Mallory Launches AI-Native Threat Intelligence Platform, Turning Global Threat Data Into Prioritized Action
Austin, Texas, United States, 9th April 2026, CyberNewswire
Hackread – Cybersecurity News, Data Breaches, AI and More – Read More
Austin, Texas, United States, 9th April 2026, CyberNewswire
Hackread – Cybersecurity News, Data Breaches, AI and More – Read More
BTS, a global K-pop phenomenon, has recently made a comeback from an almost four-year hiatus: the members of the group were completing mandatory military service in South Korea. For this reason it comes as no surprise that cybercriminals have taken advantage of the band’s highly anticipated world-tour — ARIRANG — to launch a campaign of fake websites targeting fans eager to buy tickets.
We’ve identified at least 10 fraudulent domains that mimic the official pre‑sale pages for the band’s concerts in Argentina, Brazil, Chile, Colombia, France, Mexico, Peru, Portugal, and Spain — all created in early April. We explain how the scammers operate, and how to avoid buying fake tickets.
Due to the high demand for the world-tour tickets, some of the event organizers prepared additional measures to ensure there are no ticket scalpers. In Brazil, the ticketing services adopted a “pre‑booking” format: the user first makes an online reservation, and then pays in person at the box office. Although in essence a good idea, the change has caused confusion among fans and created an opportunity for criminals to commit fraud.
Scammers create pages that are nearly identical to the official ones, replicating the layout, design, and the entire purchasing journey. For ordinary users, the experience seems completely legitimate. The links to these websites are circulating on social media — mainly on Instagram.
In Brazil, victims are prompted to make payments via PIX — an instant payment system operated by the Central Bank of Brazil. In some cases, the sites even simulate a card‑payment option, but claim high demand or system errors to pressure users into choosing PIX. PIX payments are then directed to money mule accounts — making it difficult to recover the funds.
The scam is a perfect example of how social engineering works. It exploits a massive and highly engaged fanbase — leading many users to act impulsively. The fake “errors” that the website displays during payment create a sense of urgency and cause panic — the scammers are well aware of how quickly BTS tickets sell out. In addition, doubts about the new purchasing system established by the event organizers help criminals make fake websites even more convincing.
If you really want to get tickets to your favorite group’s concert but not fall victim to the scammers, it’s important to keep these basic cybersecurity rules in mind:
More on scams:
Kaspersky official blog – Read More
Germany’s economy is a precision machine: finance fuels it, manufacturing builds it, telecom connects it, IT optimizes it, and healthcare sustains it. The country sits at the crossroads of industrial power and digital transformation, making it irresistibly attractive to attackers.
In this article, we explore real-world attacks targeting five critical German industries, analyzed by ANY.RUN’s analysts using Interactive Sandbox and Threat Intelligence Lookup. Each case is not theory. It is a live wire, recently observed, carefully dissected.
Why Germany?
Germany’s industrial backbone — the Mittelstand of small and medium-sized enterprises, alongside globally recognized corporations in chemicals, automotive, and engineering — represents a vast attack surface. These organizations often store sensitive IP, manage critical infrastructure, and handle large financial transactions, yet historically have underinvested in cybersecurity relative to their size and importance.
Geopolitics adds fuel to the fire provoking a sharp increase in professional, often state-directed attacks by APT groups (Advanced Persistent Threats) linked to geopolitical conflicts. Germany’s role in the EU, NATO, and global trade makes it a high-value intelligence target for foreign actors.
Phishing remains the most prevalent attack vector. The BSI confirmed that phishing attacks expanded well beyond the financial sector in 2024, with attackers impersonating streaming services, logistics firms, government agencies, and enterprise software platforms like Microsoft 365.
ANY.RUN’s Threat Intelligence Lookup, a searchable database of threat data from live malware analysis by a community of over 15K SOC teams, supports the mapping of attack indicators to specific sectors and regions.
A local cyberthreat landscape can be revealed by combining lookups for an industry and a malware sample submission country, and by limiting the search period to see the most recent threats.
industry:”Telecommunications” AND submissionCountry:”DE”
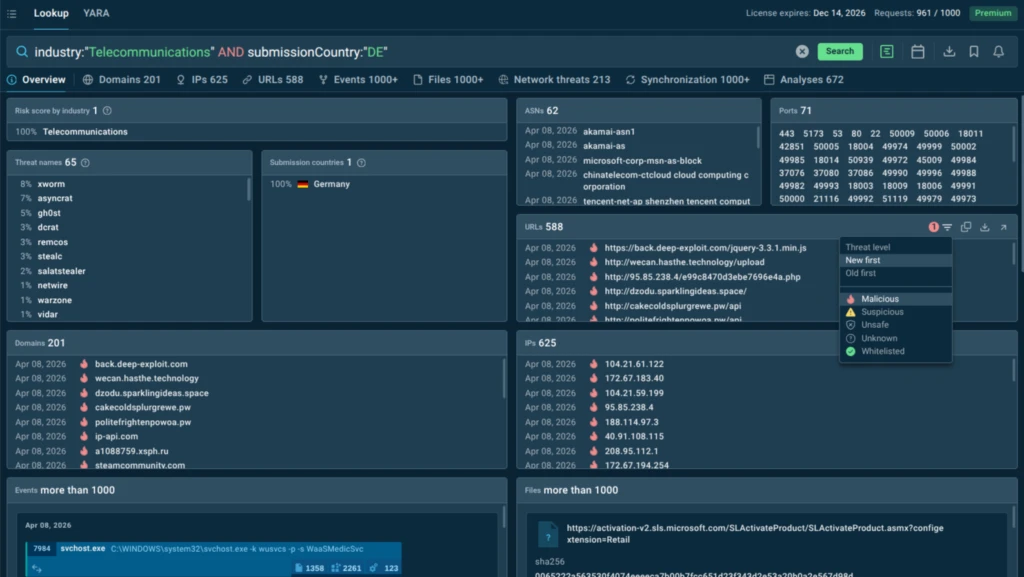
Search for a threat, country, and industry, switch to the Analyses tab in the results, and see a selection of sandbox analyses.
industry:”Telecommunications” AND submissionCountry:”DE” AND threatName:”xworm”
Pivot your research via TI Lookup using IOCs from search results and sandbox analyses and boost triage, detection, and threat hunting in your SOC.
Financial organizations in Germany operate in a high-trust, high-value environment:
This makes employee credentials a golden key. Microsoft 365 credential theft is a dominant threat vector in this sector. Attackers seek to compromise corporate email accounts to intercept transactions, conduct Business Email Compromise (BEC) fraud, or use valid credentials as a launchpad for deeper network intrusion.
