The Q1 vulnerability pulse

Welcome to this week’s edition of the Threat Source newsletter.
The first quarter of 2026 passed faster than a misconfigured firewall rule gets exploited — and the last few weeks have been firmly stamped with the “software supply chain compromise” label, with headlines surrounding incidents involving Trivy,Checkmark, LiteLLM, telnyx and axios. This edition stays focused on vulnerability statistics, although you can view Dave and Nick’s Talos blogs for more information about these incidents.
Known Exploited Vulnerabilities (KEVs) stayed roughly in line with 2025 numbers — no dramatic spike, but no room for relief either.
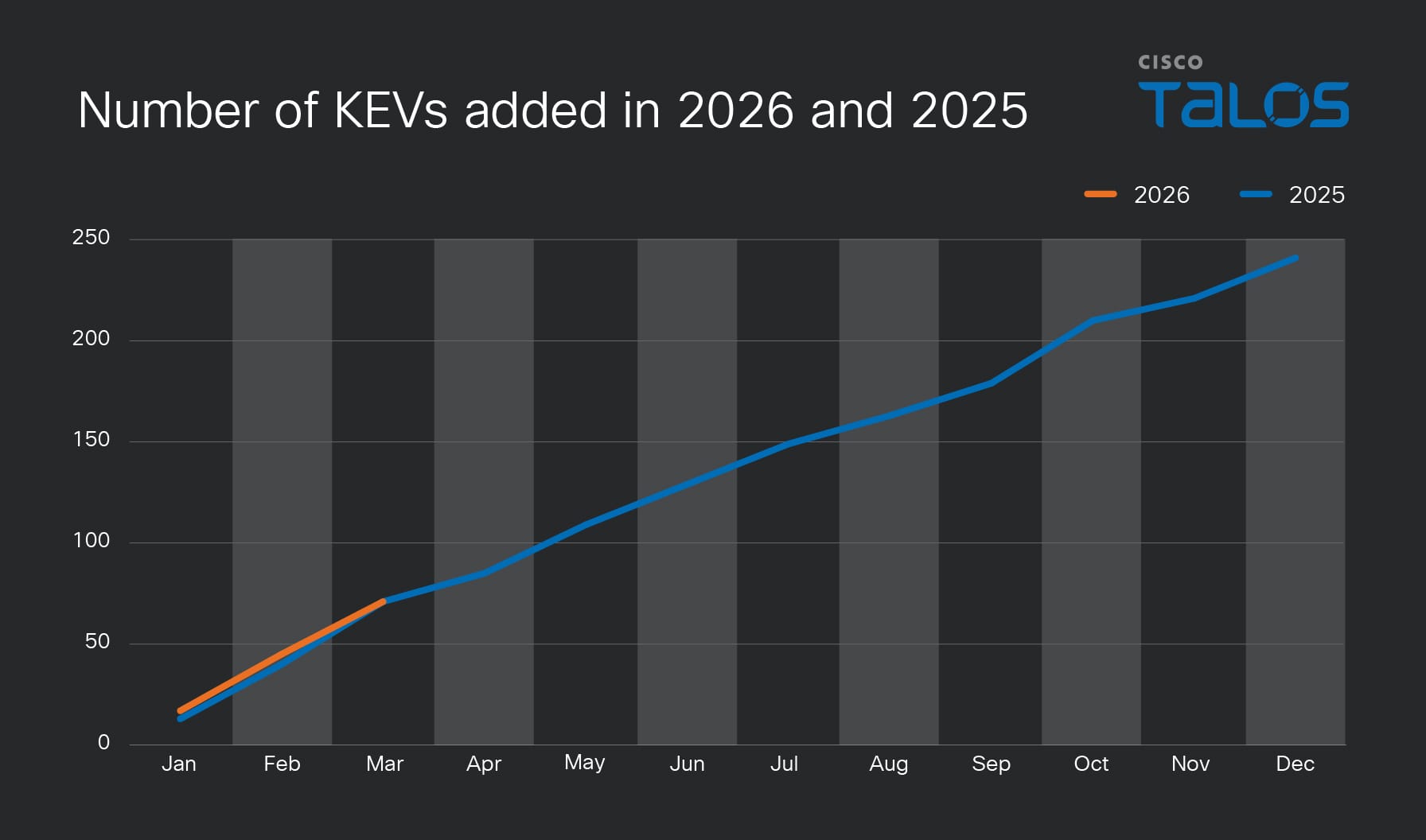
What does stand out? Networking gear accounted for 20% of KEV-related vulnerabilities, and that number is expected to climb as the year progresses. If the trend from 2025 holds, this won’t be the high-water mark.
