Imagine: you’re calmly working away on your computer, when suddenly a scary message appears on the screen: “Your computer is infected with viruses! Install an antivirus immediately!” or “Your data is at risk! Clean your system immediately!” Panic? That’s what the scammers are hoping for.
This post explains what scareware is and why this threat is dangerous. We also give tips for avoiding falling for scarewarers’ tricks, and protecting you and your family from such attacks.
What is scareware?
Scareware is a type of digital fraud that weaponizes users’ fears. The aim is to frighten the victim into visiting a malicious site and downloading something they shouldn’t. Scareware usually mimics antiviruses, system optimizers, registry cleaners, and the like. But other, more exotic types also exist.

The user is not so subtly informed that no fewer than five viruses have been found on their computer. However, the window header contains a small misprint: “Threaths detected” Source
To display their alarming messages, scammers tend to deploy browser pop-up windows and notifications, banner ads, and on occasion even good-old email.
Scareware creators use a variety of social engineering tricks to instill a sense of danger in the user. Often, threatening messages appear at the most unexpected moment — catching the victim off guard.
And scammers frequently hurry the victim into taking rash actions — not giving them time to think things over. Then, when the target has been properly prepared (that is, put into a state of panic), the attackers offer a simple solution to the problem: just install such-and-such software and all your troubles will be gone.
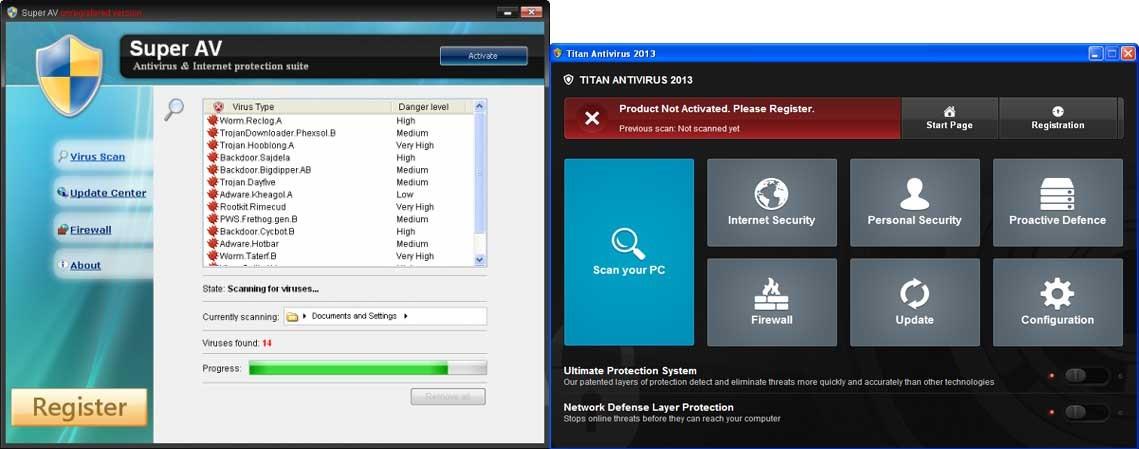
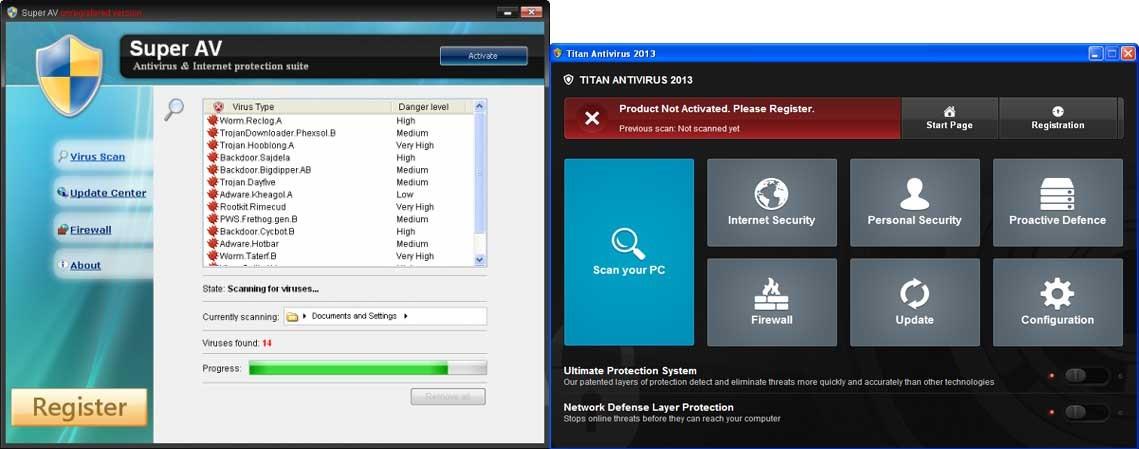
Fake antiviruses pretend to search for malware in the user’s system. Source
Upon receiving a scareware notification, in the best case scenario the victim will install a useless but harmless program on their device and pay a relatively small sum for the pleasure. But sometimes an attack can have more serious consequences. Under the guise of an “antivirus” or “system optimizer”, the victim may be fed proper malware that encrypts data or steals money from online bank accounts.
Sextortion scareware
Sometimes scammers employ a hybrid scheme: scareware combined with sextortion. It may go as follows: the user receives an intimidating email saying they’ve been caught in a compromising video.
To see for themselves, the victim is invited to visit a website where they can watch the footage. However, to view the video, they first need to install a special player. This, of course, is malware in disguise.
