How to Reduce MTTR in Your SOC with Better Threat Intelligence
MTTR is where strategy meets reality. In security operations, it is the margin between a contained incident and a catastrophic breach.
You can have perfect detection coverage, cutting-edge telemetry, and a wall of dashboards glowing like a spaceship cockpit. But if your team takes too long to respond, the attacker still wins the clock.
Reducing Mean Time to Respond is not about shaving seconds for vanity metrics. It is about compressing the window in which damage happens. And the fastest way to do that is not more alerts, but better intelligence.
Key Takeaways
- MTTR is not just an operational metric. It is a direct measure of how long your business is exposed during an active threat. Every minute counts in financial, reputational, and regulatory terms.
- Lower MTTR is achievable only through systematic improvement across all SOC workflows: detection, triage, threat hunting, incident response, and vulnerability management.
- Threat intelligence quality is the single highest-leverage variable in every stage of MTTR reduction; bad or slow intelligence creates bottlenecks that no amount of headcount can overcome.
- For CISOs and security leaders, ANY.RUN Threat Intelligence translates into a defensible, budget-aligned story: measurable MTTR reduction, reduced analyst burnout, and tangible alignment with business risk reduction.
Beyond the Number: What MTTR Actually Measures
MTTR — Mean Time to Respond — captures the average elapsed time from threat detection to full incident remediation. It is a compound metric that absorbs the latency of every step in your response chain: detection, alert triage, investigation, containment, eradication, and recovery. A high MTTR does not merely indicate a slow team; it indicates structural friction somewhere in that chain.
For experienced security leaders, this distinction matters enormously. Chasing MTTR as a raw number is a management trap. Understanding MTTR as a diagnostic readout of your entire SOC’s operational health is a strategic advantage.
Why leadership cares about MTTR
- Direct financial impact. Longer response times increase remediation costs, legal exposure, and downtime.
- Operational continuity. Faster containment keeps business processes running.
- Regulatory and compliance pressure. Many frameworks implicitly reward faster detection and response cycles;
- Reputation protection. The difference between a minor incident and a headline breach is often measured in hours.
When presenting to the board, this framing transforms MTTR from a technical KPI into a business risk metric with direct financial and compliance implications.
How MTTR reflects SOC efficiency
MTTR is not just speed. It is the sum of:
- Decision quality under uncertainty;
- Analyst workload and cognitive pressure;
- Availability of context and evidence;
- Efficiency of internal workflows.
A low MTTR signals something deeper: a SOC that understands what it sees and acts without hesitation. From an operational perspective, MTTR is the output of three interacting variables: the quality of your detections, the speed of your analyst workflows, and the fidelity of your threat intelligence. A team that receives high-fidelity, context-rich alerts and has instant access to deep threat intelligence will always outperform an equally staffed team working with noisy, low-context alerts and manual enrichment processes.
The cost of poor or slow threat intelligence is borne in analyst hours, extended dwell times, and the compounding risk of delayed containment.
The Board-Level Framing
When making the case for investment in MTTR reduction capabilities, security leaders should ground the conversation in three dimensions:
- Financial exposure: quantify the average cost per hour of active incident dwell time, drawing on breach cost benchmarks relevant to your sector.
- Regulatory risk: map MTTR gaps to breach notification obligations and the financial penalties associated with late disclosure.
- Operational resilience: frame MTTR reduction as a measure of how quickly the business can return to normal operations after a security event (a direct input into business continuity metrics that boards track).
