AI-Powered Cyber Warfare: How Autonomous Attack Agents Are Changing the Threat Landscape
Introduction
A few years ago, most cyberattacks still depended heavily on human effort—skilled operators manually probing systems, testing vulnerabilities, and executing campaigns step by step.
That model is quietly breaking down.
In conversations with security teams and analysts over the past year, one theme keeps coming up: attackers are no longer just using tools—they’re starting to deploy systems that can think, adapt, and act on their own. This is where AI-powered cyber warfare begins to shift from buzzword to reality.
At the center of this shift are autonomous attack agents, AI-driven systems that don’t just assist attackers but actively participate in decision-making. And that changes the threat landscape in a very real way.
What is AI-Powered Cyber Warfare?
At its simplest, AI-powered cyber warfare refers to the use of artificial intelligence and machine learning to enhance cyberattacks. But that definition doesn’t quite capture what’s happening on the ground.
What’s different now is how AI is being used.
Instead of just automating repetitive tasks, attackers are beginning to rely on AI to:
- Continuously scan and map attack surfaces
- Prioritize targets based on probability of success
- Adjust tactics mid-attack
- Learn from failures and retry with improved strategies
One security researcher recently described it as “moving from scripts to systems.” That distinction matters. Scripts execute instructions. Systems adapt.
This is why the AI threat landscape feels more unpredictable today—it’s no longer just about known techniques, but evolving behavior.
Understanding Autonomous Attack Agents
If there’s one concept security leaders are increasingly concerned about, it’s autonomous attack agents.
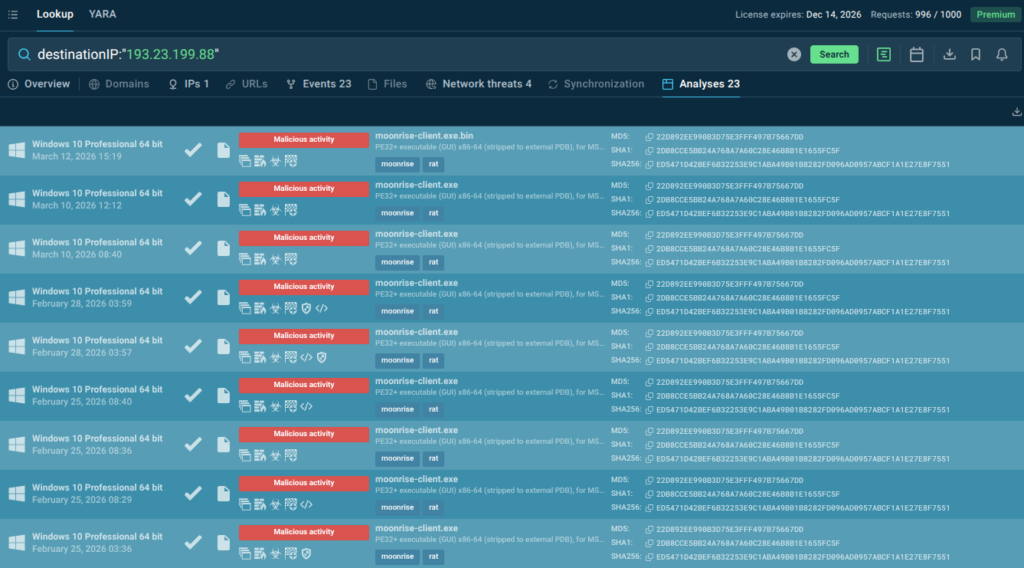
These aren’t hypothetical. Early versions are already being observed in the wild—particularly in automated reconnaissance and vulnerability scanning campaigns.
For example, researchers have documented AI-assisted tools that can:
- Crawl entire infrastructures in minutes
- Identify misconfigurations across cloud environments
- Chain vulnerabilities together without manual input
In one recent case study discussed in security circles, an AI-assisted system was able to simulate multiple attack paths against a target environment and automatically select the most efficient route. That’s a level of decision-making that traditionally required experienced human operators.
This is what makes AI attack agents so significant—they compress both time and expertise. What once required a skilled team can increasingly be done by a single operator backed by intelligent systems.
How AI is Changing Cyberattacks
The shift toward AI-driven attacks is already visible across several fronts.