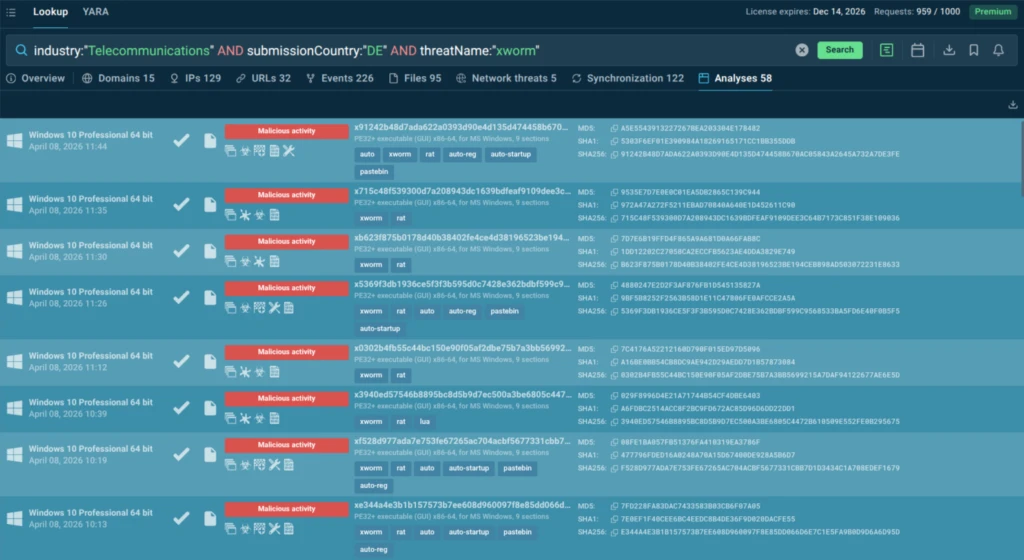
Target
A German investment company managing portfolios in private equity, real estate, and hedge funds. The attack was precision-targeted: the victim’s corporate email address was embedded directly into the phishing link, encoded in Base64.
Attack Type
Spearphishing (targeted credential theft) for Microsoft 365 accounts. ANY.RUN’s sandbox classified this threat as FlowerStorm — a sophisticated phishing-as-a-service platform known for its multi-stage evasion techniques and precision targeting.
Kill Chain
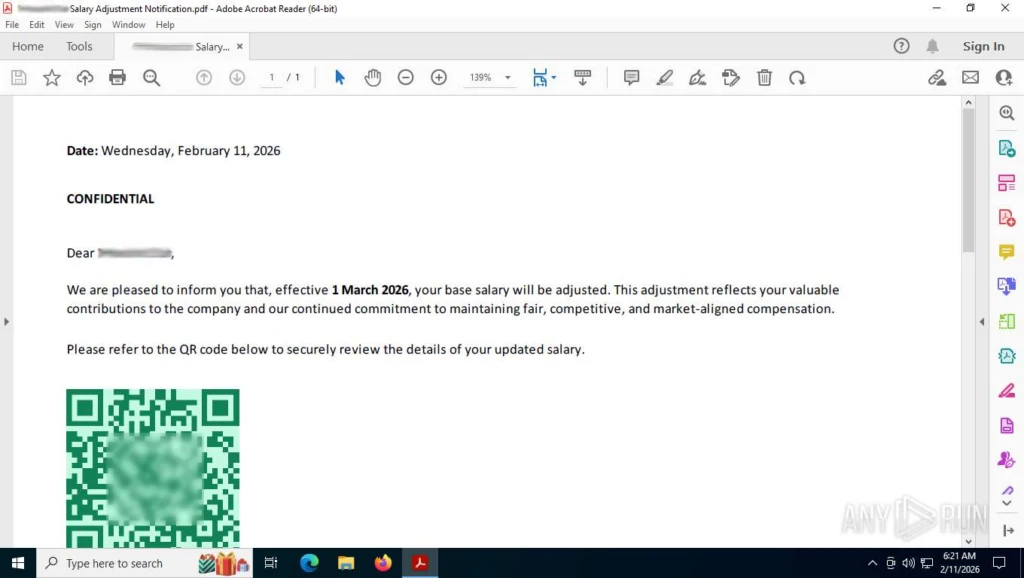
Why It Works
FlowerStorm combines multiple layers of evasion (QR codes, browser fingerprinting, CAPTCHA, Base64 encoding) with surgical targeting. The salary-themed lure is psychologically effective: employees in a finance firm expect payroll-related communications, reducing suspicion. The Microsoft 365 OAuth imitation is technically convincing enough to fool even security-conscious users.
Healthcare in Germany is:
This creates a perfect storm for authentication abuse attacks.
Healthcare breaches carry compounded consequences: regulatory penalties under GDPR, reputational damage, potential disruption to patient care, and the loss of research data that may represent years of work and significant public investment.
Target
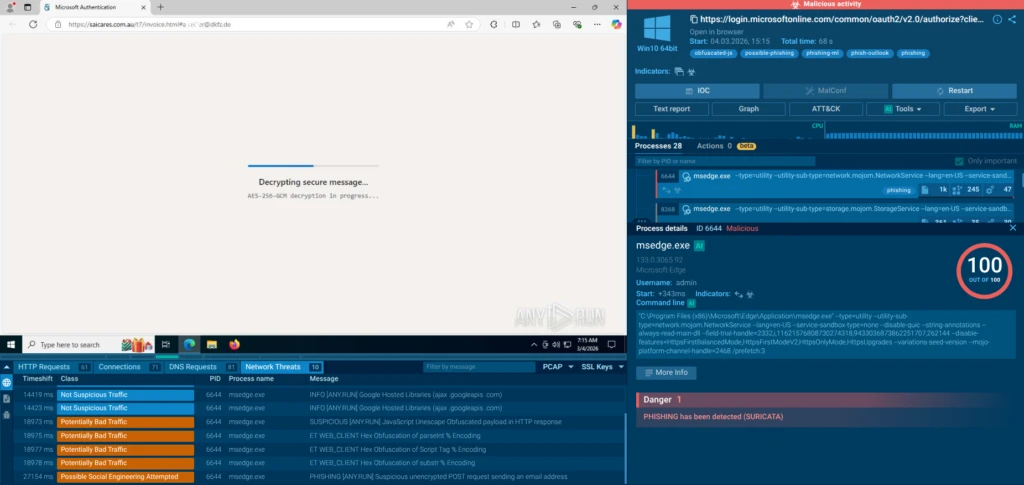
Germany’s largest medical research center. The attack was highly targeted: the victim’s corporate email appeared in plaintext in the OAuth state parameter and in Base64 in the URL fragment of the phishing page.
Attack Type
Phishing via Microsoft OAuth abuse combined with a fake Outlook login page. The attackers exploited Microsoft’s legitimate OAuth 2.0 authentication mechanism, substituting a malicious redirect_uri to capture credentials after the authentication handshake.
