Sweet Security Introduces Patent-Pending LLM-Powered Detection Engine, Reducing Cloud Detection Noise to 0.04%
Tel Aviv, Israel, 15th January 2025, CyberNewsWire
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More
Tel Aviv, Israel, 15th January 2025, CyberNewsWire
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More
The proposed HIPAA Security Rule introduces mandatory measures to prevent malicious cyberattacks in health care.
Security | TechRepublic – Read More
As many as six security vulnerabilities have been disclosed in the popular Rsync file-synchronizing tool for Unix systems, some of which could be exploited to execute arbitrary code on a client.
“Attackers can take control of a malicious server and read/write arbitrary files of any connected client,” the CERT Coordination Center (CERT/CC) said in an advisory. “Sensitive data, such as SSH keys,
The Hacker News – Read More
Nvidia, Zoom, and Zyxel have released patches for multiple high-severity vulnerabilities across their products.
The post Nvidia, Zoom, Zyxel Patch High-Severity Vulnerabilities appeared first on SecurityWeek.
SecurityWeek – Read More

Fortinet has disclosed a critical authentication bypass vulnerability affecting FortiOS and FortiProxy systems, identified as CVE-2024-55591. With a CVSS score of 9.6, this vulnerability allows unauthenticated attackers to execute unauthorized code or commands, granting them “super-admin” privileges.
The exploitation of this vulnerability has already been observed “in the wild,” stressing the urgency for affected organizations to act immediately.
CVE-2024-55591 arises from a flaw in the Node.js websocket module, specifically within FortiOS and FortiProxy, where an alternate path or channel can bypass authentication mechanisms (CWE-288). This allows remote attackers to gain administrative access and compromise device configurations.
The vulnerability impacts specific versions of FortiOS and FortiProxy:
Unpatched systems are vulnerable to unauthorized access and subsequent exploitation.
Organizations are advised to monitor for the following IoCs to detect potential compromise:
Post-exploitation, attackers typically perform the following actions:
These actions allow lateral movement within the network, further compromising critical assets.
Upgrade to Secure Versions:
If patching is not immediately feasible, the following steps can temporarily mitigate risks:
Organizations leveraging Fortinet solutions must act promptly to secure their infrastructure against CVE-2024-55591exploitation, leveraging patches, access restrictions, and continuous monitoring to detect and mitigate potential attacks. Proactively implementing these measures not only reduces the attack surface but also strengthens overall network security against advanced threat actors.
https://www.fortiguard.com/psirt/FG-IR-24-535
https://docs.fortinet.com/upgrade-tool
The post Fortinet’s Authentication Bypass Zero-Day: Mitigation Strategies and IoCs for Enhanced Security appeared first on Cyble.
Blog – Cyble – Read More
Every ticking second is a chance for cyber threats to creep in.
For businesses, the stakes couldn’t be higher. One malicious email opened by an employee, and the malware can spread across office computers faster than mushrooms after rain. The consequences? Lost data, financial damage, and a hit to your company’s reputation.
To stop these threats before they cause harm, businesses need to stay prepared.
This is where YARA rules come in. They help cybersecurity teams to detect potential threats, simplify the process, and deliver clear, actionable insights to fight back against potential dangers.
In this article, we’ll dive into the crucial role of YARA rules, how they work, and how their integration into ANY.RUN’s sandbox helps teams to detect and handle cyber threats with confidence and efficiency.
Just as a lighthouse guides sailors safely past hidden rocks and treacherous waters, YARA rules guide cybersecurity professionals by identifying malicious patterns and offering a clear signal amidst the noise of potential threats.
YARA, funnily enough, stands for Yet Another Ridiculous Acronym. However, its actions are far more serious than its name suggests. YARA rules play a critical role in cybersecurity, helping professionals identify and classify malware by matching patterns in files, processes, or even memory.
At its core, YARA is a rule-based system that scans for specific characteristics, like unique strings or byte sequences, that are commonly found in malicious software. Think of it as a highly specialized filter that can sift through data to pinpoint potential threats with precision and speed.
YARA simplifies threat detection by identifying malicious patterns in files, processes, and memory with precision. It automates the scanning process, reducing the need for manual analysis and speeding up response times.
The beauty of YARA lies in its adaptability. Organizations can customize rules to target specific threats or emerging malware families, ensuring their defenses evolve alongside the threat landscape.
