Margin vs. Madness: Fixing MSSP Top 5 Operational Nightmares
Leading a managed security services provider has never been a comfortable job. And it isn’t now, though the demand for MSSPs has never been higher. The global threat landscape is expanding faster than most enterprise security teams can keep pace with, and organizations across every sector are turning to managed providers to fill the gap.
For MSSP leaders, this looks like an opportunity. And it is. The problem is that seizing it costs more than it used to.
Key Points
- Linear scaling kills margins.
Adding more clients traditionally requires proportionally more analysts, making profitable growth nearly impossible.
- Alert noise is expensive.
Up to 70% of alerts are false positives that waste analyst time and inflate operational costs.
- Context gaps slow everything down.
Disconnected tools force manual aggregation of data from multiple systems, delaying investigations.
- Tool switching destroys efficiency.
Constant platform hopping increases turnaround time and contributes to missed SLAs.
- Standardization is essential for multi-client environments.
Every client being unique creates bespoke processes that do not scale and accelerate analyst burnout.
- ANY.RUN’s Threat Intelligence (TI Lookup + TI Feeds) and Interactive Sandbox work as an integrated infrastructure layer that reduces manual labor and improves unit economics.
- True scalability comes from automation and shared context.
MSSPs can serve more clients at higher quality without linear headcount increases, while lowering stress and turnover.
The quiet storm inside every MSSP
Threat actors automate attacks at unprecedented speed, while client environments grow more complex and diverse. MSSP leaders face mounting pressure to deliver faster, deeper, and more reliable protection across dozens or hundreds of customers: all while keeping margins healthy and SLAs intact.
- More clients still often means more analysts;
- More alerts still means more noise;
- More data still doesn’t mean more clarity.
Meanwhile, the analysts carrying the weight are burning out. Turnover in MSSP analyst roles is among the highest in the industry, creating a perpetual cycle of recruitment, onboarding, and knowledge loss that compounds every other problem.
MSSP leaders aren’t looking for “another feature.” They’re looking for something closer to an operational backbone. Something that reduces manual effort and improves unit economics without adding complexity.
1. Linear Growth Equals Margin Death: The Scalability Trap
For many MSSPs, growth is a paradox: every new client increases revenue — but also operational cost at nearly the same rate. Hiring, training, and retaining talent is expensive and painful, with turnover creating constant friction. The more manual the work your analysts do per client, the harder it is to decouple revenue from headcount.
Your revenue line and your cost line climb together, and the margin in between never quite widens the way a growth business should.
How ANY.RUN helps
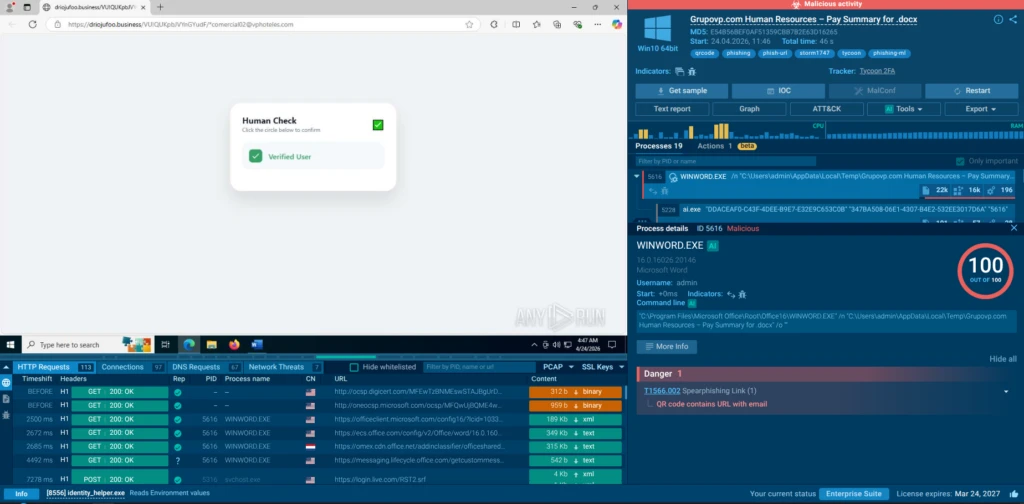
The Interactive Sandbox directly attacks the cost-per-investigation problem by compressing deep malware analysis from hours to minutes and speeding up triage, so each analyst can handle significantly more cases without sacrificing quality or output depth.
