an Ivanti Endpoint Manager Mobile (EPMM) Code Injection vulnerability.
CVE-2026-24061 is another recent CISA KEV addition, a critical authentication bypass vulnerability in GNU Inetutils telnetd. The flaw lies in the improper neutralization of argument delimiters, specifically allowing an attacker to inject the “-f root” value into the USER environment variable. After successful exploitation, a remote unauthenticated attacker can bypass authentication mechanisms to gain immediate root-level access to the system over the network. Cyble dark web researchers have observed threat actors on underground forums discussing weaponizing the vulnerability.
Another vulnerability under discussion by threat actors on the dark web is CVE-2025-27237, a high-severity local privilege escalation vulnerability affecting Zabbix Agent and Agent 2 on Windows. The vulnerability is caused by an uncontrolled search path that loads the OpenSSL configuration file from a directory writable by low-privileged users. By modifying this configuration file and injecting a malicious DLL, a local attacker could elevate their privileges to the SYSTEM level on the affected Windows host.
CVE-2026-22794, a critical authentication bypass vulnerability in Appsmith, is also under active discussion by threat actors. The flaw occurs because the application trusts a user-controlled HTTP “Origin” header during security-sensitive workflows, such as password resets. An attacker could use this to generate fraudulent links that, when clicked by a victim, send secret authentication tokens to an attacker-controlled domain, enabling full account takeover of any user, including administrators.
Among industrial control system (ICS) vulnerabilities of note, Festo Didactic SE MES PCs shipped with Windows 10 include a copy of XAMPP that contains around 140 vulnerabilities from third-party open-source applications, CISA said in a recent advisory. The issues can be fixed by replacing XAMPP with Festo Didactic’s Factory Control Panel application.
The high number of number of open-source vulnerabilities this week highlights the ever-present threat of software supply chain attacks, requiring constant vigilance by both security and development teams. Best practices aimed at reducing cyber risk and improving resilience include:
Cyble’s comprehensive attack surface management solutions can help by scanning network and cloud assets for exposures and prioritizing fixes, in addition to monitoring for leaked credentials and other early warning signs of major cyberattacks.
Additionally, Cyble’s third-party risk intelligence can help organizations carefully vet partners and suppliers, providing an early warning of potential risks.
The post The Week in Vulnerabilities: Open-Sources Fixes Urged by Cyble appeared first on Cyble.
Cyble – Read More
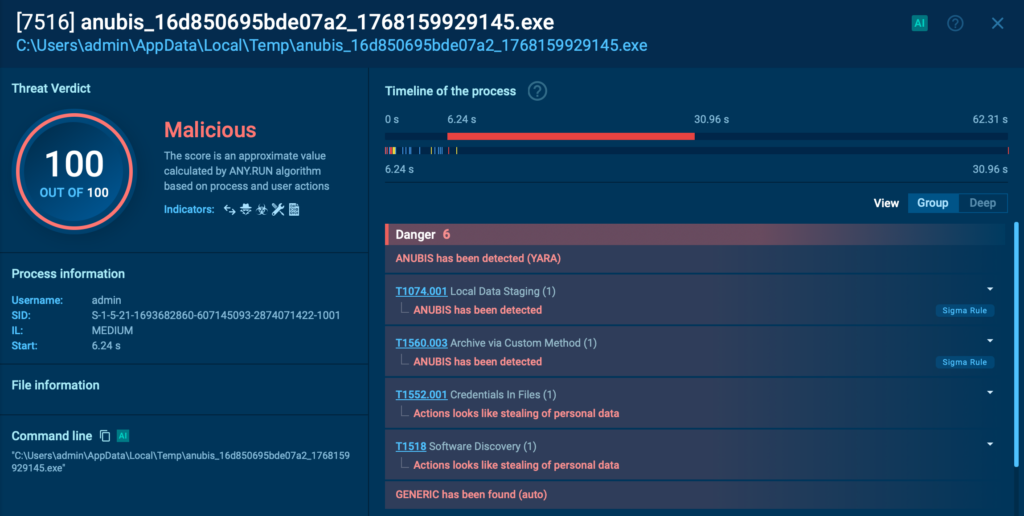
ANY.RUN observes a growing trend of phishing kit infrastructure being hosted on legitimate cloud and CDN platforms, rather than on newly registered domains. These campaigns often target enterprise users specifically, creating a global threat to businesses. The shift createsserious visibility challenges for security teams, as trusted platforms and valid indicators shield malicious activity from detection.
For a deeper dive, read on and see the breakdown of such cases, along with tips on what works and what doesn’t.
The most widespread and dangerous phishing campaigns today are powered by AiTM (Adversary-in-the-middle kits). These toolsets help unfold phishing attacks where threat actors become a proxy between the victim and a legitimate service.
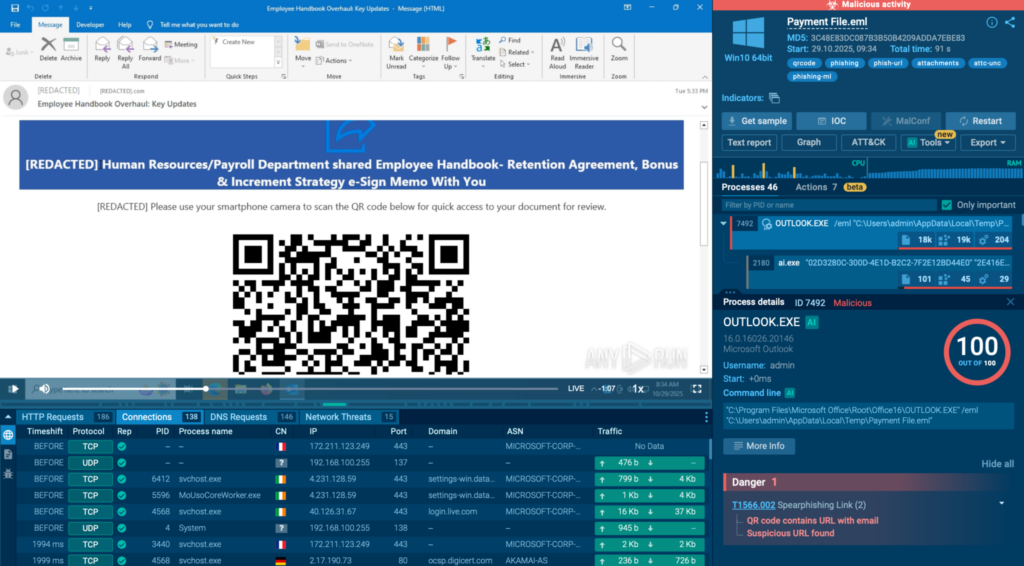
A typical phishkit attack starts with an email containing a link (including in the form of a QR code) leading to attackers’ infrastructure. Most campaigns also involve a CAPTCHA challenge and a string of redirects as a means to avoid detection by AVs and static systems.Advanced evasion leads to a high rate of missed attacks for organizations that suffer from data theft as a result of this.