1. AI-Powered Malware
We’re seeing early signs of AI-powered malware that can alter its behavior to avoid detection. Instead of relying on fixed signatures, these threats experiment—adjusting execution patterns until they find a way through.
While still evolving, this approach is forcing defenders to rethink how detection works.
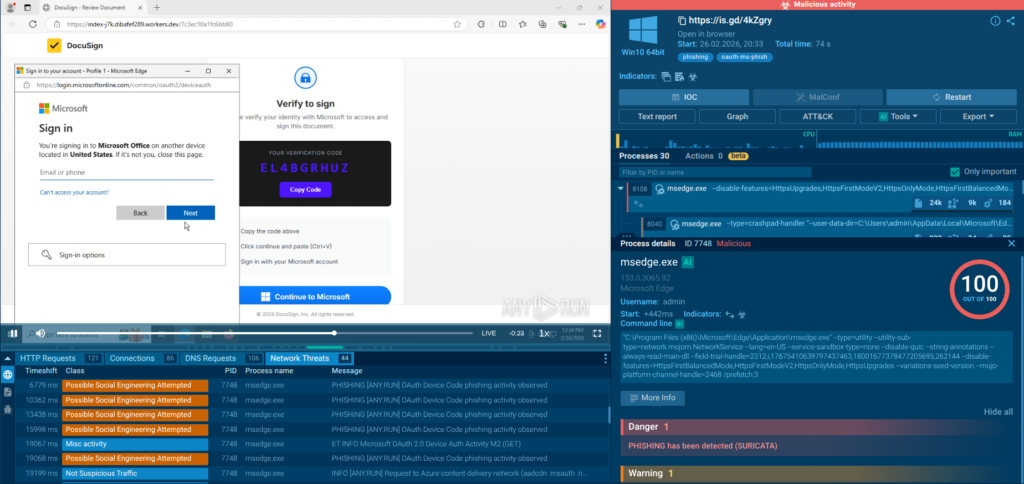
2. Smarter Phishing and Deepfakes
Perhaps the most visible impact of AI is in phishing.
Security teams report a noticeable increase in highly personalized phishing emails—messages that reflect tone, context, and even internal communication styles. With generative AI, attackers can now scale this level of personalization effortlessly.
Add deepfake audio or video into the mix, and AI-driven cyber attacks start to blur the line between technical compromise and social engineering.
3. Real-Time Decision Making
AI doesn’t wait.
Attack systems can process signals in real time—whether it’s detecting a defensive response or identifying a new entry point—and adjust instantly. This gives attackers a speed advantage that traditional defenses often struggle to match.
4. Scalable, Automated Attacks
Automation isn’t new in cybersecurity, but AI takes it further.
With automated penetration attacks, a single campaign can test thousands of variations simultaneously. Instead of guessing what might work, attackers can experiment at scale.
A Rapidly Evolving Threat Landscape
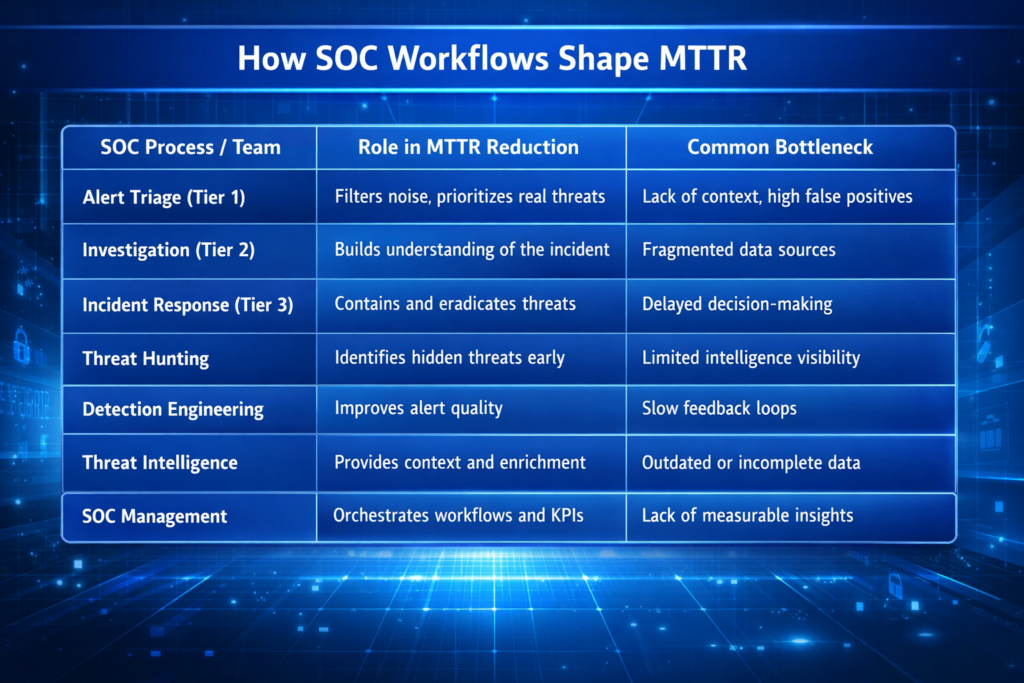
From an analyst’s perspective, the biggest shift isn’t just technical—it’s operational.