To see how the Sandbox automatically interacts with malware detonating the kill chain elements and eliminating the need for manual interventions for a malware analyst, view an analysis session:
Threat Intelligence Lookup removes repetitive investigation steps by providing instant access to previously analyzed artifacts, indicators, and behaviors. It supports quick search across a huge database of contextual data on indicators and attacks drawn from sandbox investigations of over 15K SOC teams that are using ANY.RUN.
Together, these solutions shift effort from linear human scaling to knowledge reuse and automation. Analysts spend less time rebuilding context and more time making decisions.

2. Alert Noise Equals Wasted Money
With up to 70% of alerts representing noise, MSSPs burn resources investigating false positives. Every unnecessary alert translates into extra analyst time, higher operational costs, and increased risk of missing genuine threats amid the fatigue.
The downstream effects compound quickly. Analysts fatigued by noise start to triage faster and less carefully. Real threats get downgraded. Critical detections get buried under the volume. The service quality the MSSP is paid to deliver degrades — quietly, then suddenly.
How ANY.RUN helps
ANY.RUN Threat Intelligence — comprising TI Lookup and Threat Intelligence Feeds — puts a verification and enrichment layer in front of the analyst queue, so that the 70% that doesn’t matter gets filtered before it consumes investigation resources, and the 30% that does matter arrives with actionable context.
- Cuts false positive handling time;
- Raises triage confidence;
- Reduces analyst fatigue across multi-client environments;
- Feeds directly into SIEM and SOAR workflows.
TI Lookup provides on-demand, deep queries across a continuously updated database of threats, allowing an analyst to determine in seconds whether a suspicious IP, domain, file hash, or URL is genuinely malicious, benign, or requires deeper analysis.
destinationIP:”103.224.212.211″
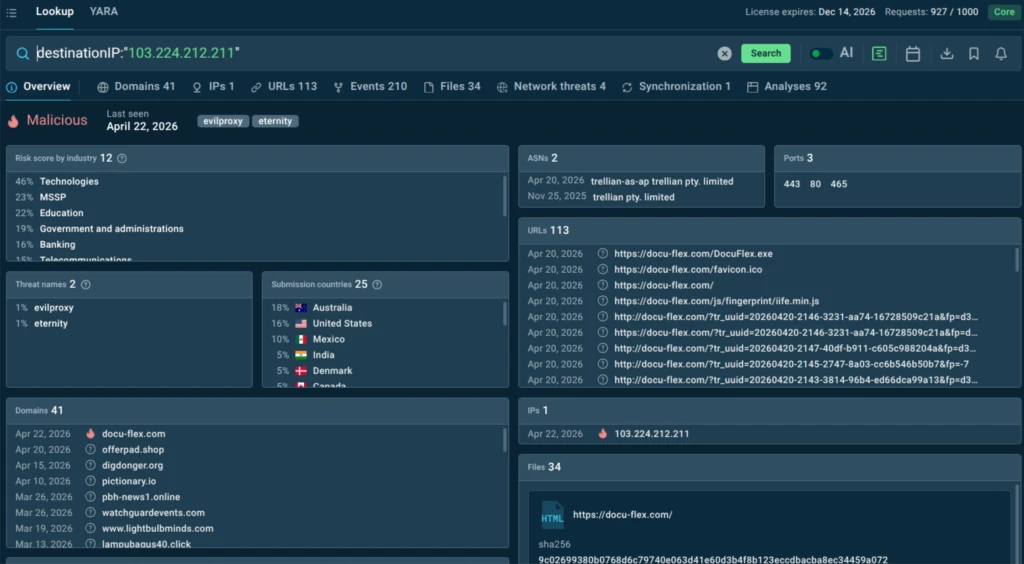
TI Feeds deliver structured, high-fidelity threat data enriched with behavioral context that integrates directly into SIEM and SOAR workflows.
