Chinese APT Abuses Multiple Cloud Tools to Spy on Mongolia
The threat actor gave itself plenty of options to support command and control, tapping Microsoft Outlook, Slack, Discord, and file.io for online espionage.
darkreading – Read More
The threat actor gave itself plenty of options to support command and control, tapping Microsoft Outlook, Slack, Discord, and file.io for online espionage.
darkreading – Read More

Cisco Talos is aware of UAT-4356‘s continued active targeting of Cisco Firepower devices’ Firepower eXtensible Operating System (FXOS). UAT-4356 exploited n-day vulnerabilities (CVE-2025-20333 and CVE-2025-20362) to gain unauthorized access to vulnerable devices, where the threat actor deployed their custom-built backdoor dubbed “FIRESTARTER.” FIRESTARTER considerably overlaps with the technical capabilities of RayInitiator’s Stage 3 shellcode that processes incoming XML-based payloads to endpoint APIs.
In early 2024, Cisco Talos attributed ArcaneDoor, a state-sponsored campaign focused on gaining access to network perimeter devices for espionage, to UAT-4356.
Customers are advised to refer to Cisco’s Security Advisory for mitigation and detection guidance, indicators of compromise (IOCs), affected products, and applicable software upgrade recommendations.
FIRESTARTER is a malicious backdoor implanted by UAT-4356 that allows remote access and control to execute arbitrary code inside the LINA process, a core component of Cisco’s ASA and FTD appliances running FXOS.
UAT-4356 established persistence for FIRESTARTER on compromised devices by manipulating the mount list for Cisco Service Platform (CSP), namely “CSP_MOUNT_LIST”, to execute FIRESTARTER. The mount list allows programs and commands to be executed as part of the device’s boot sequence. The persistence mechanism triggers during graceful reboot (i.e., when a process termination signal is received). FIRESTARTER also checks the runlevel for value 6 (indicating device reboot) and in case of a match, writes itself to backup location “/opt/cisco/platform/logs/var/log/svc_samcore.log” and updates the CSP_MOUNT_LIST to copy itself back to “/usr/bin/lina_cs” and then be executed. When FIRESTARTER runs after a reboot, it restores the original CSP_MOUNT_LIST and removes the trojanized copy. Because the runlevel triggers establishment of this transient persistence mechanism, a hard reboot (for example, after the device has been unplugged from power) effectively removes the implant from the device.
FIRESTARTER has used the following commands to establish persistence for itself using the transient persistence mechanism:
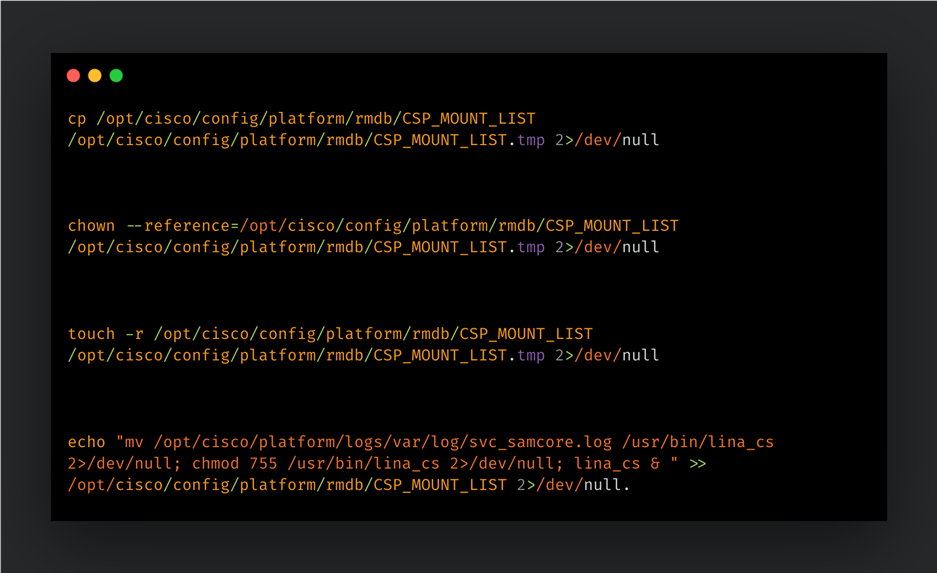
When the implant injects itself into the LINA process, it removes the traces of its persistence mechanism by restoring the CSP_MOUNT_LIST from a temporary copy (“CSP_MOUNTLIST.tmp”), then removing the temporary copy and the FIRESTARTER file from disk (“/usr/bin/lina_cs”).