How SOC Workflows Shape MTTR
MTTR is not owned by one team. It is the emergent result of everything your SOC does. Here is how different workflows influence it:
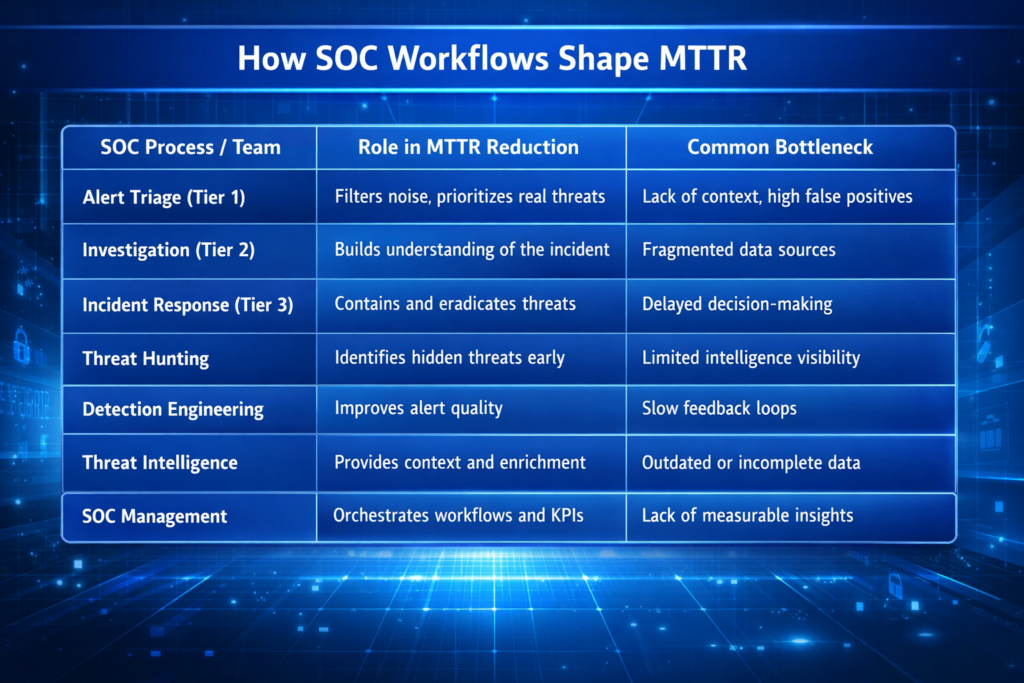
Each of these workflows is, in effect, a constraint in a pipeline. MTTR optimization requires removing the binding constraint — and in the majority of SOC environments, that constraint is the quality, speed, and accessibility of threat intelligence.
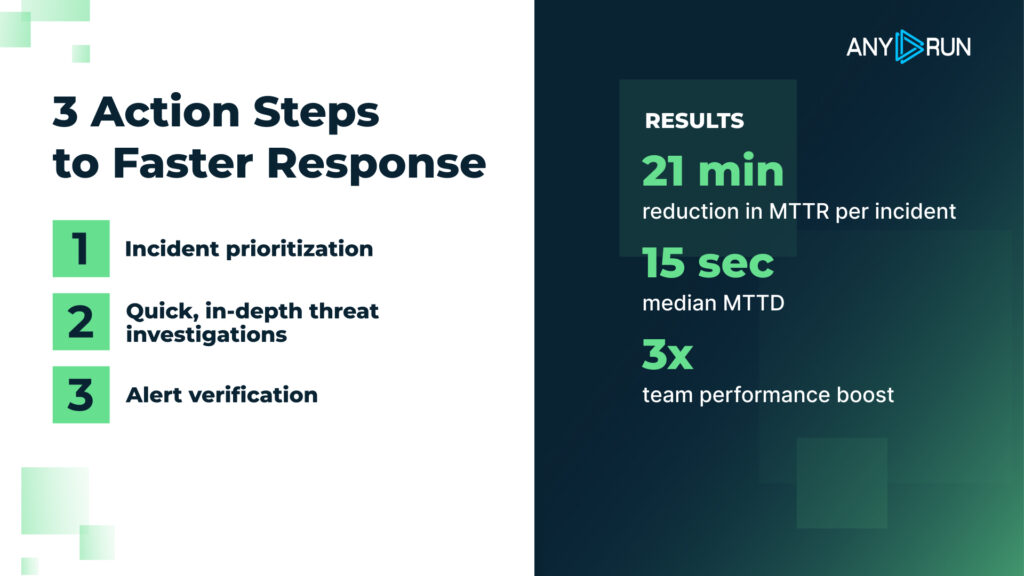
How ANY.RUN Threat Intelligence Optimizes Every SOC Workflow
ANY.RUN Threat Intelligence is a set of capabilities designed to address the most persistent sources of MTTR inflation: intelligence latency, analyst enrichment overhead, and incomplete threat context. It is composed of three tightly integrated components: Threat Intelligence Feeds, Threat Intelligence Lookup, and the ANY.RUN Interactive Sandbox. Together, they form a comprehensive intelligence layer that accelerates every stage of the response chain described above.
Threat Intelligence Feeds: Eliminating Intelligence Latency at Scale
ANY.RUN’s Threat Intelligence Feeds deliver a continuous, real-time stream of high-confidence indicators of compromise (IP addresses, domains, URLs) extracted directly from live malware analysis sessions conducted in the ANY.RUN sandbox environment. Originating from first-hand dynamic analysis places them among the most timely and behaviorally validated IOC sources available.
