Release Notes: Expanded Threat Intelligence Access, AI Assisted Search 1,770 New Detections and More
April brought several updates across ANY.RUN’s Threat Intelligence and detection coverage.
The biggest change is expanded access to Threat Intelligence: Free plan users now get 20 premium requests in TI Lookup and YARA Search. This gives security teams a practical way to check suspicious indicators, explore related sandbox sessions, and validate malware or phishing activity using real attack data.
On the detection side, our team added 78 new behavior signatures, 1,657 new Suricata rules, and 35 new YARA rules. We also released new Threat Intelligence Reports covering malware, loaders, RATs, backdoors, and supply-chain threats observed in recent submissions.
Here’s a closer look at what’s new.
Product Updates
In April, ANY.RUN expanded access to Threat Intelligence capabilities, giving more teams a way to test threat context directly in their SOC workflows.
The key update: Free plan users now get 20 premium requests in TI Lookup and YARA Search. This gives security teams a practical way to check indicators, explore related sandbox sessions, and validate suspicious activity using real attack data from ANY.RUN’s community.
More Threat Context with 20 Premium TI Requests
Threat intelligence brings the most value when it helps teams make faster decisions during active investigations. Instead of stopping at one suspicious IP, domain, hash, or behavior, analysts can pivot to connected samples, infrastructure, artifacts, and attack context.
With 20 premium requests now included in the Free plan, SOC and MSSP teams can explore threat data across IOCs, IOBs, and IOAs linked to recent malware and phishing activity.
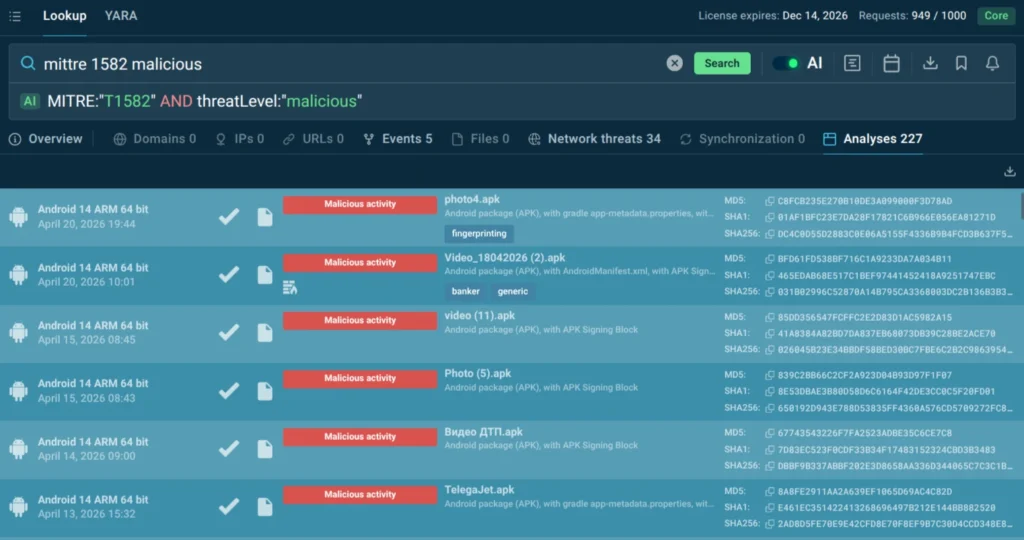
Teams can use this expanded access across key SOC workflows:
- Alert triage: Check suspicious indicators against real sandbox data and get more context before closing or escalating an alert.
- Incident response: Pivot from one indicator to related artifacts, infrastructure, and behavior to understand the wider attack chain.
- Threat hunting: Use TI Lookup and YARA Search to test hypotheses against real-world malware data.
- Detection work: Find patterns and artifacts that can support new or improved detection logic.
ANY.RUN also introduced AI-assisted search in TI Lookup, allowing users to describe what they need in natural language while the system helps translate the request into a structured query.