We’re moving from a world of occasional, targeted attacks to one of continuous, adaptive pressure.
That translates into:
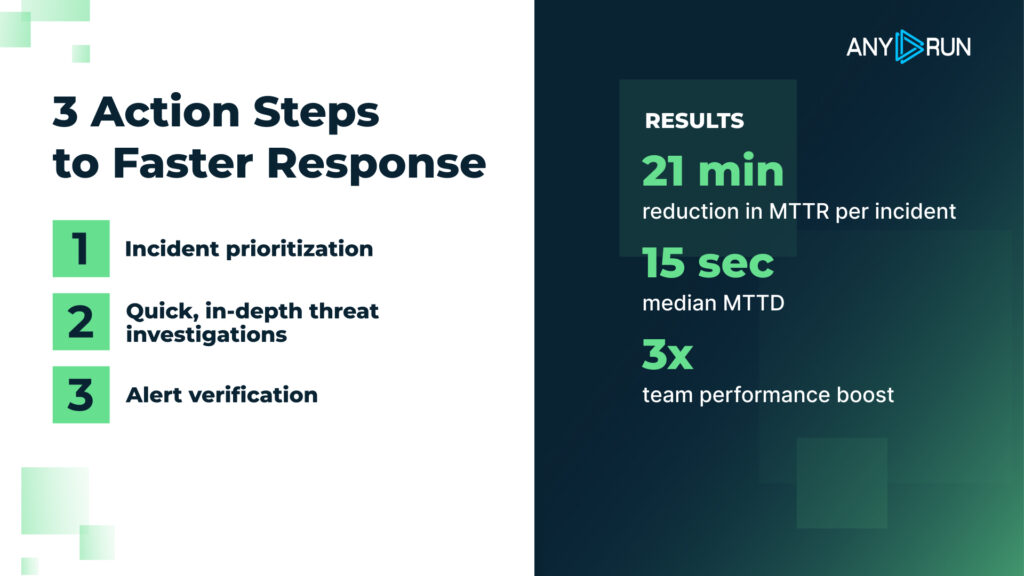
- Shorter detection and response windows
- A constant stream of attack attempts
- More sophisticated and evolving tactics
- A growing presence of intelligent cyber threats
In discussions with CISOs, a common concern is fatigue—not just human fatigue, but system fatigue. Defenses designed for periodic threats are now dealing with persistent, automated adversaries.
Blaze AI and the Shift Toward AI-Driven Defense
If attackers are using AI to scale and adapt, defenders are being pushed in the same direction.
This is where platforms like Blaze AI become relevant—not as a silver bullet, but as part of a broader shift toward intelligent defense.
Instead of relying purely on predefined rules, Blaze AI focuses on:
- Detecting patterns and anomalies in real time
- Automating threat analysis and response
- Providing visibility into emerging AI-driven cyber threats
From what we’re seeing across the industry, this reflects a larger trend: cybersecurity is becoming a contest of learning systems. In other words, AI vs cybersecurity defense is no longer a future concept—it’s already underway.