Instead of raw indicator lists that require manual validation, analysts receive intelligence that has already been correlated with real-world malware behavior observed in the Sandbox. The noise doesn’t just get filtered; it gets explained. Analysts spend time on what matters, and triage decisions become faster and more defensible.
3. Missing Context: The Manual Puzzle Problem
An MSSP analyst’s work happens across a fractured landscape. Threat intelligence feeds live in one place. SIEM alerts in another. Endpoint telemetry in a third. Sandboxing results in a fourth. An analyst responding to an incident doesn’t get the full picture handed to them. They construct it, manually, by pulling data from multiple sources, correlating it in their head or in a spreadsheet, and hoping nothing slips through the cracks.
This manual context assembly is slow, error-prone, and analyst-dependent. Investigations that should take minutes take hours. And in a threat landscape where speed matters, fragmented context is a liability that shows up in missed detections and broken SLAs.
How ANY.RUN helps
ANY.RUN collapses the distance between intelligence and action by delivering investigation context as a connected whole, giving MSSPs faster incident resolution, less analyst-dependent knowledge, and investigation outputs that hold their value even when team composition changes.
- Eliminates manual context assembly;
- Connects intelligence to behavior;
- Reduces investigation time per incident.
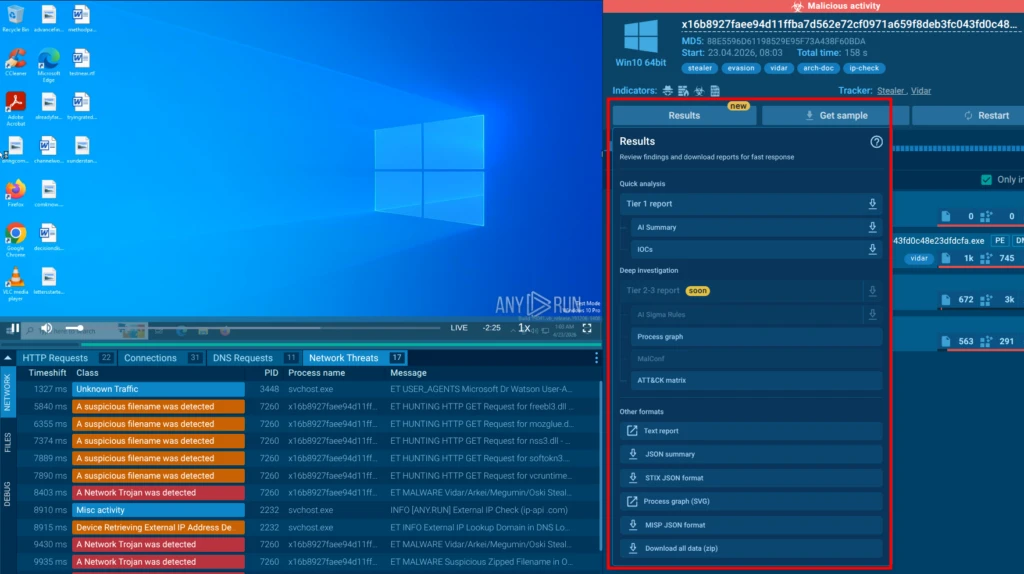
ANY.RUN’s modules are designed for seamless integration and context sharing. The Interactive Sandbox delivers comprehensive behavioral data in one place: processes, network activity, MITRE ATT&CK mappings, and more. TI Lookup instantly correlates any indicator (IOC, IOA, or IOB) with related threats, full attack chains, and supporting sandbox reports. TI Feeds extend this intelligence across the entire stack, feeding enriched data into existing workflows.

