You may finally be able to fix your embarrassing Gmail address – here’s how
Official documents indicate a long-awaited change might be coming.
Latest news – Read More
Official documents indicate a long-awaited change might be coming.
Latest news – Read More
ANY.RUN is wrapping up 2025 with updates that take pressure off your SOC and help your team work faster. You can now get AI‑generated Sigma rules, track threats by industry and region, and detect new campaigns with better speed and accuracy.
Let’s see what these improvements bring to your security stack.
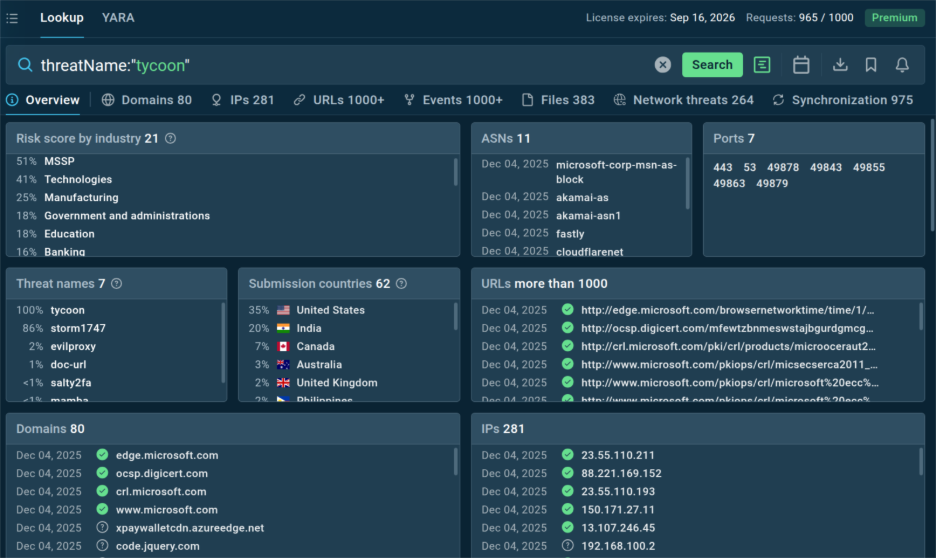
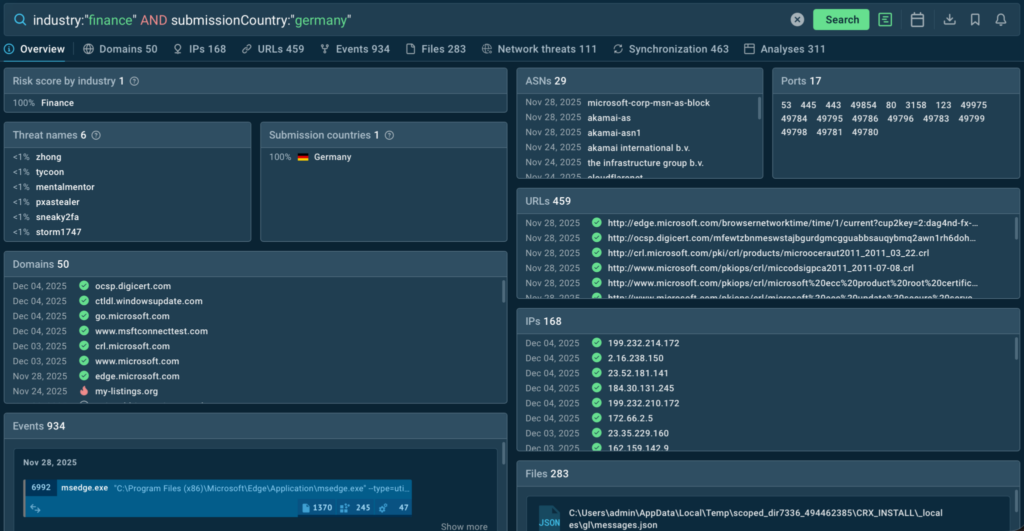
TI Lookup now gives every indicator extra context showing which industries and countries are linked to the threat of your industry and where similar activity is trending. It’s an easy way to see whether a threat actually affects your business or if it’s just background noise.
