G2 Recognizes ANY.RUN Among the Top 50 Best Software Companies in the Region
G2, the world’s largest and most trusted software marketplace, has recognized ANY.RUN among the Best Software Companies.
The ranking is based on verified reviews from organizations actively using ANY.RUN’s solutions. It reflects the company’s strong international presence and measurable impact across global cybersecurity markets.
Thank You to Our Community
Recognition on G2’s Top 50 Best Software Companies list is a reflection of peer validation, powered by customer reviews and feedback. We are very grateful to all analysts, SOC teams, and experts whose insights and evaluations contributed to the ranking.
For ANY.RUN, entering the G2 ranking is a milestone, not a finish line. We will continue to invest in product innovation, community-driven improvements, and measurable outcomes for security operations worldwide.
Impact with ANY.RUN: Customer-Reported Outcomes

ANY.RUN delivers measurable operational value to security teams with demanding workloads and strict SLAs. Among results reported by our customers are 50%+ reduction in investigation & IOC extraction time and 30–55% fewer irrelevant escalations.
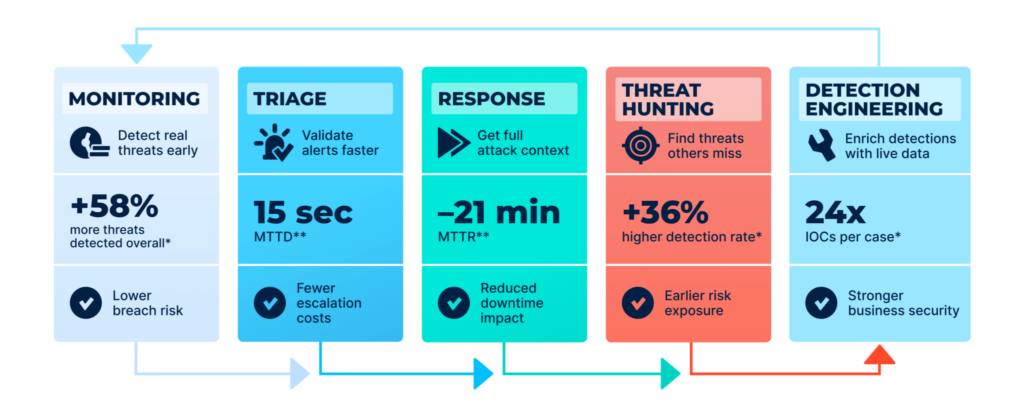
Beyond the metrics, ANY.RUN’s rising position in software rankings is by its ability to solve operational challenges across the SOC lifecycle:
- Unified SOC Workflow: ANY.RUN delivers solutions that support processes from monitoring to triage and incident response in a single ecosystem, enabling investigation without switching tools.
- Accelerated Decision-Making: Interactive malware analysis combined with contextual threat data provides immediate behavioral insight and evidence.
- Solved SOCs and MSSP Challenges: Standardized workflows and integrated intelligence enable efficient operations at scale, filling the gaps in work processes.
Trusted by the World’s Most Demanding Organizations
We support analysts in accelerating investigations, reducing risk, and improving operational outcomes across industries. Among 15,000 SOC teams applying our solutions, there are 3,102 IT & technology companies, 1,778 financial institutions, 1,059 government entities, and 919 healthcare providers.
ANY.RUN is used broadly by organizations with high security requirements, including the world’s largest enterprises:
- 74% of Fortune 100 companies rely on ANY.RUN for malware analysis and threat investigation workflows.
- 64% of Fortune 500 companies incorporate ANY.RUN into broader threat detection and response strategies.
“We just stopped losing time to uncertainty. Now we can confirm what’s happening faster and escalate only when it actually makes sense.”
Fortune 500 technology company on embedding ANY.RUN to their workflow.
About ANY.RUN
ANY.RUN has become an integral component of modern security operations, enabling teams to make faster, more confident decisions across Tier 1, Tier 2, and Tier 3. It integrates seamlessly into existing workflows and reinforces the full investigation lifecycle from initial validation to in-depth analysis and continuous threat monitoring.
By exposing real attacker behavior, enriching investigations with critical context, and ensuring detections reflect the evolving threat landscape, ANY.RUN helps SOC teams reduce alert fatigue, accelerate response times, and minimize operational impact.
Today, more than 600,000 security professionals and 15,000 organizations worldwide rely on ANY.RUN to streamline triage, reduce unnecessary escalations, and stay ahead of constantly shifting phishing and malware campaigns.
The post G2 Recognizes ANY.RUN Among the Top 50 Best Software Companies in the Region appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More