Kill Chain
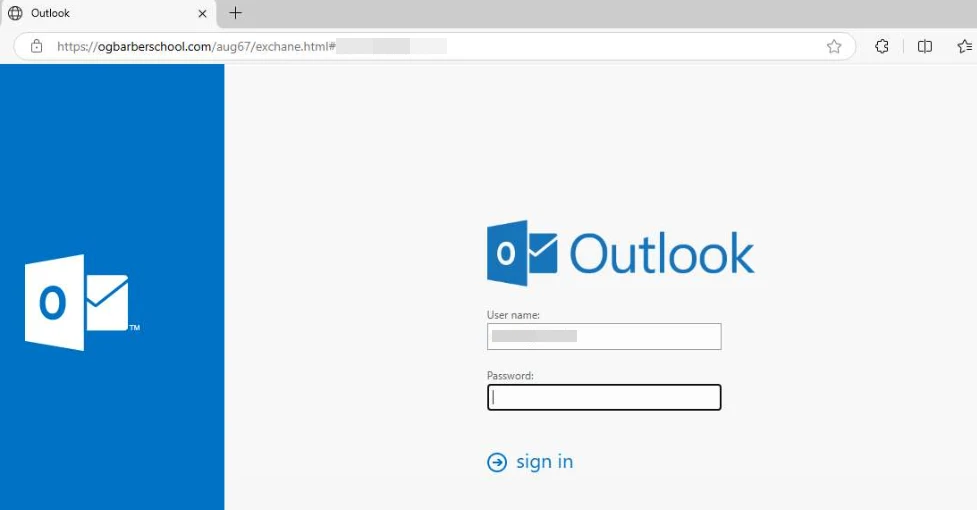
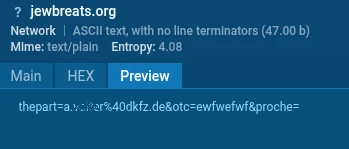
Why It Works
This attack is particularly dangerous because it begins with a genuine Microsoft domain. A victim who inspects the initial link sees a legitimate login.microsoftonline.com URL, providing false reassurance. By the time the malicious redirect occurs, the victim is already engaged. The use of a compromised WordPress site and decentralized storage makes the infrastructure difficult to detect and take down quickly.
IT companies:
The sector’s familiarity with technology can create a paradoxical blind spot: IT professionals may be more likely to click links in emails that appear technical or work-related, assuming their technical knowledge makes them immune to social engineering.
Target
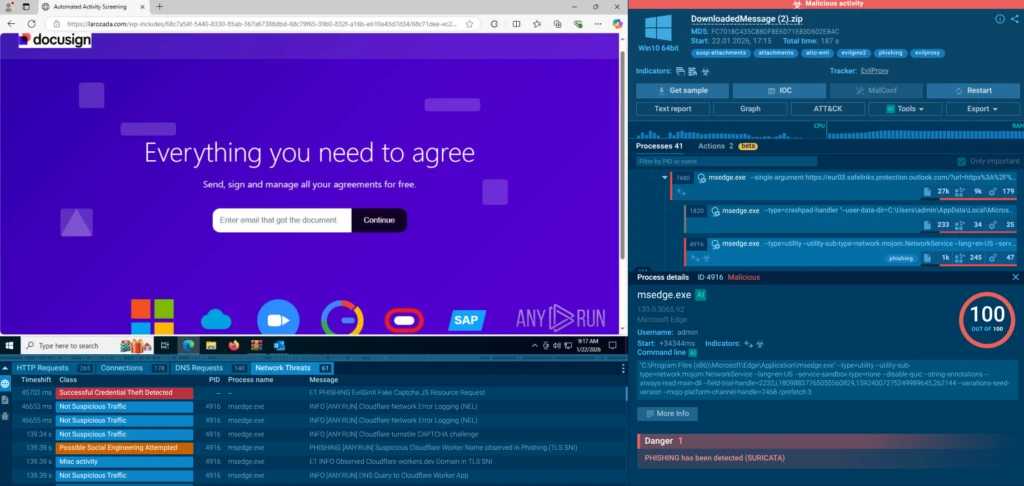
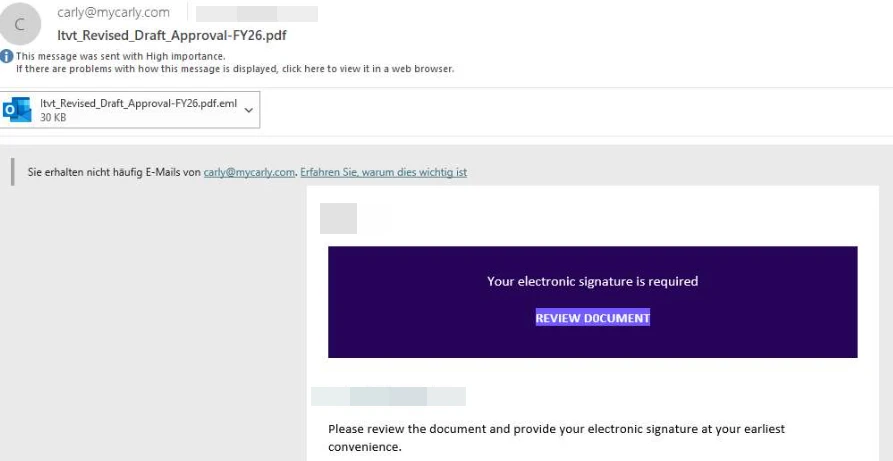
A German IT company. The attack targeted a specific employee, whose email was extracted from the data parameter of a Microsoft Safe Links wrapper, indicating the attacker had prior visibility into the target’s email infrastructure.
Attack Type
Phishing via a combination of EvilProxy and EvilGinx2: two reverse proxy tools used in tandem. EvilProxy serves as the primary credential harvesting platform, while EvilGinx2 handles session token interception. Together, they create a real-time proxy of Microsoft’s login infrastructure capable of bypassing multi-factor authentication.
Kill Chain
Why It Works
The use of legitimate services (Mailchimp, Cloudflare Workers, WordPress) at each stage of the attack chain makes it nearly impossible for conventional email filters and web gateways to block. The final EvilProxy stage defeats MFA entirely by hijacking the post-authentication session rather than attempting to steal the second factor. This is an adversary-in-the-middle attack that neutralizes one of the most commonly recommended security controls.
