Chile’s Cybersecurity Framework Law: How SOCs Achieve Compliance and Response Readiness
In Chile, cybersecurity compliance is becoming an operational issue, not just a legal one. Under the new Cybersecurity Framework Law, organizations must show they have real capabilities for threat detection, incident analysis, and response. For many teams, that exposes a serious gap between regulatory expectations and day-to-day security operations.
Key Takeaways
- Chile’s Cybersecurity Framework Law raises the pressure on operational readiness: Security leaders need teams that can detect threats, investigate incidents, and support response decisions without delay.
- Slow investigation can quickly become a business risk: Delayed response weakens evidence, increases regulatory pressure, and makes post-incident review harder to manage.
- Faster triage and clearer evidence now matter more: Better visibility into suspicious activity helps reduce disruption, improve reporting quality, and support faster decisions under tight deadlines.
- For business leaders, this is about continuity as much as compliance: Teams must be able to contain incidents, document actions, and maintain control during regulatory scrutiny.
- ANY.RUN’s Enterprise solutions help reduce operational risk under compliance pressure: They support faster investigations, stronger evidence, and more controlled analysis workflows.
The Regulatory Shift
Chile has taken a decisive step toward strengthening its national cybersecurity posture with the approval of Law No. 21.663 – the Cybersecurity Framework Law. This legislation establishes mandatory cybersecurity obligations for organizations classified as:
- Operators of Vital Importance (OIV)
- Operators of Essential Services
- Critical public sector entities
Unlike traditional compliance frameworks that focus on policies and documentation, Chile’s approach is outcome-driven and risk-based. Organizations must demonstrate real operational capabilities– not just checkbox compliance. With enforcement and audits ramping up through 2025-2026, the compliance window is closing fast.
The scope is broad. An estimated 915 organizations across energy, telecommunications, banking and financial services, digital infrastructure, healthcare, and public institutions must now prove their cybersecurity readiness.
What the New Law Requires from Security Teams
Chile’s Cybersecurity Framework Law does not mandate specific tools, but it does set clear expectations for operational readiness. Regulated organizations are expected to have the following:
 Effective threat detection: Identify malicious activity before it causes damage
Effective threat detection: Identify malicious activity before it causes damage  Timely incident analysis and response: Understand what happened, how, and what to do
Timely incident analysis and response: Understand what happened, how, and what to do  Continuous risk management: Adapt defenses as the threat landscape evolves
Continuous risk management: Adapt defenses as the threat landscape evolves  Evidence-based reporting: Provide detailed, defensible reports to Chile’s national CSIRT and regulatory authorities
Evidence-based reporting: Provide detailed, defensible reports to Chile’s national CSIRT and regulatory authorities
Regulated entities must permanently apply technical and organizational measures to prevent, report, and resolve cybersecurity incidents in line with ANCI protocols and sector-specific standards. They must also report significant cyberattacks and incidents to the national CSIRT under a defined timeline.
For operators of vital importance, requirements are stricter. They must run a continuous information security management system, document security actions, and maintain certified cybersecurity and continuity plans, reviewed at least every two years.
They are also expected to conduct regular exercises, implement rapid containment measures, train staff, and appoint an independent cybersecurity delegate with direct access to top management and formal responsibility for coordination with ANCI.
The reporting timelines are especially important for CISOs, SOC leaders, and MSSPs serving regulated clients. The law requires an early warning within three hours after learning of a significant incident, an updated report within 72 hours, and a final report within 15 days.
If the affected entity is an OIV and the incident disrupts its essential service, the second report deadline tightens to 24 hours. OIVs must also communicate a formal action plan within seven days.
The key shift is simple: the law focuses less on documented intent and more on proven capability. It is not enough to say controls are in place. Organizations need to show they can investigate suspicious activity, confirm whether a threat is real, and support response decisions with evidence.
That changes the standard for security teams. Alerts alone are not enough. Teams need visibility, faster analysis, and a reliable investigation trail they can stand behind during reporting, audits, and post-incident review.
