Turn Your SOC Into a Detection Engine: Rethinking Threat Monitoring
Threat monitoring is treated as one capability among many. Something that sits alongside incident response and threat hunting on an org chart. That framing undersells how central it actually is.
Monitoring is the connective tissue of the entire security operation. Every other SOC function depends on it working well.
For SOC and MSSP leaders, building effective threat monitoring is not about “more alerts.” It is about designing the core process that connects detection, triage, hunting, response, intelligence, reporting, and ultimately business resilience.
Key Takeaways
- Threat monitoring is structural, not supplemental. Every core SOC workflow (triage, threat hunting, forensics, vuln management, MSSP SLA delivery) depends on monitoring quality. Weaknesses propagate everywhere.
- More alerts do not equal better visibility. Context and prioritization define effectiveness.
- Inefficient monitoring increases business risk. Missed early-stage attacks lead to higher remediation costs and regulatory exposure. Dwell time reduction translates directly to breach loss reduction.
- Intelligence must be operationalized, not stored. Threat intelligence only creates value when embedded into monitoring workflows.
- Behavior-backed indicators outperform static IOC lists. Fresh, validated data improves detection accuracy and reduces false positives.
- Monitoring should reflect business risk, not system capabilities. Crown-jewel assets and regulatory drivers must shape detection priorities.
- Enhanced monitoring directly supports executive-level objectives. Faster detection, lower incident impact, and measurable performance strengthen board confidence.
Threat Monitoring: Not a Feature But the Foundation
Consider how the core workflows intersect with monitoring:
- Detection engineering: Monitoring consumes detection rules and reveals where they fail.
- Alert triage and incident response cannot function without a continuous stream of prioritized, contextualized signals. When monitoring is weak — too noisy, too narrow, or too slow — analysts drown in false positives or miss real incidents entirely. Neither outcome is tolerable.
- Vulnerability management and patch prioritization increasingly depend on live threat intelligence to decide what gets fixed first.
- Even threat hunting is informed by monitoring outputs: analysts use baseline behavioral data, detection gaps, and historical alert patterns to define their hunting hypotheses.
- Digital forensics and incident investigation rely on monitoring having captured enough data — the right logs, network flows, endpoint telemetry — to reconstruct attack timelines after the fact.
- MSSP client reporting and SLA management live and die by monitoring quality. When clients ask “are we covered against this new ransomware family?”, the answer depends entirely on whether detection rules exist, whether indicators are up to date, and whether the monitoring stack is generating meaningful signal.
This is why threat monitoring must be treated as a first-class, continuously maintained operational capability, not a set-and-forget configuration.
Signal vs. Noise: The Battle That Defines Your SOC
Effective threat monitoring is:
- Context-rich rather than alert-dense;
- Intelligence-driven rather than purely rule-based;
- Adaptive rather than static;
- Prioritized by risk rather than by volume;
- Aligned with business-critical assets rather than generic telemetry.
How to tell if your monitoring works at its best? Ask these questions:
- Does it consistently reduce mean time to detect (MTTD)?
- Are high-risk alerts surfaced early, or buried in noise?
- Do detections map to real-world adversary behavior?
- Is intelligence automatically operationalized, or manually researched?
- Does monitoring adapt when new campaigns emerge?
If analysts spend most of their time enriching alerts manually, chasing false positives, or investigating low-impact noise, monitoring is underperforming. Inefficient monitoring does more than exhaust analysts. It leads to delayed breach discovery, higher remediation costs, and regulatory exposure. Leadership questions investment, and security becomes reactive instead of strategic.
Powering Monitoring with Real-World Adversary Data
That’s where the separation between reactive and proactive monitoring happens. Threat intelligence — continuously updated, high-fidelity data on active threats — transforms a monitoring program from one that reacts to known indicators to one that anticipates emerging attack patterns.
The mechanism is straightforward: if your monitoring infrastructure receives a live stream of newly identified malicious IPs, domains, and URLs extracted from real attacks happening right now, your detection coverage extends beyond what your own environment has encountered.
ANY.RUN operates one of the world’s largest interactive malware analysis sandboxes, used by over 600,000 security professionals and SOC teams from more than 15,000 organizations globally.