Analysts no longer “build the picture manually.” They access unified, actionable intelligence that accelerates triage, investigation, and reporting across all clients, reducing context gaps and enabling consistent, high-quality outcomes. The investigation pipeline becomes a connected workflow rather than a manual collage.
4. Tool-Switching: The Hidden Time Tax
Constantly jumping between platforms kills efficiency and extends turnaround times. Analysts lose momentum with every tab switch, every login, and every manual data transfer, directly impacting SLA compliance and team morale.
When tools are slow, unreliable, or disconnected, analysts route around them. They rely on memory, on informal knowledge-sharing, on workarounds. All of it introduces inconsistency and risk.
How ANY.RUN Helps
ANY.RUN’s API-first architecture is built to disappear into the workflows analysts already use, surfacing intelligence in the context where work is happening, rather than requiring analysts to pivot toward it. The result is less friction, higher adoption, and more consistent investigation quality across the team.
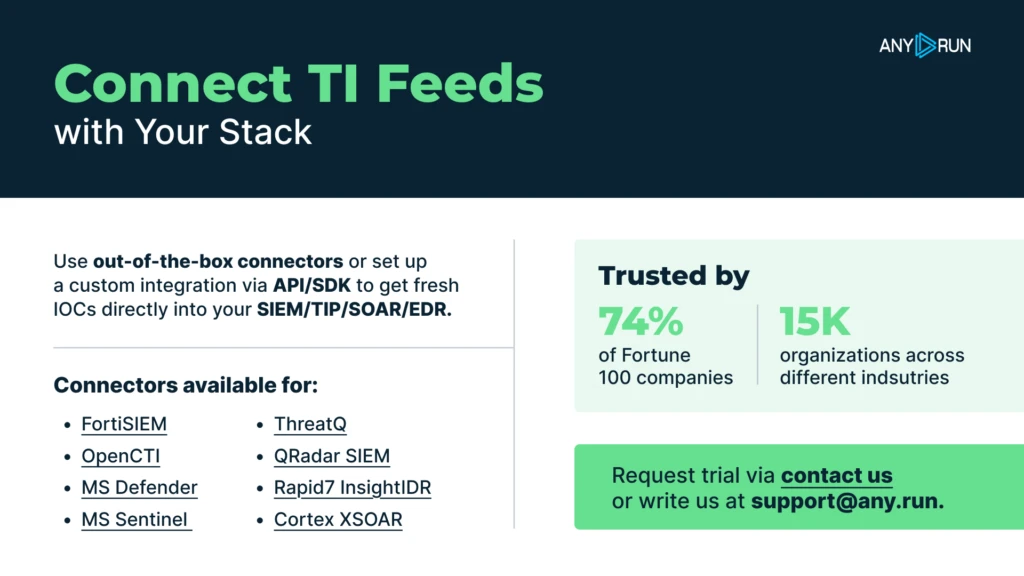
TI Lookup and TI Feeds can be embedded directly into SIEM, SOAR, and ticketing environments, so analysts can surface intelligence without leaving the context they’re already working in. The Interactive Sandbox can be invoked as part of an automated or semi-automated investigation pipeline, with results returned in structured, machine-readable formats that feed directly into case management.
The goal is to make ANY.RUN invisible in the best sense: present at every stage of investigation, without requiring analysts to pivot their attention toward it.
5. No Standardization — Scaling Chaos Across Clients
No two MSSP clients are alike. One runs a legacy on-premises environment with minimal telemetry. Another is cloud-native with dozens of SaaS integrations. A third has custom applications, bespoke logging configurations, and a security team with strong opinions about how investigations should be documented. For the MSSP trying to serve all three, the challenge isn’t just operational: it’s structural.
When client environments are siloed, institutional knowledge about one doesn’t transfer to another. When investigation workflows differ by engagement, onboarding new analysts takes longer, errors are harder to catch, and QA becomes a guessing game. What scales, in the absence of standardization, is chaos. And chaos has a cost.