What Non-Compliance Can Cost
The legal exposure is serious. Minor infringements can be fined up to 5,000 UTM, serious infringements up to 10,000 UTM, and very serious infringements up to 20,000 UTM. For operators of vital importance, those maximums double to 10,000, 20,000, and 40,000 UTM respectively.
For leadership, the business risk goes beyond the fine itself. When teams cannot investigate suspicious activity quickly, explain what happened, or produce defensible incident evidence, the result can be longer disruption, slower communication with authorities, and more exposure during audits. That is why this law should not be treated as only a legal issue. It is also a detection, response, and operational-readiness issue.
The Compliance Challenge: Why This Is Hard
For SOCs and incident response teams across Chile, the new requirements create significant operational pressure:
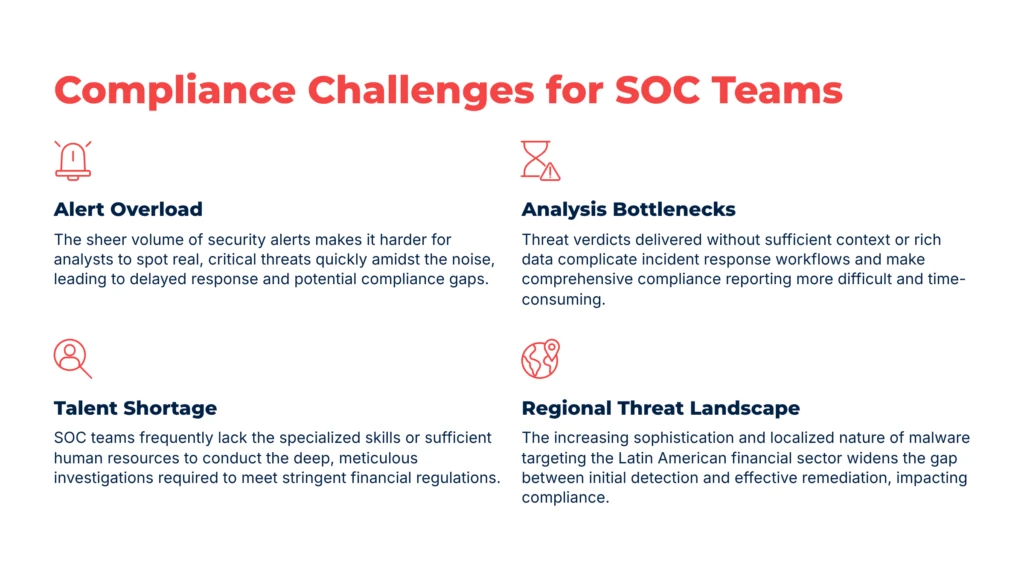
1. Alert Overload, Limited Analysis Capacity
Chilean organizations are facing the same challenge plaguing SOCs globally: too many alerts, not enough time to investigate them properly. SOC teams are drowning in noise from SIEM and EDR platforms, struggling to separate real threats from false positives.
2. Talent Shortage
The cybersecurity skills gap is acute in Latin America. According to industry data, LATAM experiences approximately 2,716 cyberattacks per organization per week, significantly above the global average. Yet there aren’t enough trained analysts to keep pace with investigation demands.
3. Malware Analysis Bottlenecks
Many sandbox solutions provide a verdict, but limited visibility into how the threat behaves or why it matters. When regulators ask for detailed incident reports, security teams need more than a malicious or benign label. They need evidence, context, and a clearer view of the attack chain.
4. Rising Threat Sophistication
Attackers targeting Latin America, particularly Chile’s banking and financial sectors, are deploying region-specific malware families like Mekotio, Grandoreiro, and Casbaneiro. These threats use novel evasion techniques specifically designed to bypass legacy detection systems.
Close the Security Gap with Better Threat Visibility, Analysis, and Response
Under Chile’s new framework, security gaps are no longer just technical weaknesses. They can become compliance failures, reporting delays, and broader business risks. ANY.RUN helps organizations close those gaps with stronger threat visibility, faster analysis, and more defensible response workflows.