For SOC teams, this distinction is critical. An IOC that has been validated through behavioral sandbox analysis carries far more operational confidence than one extracted from a static signature or passive aggregation. Analysts and automated playbooks can act on it immediately — without the validation overhead that depresses response speed and inflates MTTR.
What Feeds Deliver Across SOC Workflows
1. Alert Triage: Context-rich IOCs reduce the investigation burden on tier1/tier2 analysts. When an alert fires against a known, characterized IOC, analysts have immediate access to associated threat actor, malware family, and behavioral context, eliminating the manual lookup step that typically consumes 15-30 minutes per alert.
2. Automated Response: High-confidence IOCs from ANY.RUN TI Feeds can trigger automated blocking, quarantine, and notification playbooks with low risk of false-positive action.
3. Threat Hunting: Teams can use the feeds as fresh hypotheses for proactive hunts, immediately operationalizing newly observed IOCs from the broader threat landscape.
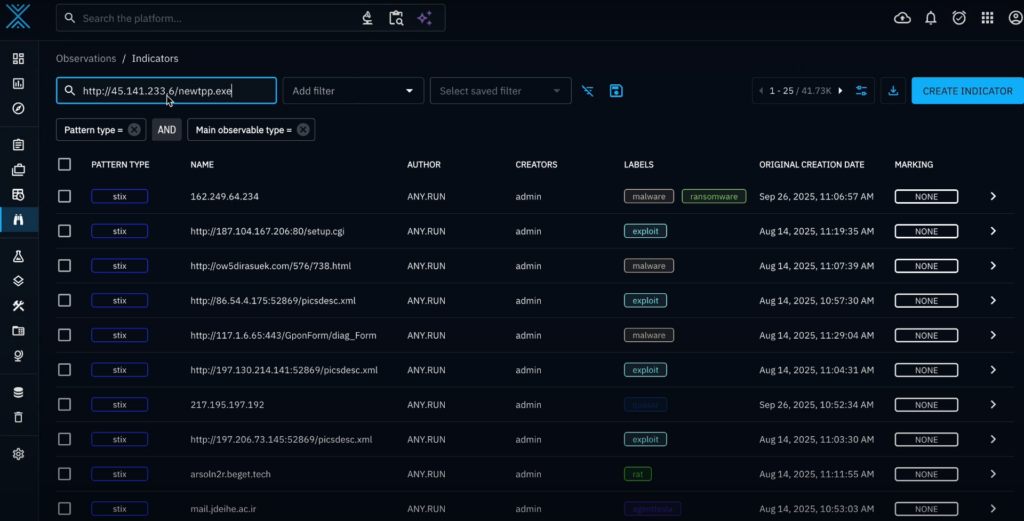
4. Detection Engineering & SIEM: Feeds integrate directly into SIEM and SOAR platforms via STIX/TAXII, CSV, and JSON formats, enabling continuous rule enrichment without manual input. Detection coverage stays current with the threat landscape automatically.

The net effect on MTTR is compounded across the SOC: faster detection, faster triage, faster automated response, and faster hunting cycles, all driven by the elimination of intelligence latency.
Threat Intelligence Lookup: Compressing Analyst Investigation Time
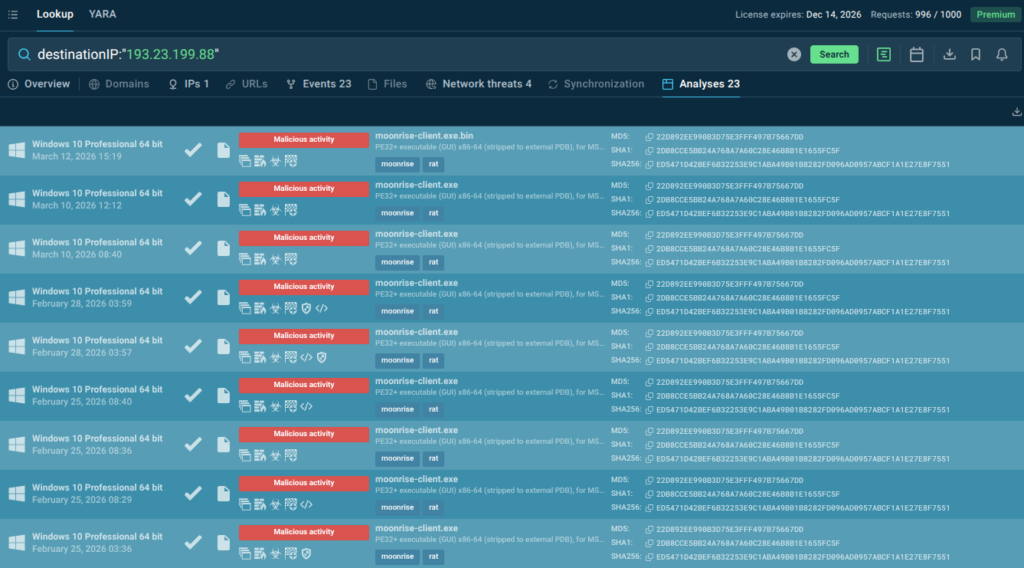
ANY.RUN Threat Intelligence Lookup provides analysts with instant, deep analysis of any artifact — file hash, IP address, domain, or URL — against a continuously updated database of analyzed threats. This is not a static reputation check. It surfaces detailed behavioral context: what a file does when executed, what network infrastructure it communicates with, what threat actor campaigns it is associated with, and what MITRE ATT&CK techniques it employs.