Built on live data from more than 15,000 organizations, this update helps your team tighten detection focus and reduce blind spots:
With TI Lookup, you spot threats earlier, respond faster, and keep your attention where it counts.
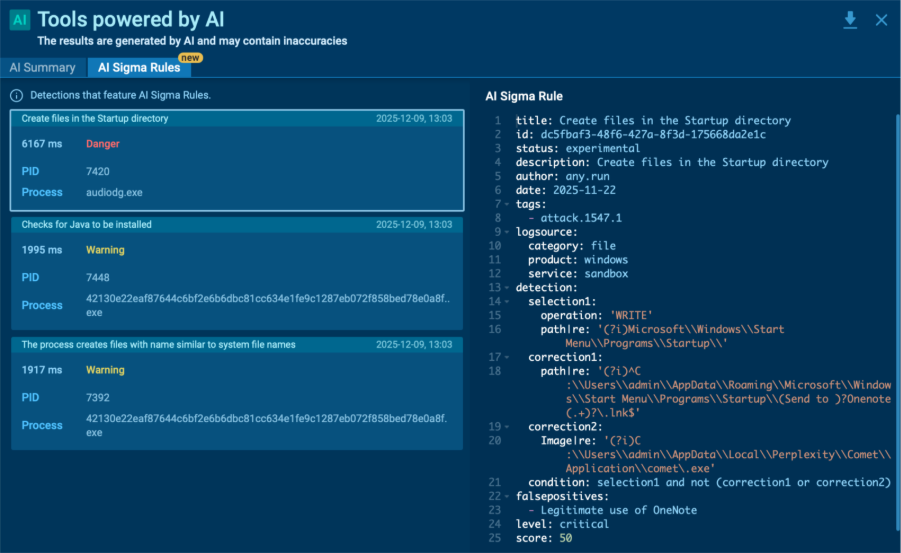
The new AI Sigma Rules feature in the Interactive Sandbox turns your confirmed detections into ready‑to‑use Sigma rules automatically. Instead of spending hours writing them by hand, you can now take the rule straight from the sandbox and add it to your SIEM or SOAR in seconds.
The rules are created from the same processes, files, and network events you see in the sandbox, so they stay closely tied to real attacker behavior. That means better accuracy and quicker response without extra effort.
Here’s what you gain:
In December, our detection team rolled out another wave of coverage improvements with:
These updates enhance phishing detection, expand coverage of stealers, loaders, and RATs, and clean up false positives across multi‑stage attacks.

Fresh signatures add visibility into persistence, lateral movement, and abuse of system tools seen across mixed environments.
Highlighted families include:
These detections help analysts catch miner and loader activity earlier and recognize evasion tricks like rundll32 abuse or PowerShell obfuscation.
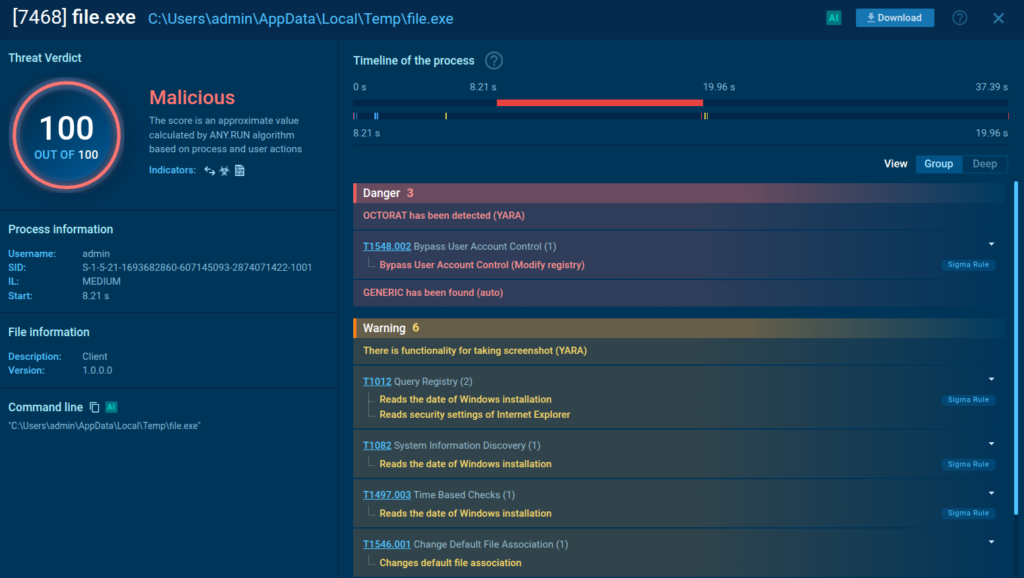
We added 13 YARA rules to improve detection across new malware strains and living‑off‑the‑land tools.