1. Threat Intelligence for Better Visibility and Prioritization
One of the hardest parts of compliance is knowing which threats deserve immediate attention. Security teams already deal with large volumes of alerts, but the new law raises the need for monitoring that is not only active, but relevant to actual business risk.
ANY.RUN’s Threat Intelligence Lookup helps teams focus on threats that matter most to their environment. Rather than treating threat intelligence as just another dataset, it works as an operational layer that connects threat context with prioritization and action across the SOC lifecycle. Instead of relying only on generic indicators, organizations can investigate threats through industry- and geo-specific context.
For example, a query such as submissionCountry:”CL” AND industry:”banking” can help teams understand what is actively targeting Chile’s financial sector. This gives analysts faster context for triage, supports continuous risk management, and helps organizations build monitoring around real threats rather than assumptions.
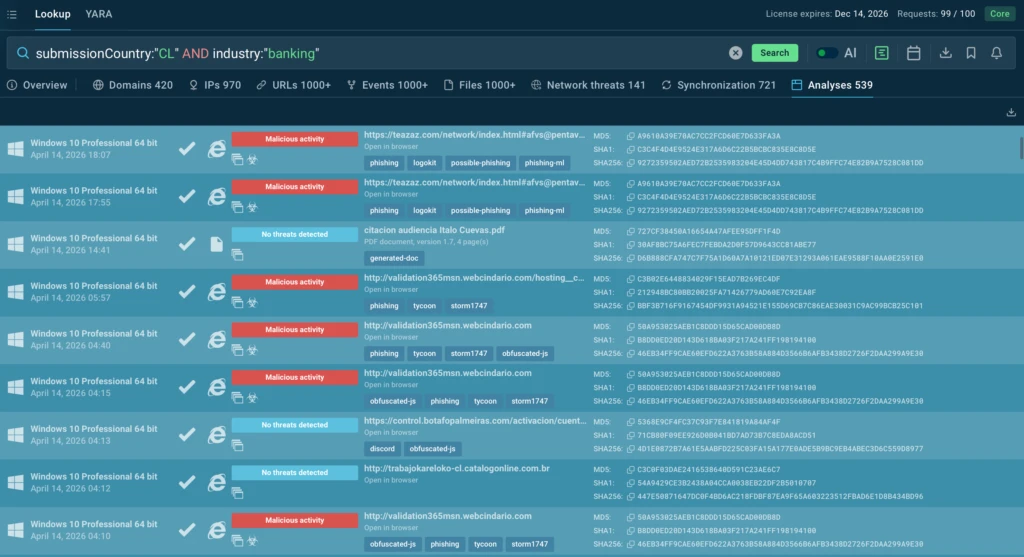
With this approach, organizations can:
- Focus security efforts on the threats most relevant to their sector
- Improve prioritization across monitoring and triage workflows
- Reduce investigation delays caused by low-context alerts
- Strengthen continuous risk management with more relevant threat visibility
- Build a stronger foundation for defensible response and reporting
2. Behavioral Analysis for Faster Investigation and Clearer Evidence
Threat visibility is only the first step. Once a suspicious file, URL, or email is detected, teams still need to understand what it actually does, how serious it is, and what actions should follow.
ANY.RUN’s Interactive Sandbox helps security teams investigate threats through real behavioral analysis. Instead of receiving only a verdict, analysts can observe malicious activity as it unfolds, understand the attack chain, extract indicators, and see the broader context of the incident. This makes it easier to validate threats faster, support containment decisions, and produce clearer evidence for reporting, audits, and post-incident review.