FIRESTARTER can run arbitrary shellcode received by the device. A pre-defined handler function specified by a hardcoded offset in the LINA process’ memory is replaced by an unauthorized handler routine that parses the data being served to it. FIRESTARTER specifically looks for a WebVPN request XML. If the request data received matches a specific pattern of custom-defined prefixing then the shellcode that immediately follows it is executed in memory. If the prefixing bytes are not found, then the data is treated as regular request data and passed to the original handler function (if any).
FIRESTARTER’s loading mechanism, Stage 2 shellcode (i.e., the actual request handler component), handler function replacement, XML parsing for magic bytes, and final payload execution display considerable overlaps with RayInitiator’s Stage 3 deployment actions and accompanying artifacts.
FIRESTARTER first reads the LINA process’ memory to search for and verify the presence of the bytes (long) 0x1, 0x2, 0x3, 0x4, 0x5 at specific locations in memory. If found, FIRESTARTER will then query the process’ memory to find an “r-xp” memory range for the shared library “libstdc++.so”. It then copies the next stage shellcode (Stage 2) to the last 0x200 bytes of the memory region. FIRESTARTER then overwrites an internal data structure in the LINA process’ memory to replace a pointer to a WebVPN-specific, legitimate XML handler function with the address of the malicious Stage 2 shellcode.
The malicious shellcode is triggered as part of the authentication API’s request handling process and parses the incoming request data for magic markers signifying an executable payload. If found, the executable payload is then executed on the compromised device.
The presence of the following artifacts – specifically the filenames “lina_cs” and “svc_samcore.log” – though somewhat brittle indicators, may indicate the presence of the FIRESTARTER on a Firepower device:
For more comprehensive detection guidance, please refer to Cisco’s Security Advisory here. Please also refer to CISA’s update to V1: Emergency Directive (ED) 25-03: Identify and Mitigate Potential Compromise of Cisco Devices and FIRESTARTER Backdoor Malware Analysis Report for more information and guidance.
We recommend that Cisco customers follow the steps recommended in Cisco’s advisory, with particular attention to any applicable software upgrade recommendations. Organizations impacted can initiate a TAC request for Cisco support.
A FIRESTARTER infection may be mitigated on all affected devices by reimaging the devices.
On Cisco FTD software that is not in lockdown mode, there is also the option of killing the lina_cs process then reloading the device:
> expert $ sudo kill -9 $(pidof lina_cs) $ exit > reload
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org.
The following Snort rules cover the vulnerabilities CVE-2025-20333 and CVE-2025-20362: 65340, 46897.
Snort rules covering FIRESTARTER: 62949
The following ClamAV signatures detect this threat: Unix.Malware.Generic-10059965-0
Cisco Talos Blog – Read More
In many countries, spring is the traditional time for filing income tax returns. These documents are a goldmine for bad actors because they contain a wealth of personal data, such as employment history, income, assets, bank account details — the list goes on. It’s no surprise that scammers ramp up their efforts around this time; the internet is currently crawling with fake websites designed to look exactly like government resources and tax authorities.
With deadlines looming and numbers to crunch, the rush to get everything done in good time can cause people to let their guard down. In the shuffle, it’s easy to miss the signs that the site where you’re detailing your finances has zero connection to the revenue service, or that the file you just downloaded, supposedly from a tax inspector, is actually malware.
In this post, we break down how these fraudulent tax agency sites operate across different countries and what you should absolutely avoid doing to keep your money and sensitive information safe.
This season, attackers have been spoofing tax authority websites across numerous countries, including the official government portals of Germany, France, Austria, Switzerland, Brazil, Chile, and Colombia. On these fraudulent sites, scammers harvest credentials for legitimate services, and steal personal data before offering to process a tax deduction — provided the victim enters their credit card details. In some cases, they even charge a fee for this fraudulent service.