Highlighted families are STEAL1, SANTASTEALER, UNIXSTEALER, OCTORAT, DonutLoader.
These cover credential theft, modular loaders, and dual‑use administrative tools to ensure better coverage for both Windows and Linux‑based systems.
We’ve added 1,686 Suricata rules targeting phishing, botnet activity, and evasive network behaviors often missed by standard IDS.
Together, these bring better coverage of C2 traffic, phishing domains, and low‑signal campaign infrastructure.
Businesses that are constantly being bombarded by hundreds of hacker attacks daily can upgrade their proactive defense with ANY.RUN’s Threat Intelligence Feeds.

Powered by sandbox analyses of the latest malware & phishing samples across 15K SOCs, they deliver fresh, real-time malicious network IOCs to numerous companies around the globe. Enriched with detailed sandbox reports, TI Feeds not only help you catch emerging threats early but also provide your analysts with actionable intelligence for fast remediation, boosting your detection rate and driving down the MTTR.
In December we published new TI Reports summarizing late‑year activity:
Each brief distills TTPs, campaigns, and IOCs from live submissions to help SOC teams anticipate what’s next.
ANY.RUN powers SOCs at more than 15,000 organizations, giving them faster visibility into live threats through interactive sandboxing and cloud‑based intelligence.
Our Interactive Sandbox lets you analyze Windows, Linux, and Android samples in real time, watch the execution flow second‑by‑second, and pull IOCs instantly, no installs, no waiting. Combined with Threat Intelligence Lookup and Threat Intelligence Feeds, you get a single workflow built to speed up investigation, cut MTTD and MTTR, and keep your SOC focused on the right threats.
Start 2026 with faster detection, better threat intel, and less noise.
Request trial of ANY.RUN’s products for your SOC.
The post Release Notes: AI Sigma Rules, Live Threat Landscape & 1,700+ New Detections appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
The ‘download’ button on the official EmEditor website served a malicious installer.
The post Infostealer Malware Delivered in EmEditor Supply Chain Attack appeared first on SecurityWeek.
SecurityWeek – Read More
Hackers stole names, addresses, Social Security numbers, ID numbers, and medical and health insurance information from Aflac’s systems.
The post 22 Million Affected by Aflac Data Breach appeared first on SecurityWeek.
SecurityWeek – Read More
From university breaches to cyberattacks that shut down whole supply chains, these were the worst cybersecurity incidents of the year.
Security Latest – Read More
From Donald Trump to DOGE to Chinese hackers, this year the internet’s chaos caused outsized real-world harm.
Security Latest – Read More
Privacy may be dead, but civilians are turning conventional wisdom on its head by surveilling the cops as much as the cops surveil them.
Security Latest – Read More
Dubbed MongoBleed, the high-severity flaw allows unauthenticated, remote attackers to leak sensitive information from MongoDB servers.
The post Fresh MongoDB Vulnerability Exploited in Attacks appeared first on SecurityWeek.
SecurityWeek – Read More
Tech companies are increasingly warning their customers that they have been targeted by governments with advanced government spyware, such as NSO’s Pegasus or Paragon’s Graphite. What happens after receiving a threat notification?
Security News | TechCrunch – Read More
We’re glad to present our regular quarterly report highlighting the most prominent malicious trends of the last three months of 2025, as observed by ANY.RUN’s community.
Following the release of our annual report on key threats and milestones, this report offers a closer look at the threat landscape of the final chapter of 2025.
The Malware Trends report Q4 features top malware types, families, phishing kits, TTPs, APTs, and other notable insights.
You can turn to the previous Q3 report for reference.