ANY.RUN’s Interactive Sandbox provides security teams with the capabilities to quickly detect phishkit attacks thanks to interactive analysis. In addition to static detection, the sandbox lets SOC analysts safely follow the entire attack chain in an isolated VM and go past all the evasion layers to reveal the final malicious credential theft page or payload.
The result for businesses that have adopted ANY.RUN’s solutions in their infrastructure is a lower risk of a data breach and a more effective SOC team that can quickly identify phishing attempts with a high degree of certainty.
The top three most active phishing kits remain stable quarter to quarter. The list features:
Mostly these campaigns are hosted behind Cloudflare CDN infrastructure. You can find live examples using Threat Intelligence Lookup with queries like these:
threatName:”tycoon” AND destinationIpAsn:”cloudflarenet”
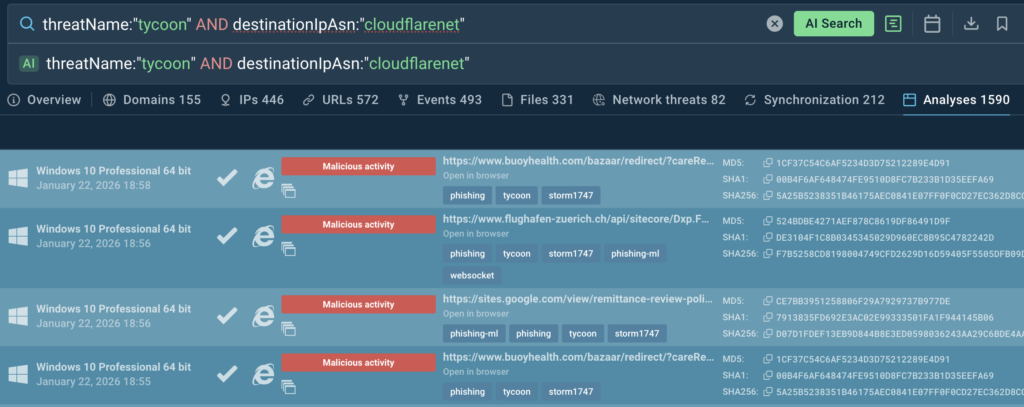
Use TI Lookup to strengthen alert triage and proactive threat hunting:
For threat actors, Cloudflare abuse offers critical advantages:
Because TLS termination happens at Cloudflare, SSL certificates and TLS session’s fingerprints like JA3S lose value as indicators for SOC analysts. IP- and TLS-based detection becomes inefficient, and the only remaining leads for analysts are domains and their reputation.

Interactive sandboxing combined with threat intelligence solutions enable analysts to uncover evasive phishing threats and helps achieve:
| The result is measurable: |
|---|
