UAT-4356’s Targeting of Cisco Firepower Devices

Cisco Talos is aware of UAT-4356‘s continued active targeting of Cisco Firepower devices’ Firepower eXtensible Operating System (FXOS). UAT-4356 exploited n-day vulnerabilities (CVE-2025-20333 and CVE-2025-20362) to gain unauthorized access to vulnerable devices, where the threat actor deployed their custom-built backdoor dubbed “FIRESTARTER.” FIRESTARTER considerably overlaps with the technical capabilities of RayInitiator’s Stage 3 shellcode that processes incoming XML-based payloads to endpoint APIs.
In early 2024, Cisco Talos attributed ArcaneDoor, a state-sponsored campaign focused on gaining access to network perimeter devices for espionage, to UAT-4356.
Customers are advised to refer to Cisco’s Security Advisory for mitigation and detection guidance, indicators of compromise (IOCs), affected products, and applicable software upgrade recommendations.
The FIRESTARTER backdoor
FIRESTARTER is a malicious backdoor implanted by UAT-4356 that allows remote access and control to execute arbitrary code inside the LINA process, a core component of Cisco’s ASA and FTD appliances running FXOS.
Persistence
UAT-4356 established persistence for FIRESTARTER on compromised devices by manipulating the mount list for Cisco Service Platform (CSP), namely “CSP_MOUNT_LIST”, to execute FIRESTARTER. The mount list allows programs and commands to be executed as part of the device’s boot sequence. The persistence mechanism triggers during graceful reboot (i.e., when a process termination signal is received). FIRESTARTER also checks the runlevel for value 6 (indicating device reboot) and in case of a match, writes itself to backup location “/opt/cisco/platform/logs/var/log/svc_samcore.log” and updates the CSP_MOUNT_LIST to copy itself back to “/usr/bin/lina_cs” and then be executed. When FIRESTARTER runs after a reboot, it restores the original CSP_MOUNT_LIST and removes the trojanized copy. Because the runlevel triggers establishment of this transient persistence mechanism, a hard reboot (for example, after the device has been unplugged from power) effectively removes the implant from the device.
FIRESTARTER has used the following commands to establish persistence for itself using the transient persistence mechanism:
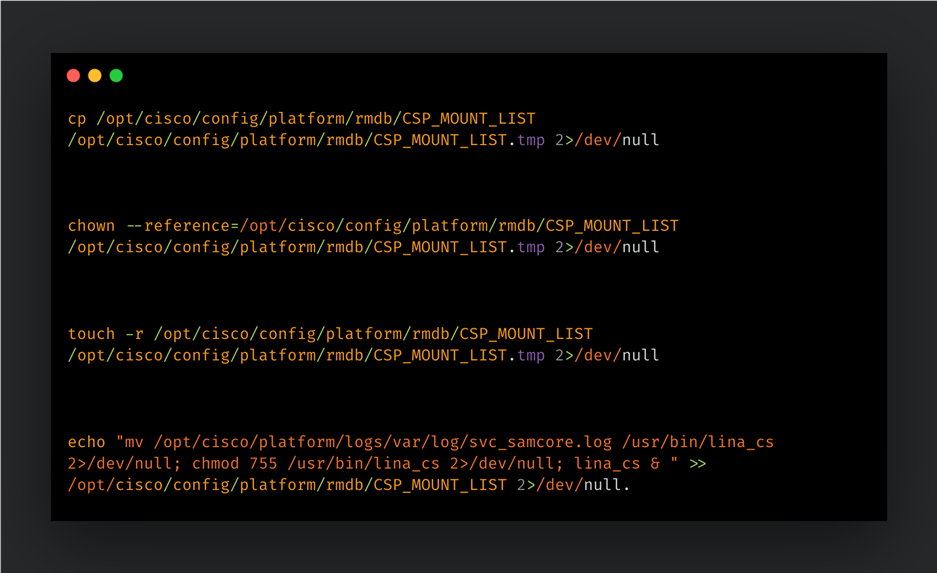
When the implant injects itself into the LINA process, it removes the traces of its persistence mechanism by restoring the CSP_MOUNT_LIST from a temporary copy (“CSP_MOUNTLIST.tmp”), then removing the temporary copy and the FIRESTARTER file from disk (“/usr/bin/lina_cs”).
FIRESTARTER’s backdoor capabilities
FIRESTARTER can run arbitrary shellcode received by the device. A pre-defined handler function specified by a hardcoded offset in the LINA process’ memory is replaced by an unauthorized handler routine that parses the data being served to it. FIRESTARTER specifically looks for a WebVPN request XML. If the request data received matches a specific pattern of custom-defined prefixing then the shellcode that immediately follows it is executed in memory. If the prefixing bytes are not found, then the data is treated as regular request data and passed to the original handler function (if any).
FIRESTARTER’s loading mechanism, Stage 2 shellcode (i.e., the actual request handler component), handler function replacement, XML parsing for magic bytes, and final payload execution display considerable overlaps with RayInitiator’s Stage 3 deployment actions and accompanying artifacts.
Injecting and activating the malicious shellcode in LINA
FIRESTARTER first reads the LINA process’ memory to search for and verify the presence of the bytes (long) 0x1, 0x2, 0x3, 0x4, 0x5 at specific locations in memory. If found, FIRESTARTER will then query the process’ memory to find an “r-xp” memory range for the shared library “libstdc++.so”. It then copies the next stage shellcode (Stage 2) to the last 0x200 bytes of the memory region. FIRESTARTER then overwrites an internal data structure in the LINA process’ memory to replace a pointer to a WebVPN-specific, legitimate XML handler function with the address of the malicious Stage 2 shellcode.
The malicious shellcode is triggered as part of the authentication API’s request handling process and parses the incoming request data for magic markers signifying an executable payload. If found, the executable payload is then executed on the compromised device.
Detection guidance
The presence of the following artifacts – specifically the filenames “lina_cs” and “svc_samcore.log” – though somewhat brittle indicators, may indicate the presence of the FIRESTARTER on a Firepower device:
- Any output from the commands:
- show kernel process | include lina_cs
- The presence of the following files on disk:
- /usr/bin/lina_cs
- /opt/cisco/platform/logs/var/log/svc_samcore.log
For more comprehensive detection guidance, please refer to Cisco’s Security Advisory here. Please also refer to CISA’s update to V1: Emergency Directive (ED) 25-03: Identify and Mitigate Potential Compromise of Cisco Devices and FIRESTARTER Backdoor Malware Analysis Report for more information and guidance.
Mitigation and coverage
We recommend that Cisco customers follow the steps recommended in Cisco’s advisory, with particular attention to any applicable software upgrade recommendations. Organizations impacted can initiate a TAC request for Cisco support.
A FIRESTARTER infection may be mitigated on all affected devices by reimaging the devices.
On Cisco FTD software that is not in lockdown mode, there is also the option of killing the lina_cs process then reloading the device:
> expert $ sudo kill -9 $(pidof lina_cs) $ exit > reload
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org.
The following Snort rules cover the vulnerabilities CVE-2025-20333 and CVE-2025-20362: 65340, 46897.
Snort rules covering FIRESTARTER: 62949
The following ClamAV signatures detect this threat: Unix.Malware.Generic-10059965-0
Cisco Talos Blog – Read More


