Best early Amazon Spring Sale phone deals 2026: 20 sales out now
For Amazon’s Big Spring Sale, I’ve rounded up the best early phone deals from major brands like Apple, Samsung, Motorola, and more.
Latest news – Read More
For Amazon’s Big Spring Sale, I’ve rounded up the best early phone deals from major brands like Apple, Samsung, Motorola, and more.
Latest news – Read More
Early Amazon Spring Sale offers are here, and it’s a great time to grab these tiny gadgets packed with huge function.
Latest news – Read More
As part of a recent live expert panel, ANY.RUN together with threat researcher and ethical hacker Mauro Eldritch explored biggest security risks companies should be prepared for in 2026.
The discussion covered several relevant cases, from the Lazarus IT Workers operation to the rapid rise of AI-driven phishing attacks, and examined the common thread behind them: trust abuse.
Below are the key takeaways for those seeking a clearer view of modern cyber risks and how to prepare as a SOC leader.
Watch the full panel on our YouTube channel
In 2026, many cyberattacks don’t look like attacks at all. Instead of exploiting technical vulnerabilities, threat actors increasingly exploit human trust. This tactic is known as trust abuse, and it’s what many modern cyber threats are based on.
Businesses inevitably rely on trust between employees, systems, vendors, and partners. Without it, organizations cannot operate efficiently. Threat actors know what, so they’ve learnt to mimic legitimate identities, infiltrate communication channels and everyday workflows, and turn employees into unwitting entry points.
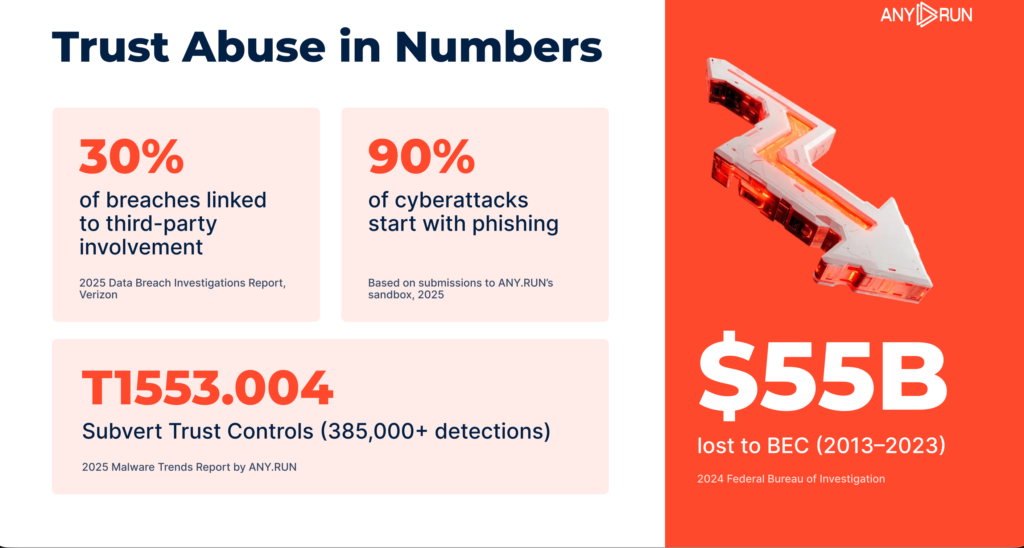
AI-assisted social engineering pushes trust abuse even further. These attacks closely resemble legitimate activity and often fail to trigger traditional alerts. For security leaders, this changes how risk must be understood.
Risk mitigation is no longer only about patching vulnerabilities or strengthening perimeter defenses. Detecting trust abuse requires visibility into behavior, context, and how trust moves inside the enterprise.
Lazarus, a North-Korean state-sponsored threat actor, has shifted its tactics. Instead of relying only on malware, the group infiltrates Western and Middle Eastern companies to conduct corporate espionage.
The scheme was investigated by Mauro Eldritch and Heiner García from NorthScan inside ANY.RUN’s controlled infrastructure. The researchers were able to trap the attackers in a sandbox environment and observe their activity while the threat actors believed they had gained access to a corporate network.