| +62.7% more threats detected overall |
| 94% of surveyed users report faster triage |
| 63% year-over-year user growth, driven by analyst efficiency |
| 30% fewer alerts require escalation to senior analysts |
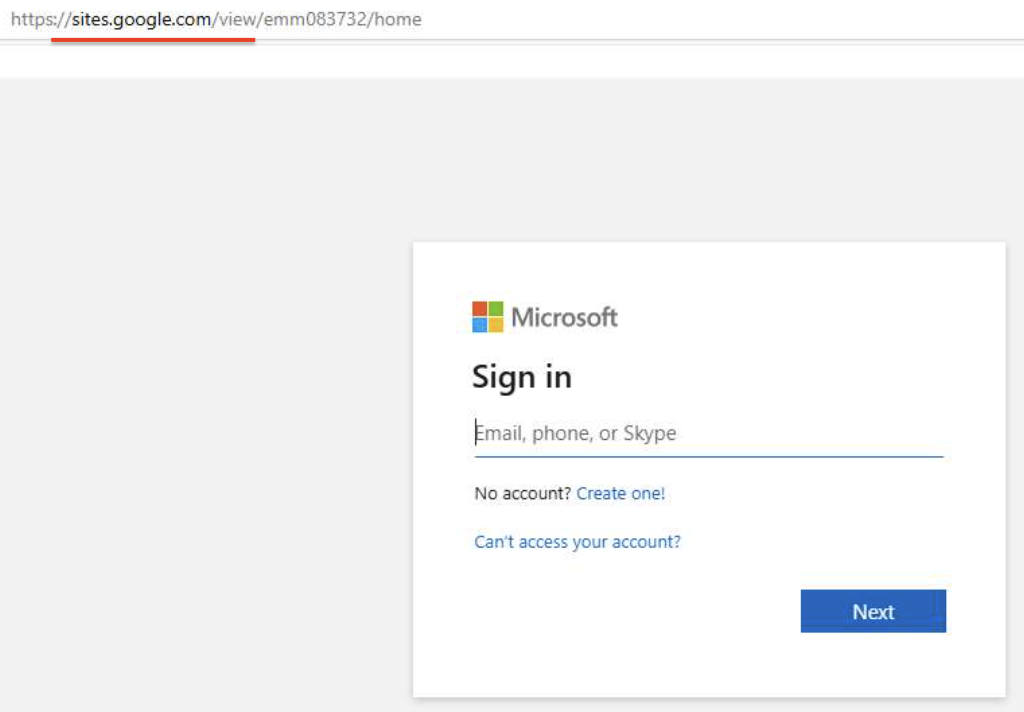
Until recently, a typical phishing attack looked like this:
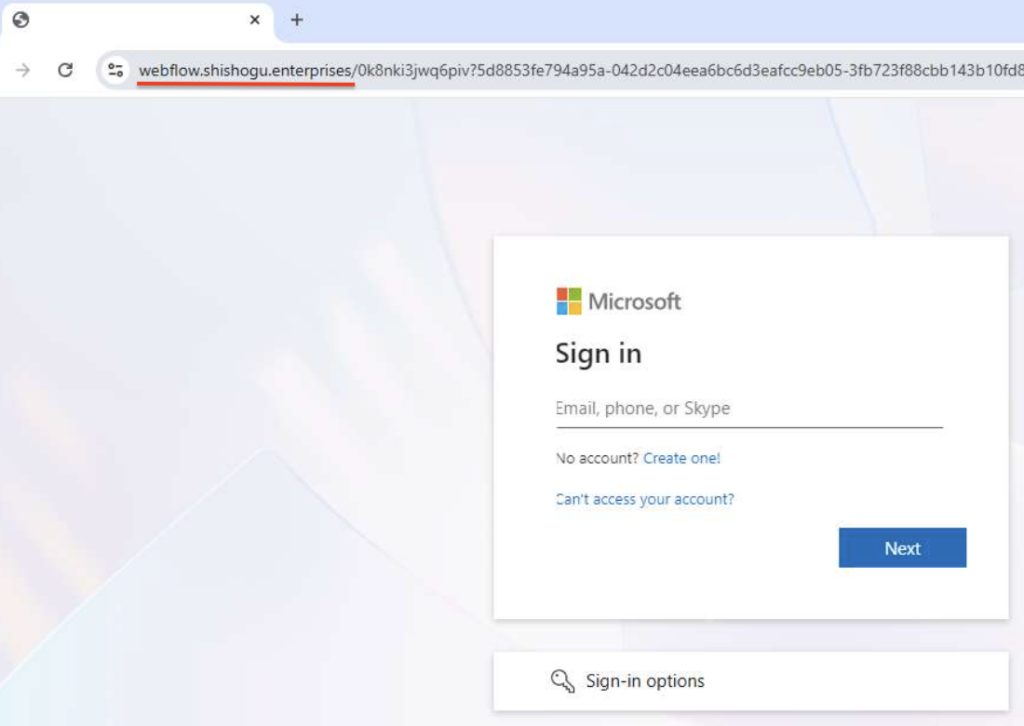
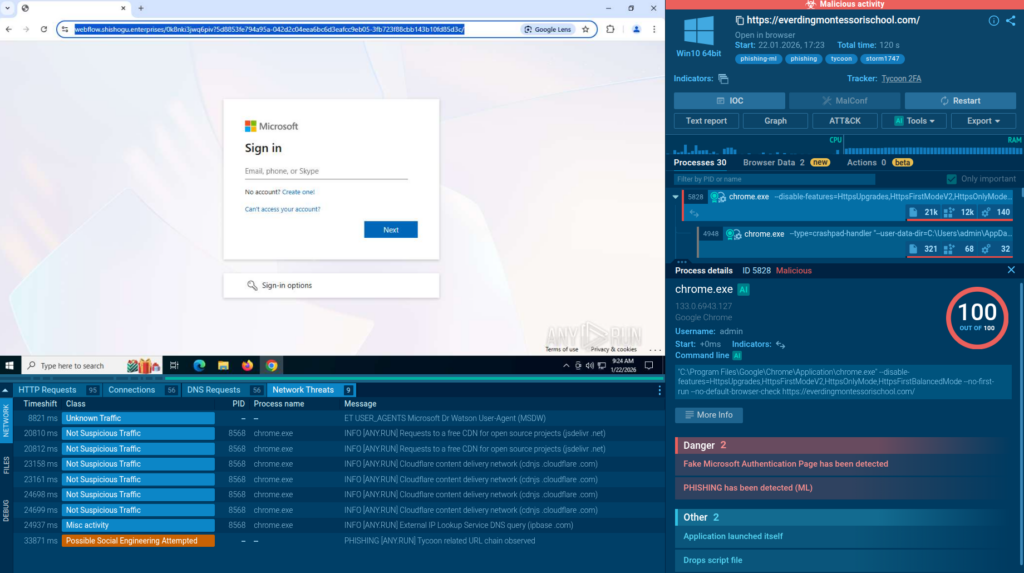
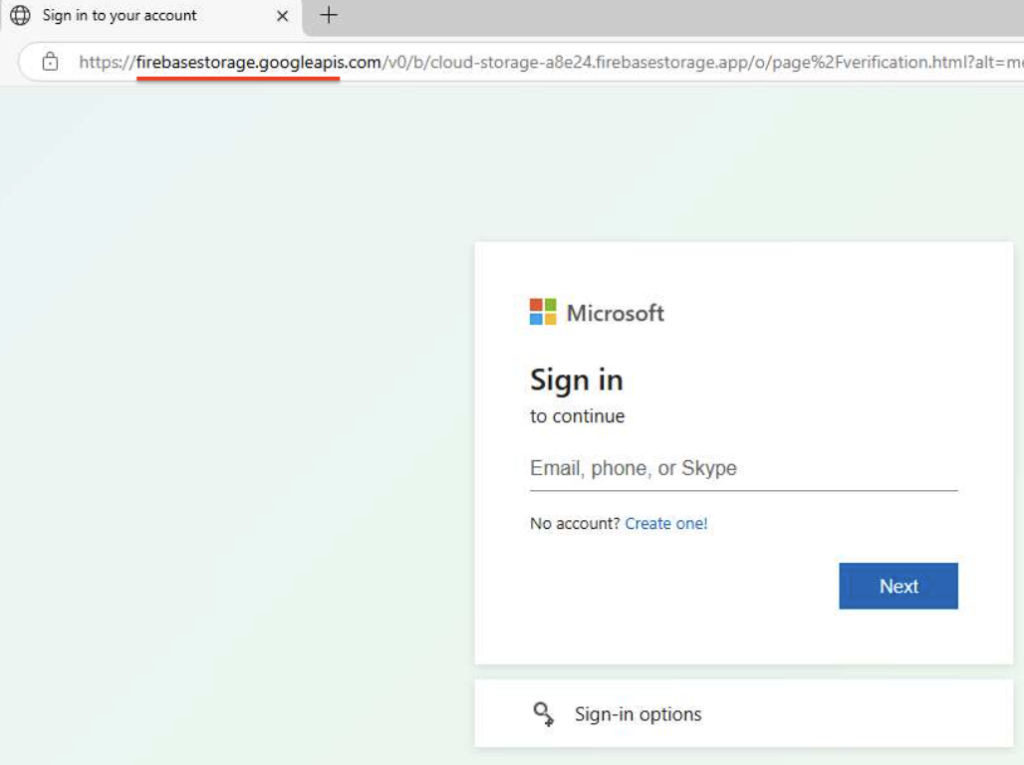
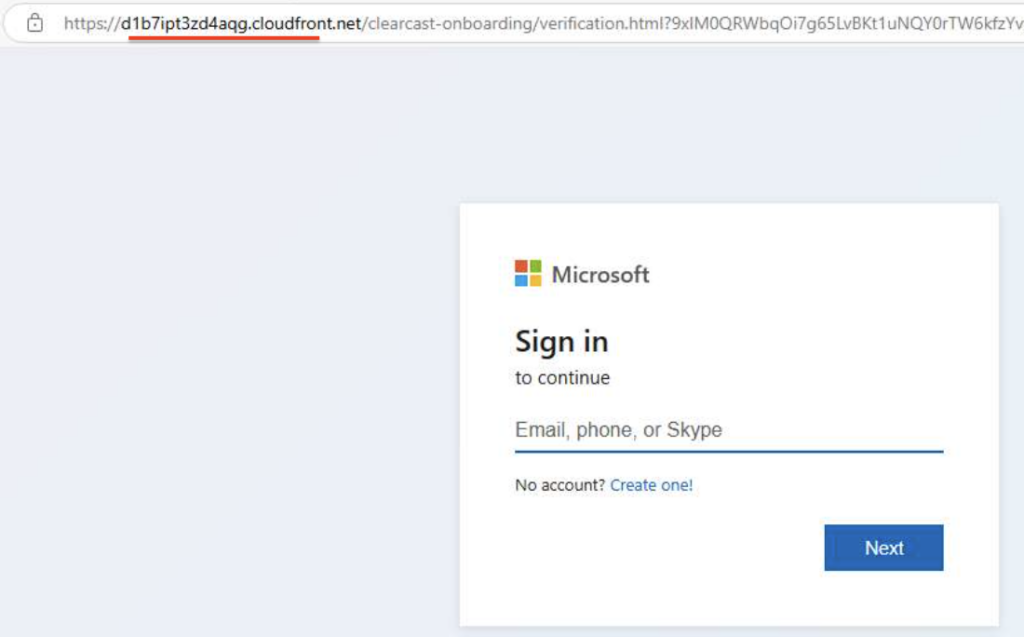
As shown above, the login form is hosted on a newly registered domain, not legitimate Microsoft 365 one (e.g., windows[.]net, microsoftonline[.]com, office[.]net, or live[.]com). This clearly indicates phishing.
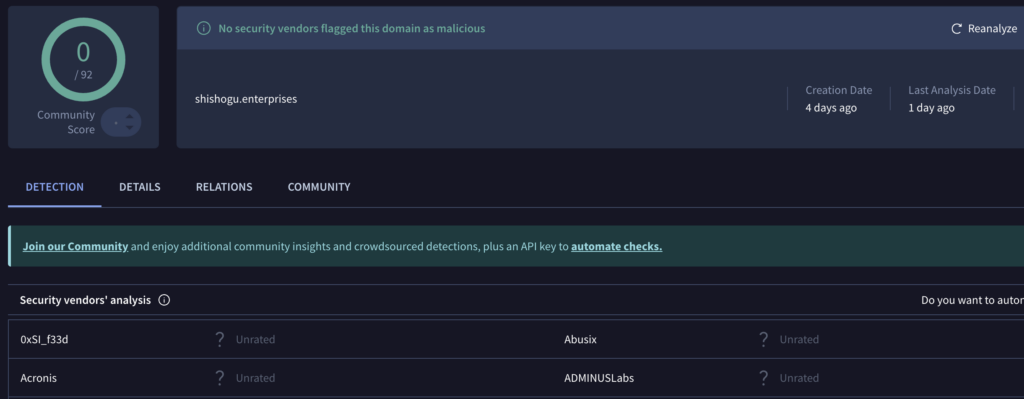
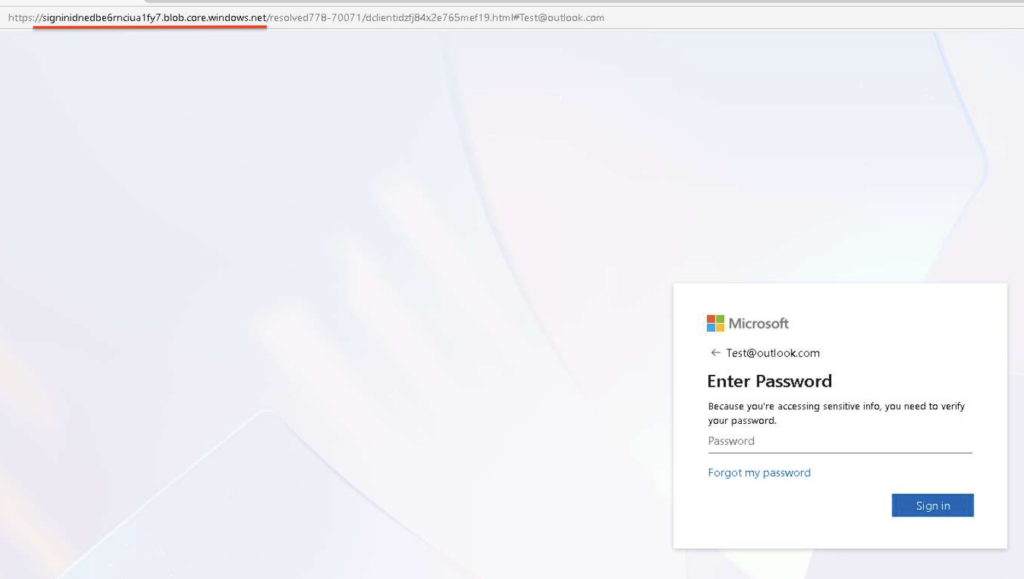