Combined with the real-time capabilities of ANY.RUN’s sandbox, this framework not only detects threats but also helps businesses understand their behavior, enabling them to mitigate risks before serious damage occurs.
Main benefits of YARA rules in organizations:

YARA operates as a powerful pattern-matching tool that scans files, processes, or memory dumps for specific characteristics. At its core, it relies on rules, predefined sets of instructions that describe what YARA should look for and under what conditions it should flag something as suspicious.
Here’s how the main process works:
YARA rules are made up of several essential components, each playing a critical role in detecting and classifying malware. To better understand how YARA works, let’s break down its key elements and examine an example.
The meta section provides descriptive information about the rule. This includes details like the author, creation date, a brief description of the rule’s purpose, and additional contextual data. While it doesn’t affect the execution of the rule, it helps organize and document it for future use.
This section contains the patterns the rule will search for in files or processes. These patterns can include:
The condition section defines the logic that determines when the rule will trigger. It specifies the criteria for matching patterns, such as requiring a minimum number of matches from the strings section or looking for specific file characteristics.
Below is an example of a YARA rule created to detect the Sakula malware family. It shows how each element works together to flag potential threats:
rule Sakula {
meta:
author = "ANY.RUN"
date = "2024-12-11"
description = "Detects Sakula samples"
family = "Sakula"
sample1= "https://app.susp.io/tasks/3c4f4b5e-7254-4fb4-a31e-4617b03110b1"
sample2= "https://app.susp.io/tasks/5722f2e3-64fc-49a4-beac-600c992ab765"
hash1 = "5de4e79682120f5b115eea30ce2da200df380f6256f03e38d3692a785f06fd64"
hash2 = "a9430482e5695c679f391429c7f7a6d773985f388057e856d50a54d1b19f463b"
strings:
$s1 = "%d_of_%d_for_%s_on_%s"
$s2 = "/c ping 127.0.0.1 & del "%s""
$s3 = "/c ping 127.0.0.1 & del /q "%s""
$s4 = "cmd.exe /c rundll32 "%s""
$s5 = "I'm a virus. My name is sola" ascii
$s6 = "Local\SM0:%d:%d:%hs" wide
$s7 = "Vxzruua/5.0" ascii
$s8 = "MicroPlayerUpdate.exe" ascii
$s9 = "CCPUpdate" ascii
$s10 = "Self Process Id:%d" ascii
$op1 = { 81 3E 78 03 00 00 75 57 8D 54 24 14 52 68 0C 05 41 00 68 01 00 00 80 FF 15 00 F0 40 00 85 C0 74 10 8B 44 24 14 68 2C 31 41 00 50 FF 15 10 F0 40 00 8B 4C 24 14 51 FF 15 24 F0 40 00 E8 0F 09 00 }
$op2 = { 50 E8 CD FC FF FF 83 C4 04 68 E8 03 00 00 FF D7 56 E8 54 12 00 00 E9 AE FE FF FF E8 13 F5 FF FF }
condition:
uint16(0) == 0x5a4d and
(4 of ($s*) or
any of ($op*))}Let’s highlight some of the key elements in this rule:
To better understand how this YARA rule detects Sakula malware, you can observe its behavior in real time using ANY.RUN’s Interactive Sandbox.
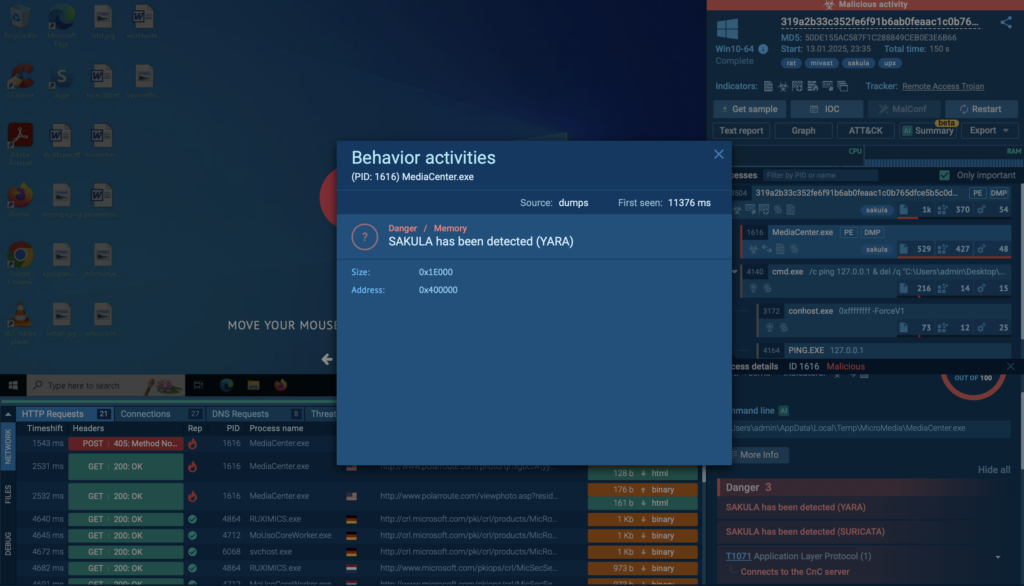
This analysis session showcases the malware’s activity and how the rule effectively identifies its patterns.