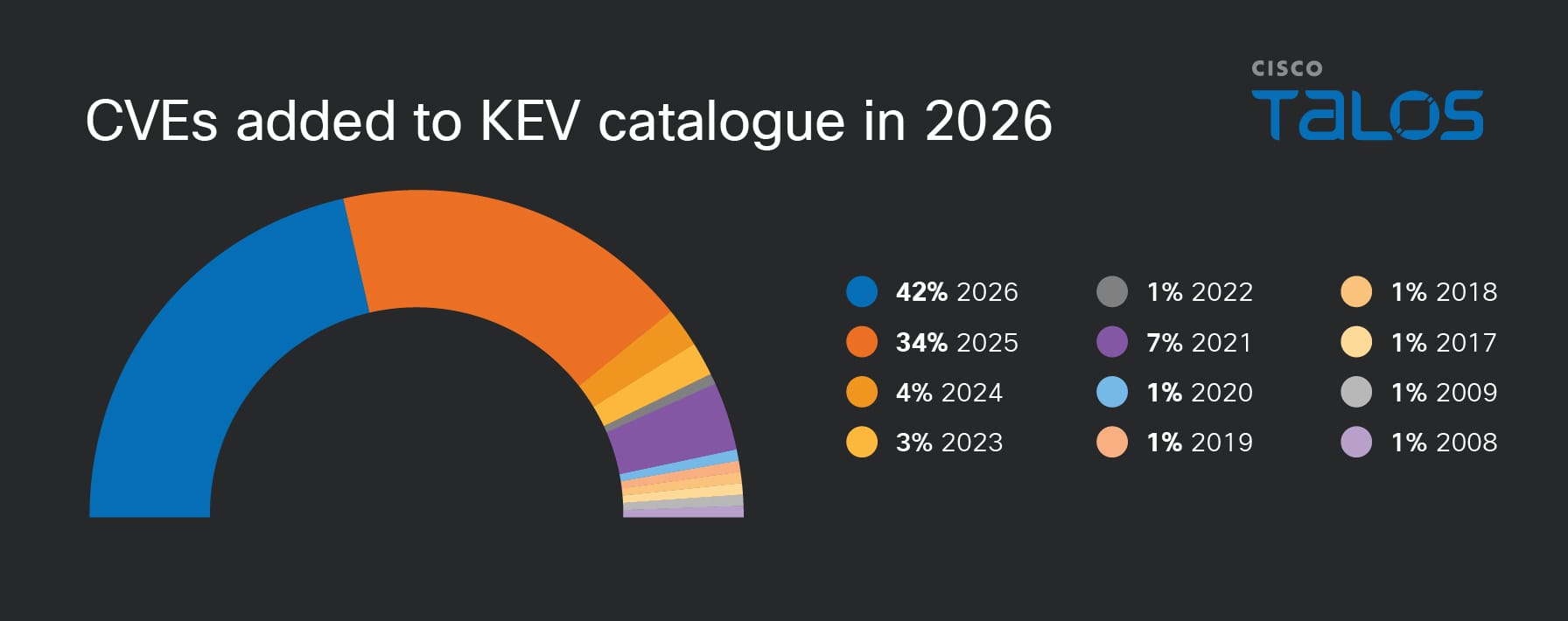
Patch management remains one of the industry’s most persistent challenges, and I understand all the operational complexity that comes with it. That said, it still stings to come across CVEs with disclosure dates reaching back to 2009 — and roughly 25% of the CVEs we’re tracking date to 2024 or earlier. Old vulnerabilities don’t retire. They wait. It starts with visibility: Knowing what’s actually running in your environment is the prerequisite for everything else.