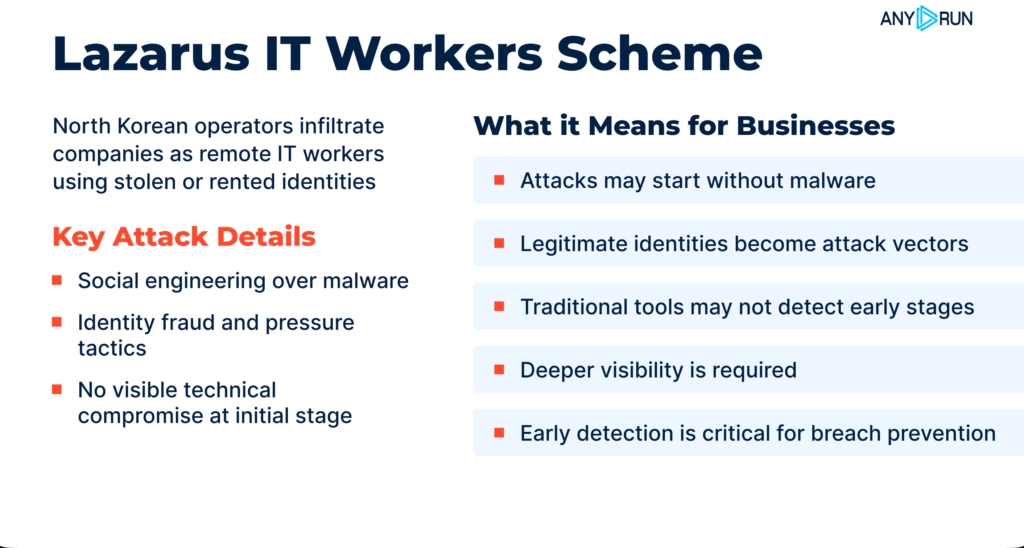
Lazarus operation is a vivid example of trust abuse in a business environment. No advanced malware was involved in the attack initially. Because of that, the potential implications for the victims can be catastrophic. Attacks like that don’t trigger alerts; there’s simply nothing suspicious to detect.
This is why, unlike short-lived malware campaigns, trust-based infiltrations can persist much longer. Once attackers gain access, they may embed themselves deeper in the organization or even place additional operatives inside the company.
ANY.RUN exposed this campaign before the broader market. The investigation was conducted entirely within our controlled infrastructure, which allowed researchers to observe attacker behavior in real time.
Read more on Lazarus case investigation supported by ANY.RUN
But most companies do not have the resources to monitor suspicious activity at this level.
In practice, risk mitigation depends on the ability to detect and interpret unusual behavior early, before it escalates into a full incident. Trust abuse attacks make early visibility and detection critical for enterprise security.

Phishing attacks today look very different from the obvious scam emails many people are used to spotting. With AI-assisted tools, threat actors can now mimic completely normal email conversations, using polished language and highly personalized content.
AI makes these attacks both believable and scalable. The core vulnerability here is human trust, which becomes an easy entry point for attackers.
Modern phishing campaigns increasingly focus less on technical exploits and more on manipulating communication chains and legitimate domains that employees already trust.
As a result, traditional security tools are often left with no clear indicators of compromise to detect. These attacks blend into normal business communication, making them much harder to identify before damage occurs.
To address this challenge, modern security requires a layered approach. Early detection does not depend on a single tool but on a set of coordinated processes. In particular, effective defense relies on three core SOC activities: monitoring, triage, and threat hunting.
Traditional security tools are important to have, but they aren’t universal. Unless they can show what happens after a user interacts with a suspicious file, link, or attachment, organizations may lack the full visibility needed to understand the threat. This gap leaves companies vulnerable to increasingly evasive attack techniques.
ANY.RUN helps strengthen these processes by providing greater visibility, faster investigations, and reliable threat context.