But modern phishing threats are significantly more complex and therefore dangerous. In many cases, even the domain name stops being a reliable IOC. That’s what can be observed in this sample:
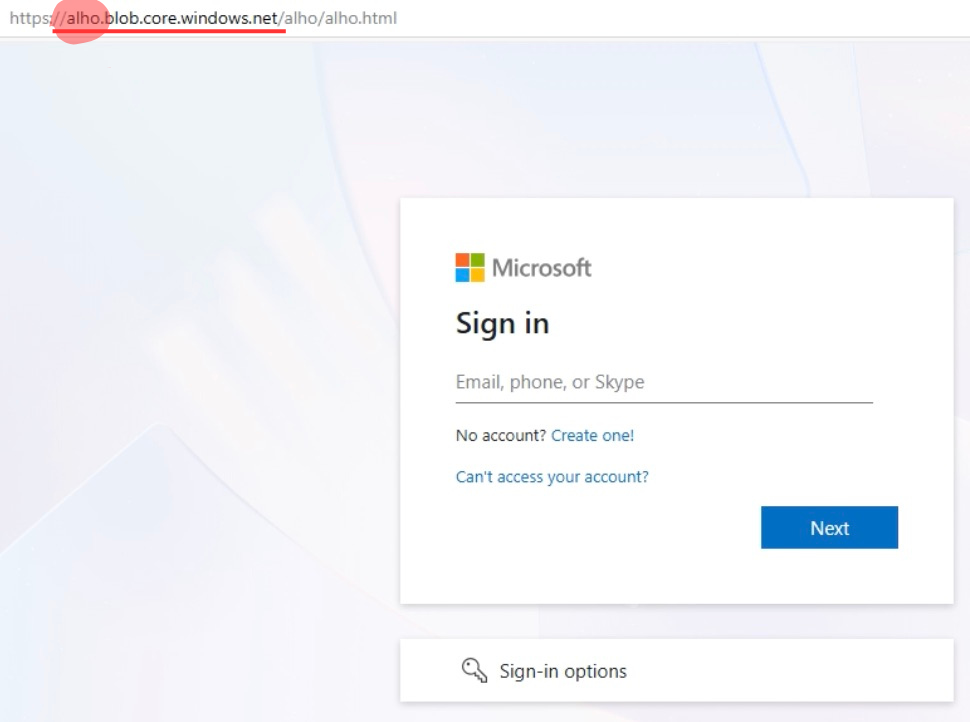
In this analysis, login form is hosted on legitimate Microsoft Azure Blob Storage, complicating the chance of detection. This sample belongs to Tycoon2FA, which we’ve discussed in detail in this article.
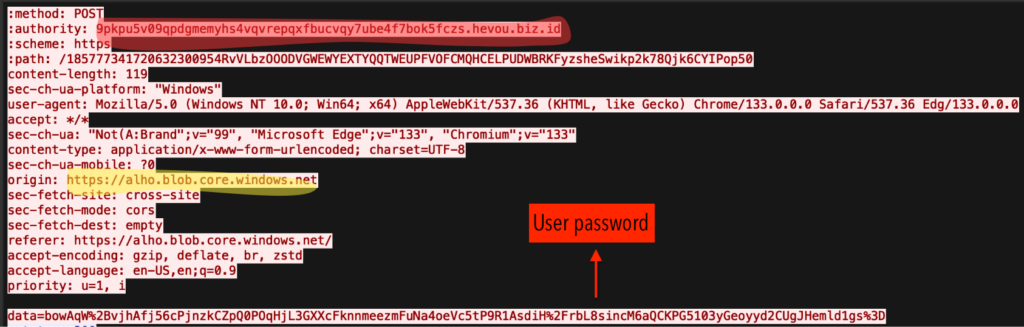
In the POST request below, the victim’s encrypted password is transmitted from Microsoft Azure page to an attacker-controlled server:
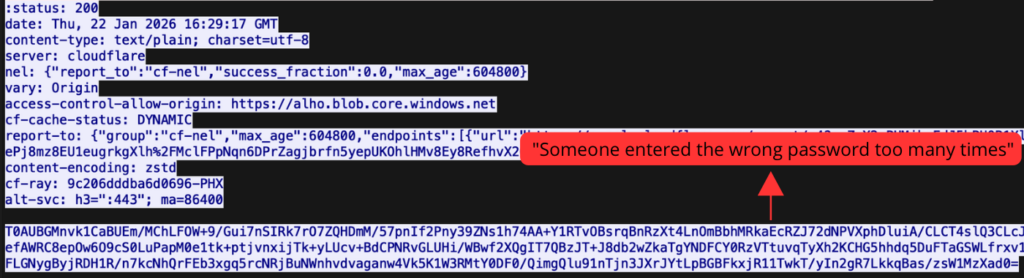
The response from a malicious reserve proxy returns a “wrong password” message, mimicking Microsoft’s legitimate authentication flow.