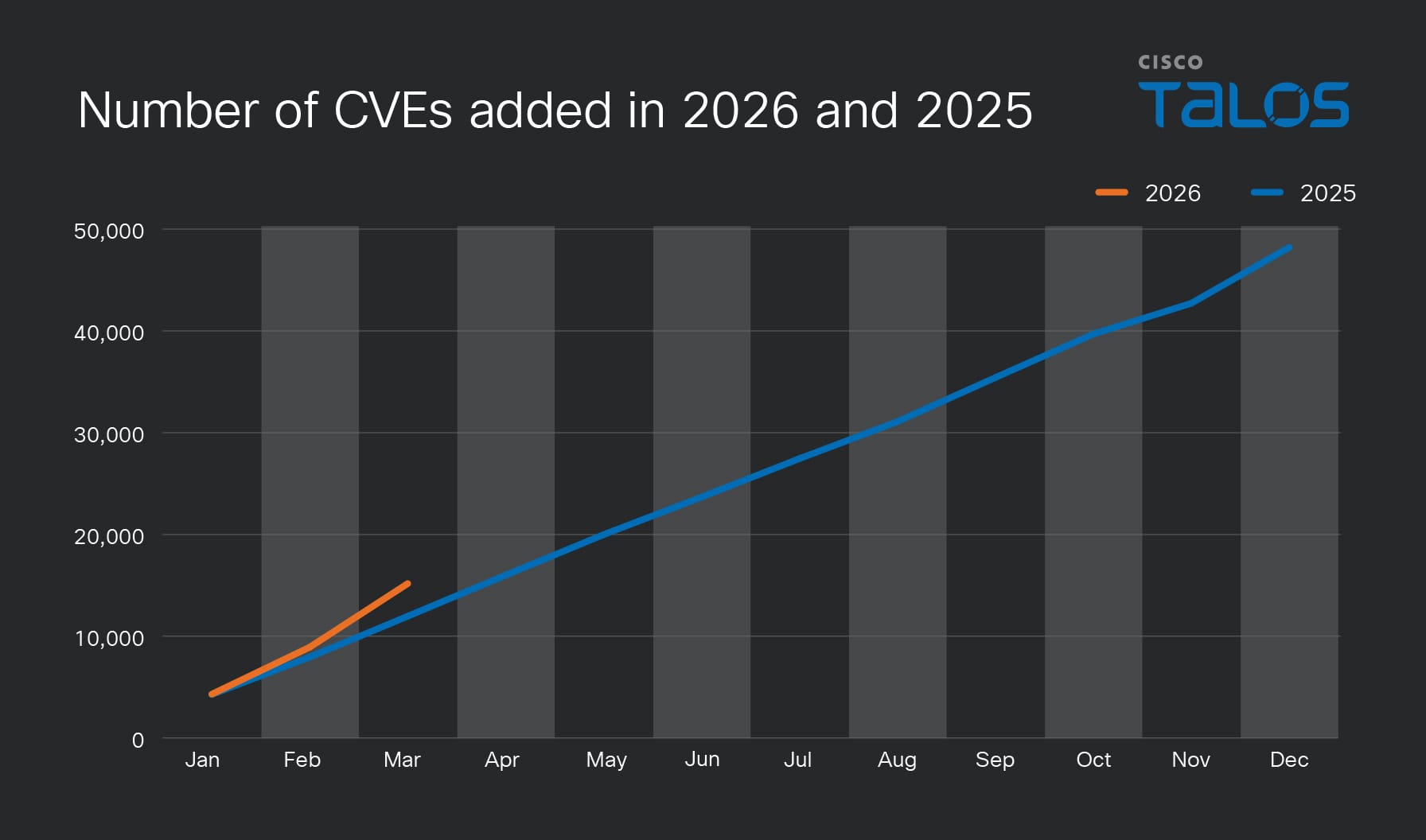
Overall CVE counts increased in Q1, with March showing the sharpest climb. Whether that reflects improved disclosure pipelines, increased researcher activity, ora genuine uptick in vulnerability density, the trend line from 2025 hasn’t flattened — if anything, it’s still pointing up.
Using the keyword methodology described here, 121 CVEs with AI relevance were identified in Q1 — more than Q1 2025, though consistent with what adoption trends would predict. As AI components become more deeply embedded across the software stack, this number will keep climbing.
Given the recent developments with models like the Mythos preview and the industry teaming up in initiatives like Project Glasswing, I’m curious how the trajectory will change moving forward. If you haven’t read about it:
“During our testing, we found that Mythos Preview is capable of identifying and then exploiting zero-day vulnerabilities in every major operating system and every major web browser when directed by a user to do so.” – Anthropic Frontier Red Team
That’s a substantial capability jump in agentic coding and reasoning, which eventually needs to be implemented early in the development lifecycle. And as Anthony points out, those capabilities will become available to adversaries. Read Cisco’s guidance on defending in the age of AI-enabled attacks for more.
Will we see fewer CVEs or even more negative times-to-exploit (TTEs)?
It’s on us. Defenders need to get ahead of the adversaries, and at the same time, we need to pay attention to (sometimes decade-old) vulnerabilities.
The one big thing
Cisco Talos has identified a significant increase in the abuse of n8n, an AI workflow automation platform, to facilitate malicious campaigns including malware delivery and device fingerprinting. Attackers are weaponizing the platform’s URL-exposed webhooks to create phishing lures that bypass traditional security filters by leveraging trusted, legitimate infrastructure. By masking malicious payloads as standard data streams, these campaigns effectively turn productivity tools into delivery vehicles for remote access trojans and other cyber threats.
Why do I care?
The abuse of legitimate automation platforms exploits the inherent trust organizations place in these tools, which often neutralizes traditional perimeter-based security defenses. Because these platforms are designed for flexibility and seamless integration, they allow attackers to dynamically tailor payloads and evade detection through standard reputation-based filtering.
So now what?
Move beyond static domain blocking and implement behavioral detection that alerts on anomalous traffic patterns directed toward automation platforms. Restrict endpoint communication with these services to only those explicitly authorized by the organization’s established internal workflows. Finally, utilize AI-driven email security solutions to analyze the semantic intent of incoming messages and proactively share indicators of compromise, such as specific webhook structures, with threat intelligence communities.
