Your Google Chrome browser just got a useful autopilot feature – here’s how it works
Google’s new Auto Browse feature aims to handle your digital chores by taking actions on your behalf.
Latest news – Read More
Google’s new Auto Browse feature aims to handle your digital chores by taking actions on your behalf.
Latest news – Read More
The DeWalt 60V Max snow blower is tough enough to handle everything from fresh powder to ice. Here’s how it weathered the most recent storm.
Latest news – Read More
Police raids led to the arrests of three Hungarians and one Romanian suspected of swatting and doxxing incidents, authorities said.
The Record from Recorded Future News – Read More
Malicious attacks are increasing in frequency, sophistication and damage. Defenders need to find and harden system weaknesses before attackers can attack them.
The post Cyber Insights 2026: Offensive Security; Where It is and Where Its Going appeared first on SecurityWeek.
SecurityWeek – Read More
TechCrunch Founder Summit 2026 unites 1,100 founders and investors in Boston on June 23 for a day focused on real-world scaling insights and networking that pushes the needle. Save up to $300 on your ticket.
Security News | TechCrunch – Read More
The fastest way to squander the promise of AI is to mistake automation for assurance, and novelty for resilience.
The post Why We Can’t Let AI Take the Wheel of Cyber Defense appeared first on SecurityWeek.
SecurityWeek – Read More
Most ransomware attacks are opportunistic, not targeted at a specific sector or region
Categories: Threat Research
Tags: Ransomware, cybercrime, state-sponsored ransomware, victimization
Sophos Blogs – Read More
Think you can trust every email that comes from a business partner?
Unfortunately, that’s no longer guaranteed; attackers now slip into legitimate threads and send messages that look fully authentic.
That’s exactly what happened in a new case uncovered by ANY.RUN researchers; a trust takeover inside a real executive discussion about a document awaiting final approval.
By detonating the suspicious message, the investigation exposed the full execution chain and linked it to a broader phishing campaign already active since 2025.
Let’s find out how this attack worked, and how your team can detect similar threats faster, safely, and without disrupting business processes.
TL;DR
This incident started as something that looked completely normal from the outside: a live email discussion about a document waiting for final approval. It didn’t contain any strange subject line or a cold intro. Just a reply that appeared to belong in the thread.
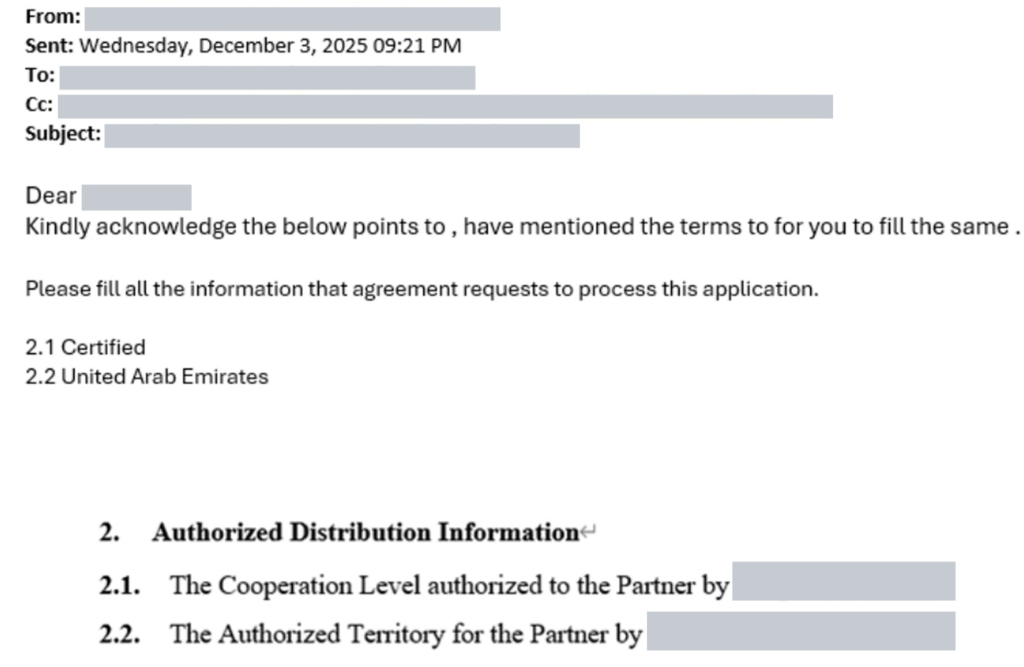
What made it dangerous was the access path. The attacker likely got into a supplier-side mailbox (a contractor’s sales manager account) and used that trusted identity to respond directly inside the active discussion among C-suite executives about a document pending final approval.