Using TI Lookup, we can see that larozada[.]com is intensely correlated with this attack scenario:
domainName:”larozada.com”
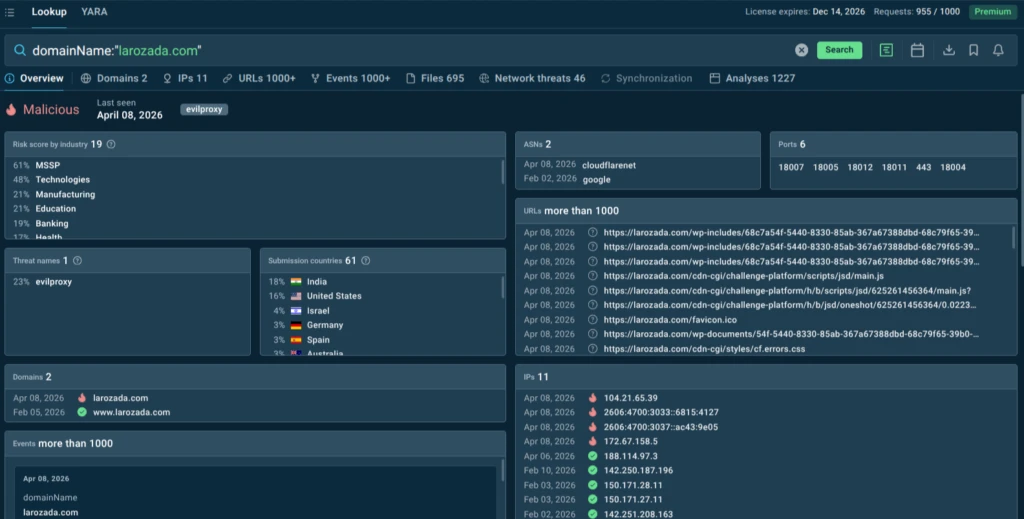
Integrate Threat Intelligence Feeds in your security stack to have it continuously updated with a real-time stream of indicators (domains, URLs, IPs) for early detection and timely response.
Telecom companies:
Telecom companies are targeted for multiple strategic reasons: access to customer data at scale, the potential for SIM-swapping attacks, the ability to intercept communications, and the value of internal network access for espionage or infrastructure disruption.
Account takeover via Microsoft 365 credential theft is a priority threat for this sector, as telecom employees use cloud platforms extensively for internal communications, customer management, and operational coordination.
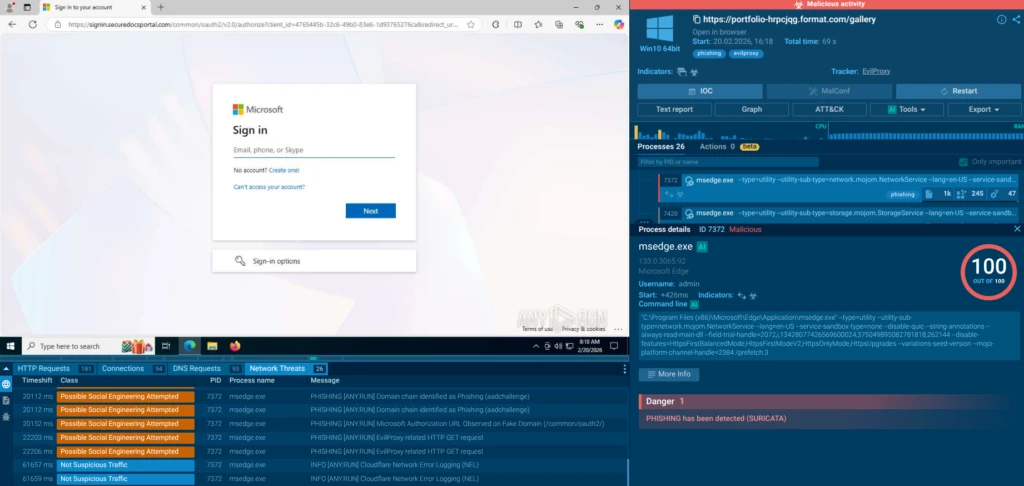
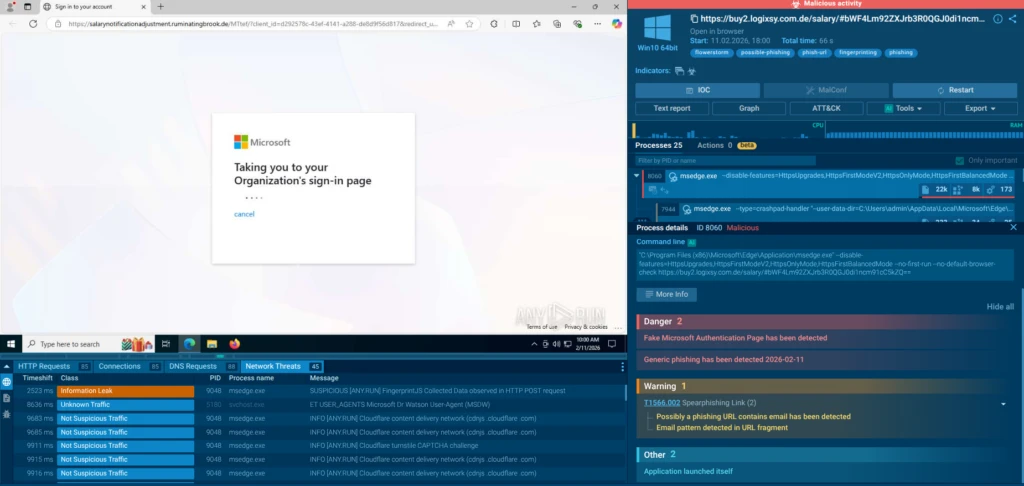
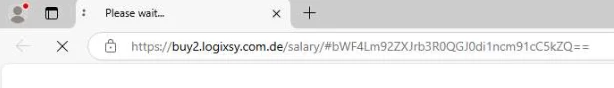
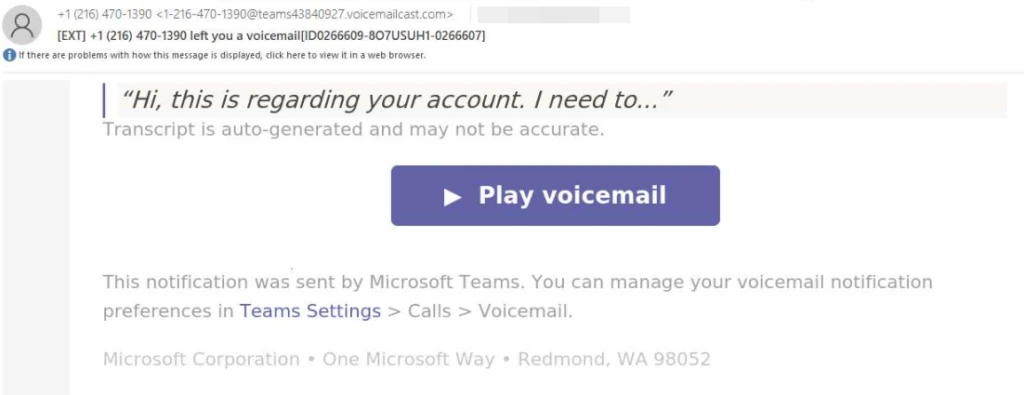
Target
An employee of a German telecommunications company. Unlike the finance and healthcare cases, this campaign used a non-personalized phishing page (no email embedded in the URL) suggesting a broader campaign that may target multiple companies simultaneously rather than a single individual.