At the time of writing, it’s been a week the previous publication of these findings. Since then, the amount of similar phishing cases has nearly doubled.
You can find examples of this trend on TI Lookup:
threatName:”tycoon” AND domainName:”*.blob.core.windows.net”
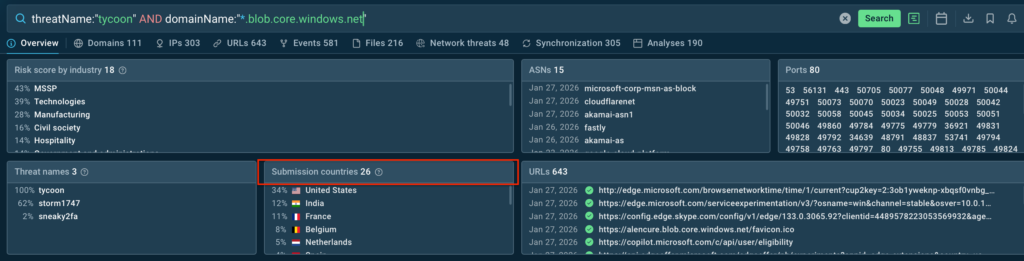
On average, SOC teams from the US and Europe encounter Tycoon-based phishing abusing trusted Microsoft infrastructure multiple times a day, indicating a growing rise in their activity.
Similar behavior is observed in Sneaky2FA campaigns, commonly hosted at Google Firebase Storage:
As well as at AWS CloudFront:
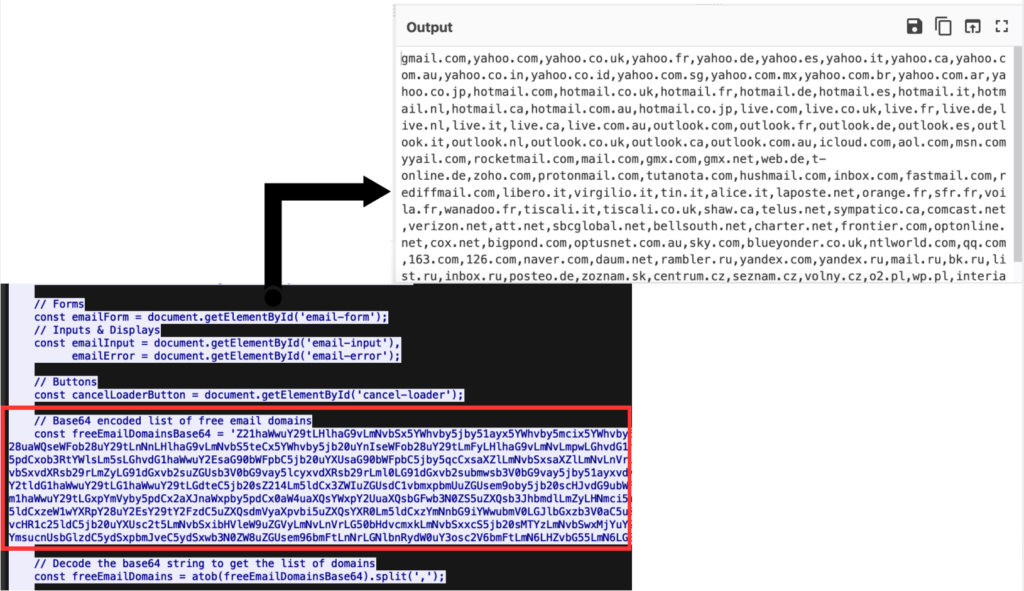
What differentiates Sneaky2FA from Tycoon2FA is its focus on large companies, not mass campaigns. The kit excludes free personal email addresses hosted on gmail.com, yahoo.com, and outlook.com, focusing only on corporate emails.
In addition to Tycoon2FA and Sneaky2FA, EvilProxy also demonstrates similar abuse of trusted cloud platforms:
The underlying strategy is similar and involves hiding malicious activity behind legitimate infrastructure.
Another example of a Microsoft 365 phishing abusing a trusted cloud infrastructure was found among less common phishkits, such as Cephas.
This confirms the trend, which solidifies cloud platform abuse as a standard technique, not a one-off case.
To find more phishing domains based on Microsoft Azure, use the following TI Lookup query:
threatName:”phishing” AND domainName:”*blob.core.windows.net”
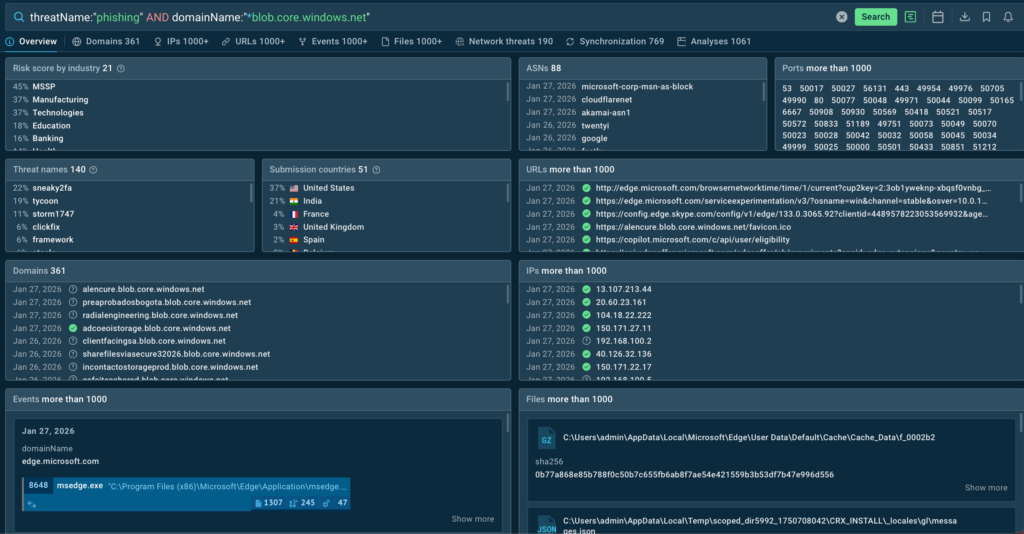
Phishing hosted on trusted cloud infrastructure is becoming increasingly widespread. The risk for large organizations grows daily, and detecting this type of attacks at early stages is made possible through continuous monitoring of phishing campaigns.