With threat intelligence available directly in the workflow, SOC and MSSP teams can move faster from suspicious signal to confident action:
- Faster alert validation: Teams can check suspicious indicators against real attack data and make decisions sooner.
- Lower escalation noise: More context helps reduce escalations driven by uncertainty.
- Shorter investigations: Analysts can move from one indicator to related samples, infrastructure, and behavior faster.
- Stronger threat hunting: Teams can test hypotheses against current malware and phishing data.
- Better detection quality: Real-world artifacts and behavior patterns can support more relevant detection logic.
- More measurable security value: Faster triage, better prioritization, and clearer evidence help teams focus capacity on confirmed risk.
Threat Coverage Updates
In April, our detection team continued to strengthen ANY.RUN’s threat coverage with new behavior signatures, Suricata rules, and YARA rules.
This month’s updates include:
- 78 new behavior signatures
- 1,657 new Suricata rules
- 35 new YARA rules
These additions help expand detection coverage across suspicious behavior, network activity, and file-based indicators.
New Behavior Signatures
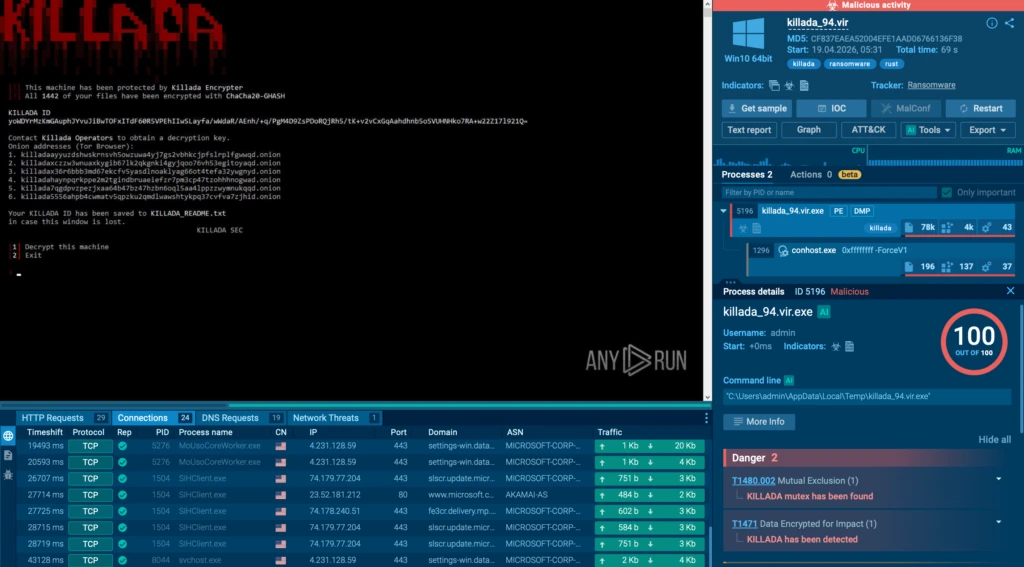
In April, we added 78 new behavior signatures covering malware-specific activity, mutex-based indicators, suspicious persistence behavior, and exploitation-related activity.
The new signatures focus on observable actions and artifacts that appear during detonation, helping teams move beyond file reputation and confirm what a sample actually does in the sandbox.
Highlighted detections include:
New Suricata Rules
In April, we also added 1,657 new Suricata rules to improve visibility into malicious network activity, including payload retrieval, DLL downloads, and possible command-and-control checks.
- DonutLoader base64-exe payload retrieval via HTTP (sid: 85007037): Detects malware’s attempts to get executable payload from stager server via HTTP
- Winos/ValleyRAT DLL download via TCP (sid: 85007024): Identifies ValleyRAT related DLL-file downloads via non-standard port TCP connection
- Possible AsyncRAT-style TCP C2 connectivity check (sid: 85007061): Heuristic rule tracking AsyncRAT-like malware implementations, based on set of connections to specific ports on the same host, likely checkingconnectivity with C2.
With these additions, sandbox sessions can surface more network-level indicators tied to malware delivery and post-infection communication.