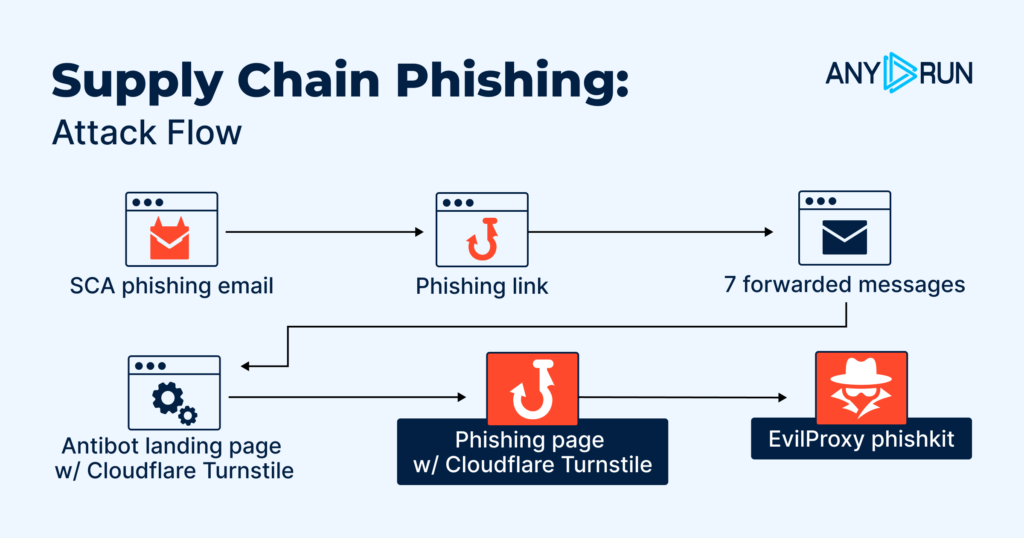
SCA phishing email → 7 forwarded messages → phishing link → anti-bot landing page (Cloudflare Turnstile) → phishing page (Cloudflare Turnstile) → EvilProxy
The campaign begins with a message designed to look like routine business communication from the supply chain side (contractor/vendor context). The goal at this stage is simple: land the first message in an inbox that’s already part of real business workflows, so later steps inherit trust.
The attacker didn’t need to write a convincing pitch. The thread did that work for them. As the email was forwarded across stakeholders, it picked up real context, real names, and the natural “we’re already discussing this” signal that makes people drop their guard. By the time it landed with executives, the link looked like just another step in a legitimate approval flow, not a new request that needed to be questioned.
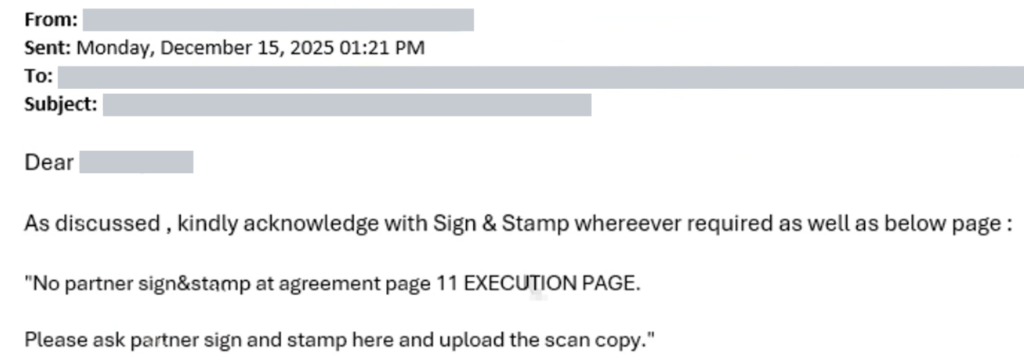
The link is placed where it looks expected: tied to “review,” “final approval,” or “document access.” It’s not framed as suspicious or urgent in a classic way.