Top security headlines of the week
Adobe patches actively exploited zero-day that lingered for months
Adobe patched an arbitrary code execution vulnerability in the latest versions of its Acrobat and Reader for Windows and macOS, nearly four months after an attacker first appeared to have begun exploiting it. (Dark Reading)
Fake Claude website distributes PlugX RAT
A threat actor created a site that hosts a download link pointing to a ZIP archive allegedly containing a pro version of the LLM. (SecurityWeek)
Sweden blames Russian hackers for attempting “destructive” cyber attack on thermal plant
Sweden’s minister of civil defense said during a press conference on Wednesday that the attempted attack happened in early 2025 and attributed the incident to hackers with “connections to Russian intelligence and security services.” (TechCrunch)
FBI and Indonesian police dismantle W3LL phishing network behind $20M fraud attempts
The W3LL phishing kit, advertised for a fee of about $500, allowed criminals to mimic legitimate login pages to deceive victims into handing over their credentials, allowing the attackers to seize control of their accounts. (The Hacker News)
Google API keys in Android apps expose Gemini endpoints to unauthorized access
Armed with the key, an attacker could access private files and cached content, make arbitrary Gemini API calls, exhaust API quotas and disrupt legitimate services, and access any data on Gemini’s file storage. (SecurityWeek)
Can’t get enough Talos?
More than pretty pictures: Wendy Bishop on visual storytelling in tech
From her early beginnings in web design and journalism to leading the creative vision for Talos, Wendy talks about the unique challenges and rewards of bridging the gap between artistic expression and highly technical research.
PowMix botnet targets Czech workforce
Cisco Talos discovered an ongoing malicious campaign affecting Czech workers with a previously undocumented botnet we call “PowMix.” It employs random beaconing intervals to evade the network signature detections.
APTs: Different objectives, similar access paths
Across the Talos 2025 Year in Review, state-sponsored threat activity from China, Russia, North Korea, and Iran all had varying motivations, such as espionage, disruption, financial gain, and geopolitical influence.
Upcoming events where you can find Talos
- PIVOTcon (May 6 – 8) Málaga, Spain
- OffensiveCon (May 15 – 16) Berlin, Germany
Most prevalent malware files from Talos telemetry over the past week
SHA256: 9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507
MD5: 2915b3f8b703eb744fc54c81f4a9c67f
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507
Example Filename: VID001.exe
Detection Name: Win.Worm.Coinminer::1201**
SHA256: 96fa6a7714670823c83099ea01d24d6d3ae8fef027f01a4ddac14f123b1c9974
MD5: aac3165ece2959f39ff98334618d10d9
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=96fa6a7714670823c83099ea01d24d6d3ae8fef027f01a4ddac14f123b1c9974
Example Filename: d4aa3e7010220ad1b458fac17039c274_63_Exe.exe
Detection Name: W32.Injector:Gen.21ie.1201
SHA256: 90b1456cdbe6bc2779ea0b4736ed9a998a71ae37390331b6ba87e389a49d3d59
MD5: c2efb2dcacba6d3ccc175b6ce1b7ed0a
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=90b1456cdbe6bc2779ea0b4736ed9a998a71ae37390331b6ba87e389a49d3d59
Example Filename: APQ9305.dll
Detection Name: Auto.90B145.282358.in02
SHA256: a31f222fc283227f5e7988d1ad9c0aecd66d58bb7b4d8518ae23e110308dbf91
MD5: 7bdbd180c081fa63ca94f9c22c457376
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=a31f222fc283227f5e7988d1ad9c0aecd66d58bb7b4d8518ae23e110308dbf91
Example Filename: d4aa3e7010220ad1b458fac17039c274_62_Exe.exe
Detection Name: Win.Dropper.Miner::95.sbx.tg**
SHA256: 38d053135ddceaef0abb8296f3b0bf6114b25e10e6fa1bb8050aeecec4ba8f55
MD5: 41444d7018601b599beac0c60ed1bf83
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=38d053135ddceaef0abb8296f3b0bf6114b25e10e6fa1bb8050aeecec4ba8f55
Example Filename: content.js
Detection Name: W32.38D053135D-95.SBX.TG
SHA256: 3c1dbc3f56e91cc79f0014850e773a7f12bbfef06680f08f883b2bf12873eccc
MD5: d749e0f8f2cd4e14178a787571534121
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=3c1dbc3f56e91cc79f0014850e773a7f12bbfef06680f08f883b2bf12873eccc
Example Filename: Unconfirmed 280575.crdownload.exe
Detection Name: W32.3C1DBC3F56-90.SBX.TG
Cisco Talos Blog – Read More