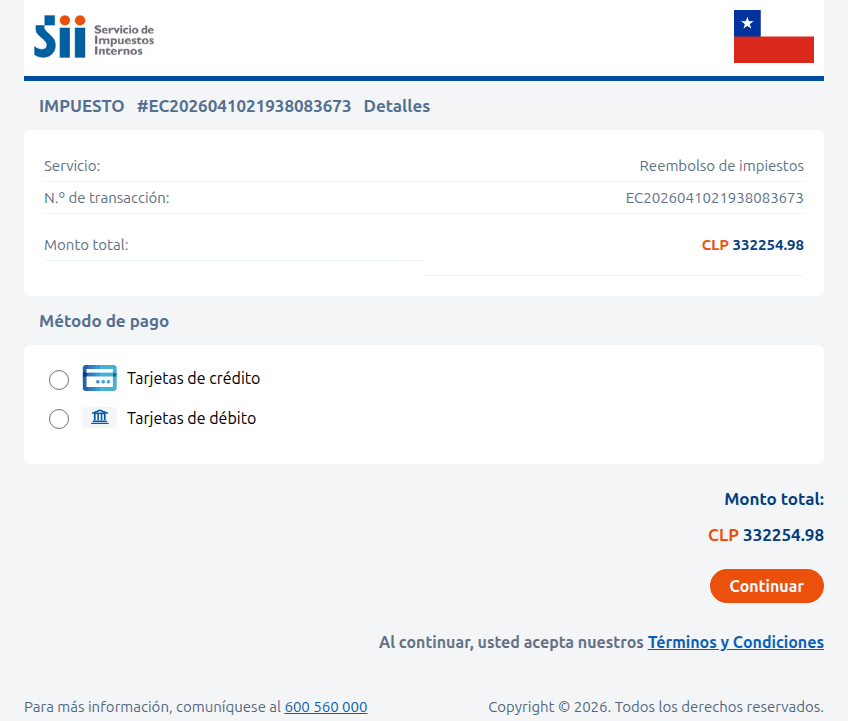
A site imitating the Chilean tax authority. The victim is prompted to enter their credit card information to receive a substantial tax refund — roughly US$375. Instead, the funds are siphoned from the victim’s account directly to the scammers
Sometimes, the tactic involves accusations issued on behalf of government bodies. In the image below, for example, a “head of tax audit” in Paris informs the victim that they provided incomplete income information. To avoid penalties, the user is told to download a document and make corrections immediately. However, the PDF file hides something much worse: malware.
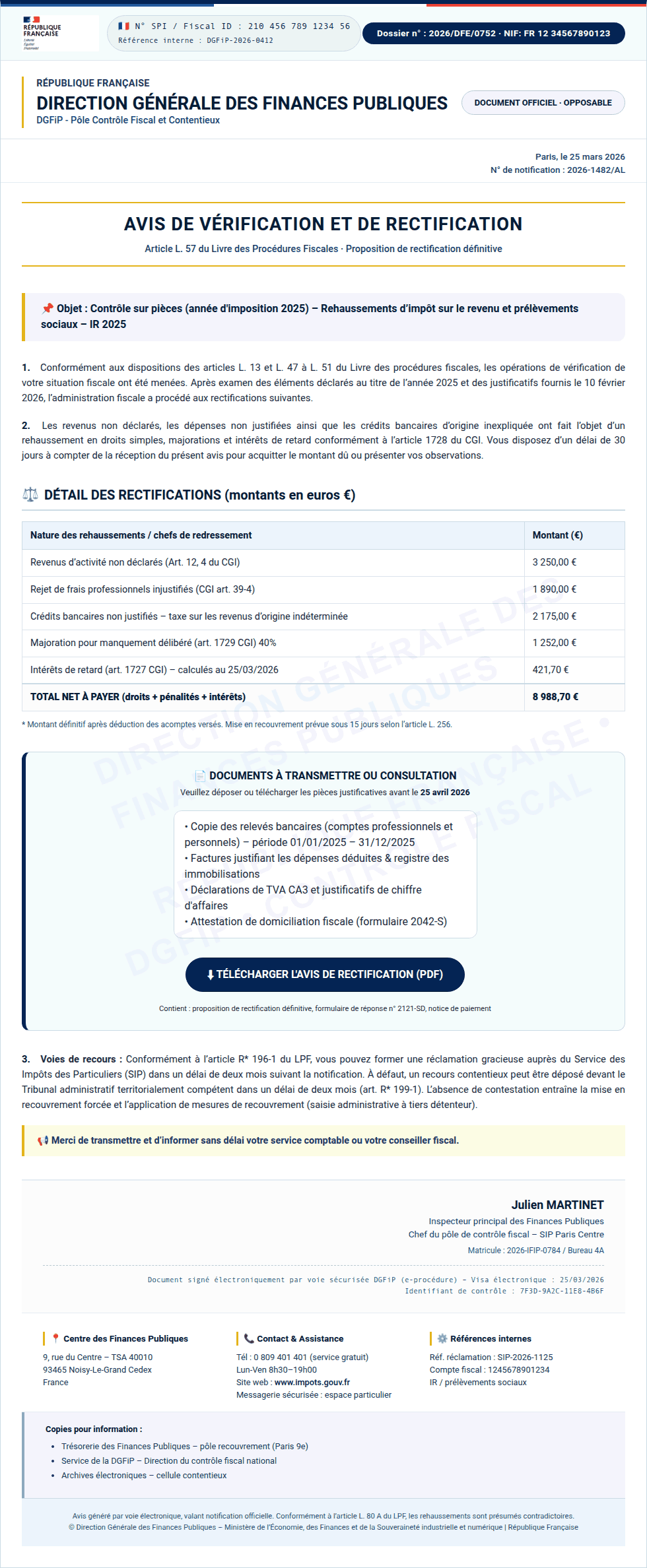
Instead of an official document from the French tax service, the user finds malware waiting inside the PDF
In Colombia, a fake National Directorate of Taxes and Customs site similarly prompts users to download documents that must be “unlocked with a security key”. In reality, this is simply a password-protected, malicious ZIP archive.
Beyond phishing sites mimicking legitimate resources, our experts have discovered fraudulent websites promising paid services for filling out and auditing tax documents — and stealing high-value data, such as taxpayer identification numbers (TINs), instead.
Cryptocurrency holders have emerged as a specific target for attackers. Fake German tax authorities are demanding that wallet owners “verify their digital asset holdings”, citing EU regulations for tax calculation purposes. And of course, there’s a “silver lining”: it turns out crypto earnings are supposedly tax-exempt! However, to claim this generous benefit, users must go through a “verification” procedure. The site even promises to encrypt data using a “2048-bit SSL protocol”.
To complete the “verification” process, users are prompted to enter their seed phrase — the unique sequence of words tied to a crypto wallet that grants full recovery access. This request is paired with a threat: refusing to provide the data will lead to serious legal consequences, such as fines up to one million euros or criminal prosecution.