After clicking, the victim doesn’t land on the phishing form immediately. First, they hit an intermediary page protected by Cloudflare Turnstile. This step helps the attackers in two ways:
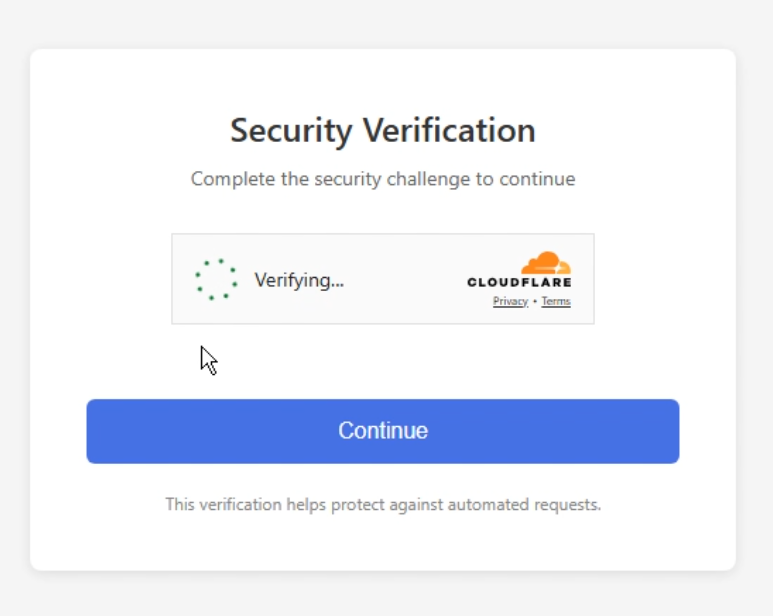
Once the user passes the first gate, they’re redirected to the phishing page; often with another Turnstile challenge. This extra layer reduces automated analysis success even more and increases the chance that the only “real” views of the credential page come from actual targets.
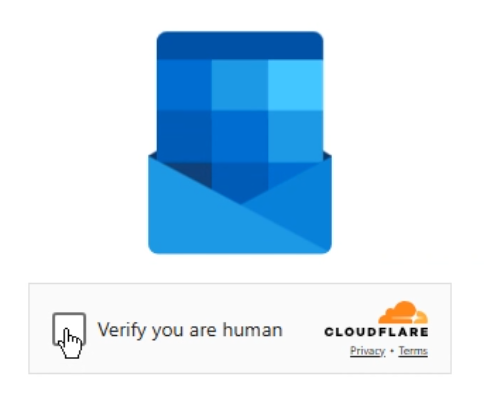
After passing the gates, the user is presented with a fake Microsoft authentication flow that’s built to steal credentials in a way that works even when users have strong security habits. The intent is to capture what the attacker needs to access the account and continue the intrusion, often by expanding access to other threads, mailboxes, and internal resources.
Supply chain phishing has changed. Modern campaigns run like full operations, built to blend into real workflows and scale quietly across vendors and partners. The biggest shift is simple: these attacks exploit business trust, not technical vulnerabilities.
What makes this wave different:
Thread-hijack phishing is built to pass “quick checks.” The only reliable way to beat it is to run a repeatable cycle that moves from early signals → proof → context → action → prevention. With ANY.RUN, teams can validate suspicious activity safely, uncover full campaigns, and strengthen detections in minutes, instead of hours.
Here’s how to do it step-by-step:
Once a thread-hijack email lands in someone’s inbox, the biggest mistake teams make is relying on quick checks. These attacks are built to look clean until the moment a real person interacts. That’s why the first step is always safe detonation.