ANY.RUN’s interactive sandbox is a dynamic environment where cybersecurity teams can analyze files and observe their behavior in real time. Unlike traditional sandboxes, ANY.RUN lets users interact with the malware, providing deeper insights and faster results.
YARA is an inseparable part of this process. By integrating YARA rules into the sandbox, ANY.RUN identifies malicious patterns in files and processes with precision and speed.
ANY.RUN experts are constantly adding new YARA rules to the core of our malware sandbox, making the analysis process faster and saving security teams loads of time.
You can easily upload any suspicious file or link into the sandbox, and during the analysis, YARA rules will kick in. If there’s malware hiding in your file or link, the sandbox will spot it for you.
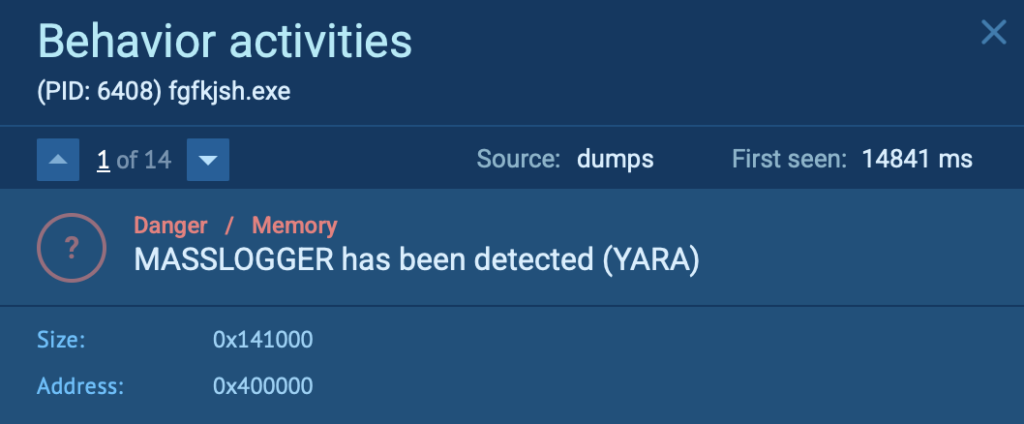
For example, after analyzing the following sample in the ANY.RUN sandbox, the process fgfkjsh.exe was flagged as malicious with the “MassLogger” tag.
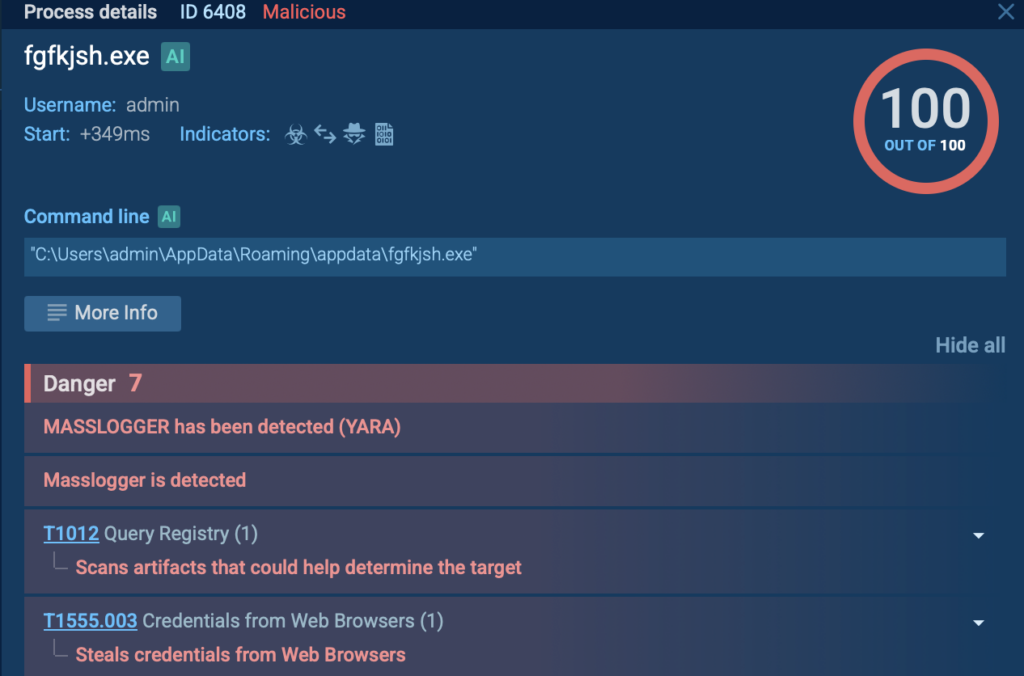
By clicking on the process located on the right side of the screen, the sandbox displays the message “MASSLOGGER has been detected (YARA).”