Attackers pulled a similar stunt on French users as well. They created a non-existent “Crypto Tax Compliance Portal”, which mimics the design of the French Ministry of Economy and Finance website. The phishing site aggressively demands that French residents submit a “digital asset declaration”.
After the user enters their personal information, the scammers prompt them to either manually enter their seed phrase, or “link” their crypto wallet to the portal. If they go through with this, their MetaMask, Binance, Coinbase, Trust Wallet, or WalletConnect wallets will be drained.
When you have AI at your fingertips that can instantly generate text and fill out spreadsheets, there’s a serious temptation to delegate everything to it. Unfortunately, this can lead to serious consequences. First, all popular chatbots process your data on their servers, which puts your sensitive information at risk of a leak. Second, they sometimes make incredibly foolish mistakes, and that can lead to actual trouble with the taxman.
Before you tell a chatbot or an AI agent how much money you made last year — complete with detailed personal and banking info — remember how frequently leaks occur within AI-powered services and consider the risks. Don’t discuss your income with AI, don’t give it personal details like your name or address, and under no circumstances should you upload photos or numbers of vital documents such as passports, insurance info, or social security numbers. Files containing confidential information should be kept in encrypted containers, such as Kaspersky Password Manager.
If you’re still determined to use AI tools, run them locally. This can be done for free even on a standard laptop, and we’ve previously covered how to set up local language models using DeepSeek as an example. However, the quality of the output from these models is often subpar. It’s quite possible that double-checking every digit in an AI-generated response will take more time than just filling out the paperwork manually. Remember, you’re the one accountable to the tax office for any errors — not the AI.