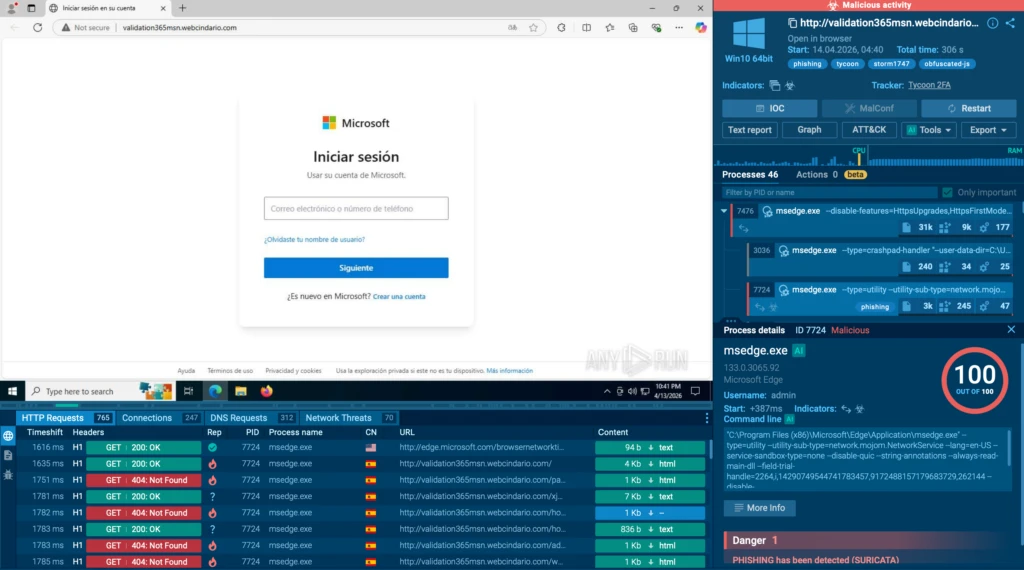
In practice, this allows organizations to:
- Understand how a threat behaves, not just whether it is malicious
- Confirm impact faster and make response decisions with more confidence
- Extract IOCs and other evidence for reporting and follow-up investigation
- Support containment with clearer visibility into attacker activity
- Build a more defensible investigation trail for audits and incident review
3. Integrations and Threat Feeds for Faster Detection and Response
Meeting regulatory expectations also depends on how quickly security teams can move from detection to action. When threat data stays locked in separate tools or requires manual handling, triage slows down, response becomes less consistent, and reporting gets harder under tight deadlines.
ANY.RUN helps reduce that friction by connecting threat intelligence and sandbox analysis directly to existing security workflows through ready-made connectors, STIX/TAXII, and API/SDK options. This allows teams to move investigation data into SIEM, SOAR, EDR, and TIP environments faster, so enrichment, correlation, and response can happen with less manual effort.
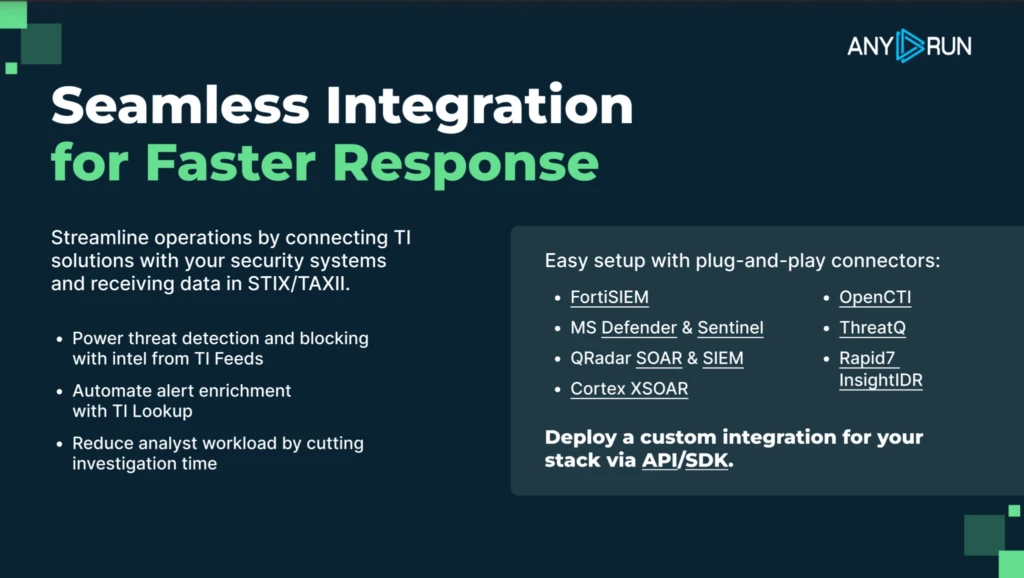
Threat Intelligence Feeds continuously deliver high-confidence malicious indicators sourced from live attack investigations across 15,000 organizations and 600,000 analysts, helping teams work with fresh threat data instead of static lists.