But note that YARA isn’t working alone: ANY.RUN’s sandbox also uses Suricata rules to make detections even sharper.
Discover more about Suricata rules and how they complement YARA in this detailed article: Detection with Suricata IDS
YARA rules aren’t just limited to the sandbox: they’re also available in ANY.RUN’s Threat Intelligence (TI) Lookup. This tool lets you search a massive database of malware artifacts using YARA rules, helping you find connections between known threats and your own files.
It’s perfect for teams handling big datasets or looking to spot trends in cyber threats. By combining YARA’s precision with the power of the sandbox and TI Lookup, ANY.RUN gives businesses a complete solution to fight back the evolving threats.
Check out this video on YARA Search in TI Lookup.
ANY.RUN helps more than 500,000 cybersecurity professionals worldwide. Our interactive sandbox simplifies malware analysis of threats that target both Windows and Linux systems. Our threat intelligence products, TI Lookup, YARA Search, and Feeds, help you find IOCs or files to learn more about the threats and respond to incidents faster.
Request free trial of ANY.RUN’s services →
The post YARA Rules: Cyber Threat Detection Tool for Modern Cybersecurity appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More

Lilith >_> of Cisco Talos discovered these vulnerabilities.
Forty-four vulnerabilities and sixty-three CVEs were discovered across ten .cgi and three .sh files, as well as the static login page, of the Wavlink AC3000 wireless router web application.
The Wavlink AC3000 wireless router is one of the most popular gigabit routers in the US, in part due to both its potential speed capabilities and low price point.
Talos is releasing these advisories in accordance with Cisco’s third-party vulnerability disclosure policy. Wavlink has declined to release a patch for these vulnerabilities.
For Snort coverage that can detect the exploitation of these vulnerabilities, download the latest rule sets from Snort.org, and our latest Vulnerability Advisories are always posted on Talos Intelligence’s website.
An attacker can send a specially crafted set of network packets over WAN to gain root access to the router via the wcrtrl service and static login credentials.
Static Login
An unauthenticated HTTP request can trigger the following types of vulnerabilities:
touchlist_sync.cgi
Login.cgi
internet.cgi
firewall.cgi
adm.cgi
wireless.cgi
usbip.cgi
qos.cgi
openvpn.cgi
nas.cgi
Attackers can send specially crafted HTTP requests. A man-in-the-middle attack can trigger the fw_check.sh and update_filter_url.sh vulnerabilities.
testsave.sh
fw_check.sh
update_filter_url.sh
Cisco Talos Blog – Read More
Fortinet patches critical vulnerabilities, including a zero-day that has been exploited in the wild since at least November 2024.
The post Fortinet Confirms New Zero-Day Exploitation appeared first on SecurityWeek.
SecurityWeek – Read More
Ivanti has released patches for multiple vulnerabilities in Endpoint Manager (EPM), including four critical-severity flaws.
The post Ivanti Patches Critical Vulnerabilities in Endpoint Manager appeared first on SecurityWeek.
SecurityWeek – Read More
CVE-2024-44243, a critical macOS vulnerability discovered recently by Microsoft, can allow attackers to bypass Apple’s System Integrity Protection…
Hackread – Latest Cybersecurity, Tech, Crypto & Hacking News – Read More