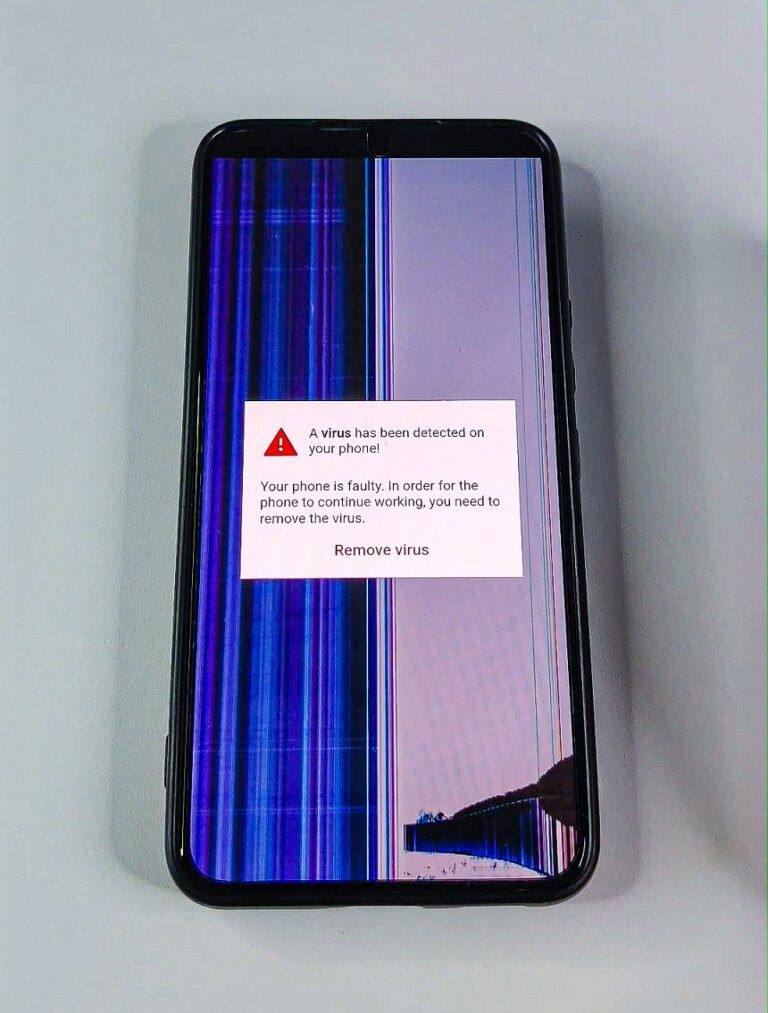
Faulty screen caused by a virus
In a new variant of the scareware scheme, the user is told that a virus has infected their smartphone. Nothing unusual so far — mobile versions of scareware have been around for ages. Here, however, the focus is artfully placed on what perhaps all smartphone owners fear the most: a faulty screen:
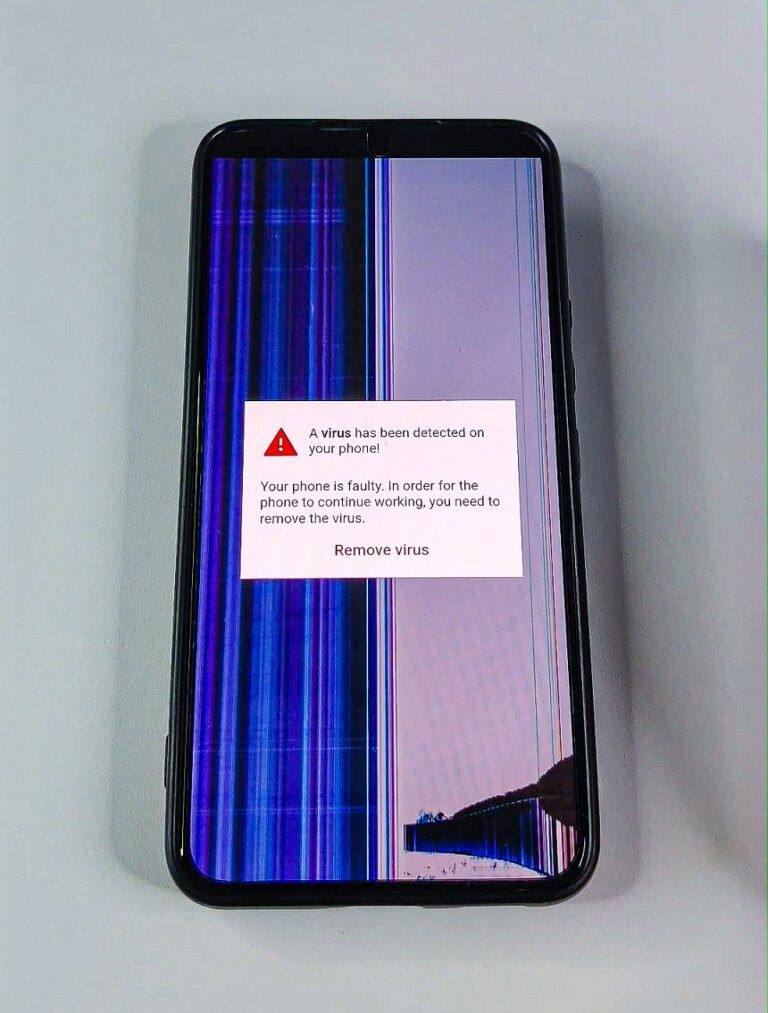
The scareware simulates screen damage caused by a virus that must be removed.Source
Curiously, the “faulty” display — which also blinks for added alarm — is capable of clearly showing the message about the supposed virus infection. How this window is able to float above a damaged screen is a mystery… To “fix” the screen, you just need to tap the button in the box and purchase the offered “antivirus”.
How to protect against scareware
Of course, the best defense against fake “protection” is the real thing. To defeat scareware, install a bona fide antivirus from a reputable developer, keep a close eye on its notifications, and always heed its recommendations.
Also bear in mind that it’s seniors who are most likely to fall victim. So it’s worth helping your older relatives get the right protection since it can be a challenge for them.
Kaspersky official blog –