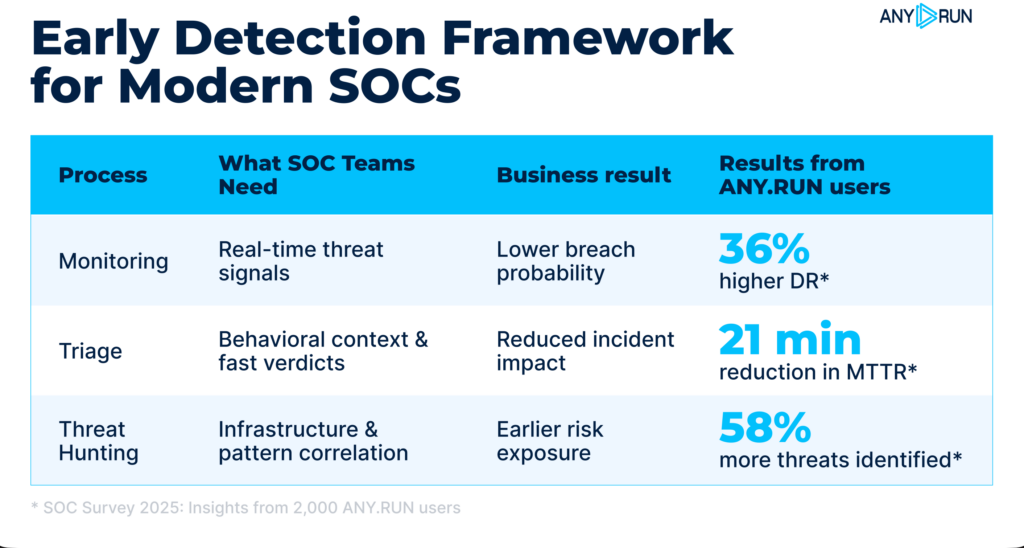
Effective monitoring helps identify threats before they reach internal systems, preventing breaches. ANY.RUN enhances monitoring by enabling teams to:
Triage is critical for handling high alert volumes and avoiding delays in response. ANY.RUN helps streamline triage by allowing teams to:
Threat hunting focuses on uncovering patterns and anticipating attacker behavior. ANY.RUN supports proactive hunting by enabling teams to:
By strengthening these three processes, organizations can achieve earlier detection, faster response, and more efficient SOC operations, reducing the risk of modern, trust-based attacks.
Enterprise cyber threats are shifting toward identity-based and trust-driven attacks. Campaigns like Lazarus and AI-powered phishing show that attackers no longer rely solely on malware or exploits.
For decision-makers, this means rethinking how risk is assessed and how security operations are structured. Visibility, context, and speed are becoming critical factors in effective defense.
Organizations that adapt their SOC processes to these realities will be better positioned to detect threats early and prevent incidents before they escalate.
ANY.RUN delivers interactive malware analysis and actionable threat intelligence trusted by more than 15,000 organizations and 600,000 security analysts worldwide.
Interactive Sandbox, Threat Intelligence Lookup, and Threat Intelligence Feeds help SOC and MSSP teams analyze threats faster, investigate incidents with deeper context, and detect emerging attacks earlier.
ANY.RUN meets enterprise security and compliance expectations. The company is SOC 2 Type II certified, reinforcing its commitment to protecting customer data and maintaining strong security controls.
The post Lazarus, AI, and Trust Abuse: Top Enterprise Cybersecurity Risks 2026 appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
Forget Amazon. These Costco deals will help you save substantially on everything from household goods to Apple devices.
Latest news – Read More
We tested the top business desktops from major brands like Dell, Lenovo, and Apple to find the best PCs for work and play.
Latest news – Read More
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Wing FTP to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation.
The vulnerability, CVE-2025-47813 (CVSS score: 4.3), is an information disclosure vulnerability that leaks the installation path of the application under certain conditions
The Hacker News – Read More
Researchers uncovered an extensive cyberespionage campaign that used novel backdoors and familiar evasion techniques to maintain persistent access to regional targets.
darkreading – Read More
These are the physical AI advancements Nvidia said it’s making in robotics, autonomous vehicles, and more.
Latest news – Read More
Every OSINT analyst has been there. You pulled the threads, mapped the connections, built the timeline. The data looks clean and the narrative holds. Then someone asks a question you didn’t consider and the whole picture shifts. The failure was not in your tooling or your collection. It was in your reasoning. The missing discipline in information security is not technical. It is intellectual.
We spend enormous energy mastering technical tradecraft. We learn to pivot across data sources, chain identifiers, verify imagery and attribute infrastructure. We build workflows, automate enrichment and refine our toolkits constantly.