View a sandbox analysis example
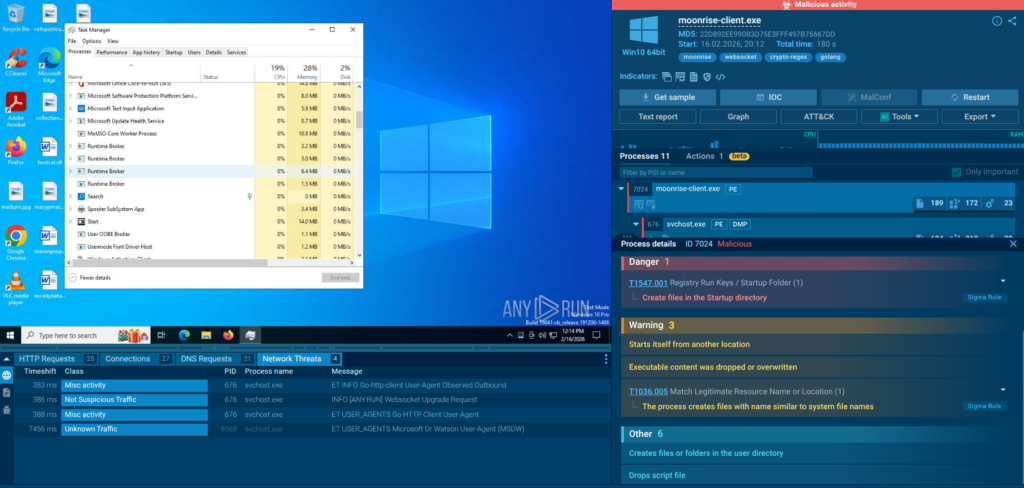
Here Interactive Sandbox exposes the attack chain and infrastructure of Moonrise – a RAT recently discovered by ANY.RUN’s analysts.
Every analysis session generates structured threat data — IOCs, IOAs (Indicators of Attack), IOBs (Indicators of Behavior), and TTPs mapped to the MITRE ATT&CK framework. ANY.RUN’s Threat Intelligence Feeds channel that data directly into customers’ detection infrastructure in real time.
This creates a network effect with genuine security value: organizations that were the first to face incidents help others anticipate and prevent them. In a documented case, Interlock ransomware targeting healthcare organizations appeared in ANY.RUN’s data nearly a month before the first public threat reports, giving subscribers time to build detections and harden defenses while most of the industry was still unaware.
Operational Benefits
- Faster enrichment during alert triage;
- Improved detection accuracy;
- Reduced false positives;
- Early identification of active campaigns;
- Support for proactive threat hunting.
Instead of simply adding more indicators, these feeds strengthen the connective tissue between intelligence and monitoring workflows. Monitoring becomes intelligence-infused rather than indicator-overloaded.

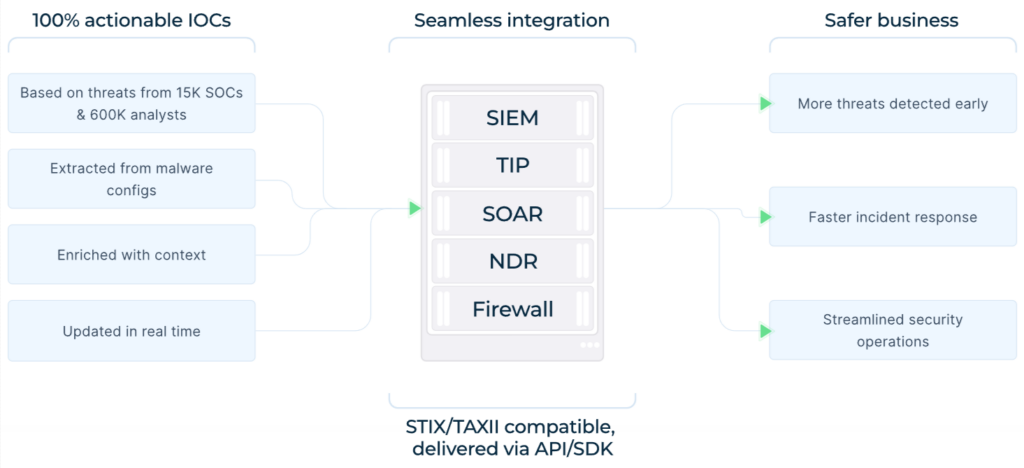
Integration: Minimal Friction, Maximum Compatibility
ANY.RUN delivers Threat Intelligence Feeds in the STIX/TAXII format, making it straightforward for security teams to integrate the data into their existing infrastructure — including popular platforms like OpenCTI and ThreatConnect and solutions like Microsoft Sentinel and Google SecOps. The standardized format means integration with existing SIEM, TIP, IDS/IPS, and EDR platforms is achievable without custom development work.