What Lookup Delivers Across SOC Workflows
1. Tier 1/Tier 2 Triage: Analysts can validate any suspicious artifact in seconds, obtaining verdict, behavioral context, associated IOCs, and sandbox analysis links: enough to make an escalation or closure decision without further research.
2. Incident Response: During an active incident, IR teams need to rapidly characterize malware capabilities, map likely lateral movement paths, and determine containment scope. TI Lookup provides instant access to this context, allowing IR teams to act on complete information rather than conducting time-consuming analysis under pressure.
3. Threat Hunting: Hunters can validate hypotheses at scale by running bulk lookups against historical endpoint and network telemetry, rapidly separating genuine threat signals from environmental noise.
4. Management Reporting: Lookup data supports evidence-based MTTR reporting — analysts can demonstrate exactly what intelligence was available, when it was accessed, and how it informed decisions, providing an audit trail that supports both operational review and regulatory compliance.
While TI Feeds and TI Lookup capabilities address the speed dimension of threat intelligence, ANY.RUN’s Interactive Sandbox addresses the depth dimension. It provides analysts with an interactive malware analysis environment that delivers full behavioral visibility — process trees, network traffic, registry changes, file system activity, and MITRE ATT&CK technique mapping — without requiring reverse engineering expertise.
For example, view a sandbox analysis of recently emerged device code phishing attack
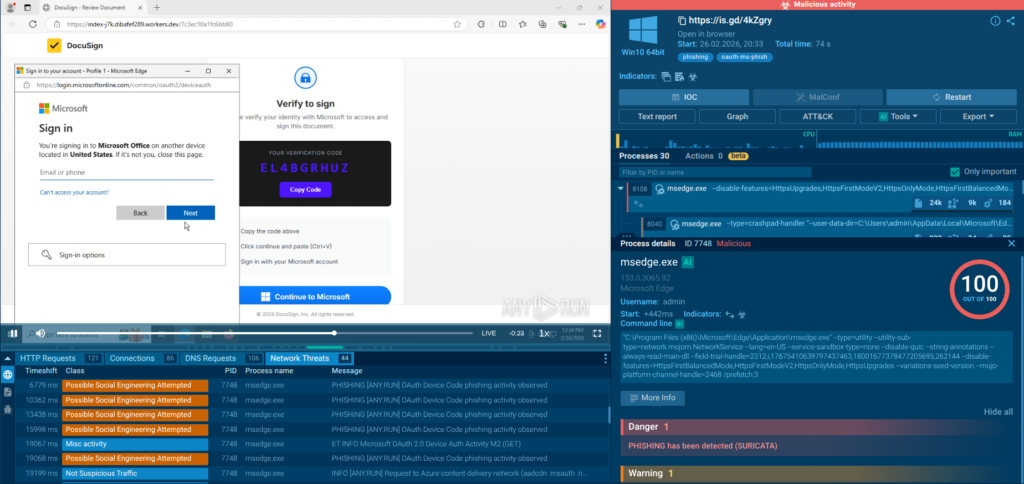
For SOC teams, this means that complex malware analysis, which would previously require escalation to a specialist (adding hours or days to MTTR), can now be performed by any competent analyst. This has a direct and measurable impact on MTTR, particularly in the incident response and escalation phases where analysis bottlenecks most commonly occur.