Attack Type
Phishing via EvilProxy (Phishing-as-a-Service) — a commercial reverse proxy platform that proxies the real Microsoft login page in real time, intercepting session tokens and bypassing MFA without ever needing to steal a password.
Kill Chain
Why It Works
EvilProxy is commercially available as a service, dramatically lowering the skill threshold for attackers. The use of a legitimate portfolio platform as the initial URL makes detection by email gateways extremely difficult. The MFA bypass via session cookie theft is highly effective against organizations that believe MFA alone is sufficient protection.
Germany’s manufacturing sector:
Germany’s manufacturing sector is the engine of its economy, encompassing global leaders in chemicals, automotive, engineering, and consumer goods. They are also increasingly connected: Industry 4.0 technologies, IoT sensors, operational technology (OT), and cloud-integrated production systems have blurred the line between IT and physical operations.
The consequences of a successful attack extend beyond data loss to potential operational shutdown, physical equipment damage, and supply chain disruption.
Social engineering attacks targeting manufacturing employees are particularly effective because plant-floor and operations staff are not traditionally cybersecurity-trained, and Microsoft Teams has become a standard communication tool across these large organizations.
Target
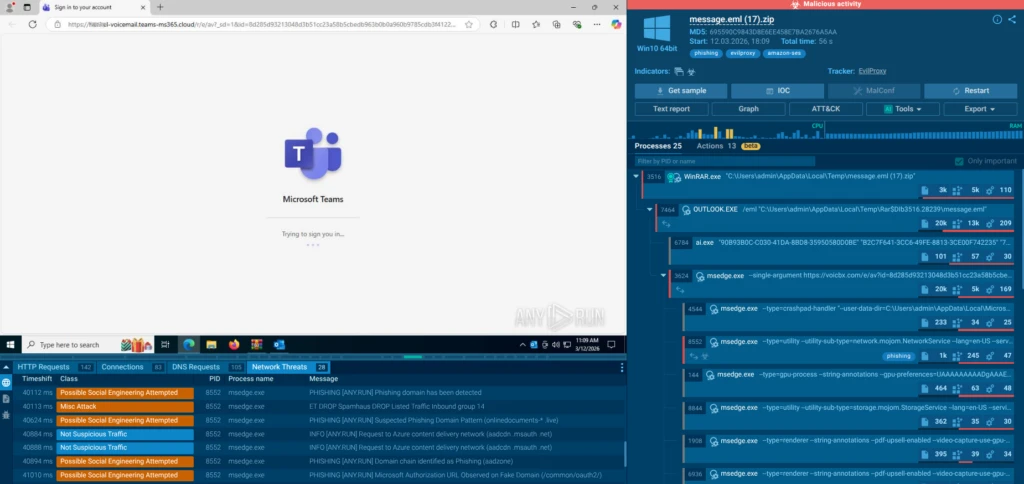
A large German industrial conglomerate, a global producer of chemical products and consumer goods. This attack was unusually specific: the phishing domains were registered to include the target company’s name, and the fake login page was styled to match the company’s Microsoft Teams branding — indicating advance reconnaissance.
Attack Type
Phishing via EvilProxy using a Microsoft Teams voice message as bait. The attack was delivered via Amazon SES, a legitimate email delivery infrastructure, making it difficult for email security tools to flag based on sender reputation.
Kill Chain
Why It Works
The combination of a highly plausible lure (missed Teams voice message), delivery via Amazon SES (bypassing sender reputation filters), and company-branded phishing pages makes this attack unusually convincing. The use of Okta for the fake authentication page suggests the attackers were aware of the target company’s specific identity infrastructure.
All five cases have been collected between January and March 2026. Finance, healthcare, IT, telecommunications, and manufacturing, the five most economically significant sectors in Germany, are not theoretical targets. They are active targets. This is systematic pressure on the German economy, not isolated incidents.
ANY.RUN’s Threat Intelligence Lookup data reinforces this: searching for EvilProxy and FlowerStorm threats linked to German organizations over the past 60 days returned more than 220 analyses, confirming that these campaigns are ongoing and widespread.
(threatName:”flowerstorm” OR threatName:”evilproxy”) and submissionCountry:”DE”
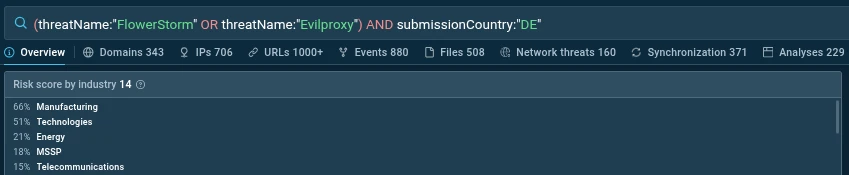
Several of these attacks show clear signs of advance reconnaissance. Phishing domains were registered with the target company’s name embedded, pages were styled to match corporate branding, and victim email addresses were pre-loaded into URLs. This level of preparation (particularly in the manufacturing case) goes beyond generic mass phishing and suggests attackers are investing in targeted intelligence gathering before launching campaigns. Some cases also used universal phishing pages, indicating a mix of targeted and mass-scale approaches within the same threat actor ecosystem.
The lures used in these attacks are not generic. A salary-themed document for a finance employee, a missed Teams voice message for a manufacturing executive, a “Review document” prompt for an IT professional. Attackers appear to be selecting bait that fits the professional context of their targets, increasing click rates and reducing suspicion. This contextual adaptation of social engineering is a significant evolution in phishing tradecraft.
EvilProxy, EvilGinx2, and FlowerStorm are not bespoke tools used by elite threat actors. They are commercially available phishing platforms sold as services. This means the barrier to launching a sophisticated, MFA-bypassing attack against a German enterprise is now accessible to a broad range of cybercriminals. These platforms proxy real Microsoft login pages in real time, intercept session cookies after successful MFA completion, and provide the attacker with a fully authenticated session — all without ever knowing the victim’s password or one-time code.
Organizations that rely on MFA as their primary defense against credential theft need to understand that adversary-in-the-middle phishing renders standard MFA ineffective. Phishing-resistant MFA (such as FIDO2 hardware keys) and Zero Trust session validation are required to defend against these techniques.
For executives across finance, healthcare, telecom, IT, and manufacturing, cybersecurity is no longer just a technical function. It is a business continuity and risk management discipline.