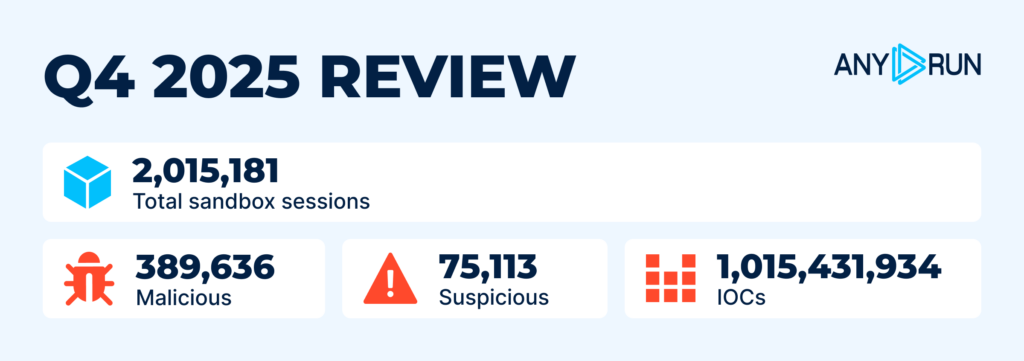
During the last quarter of 2025, overall threat investigation activity remained stable — no drastic growth in volume. The total number of sandbox analyses conducted in ANY.RUN’s Interactive Sandboxincreased slightly by 6%, surpassing 2 million since Q3.
Over one billion indicators were gathered by our community during analysis sessions. A total of 389,636 samples were labeled as malicious, and 75,113 as suspicious.
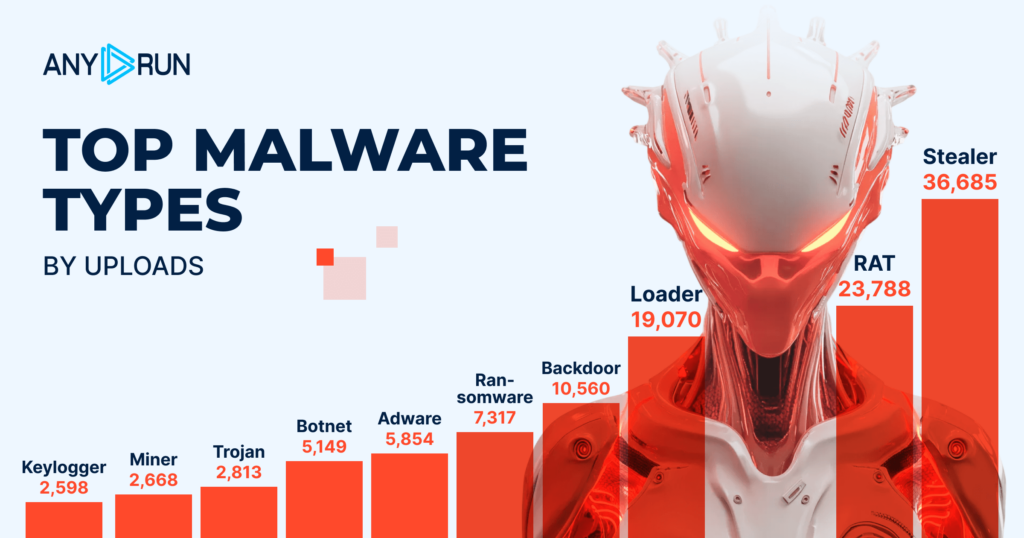
Although the list of top malware types looks similar to Q3 at first glance, several notable changes in activity levels should be pointed out:
Widespread families: Lumma, Stealc, Blank Grabber
Widespread families: XWorm, Quasar RAT, AsyncRAT
Widespread families: Smoke Loader, PureCrypter, HijackLoader
Backdoor‘s 68% activity growth reflects modular malware kits proliferating, enabling easier customization and evasion of traditional defenses.
Adware moved up two places with a 31% rise in activity, while ransomware detections decreased by the same percentage.
At the lower end of the list there are Botnet with 5K detections, Trojan with 2.8K, Miner with 2.6K, and Keylogger with 2.5K.
ANY.RUN’s Interactive Sandbox enables businesses and SOC teams to proactively identify cyber threats by analyzing files and URLs inside interactive Windows, Linux, Android VMs.