ANY.RUN provides this visibility by delivering continuous signature updates and empowering SOC teams in 195 countries to detect sophisticated phishing threats for maximum business protection.
ANY.RUN develops advanced solutions for malware analysis and threat hunting, trusted by 600,000+ cybersecurity professionals worldwide.
Its interactive malware analysis sandbox enables hands-on investigation of threats targeting Windows, Linux, and Android environments. ANY.RUN’s Threat Intelligence Lookup and Threat Intelligence Feeds help security teams quickly identify indicators of compromise, enrich alerts with context, and investigate incidents early. Together, the solutions empowers analysts to strengthen overall security posture at enterprises.
Request ANY.RUN access for your company
Enterprise phishing refers to targeted phishing attacks aimed at corporate users, often designed to steal credentials, session cookies, or gain access to business systems rather than personal accounts.
Attackers host phishing pages on legitimate services like Microsoft Azure Blob Storage, Google Firebase, and Cloudflare, allowing malicious activity to blend in with trusted cloud traffic and evade traditional detection.
Because these attacks use trusted domains, valid HTTPS, and well-known cloud infrastructure, common indicators such as IP addresses, TLS fingerprints, and certificates lose effectiveness.
AiTM (Adversary-in-the-Middle) phishing kits act as real-time proxies between victims and legitimate services, enabling attackers to bypass MFA and steal credentials without raising obvious suspicion.
Tycoon2FA, Sneaky2FA, and EvilProxy are among the most active kits, frequently used in enterprise-focused campaigns abusing trusted cloud and CDN platforms
Traditional tools alone are often insufficient, as modern phishing relies on trusted infrastructure and advanced evasion techniques that bypass static rules and reputation-based detection.
Early detection requires continuous monitoring of phishing campaigns, up-to-date threat intelligence, and behavioral analysis using interactive sandboxing and real-time investigation tools like ANY.RUN.
The post Enterprise Phishing: How Attackers Abuse Microsoft & Google Platforms appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
It’s snow joke – sporting events are a big draw for cybercriminals. Make sure you’re not on the losing side by following these best practices.
WeLiveSecurity – Read More
Not every cybersecurity practitioner thinks it’s worth the effort to figure out exactly who’s pulling the strings behind the malware hitting their company. The typical incident investigation algorithm goes something like this: analyst finds a suspicious file → if the antivirus didn’t catch it, puts it into a sandbox to test → confirms some malicious activity → adds the hash to the blocklist → goes for coffee break. These are the go-to steps for many cybersecurity professionals — especially when they’re swamped with alerts, or don’t quite have the forensic skills to unravel a complex attack thread by thread. However, when dealing with a targeted attack, this approach is a one-way ticket to disaster — and here’s why.
If an attacker is playing for keeps, they rarely stick to a single attack vector. There’s a good chance the malicious file has already played its part in a multi-stage attack and is now all but useless to the attacker. Meanwhile, the adversary has already dug deep into corporate infrastructure and is busy operating with an entirely different set of tools. To clear the threat for good, the security team has to uncover and neutralize the entire attack chain.
But how can this be done quickly and effectively before the attackers manage to do some real damage? One way is to dive deep into the context. By analyzing a single file, an expert can identify exactly who’s attacking his company, quickly find out which other tools and tactics that specific group employs, and then sweep infrastructure for any related threats. There are plenty of threat intelligence tools out there for this, but I’ll show you how it works using our Kaspersky Threat Intelligence Portal.
Let’s say we upload a piece of malware we’ve discovered to a threat intelligence portal, and learn that it’s usually being used by, say, the MysterySnail group. What does that actually tell us? Let’s look at the available intel:
First off, these attackers target government institutions in both Russia and Mongolia. They’re a Chinese-speaking group that typically focuses on espionage. According to their profile, they establish a foothold in infrastructure and lay low until they find something worth stealing. We also know that they typically exploit the vulnerability CVE-2021-40449. What kind of vulnerability is that?
As we can see, it’s a privilege escalation vulnerability — meaning it’s used after hackers have already infiltrated the infrastructure. This vulnerability has a high severity rating and is heavily exploited in the wild. So what software is actually vulnerable?
Got it: Microsoft Windows. Time to double-check if the patch that fixes this hole has actually been installed. Alright, besides the vulnerability, what else do we know about the hackers? It turns out they have a peculiar way of checking network configurations — they connect to the public site 2ip.ru:
So it makes sense to add a correlation rule to SIEM to flag that kind of behavior.
Now’s the time to read up on this group in more detail and gather additional indicators of compromise (IoCs) for SIEM monitoring, as well as ready-to-use YARA rules (structured text descriptions used to identify malware). This will help us track down all the tentacles of this kraken that might have already crept into corporate infrastructure, and ensure we can intercept them quickly if they try to break in again.
Kaspersky Threat Intelligence Portal provides a ton of additional reports on MysterySnail attacks, each complete with a list of IoCs and YARA rules. These YARA rules can be used to scan all endpoints, and those IoCs can be added into SIEM for constant monitoring. While we’re at it, let’s check the reports to see how these attackers handle data exfiltration, and what kind of data they’re usually hunting for. Now we can actually take steps to head off the attack.
And just like that, MysterySnail, the infrastructure is now tuned to find you and respond immediately. No more spying for you!