API access and SDK support allow teams to automate indicator ingestion and build custom workflows around the data. For MSSPs managing multiple client environments, this integration flexibility is essential — feed data can be channeled into per-client SIEM instances with consistent formatting and attribution.
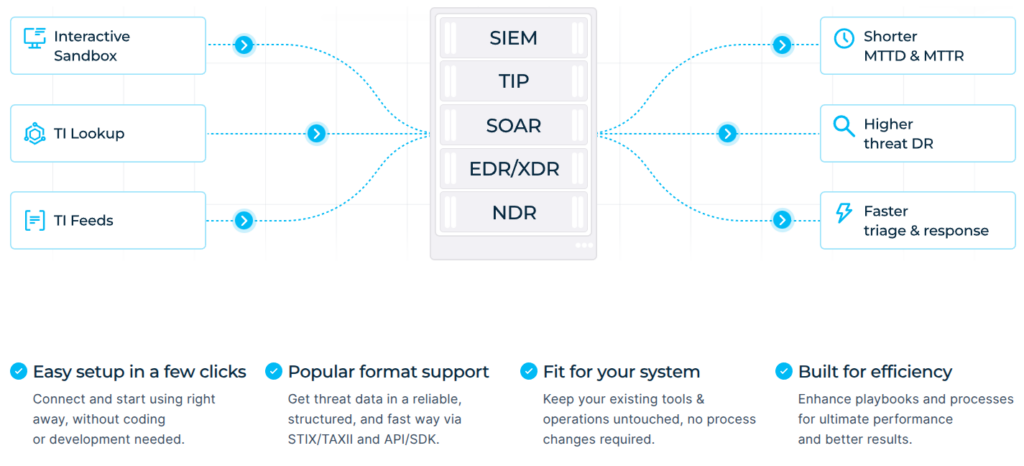
ANY.RUN’s TI Lookup: The Investigative Layer That Makes Feed Intelligence Actionable
TI Feeds solve the automation problem: keeping your SIEM and detection rules continuously stocked with validated, current indicators. But automated ingestion has a natural limit. When an analyst needs to understand why an indicator is malicious, how the associated malware behaves, what else in the environment may be connected, and whether this alert is part of a larger campaign — a feed delivering STIX records into a detection platform cannot answer those questions on its own. That is where Threat Intelligence Lookup completes the picture.
TI Lookup is a database queryable through both a web interface and an API that surfaces IOCs, IOAs, IOBs, and TTPs extracted from millions of sandbox analysis sessions. Searches can be run against URLs, TTPs, file paths, command lines, process behaviors, registry activity, network connections, port numbers, JA3/JA3S TLS fingerprints, Suricata rule IDs, and more.
This means an analyst isn’t limited to checking a hash or IP address against a known-bad list; they can search for behavioral patterns, specific command-line strings observed in active malware, or infrastructure characteristics.
registryKey:”CurrentVersion\Schedule” AND registryValue:”.exe”
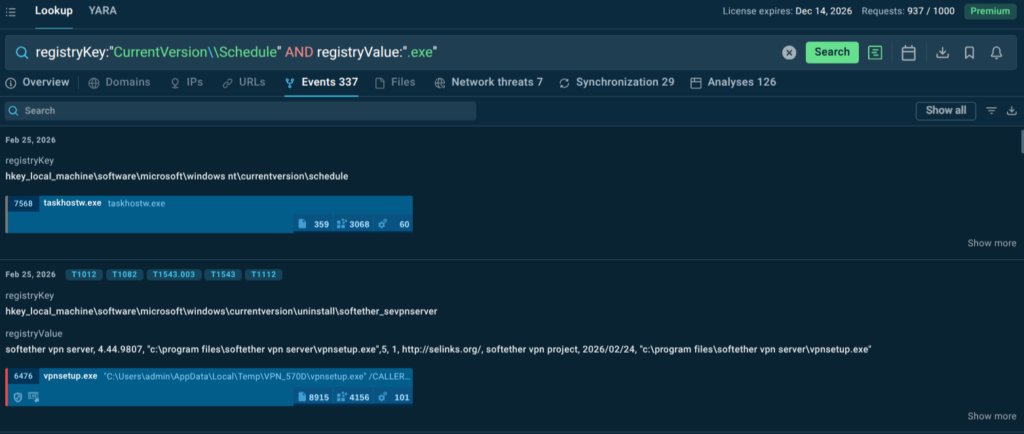
In this example, we can identify threats that aim to execute malicious code through scheduled tasks.
