Google Looker Bugs Allow Cross-Tenant RCE, Data Exfil
Attackers could even have used one vulnerable Lookout user to gain access to other GCP tenants’ environments.
darkreading – Read More
Attackers could even have used one vulnerable Lookout user to gain access to other GCP tenants’ environments.
darkreading – Read More
Two IP addresses accounted for the majority of the 1.4 million exploitation attempts observed over the past week.
The post Cryptominers, Reverse Shells Dropped in Recent React2Shell Attacks appeared first on SecurityWeek.
SecurityWeek – Read More
Once deployed on corporate networks, AI agents can become every threat actor’s fantasy. Lesson one for cybersecurity pros: limit privileges.
Latest news – Read More
Microsoft has warned that information-stealing attacks are “rapidly expanding” beyond Windows to target Apple macOS environments by leveraging cross-platform languages like Python and abusing trusted platforms for distribution at scale.
The tech giant’s Defender Security Research Team said it observed macOS-targeted infostealer campaigns using social engineering techniques such as ClickFix since
The Hacker News – Read More
First month of the year, and we’re starting it off with updates that support faster decisions and more predictable SOC operations.
In January, we introduced a major workflow enhancement with the new ANY.RUN Sandbox integration with MISP, alongside expanded detection coverage across behavior signatures, YARA rules, and Suricata.
Let’s find out what this means for your team.
January brought another solid round of improvements focused on practical SOC workflows: faster alert validation, less manual back-and-forth, and earlier decisions that help stop incidents from growing into bigger problems.
The main highlight of the month was the release of the ANY.RUN Sandbox integration with MISP; an important step for teams that use MISP daily for threat intelligence and investigations.
Most SOC teams spend too much time validating alerts, moving samples between tools, and filling in missing context. When execution evidence is separated from threat intelligence platforms, investigations slow down, MTTR increases, and SLAs come under pressure.
With the ANY.RUN Sandbox integration for MISP, analysts can now bring real execution behavior directly into MISP, turning it from a passive intelligence repository into an active investigation layer.
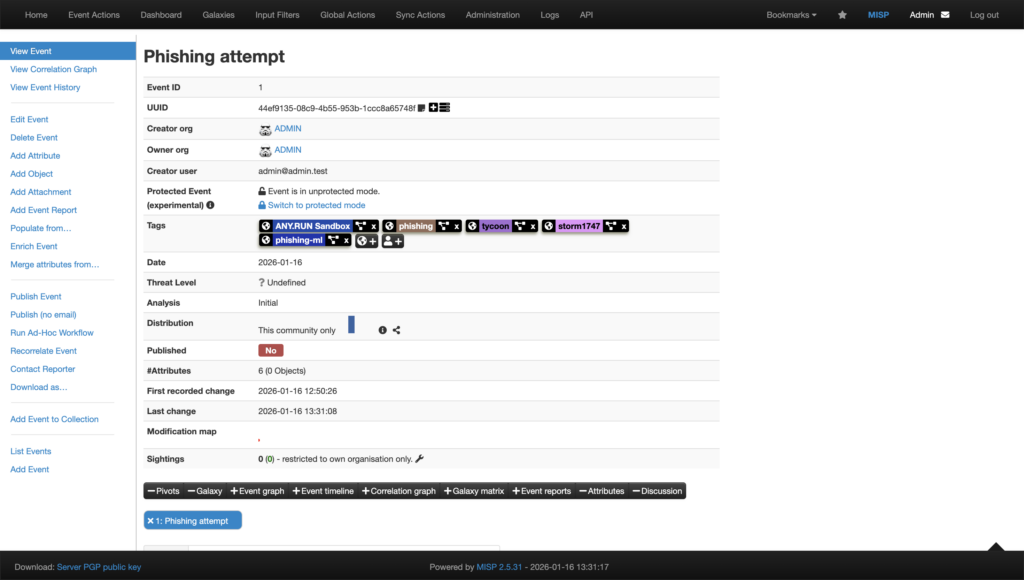
Using native MISP modules, suspicious files and URLs can be sent straight from MISP into the ANY.RUN Sandbox, without any context switching or manual handoffs.
You can easily integrate the modules, using the following links:
Analysis runs automatically using Automated Interactivity. This allows the sandbox to behave like a real user by clicking, opening files, and waiting when needed. This is critical for exposing modern threats that delay execution or hide behind user-driven actions.