The attacks described in this article share a common trait: they move fast, abuse trusted services, and bypass traditional defenses.
To counter this, organizations need more than tools. They need a workflow-driven approach, where threat intelligence and malware analysis directly improve how the SOC operates.
Here is how this translates into measurable protection across core SOC workflows.
The Challenge:
Detection gaps, delayed visibility into new campaigns, and high volumes of low-context alerts.
What to do:
Instead of waiting for alerts, your SOC gains early visibility into attacker infrastructure, often within hours of campaign emergence
Business impact:
Executive outcome: lower probability of high-severity incidents and reduced exposure window.
The Challenge:
Slow investigations, manual enrichment, and excessive escalation to senior analysts.
What to do:
Analysts move from fragmented investigation to instant, evidence-based decisions, with average detection times measured in seconds.
Business impact:
Executive outcome: more efficient SOC operations with lower staffing pressure and faster decision cycles.
The Challenge:
Limited visibility into attack scope and delayed containment decisions.
What to do:
Incidents are no longer black boxes. Teams gain full kill-chain visibility within seconds and reduce response time significantly
Business impact:
Executive outcome: minimized financial and operational impact from active threats.
The Challenge:
Outdated data, manual validation, and lack of prioritization based on business risk.
What to do:
Threat hunting becomes data-driven and context-aware, leveraging live attack activity across thousands of organizations.
Business impact:
Executive outcome: improved risk visibility and proactive defense posture.
When these capabilities are aligned across workflows, the effect compounds:
Operational gains:
Business outcomes:
The difference between a resilient organization and a vulnerable one is not whether attacks happen. It is whether your teams can see threats early, understand them instantly, and act before impact spreads.
By combining TI Feeds (visibility), TI Lookup (context), and Interactive Sandbox (depth), you turn security operations into a measurable business advantage, not just a defensive necessity.
The five attacks documented in this report share a common thread: they are sophisticated, targeted, and actively exploiting the trust that German employees place in familiar platforms like Microsoft 365, Outlook, and Teams. They represent a new generation of phishing campaigns that have moved far beyond bulk spam — into precision-engineered operations that research their targets, customize their lures, and deploy infrastructure specifically designed to survive detection.
The good news is that these attacks are detectable. ANY.RUN’s Interactive Sandbox can analyze suspicious URLs and files in real time, tracing every redirect, every script, every network connection in the attack chain. The Threat Intelligence Lookup provides historical context — showing how many organizations have seen the same indicators, which industries are most targeted, and what threat families are most active.
In an economy where a single successful breach can cost billions and disrupt national supply chains, visibility and speed of response will define resilience.
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams investigate threats faster and with greater clarity across modern enterprise environments.
It allows teams to safely execute suspicious files and URLs, observe real behavior in an Interactive Sandbox, enrich indicators with immediate context through TI Lookup, and monitor emerging malicious infrastructure using Threat Intelligence Feeds. Together, these capabilities help reduce investigation uncertainty, accelerate triage, and limit unnecessary escalations across the SOC.
ANY.RUN is trusted by thousands of organizations worldwide and meets enterprise security and compliance expectations. It is SOC 2 Type II certified, demonstrating its commitment to protecting customer data and maintaining strong security controls.
Germany’s strong economy, high digitalization, and reliance on cloud services make its organizations high-value targets with scalable attack surfaces.
Finance, healthcare, IT, telecom, and manufacturing show consistently high risk due to data sensitivity, operational complexity, and business impact.
They now use reverse proxy tools and OAuth abuse to capture authenticated sessions, allowing attackers to bypass MFA and access accounts in real time.
Session hijacking allows attackers to steal active login sessions instead of credentials, granting immediate access without needing passwords again.
It provides context, detection speed, and visibility into attacker infrastructure, enabling faster decisions and proactive defense.
TI Lookup is used for investigating specific indicators in real time, while TI Feeds provide continuous streams of threat data for proactive blocking.
Yes, with the right combination of threat intelligence, sandboxing, and fast-response workflows, organizations can detect and contain threats early.
The post How Phishing Is Targeting Germany’s Economy: Active Threats from Finance to Manufacturing appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
Beyond monitoring and compliance, visibility acts as a powerful deterrent, shaping user behavior, improving collaboration, and enabling more accurate, data-driven security decisions.
The post The Hidden ROI of Visibility: Better Decisions, Better Behavior, Better Security appeared first on SecurityWeek.
SecurityWeek – Read More

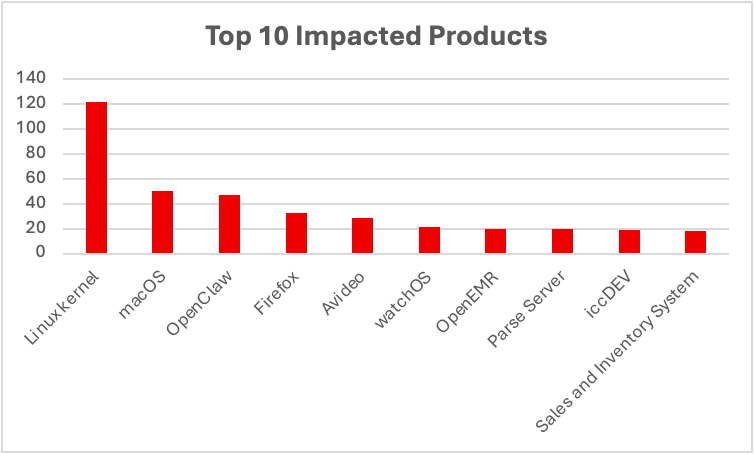
Cyble Research & Intelligence Labs (CRIL) weekly vulnerability report tracked 1,960 vulnerabilities last week, reflecting a continued surge in vulnerability disclosures across enterprise and cloud ecosystems.
Of these, 248 vulnerabilities have publicly available Proof-of-Concept (PoC) exploits, significantly increasing the likelihood of real-world attacks and accelerating exploitation timelines.
Additionally, at least 5 vulnerabilities were actively discussed across underground forums, indicating strong attacker interest and rapid weaponization.
A total of 214 vulnerabilitieswere rated critical under CVSS v3.1, while 57 were rated critical under CVSS v4.0.
Furthermore, CISA added 4 vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, confirming active exploitation in the wild.
On the industrial side, CISA issued 7 ICS advisories covering 10 vulnerabilities, impacting vendors such as Schneider Electric, WAGO, and PTC.
CVE-2026-32917 — OpenClaw (Critical)
CVE-2026-32917 is a critical remote command injection vulnerability affecting OpenClaw, an AI agent framework.
The flaw occurs in the iMessage attachment staging workflow, allowing attackers to inject commands into remote systems. Successful exploitation enables arbitrary command execution, potentially leading to full system compromise.