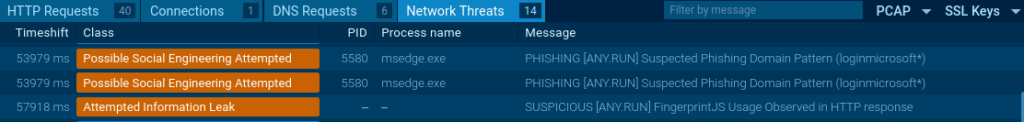
Running the link or file in ANY.RUN’s controlled environment exposes the real behavior of the attack, redirects, anti-bot gates, phishing pages, injected scripts, even the steps that remain hidden from static scans. In most cases, the full flow becomes visible in under 60 seconds.
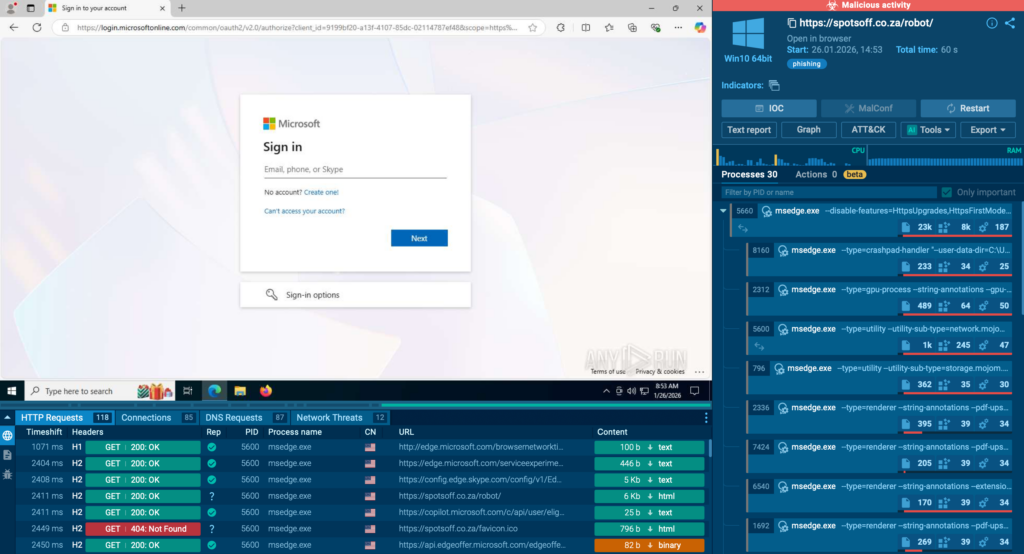
This is where teams get their first advantage:
Revealing intent early reduces workload for Tier-1 and prevents escalation loops that quietly drain SOC time and budget.
Modern supply chain phishing rarely comes as a one-off case. Behind a single malicious link usually hides an active campaign, a whole infrastructure layer, and hundreds of related samples circulating across industries.
The main advantage of ANY.RUN’s ecosystem is that a single sample is never isolated.
It lives inside a massive dataset enriched by 600,000+ analysts and telemetry from 15,000+ organizations.
This allows teams to immediately understand:
This transforms one incident into a campaign-level view; crucial for prioritization, threat hunting, and strategic response planning.
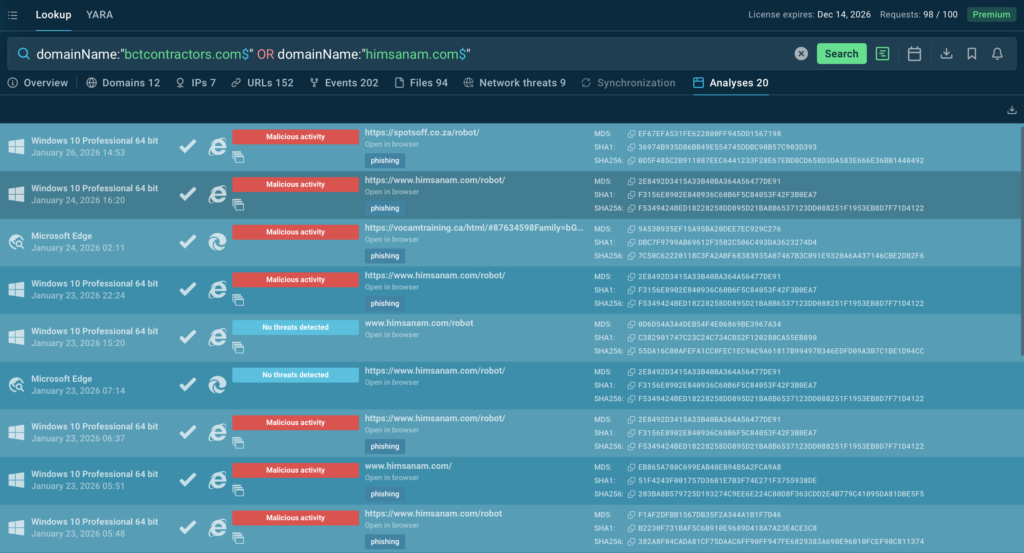
Use these TI Lookup search queries to find indicators and deeper campaign insights related to this phishing attack:
This level of visibility supports business needs too: clear audit trails, stronger reporting for leadership, and transparent decision-making during incidents.