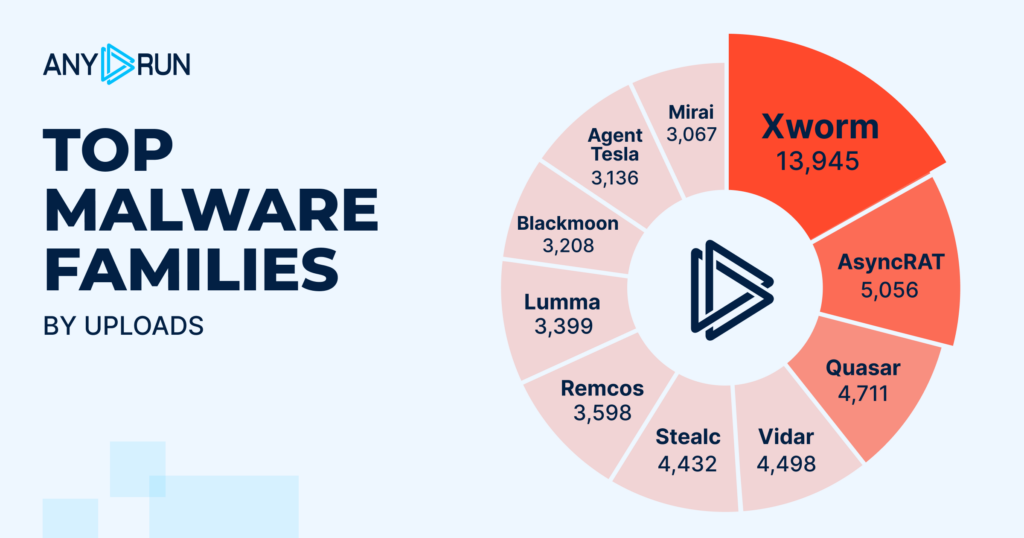
This section indicates a number of drastic changes in intensity and volume of certain threats. Key observations include:
XWorm, driven by its adaptability across industries like manufacturing and healthcare, showed a +174% surge.
XWorm IOCs from Threat Intelligence Lookup
Find more IOCs in TI Lookup with this query:
threatName:”xworm” AND domainName:””
AsyncRAT IOCs from Threat Intelligence Lookup
Find more IOCs in TI Lookup with this query:
threatName:”asyncrat” AND domainName:””
Lumma’s fall from first to eighth place with a -65% plunge highlights attacker shifts to newer, less-detected families, reducing reliance on saturated stealer platforms.
Lumma IOCs from Threat Intelligence Lookup
Find more IOCs in TI Lookup with this query:
threatName:”lumma” AND domainName:””
Vidar and Stealc with 4K+ detections each re-emerged in Q4, indicating a sudden end-of-year growth.
Another addition to the chart is Blackmoon with 3,208 detections. At the same time, AgentTesla and Remcos threats saw a reduction in detections and went from second and fourth places to tenth andseventh respectively.
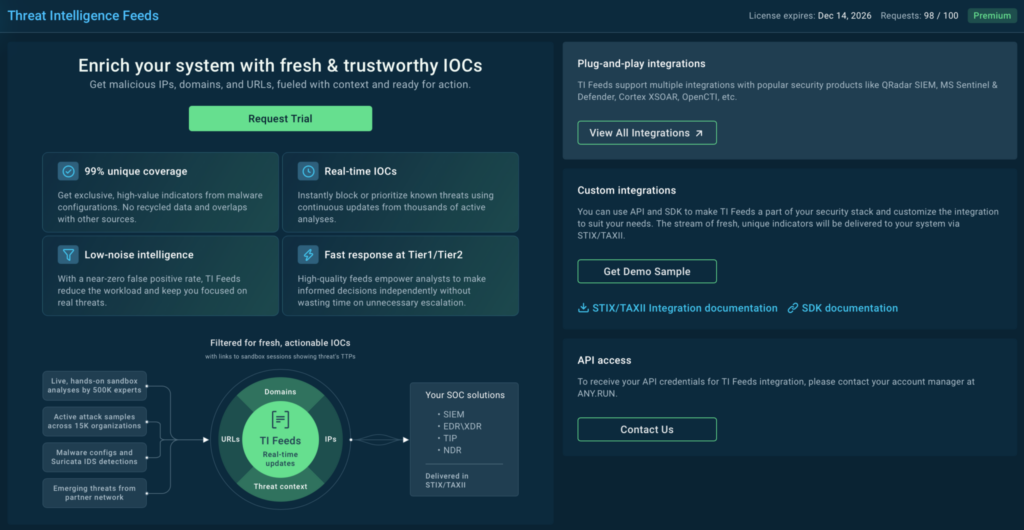
Gain a live view of the threat landscape with fresh, actionable IOCs delivered to you from investigations done across 15,000 companies.