CVE-2026-4747 — FreeBSD RPCSEC_GSS (Critical)
CVE-2026-4747 is a critical stack-based buffer overflow vulnerability in FreeBSD caused by improper bounds checking in packet handling.
Attackers can send specially crafted requests to trigger a stack overflow, resulting in remote code execution with kernel-level privileges, enabling full system takeover.
CVE-2026-31883 — FreeRDP (Critical)
CVE-2026-31883 is a heap-based buffer overflow vulnerability in FreeRDP’s audio decoding components.
A malicious RDP server or man-in-the-middle attacker can exploit this flaw to execute arbitrary code, potentially compromising remote desktop clients and enterprise environments.
CVE-2026-1207 — Django (High)
CVE-2026-1207 is a SQL injection vulnerability in Django applications using PostGIS RasterField lookups.
Insufficient input validation allows attackers to inject malicious SQL queries, leading to data exposure, modification, and potential lateral movement within backend systems.
CVE-2025-53521 — F5 BIG-IP APM (Critical)
CVE-2025-53521 is a critical vulnerability in F5 BIG-IP Access Policy Manager, initially classified as a DoS flaw but later reclassified as unauthenticated remote code execution following active exploitation.
This vulnerability allows attackers to gain full control of access management systems, posing significant risks to enterprise networks.
CISA continued expanding its KEV catalog, reflecting active exploitation trends.
Notable addition:
CVE-2025-53521 — F5 BIG-IP APM
Initially considered a denial-of-service flaw, it was reclassified as a remote code execution vulnerability after evidence of active exploitation emerged.
This shows how vulnerabilities can evolve in severity over time, reinforcing the need for continuous reassessment and monitoring.
CISA issued 7 ICS advisories covering 10 vulnerabilities, with several rated critical.
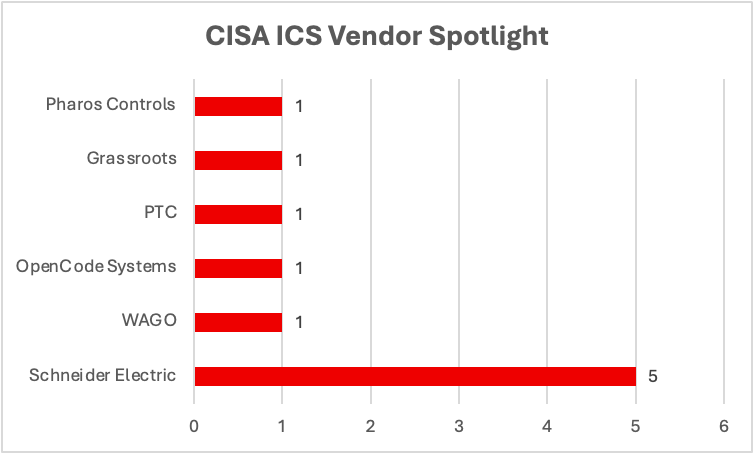
CVE-2026-2417 — Pharos Controls (Critical)
This vulnerability involves missing authentication for critical functions in Mosaic Show Controller firmware.
Attackers can exploit this flaw to gain unauthorized control over industrial systems, potentially disrupting operations.
CVE-2025-49844 — Schneider Electric Plant iT/Brewmaxx (Critical)
A use-after-free vulnerability in Schneider Electric’s industrial automation platform can lead to memory corruption and system compromise.
The presence of multiple vulnerabilities in this platform reflects systemic risk across widely deployed industrial environments.
CVE-2026-3587 — WAGO Managed Switches (Critical)
This vulnerability exposes hidden functionality in industrial switches, potentially enabling attackers to bypass controls and gain unauthorized access.
CVE-2026-4681 — PTC Windchill PDMLink (Critical)
This vulnerability involves improper control of code generation and currently has no available patch, leaving organizations exposed.
Grassroots DICOM (High, Unpatched)
A memory management flaw in Grassroots DICOM impacts healthcare imaging systems, with no vendor patch available, increasing risk to medical infrastructure.
Analysis shows that:
Commercial Facilities appear in 70% of ICS vulnerabilities
Critical Manufacturing and Energy each account for 60%
Healthcare, communications, and transportation sectors also face exposure.
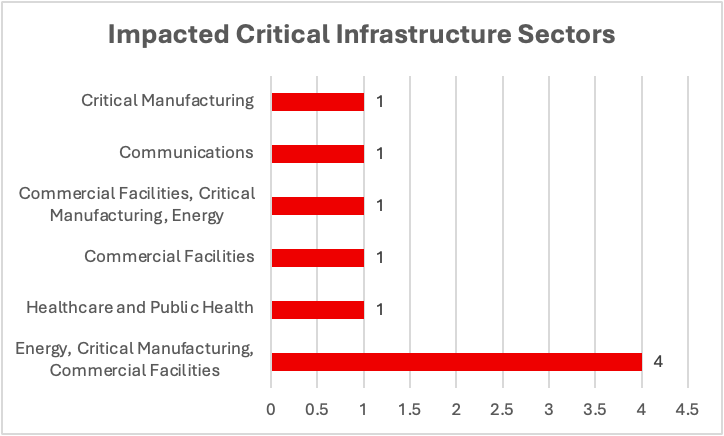
This distribution shows the strong cross-sector dependencies, where vulnerabilities in industrial platforms can cascade into multiple critical infrastructure domains.
This week’s findings highlight a convergence of:
With 248 publicly available PoCs, KEV additions confirming active exploitation, and unpatched ICS vulnerabilities, organizations face significant risk across both enterprise IT and operational technology environments.
Cyble’s attack surface management and vulnerability intelligence solutions enable organizations to identify exposed assets, prioritize remediation, and detect early indicators of compromise. By combining threat intelligence with proactive defense strategies, organizations can effectively mitigate evolving risks across enterprise and critical infrastructure environments
The post The Week in Vulnerabilities: OpenClaw, FreeBSD, F5 BIG-IP, and Critical ICS Bugs appeared first on Cyble.
Cyble – Read More

Every year, Cisco Talos publishes Year in Review, a comprehensive look at the previous year’s threat landscape. It’s drawn from an enormous volume of telemetry, such as endpoint detections, network traffic, email data, and boots-on-the-ground Cisco Talos Incident Response (Talos IR) engagements.
As incident responders, we see threats mid-detonation in the wreckage of an Active Directory environment, or in the lateral movement artifacts left behind by an affiliate who got in using nothing more than a valid account. The Year in Review distills those raw observations into structured intelligence, but that intelligence loop works both ways. The same report that our IR casework feeds into is the report that defenders should be feeding back into their own preparation cycles.