This gives organizations the ability to:
- Push fresh threat data directly into existing detection and response tools
- Reduce manual workload in enrichment and triage workflows
- Improve alert quality with validated, high-confidence indicators
- Speed up correlation and response across the SOC stack
- Build a more scalable and operationally consistent security model
Support Compliance Readiness with Privacy, Control, and Audit Confidence
Security teams also need confidence that sensitive analyses can be handled in a controlled environment that supports internal governance, confidentiality, and audit readiness. That is especially important for organizations working under stricter reporting obligations and higher regulatory scrutiny.
ANY.RUN supports that need with SOC 2 Type II attested security and private, access-controlled sandbox analysis designed for confidential investigations.
ANY.RUN’s private sandbox sessions remain confidential through strict access controls and encrypted data processing, helping organizations investigate threats without exposing case data to the public community. For leadership, this matters because improving detection and response is not enough on its own. The investigation environment also needs to meet enterprise expectations for security, privacy, and operational reliability.
This becomes especially valuable when incidents involve sensitive internal files, regulated environments, or investigations that may later be reviewed by auditors, executives, or external authorities. With stronger privacy controls around analysis data, organizations can reduce the risk of accidental exposure while giving security teams a safer way to investigate suspicious activity and preserve a defensible trail of evidence.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, helps security teams investigate threats faster and with greater clarity across modern enterprise environments.
It allows teams to safely execute suspicious files and URLs, observe real behavior in an Interactive Sandbox, enrich indicators with immediate context through TI Lookup, and monitor emerging malicious infrastructure using Threat Intelligence Feeds. Together, these capabilities help reduce investigation uncertainty, accelerate triage, and limit unnecessary escalations across the SOC.
Frequently Asked Questions
The law raises the standard from having policies on paper to proving operational readiness in practice. It sets minimum requirements for preventing, containing, resolving, and responding to cyber incidents, creates ANCI as the national authority, and gives regulators a clearer basis for oversight and sanctions. In practice, that means leadership teams need confidence that detection, investigation, reporting, and continuity measures will hold up under pressure.
The law applies to providers of essential services and to entities designated as Operators of Vital Importance, or OIVs. The covered sectors include areas such as energy, water, telecom, digital infrastructure, transport, banking and payments, postal services, and healthcare, while ANCI has the power to formally qualify OIVs.
At a minimum, regulated entities must permanently apply measures to prevent, report, and resolve incidents. For OIVs, the bar is higher: they must run a continuous information security management system, maintain records of security actions, implement and review continuity and cybersecurity plans, carry out ongoing reviews and exercises, train staff, and appoint a cybersecurity delegate who reports upward.
Because the reporting clock starts quickly. The law requires an early alert within 3 hours of learning about a significant incident, an update within 72 hours, and a final report within 15 days. If an OIV’s essential service is affected, the update deadline tightens to 24 hours, and OIVs must also adopt an action plan within 7 days. For leadership, this makes delayed investigation a business risk, not just a technical issue.
No. It does not prescribe named products. What it does require is that organizations can prevent, report, and resolve incidents, follow ANCI protocols and standards, and support continuity and incident handling with real operational capability. That is why the focus for leadership should be less on tool count and more on whether teams can investigate, decide, and report fast enough when it matters.
Because the law is built around response, reporting, and oversight. ANCI can require information needed to understand incidents, supervise compliance, and enforce sanctions, while the law also emphasizes continuity, risk management, and documented actions. For leadership teams, that makes clear evidence and a defensible investigation trail part of compliance readiness.
The post Chile’s Cybersecurity Framework Law: How SOCs Achieve Compliance and Response Readiness appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More