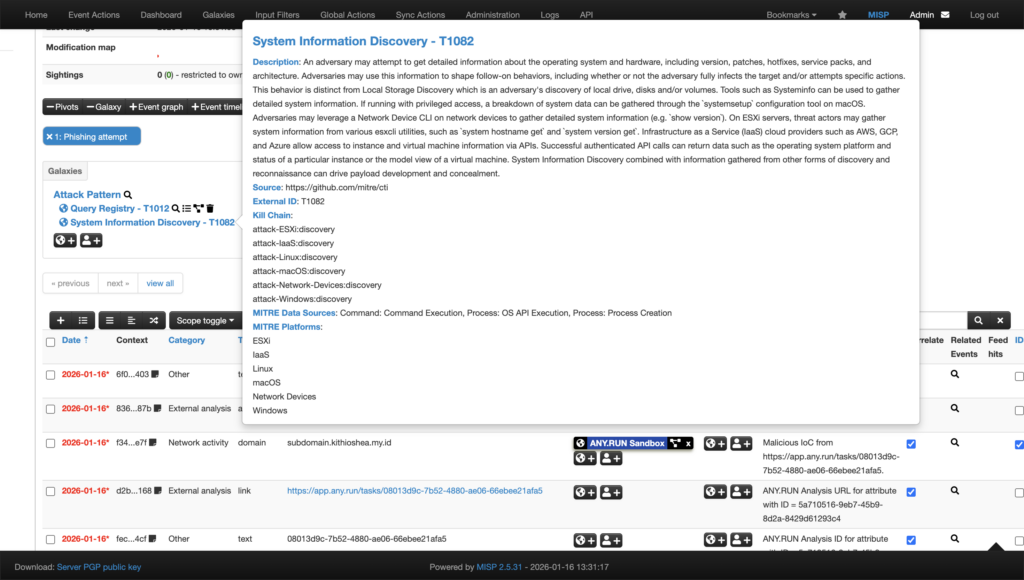
Once execution completes, results are automatically returned to MISP, including, verdict and risk assessment, extracted IOCs, adirect link to the interactive sandbox session, HTML analysis report, mapped MITRE ATT&CK techniques and tactics.
This allows analysts to validate alerts using real behavior, not assumptions, directly inside their existing workflow.
For organizations using MISP as part of daily operations, this integration delivers clear operational gains:

To support proactive coverage at scale, ANY.RUN Threat Intelligence Feeds deliver verified malicious network IOCs from real attacks across 15,000+ organizations, in STIX/TAXII format, ready for use in MISP, SIEM, or SOAR platforms.
Learn more about TI Feeds integration with MISP
In January, our team continued expanding the detection layer across sandbox execution, behavioral analytics, and network visibility, reinforcing ANY.RUN as a unified operational solution for detection, validation, and response.
This month’s updates include:
Together, these updates help security teams move faster from alert to decision, without switching tools or waiting for late-stage indicators.
January’s behavior signature updates focus on early-stage execution signals and hands-on attacker activity, helping teams identify malicious intent before payloads fully deploy or damage occurs.
The new detections expand coverage across ransomware families, loaders, stealers, and post-exploitation techniques, with particular attention to abuse of native Windows tooling and suspicious command-line behavior often seen in real-world intrusions.
This month, our team added signatures that detect:
Malware and loader execution patterns, such as
Suspicious use of built-in Windows tools, including
Persistence and system modification techniques, such as
Remote access and administrative tools observed in malicious contexts, including
Mutex- and pattern-based detections, including
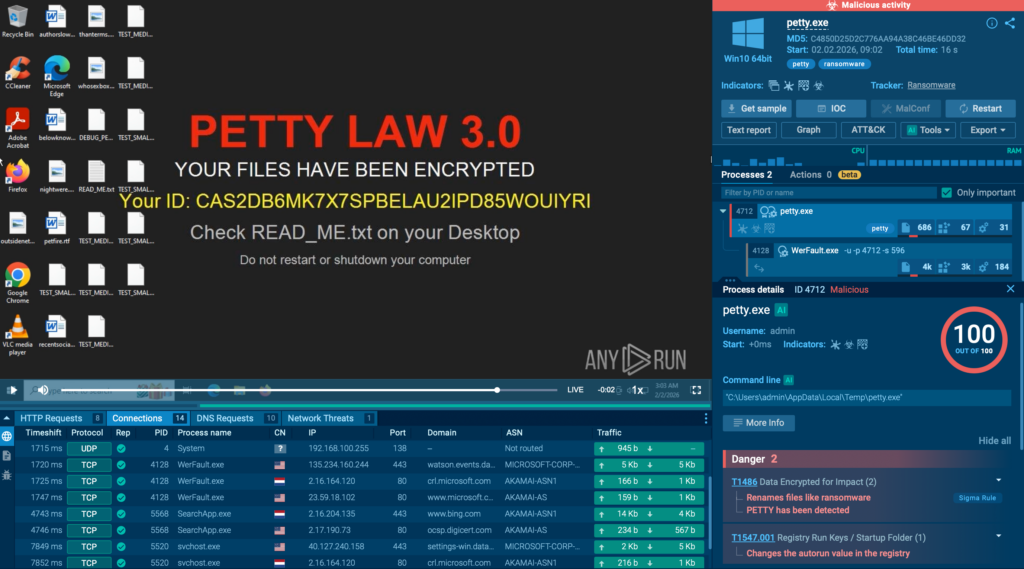
In January, 4 new YARA rules went live in production, expanding detection and hunting coverage inside ANY.RUN, especially useful when teams need quick classification and reliable pivots during triage.