Finally, watch out for phishing AI models that offer “assistance” with tax filing. Kaspersky experts have discovered websites where users are prompted to upload tax invoices, supposedly for the automated generation of returns and deduction claims. Instead, attackers collect this personal data to resell on the dark web, or to use in future phishing attacks, blackmail, and extortion schemes.
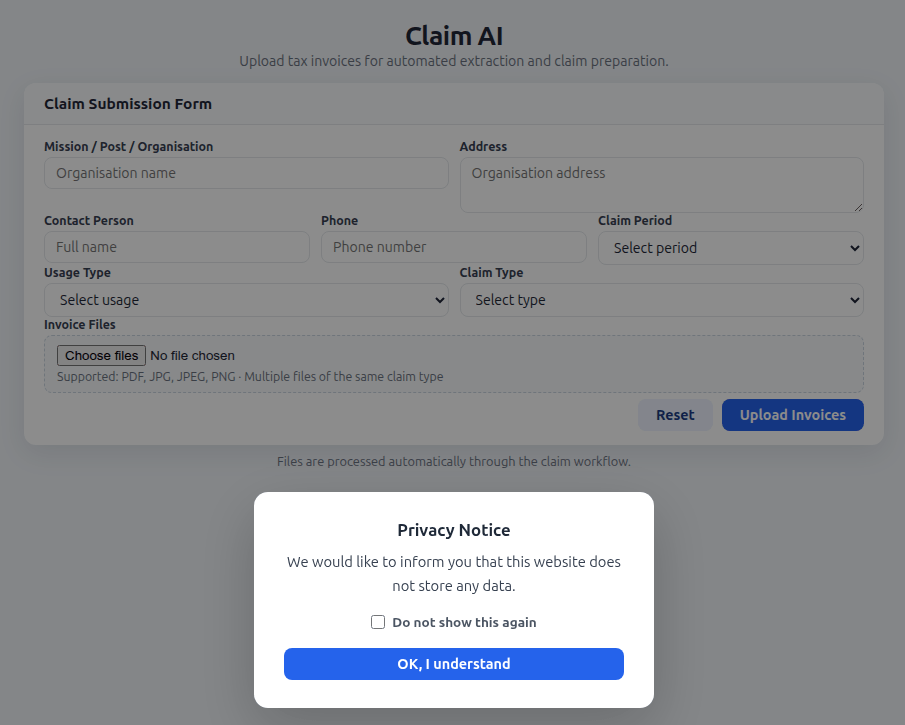
The creators of a fake AI tool prompt users to upload tax documents, and kindly assure them that the site doesn’t store any user data. In reality, every piece of information entered — name, address, documents, contact person, phone number — ends up in the hands of cybercriminals
Remember that all legitimate AI services explicitly warn users not to share confidential data, and tax documents certainly fall into this category. Any AI tools promising to help you handle your tax paperwork are quite simply a scam.
Further reading on phishing and data security:
Kaspersky official blog – Read More
360 Digital Security Group claims to have uncovered 1,000 vulnerabilities using AI, including at the Tianfu Cup hacking contest.
The post Chinese Cybersecurity Firm’s AI Hacking Claims Draw Comparisons to Claude Mythos appeared first on SecurityWeek.
SecurityWeek – Read More
The data is held by the UK Biobank charity and includes genetic sequences, blood samples, medical scans and lifestyle information.
The Record from Recorded Future News – Read More
I’ve followed SUSE for decades. Here’s how it’s helping organizations control data and avoid lock-in.
Latest news – Read More
Sean Plankey reportedly told colleagues that he needed to focus on assuaging concerns about his Coast Guard work that had led Sen. Rick Scott (R-FL) to block his nomination.
The Record from Recorded Future News – Read More
If you have a Bluetooth-supported TV or streaming stick, you can connect any wireless headphones to watch content without distracting others.
Latest news – Read More
New analysis from Abnormal AI reveals how attackers have abandoned technical exploits to weaponize routine workflows and internal trust.
The post The Behavioral Shift: Why Trusted Relationships Are the Newest Attack Surface appeared first on SecurityWeek.
SecurityWeek – Read More
The company will hire new talent and expand operations across the US and other allied countries.
The post Rilian Raises $17.5 Million for AI-Native Security Orchestration appeared first on SecurityWeek.
SecurityWeek – Read More