How to Defend Against AI-Powered Cyber Attacks
There’s no single solution to counter AI-powered cyber warfare, but there are clear priorities emerging across organizations:
1. Adopt AI-Driven Security Tools
Static defenses struggle against adaptive threats. AI-based systems help identify patterns that don’t match known attack signatures.
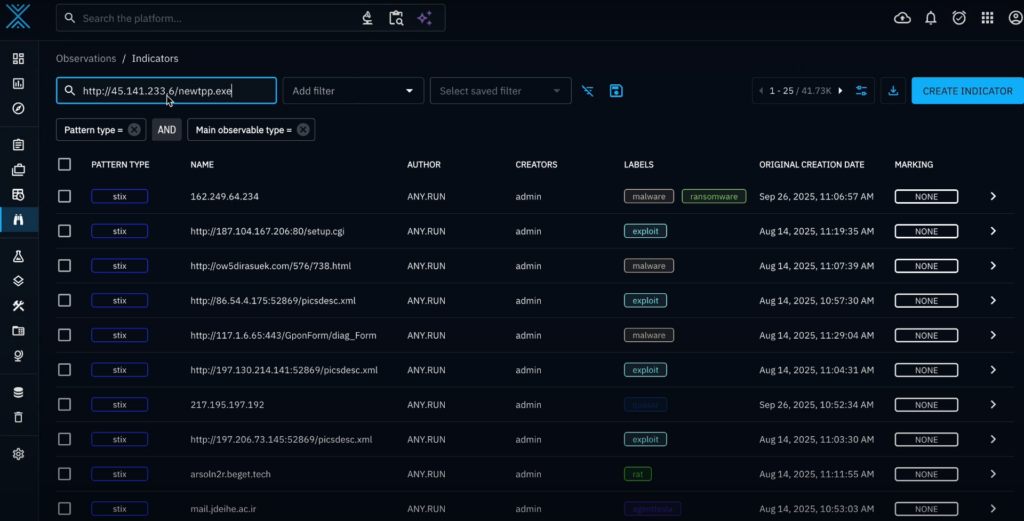
2. Strengthen Threat Intelligence
Understanding emerging AI security risks is critical. The faster teams can contextualize new threats, the better they can respond.
3. Implement Zero-Trust Architectures
Limiting access and continuously verifying users reduces the attack surface—especially important against automated systems.
4. Don’t Ignore the Human Layer
Even the most advanced attacks still exploit human behavior. Training employees to recognize sophisticated phishing and manipulation attempts remains essential.
The Future of Cyber Warfare
Looking ahead, the trajectory is fairly clear.
We’re entering a phase where artificial intelligence in cyber warfare becomes standard practice on both sides. Attackers will continue experimenting with autonomy, while defenders will invest in systems that can respond just as quickly.
The question isn’t whether AI will dominate cyber operations—it’s how quickly organizations can adapt to that reality.
Conclusion
From an analyst standpoint, this moment feels like an inflection point.
The rise of autonomous attack agents, AI-powered malware, and increasingly intelligent cyber threats signals a shift toward faster, more adaptive cyber conflict.
Organizations that treat this as a distant concern risk falling behind. Those that start integrating AI into their defense strategy today will be far better positioned for what’s coming next.
Don’t wait for threats to outpace your defenses. Experience how Cyble Blaze AI can transform your security operations with predictive intelligence and autonomous response. Request a personalized demo today and take the first step toward truly proactive cybersecurity.
Frequently Asked Questions (FAQs) about AI-powered cyber warfare
- What are autonomous attack agents?
Autonomous attack agents are AI systems capable of independently identifying vulnerabilities and launching cyberattacks with minimal human intervention.
- How is AI used in cyber warfare?
AI is used to automate attacks, improve targeting, evade detection, and scale operations more efficiently.
- Is AI making cyberattacks more dangerous?
Yes. AI increases both the speed and sophistication of cyberattacks, making them harder to detect and respond to.
- What is Blaze AI in cybersecurity?
Blaze AI is an artificial intelligence-powered cybersecurity solution that combines intelligence and automation to detect, analyze, and respond to modern cyber threats.
The post AI-Powered Cyber Warfare: How Autonomous Attack Agents Are Changing the Threat Landscape appeared first on Cyble.
Cyble – Read More