But when was the last time you systematically trained the thing that actually interprets all of that data? when was the last time you trained your mind?
The uncomfortable truth is that most of us are running sophisticated collection on top of undisciplined analysis. We know how to find information. We are far less practiced at thinking about it rigorously. Confirmation bias does not announce itself. Neither does anchoring, narrative fallacy or the dozen other cognitive traps that plague analytical work. These are not problems you solve with better OSINT tools. They are problems you solve with better thinking.
There is nothing new about this challenge. For over two thousand years a formal system existed for training exactly this capacity. The Trivium. Three disciplines studied in sequence. Grammar, Logic and Rhetoric. Grammar teaches you to define your terms precisely and understand the structure of what you are examining. Before you investigate, make sure you actually understand what you are looking at. How many investigations have gone sideways because an analyst confused correlation with connection or failed to define the scope of what they were actually trying to answer? Logic trains you to construct valid arguments, identify fallacies and stress test claims under scrutiny. This is the analytical core.
The discipline of asking whether your conclusion actually follows from your evidence or whether you have built a comfortable story around cherry picked data points. Rhetoric is the ability to communicate findings with clarity and force. Every OSINT professional who has written an intelligence product knows the gap between having good findings and delivering them in a way that drives action.
A brilliant investigation that produces an incomprehensible report is a wasted investigation. These are not abstract academic concepts. They map directly onto the intelligence cycle. Define the problem, analyse the information, communicate the assessment. The ancients understood something we have largely forgotten.
These are trainable skills, not innate talents.
The information environment is getting worse, not better. AI generated content, synthetic media, coordinated inauthentic behaviour and the sheer volume of data available to analysts all compound the challenge. The bottleneck is no longer access to information. It is the ability to think clearly about what that information means. Every year the OSINT community gets better tools and every year the adversaries get better at poisoning the well. The asymmetry does not resolve with more automation. It resolves with sharper minds. Consider how much of modern security discourse is driven by reaction rather than reasoning. A new threat report drops and the takes fly, often before anyone has critically examined the methodology, the sourcing or the assumptions behind the conclusions. We reward speed of opinion over quality of thought. That is not analysis. That is performance. The professionals who consistently produce reliable intelligence are not the ones with the most tools or the fastest takes. They are the ones who have trained themselves to slow down at the critical moment. To define terms carefully, test their logic honestly and communicate their findings precisely. They practice the Trivium whether they call it that or not.
This is what led to the creation of Trivium Prime, that and the low level of discourse in British OSINT circles. A structured training ground for exactly this kind of intellectual formation. Not a course you watch passively. Not a certificate you collect. A disciplined practice built around mastering the foundational skills of clear thinking, honest reasoning and authoritative communication.
The programme is built around progressive levels. Foundations in logic, rhetoric and the grammar of knowledge. Then strategic intelligence covering political systems, economic structures, decision making frameworks and historical case studies. Then leadership, institution building and applied strategy. Members advance through demonstrated mastery, not attendance. You test. You defend your reasoning. You earn your rank. It is structured as a selective membership order, not an open platform. Admission requires an application and the barrier is intentional. This kind of training only works with people who are serious about it.
If you work in OSINT, threat intelligence or any discipline where the quality of your thinking determines the quality of your output, ask yourself honestly. When did you last train that capacity with the same rigour you apply to your technical skills? Most of us never have. We learned to think by accident, picking up habits from mentors, from experience, from making mistakes in the field. Some of those habits are good. Some of them are invisible liabilities we have never examined.
The Trivium Way offers a systematic alternative. A framework that has produced clear thinkers for millennia, now adapted for men who take their intellectual development as seriously as their professional development. Trivium Prime is accepting applications. If you are the kind of person who reads Secjuice you already care about doing this work well. The question is whether you are willing to sharpen the one tool that every other tool depends on.
Your mind is your primary sensor. Train it accordingly.
Secjuice – Read More
FBI warns gamers after malware hidden in several Steam games stole browser data and drained cryptocurrency wallets between May 2024 and January 2026.
Hackread – Cybersecurity News, Data Breaches, AI and More – Read More