The workflow goes in the other direction too. Proactive threat hunting using TI Lookup — searching for TTPs or behavioral patterns associated with a threat actor targeting the organization’s industry — can surface indicators that have not yet appeared in automated feeds. Those indicators can then be manually added to detection rules, extending the monitoring program’s coverage before a feed update would have caught them.
Monitoring That Speaks the Language of the Board
The operational case for investing in threat monitoring is clear. The business case is sometimes harder to communicate — but it is just as strong.
Risk Reduction That Translates to Financial Terms
The cost of a breach scales with dwell time. Every day an attacker remains undetected in a network is another day of potential data exfiltration, lateral movement, and preparation for a destructive payload. Monitoring that cuts dwell time from 120 days to 5 days is not just an operational improvement. It is a material reduction in breach severity and cost. For organizations in regulated industries, it is also a meaningful factor in whether a regulatory notification obligation is triggered and whether a fine is proportionate.
Meeting SLAs and Client Expectations
For MSSPs, detection speed and coverage breadth are effectively product features. Clients sign contracts expecting that known threats will be detected and responded to within defined timeframes. TI Feeds that update continuously with indicators from active threats extend the detection surface without requiring proportional growth in headcount.
Enabling SOC Efficiency
Analyst time is expensive and scarce. When monitoring is well-designed (contextual, high-fidelity, and supported by rich threat intelligence) analysts spend more time on decisions and less time on manual enrichment, alert validation, and IOC lookups. The triage process shortens. MTTR decreases. The SOC can handle more volume with the same team, or the same volume with better quality of investigation.
Demonstrating Proactive Security Posture to the Board
Security leaders increasingly need to demonstrate not just that they respond well to incidents, but that they are actively working to prevent them. Monitoring informed by real-time threat intelligence that detects and blocks indicators of a major ransomware group weeks before public disclosure is a compelling proof point in that conversation. It shifts the narrative from incident response to threat prevention, which is where business leadership wants security programs to operate.
Conclusion: The Standard for Monitoring Has Changed
The threat landscape that SOC and MSSP teams operate in today is faster-moving, better-resourced, and more creative than it was even three years ago. Monitoring built for a previous era of threat activity will fail against current adversary techniques.
Effective threat monitoring in 2026 and beyond requires more than log aggregation and static detection rules. It requires continuous intelligence input from real attack data, behavioral detection that doesn’t depend on known signatures, and the operational discipline to keep detection logic current as threats evolve.
ANY.RUN’s Threat Intelligence Feeds represent one of the most direct paths to that standard: validated, contextualized, continuously updated IOCs and behavioral indicators sourced from millions of real malware analysis sessions, integrated directly into the security stack.
About ANY.RUN
ANY.RUN is part of modern SOC workflows, integrating easily into existing processes and strengthening the entire operational cycle across Tier 1, Tier 2, and Tier 3.
It supports every stage of investigation, from exposing real behavior during safe detonation, to enriching analysis with broader threat context, and delivering continuous intelligence that helps teams move faster and make confident decisions.
Today, more than 600,000 security professionals and 15,000 organizations rely on ANY.RUN to accelerate triage, reduce unnecessary escalations, and stay ahead of evolving phishing and malware campaigns.
To stay informed about newly discovered threats and real-world attack analysis, follow ANY.RUN’s team on LinkedIn and X, where weekly updates highlight the latest research, detections, and investigation insights.
FAQ
Threat monitoring is the continuous process of collecting, correlating, and analyzing security telemetry to detect malicious activity in real time.
Detection refers to the logic or rules that identify malicious behavior. Monitoring is the broader operational process that consumes detections, prioritizes alerts, and drives response workflows.
It is risk-aligned, intelligence-driven, adaptive, and capable of surfacing high-impact threats early while minimizing noise.
Key indicators include reduced MTTD, lower false positive rates, improved alert prioritization accuracy, and faster containment times.
Common issues include over-collection of logs, static IOC feeds, lack of intelligence integration, and weak feedback loops between incidents and detection updates.
It provides contextual, real-world adversary data that enhances detection logic, prioritization, enrichment, and proactive hunting.
Intelligence-driven monitoring improves service differentiation, reduces analyst workload, increases detection accuracy, and strengthens client trust.
The post Turn Your SOC Into a Detection Engine: Rethinking Threat Monitoring appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