When Talos IR closes out an engagement with customers, the tactics, techniques, and procedures (TTPs) we observe through forensic work and analysis are catalogued, aggregated, and analyzed alongside broader Cisco telemetry. When we track the emergence of a new exploit like React2Shell redefining attacker speed, or when we see Qilin rise to dominate the ransomware landscape while legacy groups like others maintain rare, sustained momentum, those shifts in the adversary ecosystem become the intelligence that informs what we are on the lookout for during the next investigation. When we observe patterns of behavior, they may form trend lines that span multiple years and reveal how the landscape is evolving.
For defenders, this means the Year in Review is not a theoretical document. It is a distillation of what actually happened to organizations we respond to, investigated by the people who were in the room when things broke down. Here are some suggestions on how to operationalize these findings.
One of the most immediate and practical applications of Year in Review is raw material for tabletop exercises. The report hands you the adversary playbook. For example, the 2024 Year in Review highlighted that identity-based attacks accounted for 60% of all Talos IR cases, with Active Directory being the focal point in 44% of those incidents. Attackers were not breaking down doors with zero-days; rather, they were walking through the front door with stolen credentials, often bypassing multi-factor authentication (MFA) through push fatigue, misconfigured policies, or the simple fact that MFA was never fully enrolled in the first place for some accounts.
The 2025 Year in Review reinforces and deepens this picture. Attacks against MFA evolved significantly, with MFA spray attacks doubling down on identity and access management (IAM) infrastructure while expanding efforts against high-value privileged accounts. Device compromise attacks saw a significant rise in activity, showing that actors increasingly value reliable, repeatable access methods over one-off exploitation. These are adversary preferences that should directly shape your exercise scenariosand cybersecurity preparedness.
That is a ready-made tabletop scenario. Work with your team on this exact entry scenario and walk through it just as adversary would. An adversary authenticates to your VPN. MFA fires, but the user approves the push because they were already expecting a login prompt. The attacker is now inside your perimeter with legitimate access. What does your detection look like? How quickly do your analysts identify the anomaly? Who makes the call to force a password reset and revoke sessions? These are some good questions to cover in this scenario. The 2025 Year in Review found that actors tailor their MFA attack style depending on the sector, and that manufacturing was the most impacted sector for ransomware in 2025, underscoring persistent risk to repeatedly targeted industries. If you operate in manufacturing, health care, or another sector that has appeared consistently in ransomware targeting data, your tabletop should reflect the specific TTPs directed at your vertical — not a generic ransomware exercise. These are just some ideas to get started on scenarios.
Beyond tabletops, the Year in Review provides a prioritized list of what to test your detections against. Year after year, Talos IR engagements reveal a consistent core of adversary tradecraft that organizations are still struggling to detect. Tools like PowerShell and Mimikatz appear in a significant portion of engagements. Remote services such as RDP and SSH continue to be abused for lateral movement. Ransomware operators are increasingly disabling security solutions before deploying payloads, and in 2024, they succeeded in doing so at an alarming rate.
The 2025 Year in Review adds critical nuance to detection priorities through its vulnerability analysis. The top 10 most targeted vulnerabilities tell a story about what attackers reach for. React2Shell redefined attacker speed and targeting, compressing the window between disclosure and exploitation. ToolShell’s quick rise to the top five highlighted the sheer volume and impact of attacks exploiting development tool vulnerabilities.
For defenders, this is a checklist. Can your endpoint detection and response (EDR) detect and alert on the disabling of its own agent? Do you have detections for credential dumping from LSASS or web shell deployment? What about a scenario where direct exploitation takes place, but no web shell is deployed? Are you monitoring for anomalous Remote Desktop Protocol (RDP) sessions originating from unexpected source hosts? The Year in Review tells you what the adversary is actually doing, not what they might hypothetically do. That distinction is critical when you are prioritizing detection engineering across your organization.
Map these findings to the MITRE ATT&CK framework, which the Talos Quarterly IR Trend Reports and the Year in Review already reference, and you have a structured way to assess your coverage gaps. If valid account abuse is the dominant initial access technique and your detections are heavily weighted toward exploit-based intrusions, you have a mismatch between your defensive posture and the actual threat landscape.
The Year in Review also reveals patterns in where organizations struggle that go beyond technology. Across multiple years of IR engagements, common security weaknesses keep surfacing: incomplete asset inventories, inconsistent logging, missing or misconfigured MFA, inadequate network segmentation, and unpatched or end-of-life network devices that remain exposed. The 2024 report noted that some of the most targeted network vulnerabilities affected end-of-life devices with no available patches, yet those devices remained in production environments. The 2025 data reinforce this with even sharper clarity: Legacy systems remain highly vulnerable to attack, CVE age distribution data highlights systemic patch delays, and a small number of vulnerabilities in network infrastructure continue to drive outsized risk.
Two additional areas from the 2025 report deserve attention in your planning cycle. First, phishing continues to evolve. Phishing plays a key role in both initial access and post-compromise activity, with business email compromise-style and workflow-based lures remaining the primary theme. Travel and logistics lures surged, while political lures dropped off and IT-themed lures became more prominent. These shifts matter for security awareness training; if your phishing simulations are still heavily weighted toward current-events lures, they may not reflect what your users are encountering.
Second, the AI threat landscape warrants monitoring. The 2025 observations include dedicated coverage of how AI is shaping the threat environment. While the full scope of AI-enabled threats is still emerging, defenders should consider how AI may be lowering the barrier for adversaries in areas like phishing content generation, vulnerability discovery, and social engineering at scale. Your IR plans should be tested, validated, and updated to handle the new security regime we find ourselves in.
Rather than treating the Year in Review as a one-time read, consider building a recurring preparation cycle around it. When the report drops, review the top-level findings with your security leadership and identify the three or four trends most relevant to your environment. In the quieter early months, run a tabletop exercise built around the most applicable scenario. Through the middle of the year, use Quarterly IR Trend Report data to adjust detection priorities and validate coverage. Before year-end, when threat activity tends to intensify, conduct a focused review of your IR plan.
Cisco Talos Blog – Read More
Reputable researcher Haifei Li has come across what appears to be a PDF designed to exploit an unpatched vulnerability.
The post Adobe Reader Zero-Day Exploited for Months: Researcher appeared first on SecurityWeek.
SecurityWeek – Read More
A hacker transferred more than 50 bitcoin from the Bitcoin ATM operator’s wallets after stealing credentials.
The post $3.6 Million Stolen in Bitcoin Depot Hack appeared first on SecurityWeek.
SecurityWeek – Read More
Putting your computer to sleep might not be the best way to preserve its battery. Here’s why.
Latest news – Read More
Hackers vowed to revive its efforts against America when the time was right — demonstrating how digital warfare has become ingrained in military conflict.
The post Shaky Ceasefire Unlikely to Stop Cyberattacks From Iran-Linked Hackers for Long appeared first on SecurityWeek.
SecurityWeek – Read More