Before diving into specific methods, we need to make one thing clear: for attribution to actually work, the threat intelligence provided needs a massive knowledge base of the tactics, techniques, and procedures (TTPs) used by threat actors. The scope and quality of these databases can vary wildly among vendors. In our case, before even building our tool, we spent years tracking known groups across various campaigns and logging their TTPs, and we continue to actively update that database today.
With a TTP database in place, the following attribution methods can be implemented:
Identifying TTPs during dynamic analysis is relatively straightforward to implement; in fact, this functionality has been a staple of every modern sandbox for a long time. Naturally, all of our sandboxes also identify TTPs during the dynamic analysis of a malware sample:
The core of this method lies in categorizing malware activity using the MITRE ATT&CK framework. A sandbox report typically contains a list of detected TTPs. While this is highly useful data, it’s not enough for full-blown attribution to a specific group. Trying to identify the perpetrators of an attack using just this method is a lot like the ancient Indian parable of the blind men and the elephant: blindfolded folks touch different parts of an elephant and try to deduce what’s in front of them from just that. The one touching the trunk thinks it’s a python; the one touching the side is sure it’s a wall, and so on.
The second attribution method is handled via static code analysis (though keep in mind that this type of attribution is always problematic). The core idea here is to cluster even slightly overlapping malware files based on specific unique characteristics. Before analysis can begin, the malware sample must be disassembled. The problem is that alongside the informative and useful bits, the recovered code contains a lot of noise. If the attribution algorithm takes this non-informative junk into account, any malware sample will end up looking similar to a great number of legitimate files, making quality attribution impossible. On the flip side, trying to only attribute malware based on the useful fragments but using a mathematically primitive method will only cause the false positive rate to go through the roof. Furthermore, any attribution result must be cross-checked for similarities with legitimate files — and the quality of that check usually depends heavily on the vendor’s technical capabilities.
Our products leverage a unique database of malware associated with specific hacking groups, built over more than 25 years. On top of that, we use a patented attribution algorithm based on static analysis of disassembled code. This allows us to determine — with high precision, and even a specific probability percentage — how similar an analyzed file is to known samples from a particular group. This way, we can form a well-grounded verdict attributing the malware to a specific threat actor. The results are then cross-referenced against a database of billions of legitimate files to filter out false positives; if a match is found with any of them, the attribution verdict is adjusted accordingly. This approach is the backbone of the Kaspersky Threat Attribution Engine, which powers the threat attribution service on the Kaspersky Threat Intelligence Portal.
Kaspersky official blog – Read More

For many residents in Perth, finding a rental has become a high-stakes challenge. As demand for housing surges, a troubling trend has just been revealed. An Australian housing scam preying on renters who are willing to stretch every dollar to secure a roof over their heads. These rent scams, often orchestrated by individuals posing as private landlords on online platforms like Facebook Marketplace, have left victims financially and emotionally drained.
The scheme typically begins with a seemingly genuine rental listing. Scammers steal photos from legitimate properties and post them online, offering rent well below the market rate. In Perth, median rental prices are at historic highs, with houses averaging $700 per week and units $670. Scammers exploit this stress by pitching “exclusive” opportunities that seem almost too good to be true.
Messages from these fraudsters are carefully crafted to manipulate potential tenants. One such message promises that the apartment will be “reserved exclusively only for you” in exchange for a security deposit or “commitment fee” of just a few hundred dollars. The deposit is presented as fully refundable or deductible from the first week’s rent. In reality, once the money is transferred, the scammer vanishes, leaving victims without the property and out of pocket.
WA Commissioner for Consumer Protection, Trish Blake, describes the situation as a “perfect playground for scammers.” She explains that the perpetrators often groom their targets by appealing to their sense of urgency and personal integrity, portraying themselves as allies to those struggling in the rental market. “They’ll tell you that you’re a real battler, that you’re a good person, and that they want to help you out,” Blake said, as reported by Nine News.
The scale of the problem is growing. In 2025, WA ScamNet, part of the Department of Local Government, Industry Regulation and Safety, documented 20 cases of rental scams, totaling losses of $51,875, a 27 percent increase from the previous year. Scammers typically provide a property address for drive-by inspections but evade any requests for in-person viewings. To add credibility, fake rental agreements featuring official logos may be used, and tenants are pressured to pay via bank transfer, bypassing safer, traceable channels.
Rob Mandanici, a member of the Real Estate Institute of Western Australia, stresses the emotional pressure on renters. “People have pure desperation, and they will do what they can for their family, thinking they’re doing the right thing while potentially dealing with unsavoury characters,” he said.
Commerce Minister Dr. Tony Buti noted the heartbreak of seeing renters targeted in this way. “It is particularly heartbreaking to see scammers targeting renters because they know they are under pressure and may take risks to secure a property,” he said. He advises tenants to insist on inspecting the property in person and to treat unusually cheap rent as a red flag.
Several factors make Perth an ideal environment for this type of Australian housing scam. Rental vacancies are low, demand is high, and properties are snatched quickly, often in as little as 16 days. This scarcity creates a sense of urgency among renters, which scammers exploit.
The Cook Government has issued repeated warnings to Western Australian tenants to remain vigilant, especially when dealing with private landlords or online marketplaces. Inspecting the property before paying, verifying the landlord’s identity, and consulting licensed real estate agents are critical protection methods.
Several practical tips to avoid falling victim to rental scams include:
Scams can be reported through the WA ScamNet website, or further guidance on rent is available via the Consumer Protection website. The Australian housing scam in Perth is more than a financial threat; it exploits human vulnerability in a market under immense pressure.
Renters finding high prices and fierce competition must combine caution with diligence, balancing urgency with verification. While there is no substitute for careful vetting, awareness and education remain the most effective defense against campaigns like the Australian housing scam.
The post Desperate Perth Renters Targeted by Rising Australian Housing Scam appeared first on Cyble.
Cyble – Read More