Once you link the attack to a broader operation, the next step is staying ahead of it. Thread-hijack campaigns shift domains and redirect paths constantly, so teams need threat data that updates just as fast.
Fresh indicators extracted from ongoing detonation sessions by TI Feeds can flow directly into the tools your team already uses, SIEM, SOAR, email security, and detection pipelines.
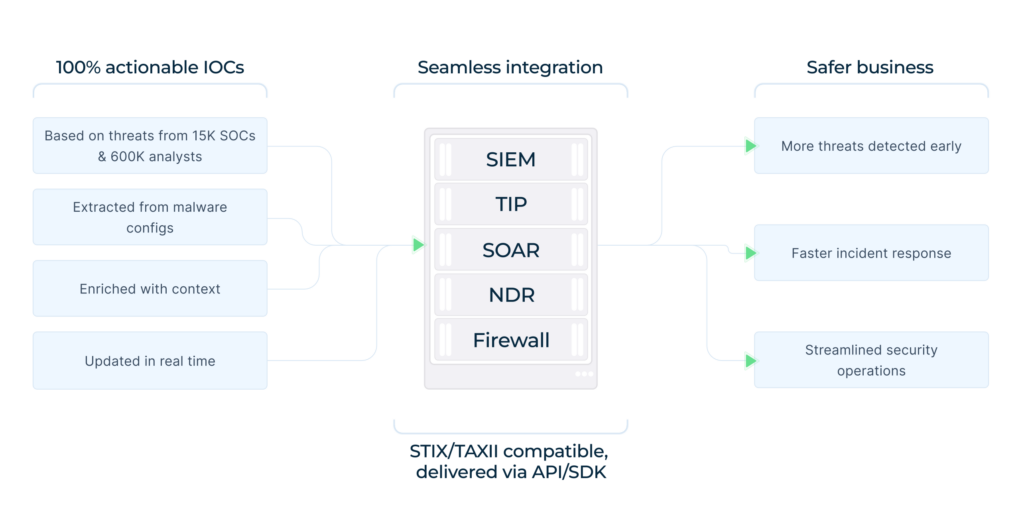
This gives defenders the ability to:
This ongoing flow transforms reactive detection into proactive monitoring, allowing teams to reduce the window between attack launch and discovery.
ANY.RUN is a part of modern SOC workflows, easily integrating into existing processes and strengthening the entire operational cycle across Tier 1, Tier 2, and Tier 3.
It supports every stage of analysis; from exposing real behavior during detonation to enriching investigations with broader threat context and delivering continuous intelligence that helps teams move faster and make confident decisions.
Today, more than 600,000 specialists and 15,000 organizations rely on ANY.RUN to accelerate triage, reduce unnecessary escalations, and stay ahead of evolving phishing and malware campaigns.
The post Attackers Are Taking Over Real Email Threads to Deliver Phishing: New Enterprise Risk appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
Learn what defines top-tier enterprise managed IT services, why they matter, and how Mindcore Technologies meets large-scale business demands.
Hackread – Cybersecurity News, Data Breaches, AI, and More – Read More
Sources say event triggered internal cybersecurity alerts and a DHS–level review into whether federal information had been improperly exposed.
The post Trump’s Acting Cyber Chief Allegedly Leaked Data to ChatGPT appeared first on TechRepublic.
Security Archives – TechRepublic – Read More