Highlighted additions include:
These rules help security teams tag and cluster related samples faster, validate whether a file matches known patterns, and speed up investigation workflows without relying on a single indicator type.
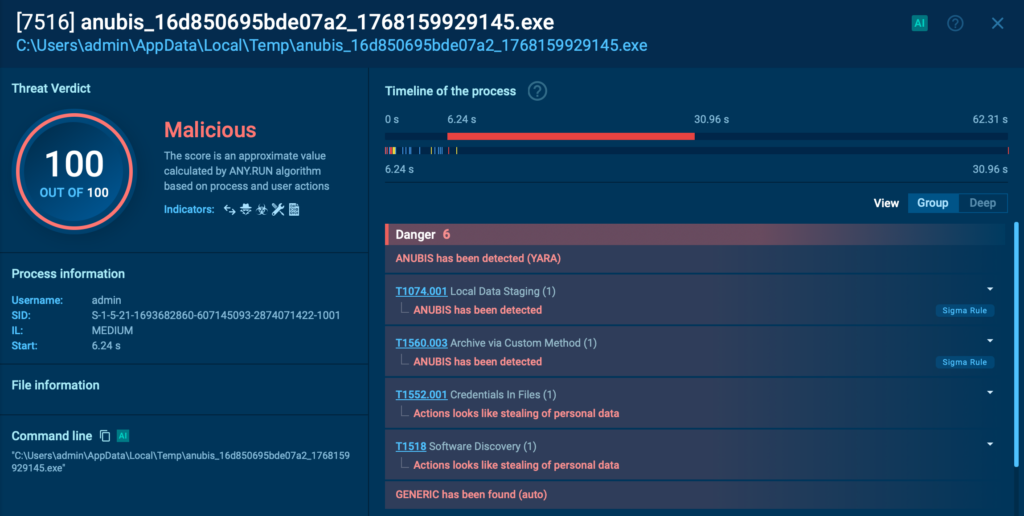
Our team deployed 1,897 new Suricata rules to expand network-level visibility into phishing infrastructure, backdoor communication, and stealer-related traffic patterns. These detections help teams identify malicious activity even when payloads are fileless, heavily obfuscated, or delivered through multi-stage web flows.
Highlighted additions include:
ANY.RUN is a core part of modern security operations, helping organizations make faster, more confident decisions across the full investigation lifecycle, from early alert validation to deep analysis and continuous threat awareness.
By exposing real attacker behavior in real time, ANY.RUN adds the context that alerts often lack and keeps detections aligned with how threats actually operate in the wild. This allows SOC teams to reduce noise, shorten response times, and focus effort where it matters most.
Today, more than 600,000 security specialists and 15,000 organizations worldwide rely on ANY.RUN to accelerate triage, limit unnecessary escalations, and stay ahead of fast-moving phishing and malware campaigns
Integrate ANY.RUN’s solution for Tier 1/2/3 in your organization →
The post Release Notes: Workflow Improvements, MISP Integration & 2,000+ New Detections appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
A Chrome extension posing as an Amazon ad blocker was caught hijacking affiliate links in the background, redirecting commissions without user consent.
The post Chrome Add-On Caught Stealing Amazon Commissions appeared first on TechRepublic.
Security Archives – TechRepublic – Read More
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a critical security flaw impacting SolarWinds Web Help Desk (WHD) to its Known Exploited Vulnerabilities (KEV) catalog, flagging it as actively exploited in attacks.
The vulnerability, tracked as CVE-2025-40551 (CVSS score: 9.8), is a untrusted data deserialization vulnerability that could pave the way for remote
The Hacker News – Read More
The Eclipse Foundation, which maintains the Open VSX Registry, has announced plans to enforce security checks before Microsoft Visual Studio Code (VS Code) extensions are published to the open-source repository to combat supply chain threats.
The move marks a shift from a reactive to a proactive approach to ensure that malicious extensions don’t end up getting published on the Open VSX Registry.
The Hacker News – Read More
Samsung will sell you a 65-inch QN1EF Neo QLED TV and HW-S700D soundbar for under $1,200 now, just in time for the Super Bowl and the Winter Olympics.
Latest news – Read More
Your company culture is the intangible knowledge new employees will absorb over time. But AI agents need all of it, all at once. Here’s how to engineer the context.
Latest news – Read More