How ANY.RUN helps
ANY.RUN Threat Intelligence was built with multi-tenant MSSP operations in mind.
- Normalizes intelligence across client environments;
- Gives analysts a single investigative interface;
- Standardizes investigation outputs;
- Shortens analyst onboarding.
TI Feeds deliver structured, consistently formatted intelligence that can be normalized and applied across client environments without per-client customization of the data layer.
TI Lookup gives analysts a single investigative interface regardless of which client environment they’re working in. And the Interactive Sandbox produces structured, reproducible analysis outputs — process trees, network maps, MITRE mappings, IOC exports — that can be templated into client-specific reporting workflows without requiring analysts to rebuild their investigation approach from scratch each time.
Standardization doesn’t mean treating every client the same. It means having a consistent intelligence layer beneath the client-specific details, so that quality and speed hold constant even as the client roster grows.
Analyst burnout (the pain that amplifies all others)
When systems don’t scale, people absorb the pressure. Overload, repetitive work, constant alert fatigue — this is where everything converges.
Burnout isn’t just a people problem. It’s an operational risk:
- Higher turnover;
- Knowledge loss
- Reduced investigation quality
How ANY.RUN helps
By reducing noise, minimizing manual work, and accelerating investigations, the combined capabilities of Interactive Sandbox, TI Lookup, and TI Feeds directly lower cognitive and operational pressure. Analysts move from reactive overload to structured, efficient workflows.
Conclusion: What MSSPs Are Actually Looking For
The pains above are not independent problems. They are interconnected symptoms of the same underlying condition: MSSP operations that have scaled their client load without scaling the intelligence infrastructure underneath it.
MSSPs don’t need more isolated features. They need:
- Less manual aggregation;
- Less switching;
- More context, faster;
- Reliable, always-available capabilities;
- Infrastructure that improves margins, not just performance.
When Threat Intelligence Lookup and Threat Intelligence Feeds operate as a unified threat intelligence layer, and Interactive Sandbox feeds it with fresh behavioral data, the result isn’t just efficiency. It’s a shift in how MSSPs operate: from effort-heavy scaling to intelligence-driven scaling.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams investigate threats faster and with greater clarity across modern enterprise environments.
It allows teams to safely execute suspicious files and URLs, observe real behavior in an Interactive Sandbox, enrich indicators with immediate context through TI Lookup, and monitor emerging malicious infrastructure using Threat Intelligence Feeds. Together, these capabilities help reduce investigation uncertainty, accelerate triage, and limit unnecessary escalations across the SOC.
ANY.RUN is trusted by thousands of organizations worldwide and meets enterprise security and compliance expectations. It is SOC 2 Type II certified, demonstrating its commitment to protecting customer data and maintaining strong security controls.
FAQ
The biggest pains include linear headcount scaling, high alert noise (up to 70%), missing context, constant tool switching, lack of standardization across clients, and resulting analyst burnout and turnover.
By combining Threat Intelligence and the Interactive Sandbox, ANY.RUN dramatically reduces time spent on triage and investigation, allowing the same team to handle more clients effectively while maintaining or improving service quality.
Yes. TI Feeds deliver high-confidence, low-noise IOCs, while TI Lookup and Sandbox analysis provide rapid behavioral context that helps filter genuine threats from noise.
The Interactive Sandbox reveals full attack behavior, and TI Lookup instantly correlates indicators with rich, real-world intelligence — all in one integrated workflow instead of manual collection across tools.
Yes. It supports strong client isolation and centralized management, replacing manual separation processes with reliable, scalable infrastructure.
The Interactive Sandbox and Threat Intelligence deliver quick turnaround times, often in seconds to minutes, helping MSSPs comfortably meet aggressive SLAs (typically ~1 hour for initial analysis).
The post Margin vs. Madness: Fixing MSSP Top 5 Operational Nightmares appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