Turning MTTR Into Measurable Business Advantage
Security leaders face a persistent translation problem: the operational metrics that matter inside the SOC do not naturally map to the language of business risk, financial exposure, and strategic investment. ANY.RUN Threat Intelligence bridges this gap by delivering improvements that are simultaneously operationally meaningful and strategically defensible:
- Risk Reduction: Faster MTTR directly reduces organizational exposure during active incidents. For every workflow improvement driven by ANY.RUN intelligence, the window of active risk narrows, translating into lower expected breach costs and reduced regulatory exposure.
- Analyst Capacity: The manual enrichment and validation work that ANY.RUN Feeds and Lookup eliminate is not just slow, it is expensive. Reclaiming analyst hours from repetitive intelligence gathering and redirecting them toward higher-order investigation and hunting delivers measurable capacity gains without headcount increases.
- Scalability Without Linear Cost Growth: As threat volumes increase, organizations that rely on manual intelligence processes face a linear scaling problem — more alerts require more analysts. ANY.RUN Threat Intelligence breaks this dependency by automating the intelligence layer, allowing SIEM/SOAR platforms to absorb greater alert volumes without proportional analyst overhead.
- Compliance and Audit Readiness: Regulators and insurers increasingly scrutinize incident response timelines. ANY.RUN’s structured, documented intelligence data supports post-incident reporting and demonstrates a defensible security program, reducing regulatory risk and potentially influencing cyber insurance premiums.
- Talent Retention: Analyst burnout is a leading cause of SOC attrition. The cognitive load of manual enrichment, alert fatigue, and tool-switching is a known driver of analyst dissatisfaction. ANY.RUN Threat Intelligence reduces this burden, contributing to the working environment improvements that retain experienced analysts.
Addressing Security Leaders’ Core Pains
The decision-makers most likely to evaluate ANY.RUN Threat Intelligence are managing a recognizable set of pressures: too many alerts, too few analysts, insufficient confidence in intelligence quality, difficulty demonstrating security ROI, and the constant risk of a major incident that would expose all three.
ANY.RUN Threat Intelligence addresses each of these directly. It does not require a wholesale platform replacement. It integrates with existing SIEM, SOAR, and TIP infrastructure. It delivers immediate capability improvements from day one of deployment. And it provides a documented, measurable improvement in detection and response performance that security leaders need to defend budget allocations and demonstrate program maturity.
Conclusion
MTTR is the number that tells you whether your security program is actually working. Under pressure, against real threats. Every minute of MTTR that you cannot account for is a minute of active risk that your organization is absorbing.
The path to lower MTTR runs through better threat intelligence. Intelligence that is timely enough to act on immediately. Intelligence that is rich enough to eliminate investigation bottlenecks. Intelligence that integrates cleanly into your existing workflows so that improvement is structural, not dependent on individual analyst heroics.
ANY.RUN Threat Intelligence — through its Feeds, Lookup, and Sandbox capabilities — is built to deliver exactly this. It addresses the real operational problems that inflate MTTR in modern SOC environments: intelligence latency, enrichment overhead, analysis depth limitations, and the manual work that consumes analyst capacity that should be directed at threat response.
For SOC leaders looking to demonstrate measurable improvement in their teams’ performance, for CISOs making the case for sustained security investment, and for business leaders who understand that security outcomes have direct financial consequences, MTTR reduction through better threat intelligence is not a technical project — it is a strategic imperative.
About ANY.RUN
As a leading provider of interactive malware analysis and threat intelligence, ANY.RUN is trusted by over 600,000 analysts across 15,000 organizations worldwide. Its solutions enable teams to investigate threats in real time, trace full execution chains, and surface critical behaviors within seconds.
Safely detonate samples, interact with them as they run, and instantly pivot to network traces, file system changes, registry activity, and memory artifacts in ANY.RUN’s Interactive Sandbox. For threat intelligence insights, integrate TI Lookup and TI Feeds supplying enriched IOCs and automation-ready intelligence.
ANY.RUN meets enterprise security and compliance expectations. The company is SOC 2 Type II certified, reinforcing its commitment to protecting customer data and maintaining strong security controls.
FAQ
Improve access to contextual threat intelligence to eliminate investigation delays.
Because detecting a threat quickly does not help if response is slow or ineffective.
It enriches alerts, prioritizes threats, and accelerates investigation and response decisions.
Yes, by optimizing workflows and providing better intelligence to analysts.
Lack of context and fragmented data across multiple systems.
They enable faster detection, reduce false positives, and support automation.
It provides deep, immediate context for indicators, speeding up investigations.
The post How to Reduce MTTR in Your SOC with Better Threat Intelligence appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More