New YARA Rules
In April, ANY.RUN added 35 new YARA rules to expand static detection coverage for suspicious files and known threat artifacts.
This layer is especially useful when a sample contains recognizable strings, code patterns, or structural markers that can link it to a known detection before or alongside behavior-based analysis.
Highlighted YARA detections include:
Together, the new behavior signatures, Suricata rules, and YARA rules give security teams broader coverage across runtime behavior, network traffic, and file-level indicators.
Threat Intelligence Reports
In April, our team released new Threat Intelligence Reports covering recent malware activity, attacker tooling, and techniques observed across real-world submissions.
Available as part of ANY.RUN’s TI Lookup Premium plan, these reports give security teams a clearer view of how specific threats behave, what artifacts they leave behind, and which indicators can support faster investigation.
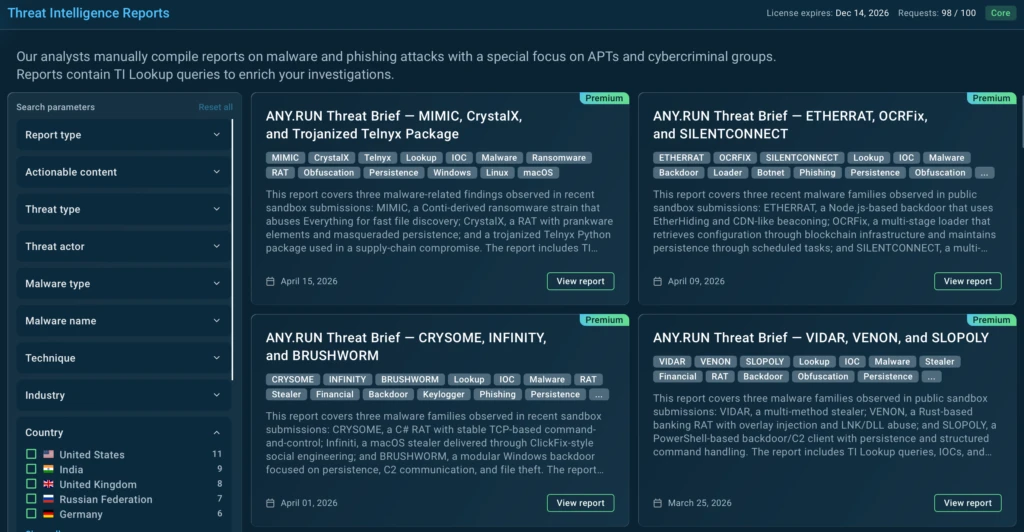
- MIMIC, CrystalX, and Trojanized Telnyx Package: This report covers MIMIC ransomware, CrystalX RAT, and a trojanized Telnyx Python SDK, focusing on encryption behavior, remote access and persistence, and malicious code execution through unauthorized PyPI releases.
- ETHERRAT, OCRFix, and SILENTCONNECT: This brief examines a Node.js backdoor, a loader/botnet component, and a Windows loader, focusing on blockchain-based C2/configuration retrieval, scheduled-task persistence, in-memory PowerShell execution, and ScreenConnect deployment.
- CRYSOME, INFINITY, and BRUSHWORM: This report examines a Windows RAT, a macOS stealer, and a Windows backdoor, focusing on TCP-based remote control, ClickFix-like delivery, credential theft, scheduled-task persistence, modular DLL download, and file theft.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams investigate threats faster and make confident decisions with real-world attack data.
Its solutions, including Interactive Sandbox and Threat Intelligence, give SOC and MSSP teams the context they need to analyze malware, phishing, infrastructure, behaviors, and indicators in one workflow.
Trusted by more than 15,000 organizations and 600,000 security professionals worldwide, including 74% of Fortune 100 companies, ANY.RUN helps teams improve triage speed, strengthen detection coverage, reduce investigation time, and respond to emerging threats with clearer evidence.
Integrate ANY.RUN into your SOC workflow →
The post Release Notes: Expanded Threat Intelligence Access, AI Assisted Search 1,770 New Detections and More appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More