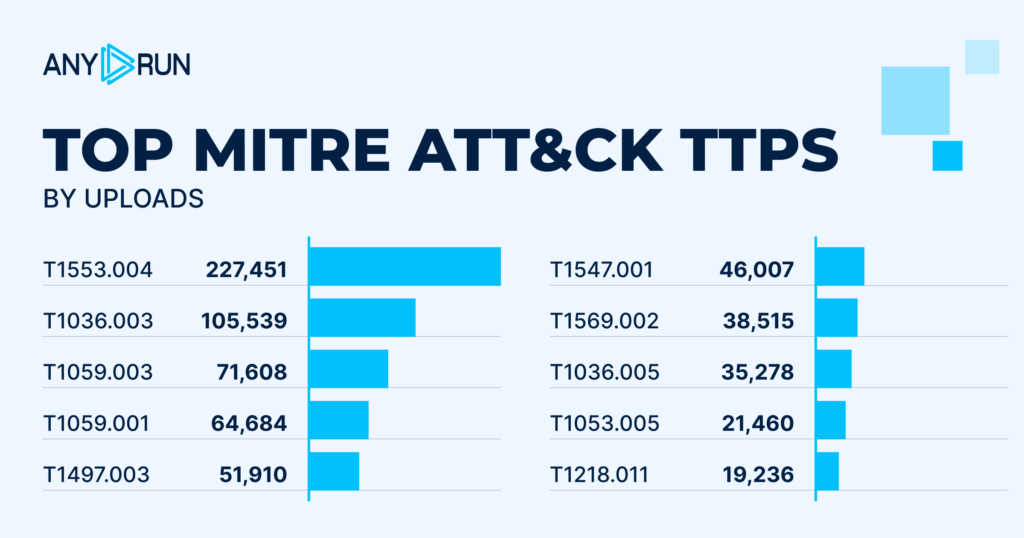
The top 10 most detected techniques, tactics, and procedures (TTPs) show significant shifts from quarter to quarter — a reminder that threat actors never stop refining and changing their methods.
The number of detections for TTPs mostly grew: the first place is taken up by Subvert Trust Controls: Install Root Certificate, T1553.004 with 227,451 detections. In Q3, the first place was taken by a TTP with activity rate twice as small.
Second place was still occupied by Masquerading: Rename Legitimate Utilities, T1036.003 with 105,539 detections (+9%).
A new addition to the list, Command and Scripting Interpreter: Windows Command Shell , T1059.003, came third with 71,608 detections.
1. Subvert Trust Controls: Install Root Certificate, T1553.004: 227,451
2. Masquerading: Rename Legitimate Utilities, T1036.003: 105,539
3. Command and Scripting Interpreter: Windows Command Shell, T1059.003: 71,608
4. Command and Scripting Interpreter: PowerShell, T1059.001: 64,684
5. Virtualization/Sandbox Evasion: Time Based Checks, T1497.003: 51,910
6. Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder, T1547.001: 46,007
7. System Services: Service Execution, T1569.002: 38,515
8. Masquerading: Match Legitimate Resource Name or Location, T1036.005: 35,278
9. Scheduled Task/Job: Scheduled Task, T1053.005: 21,460
10. Signed Binary Proxy Execution: Rundll32, T1218.011: 19,236
TI Lookup offers a searchable database of fresh Indicators of Compromise (IOCs), Attack (IOAs), and Behavior (IOBs) belonging to the latest cyber attacks on 15,000 companies.

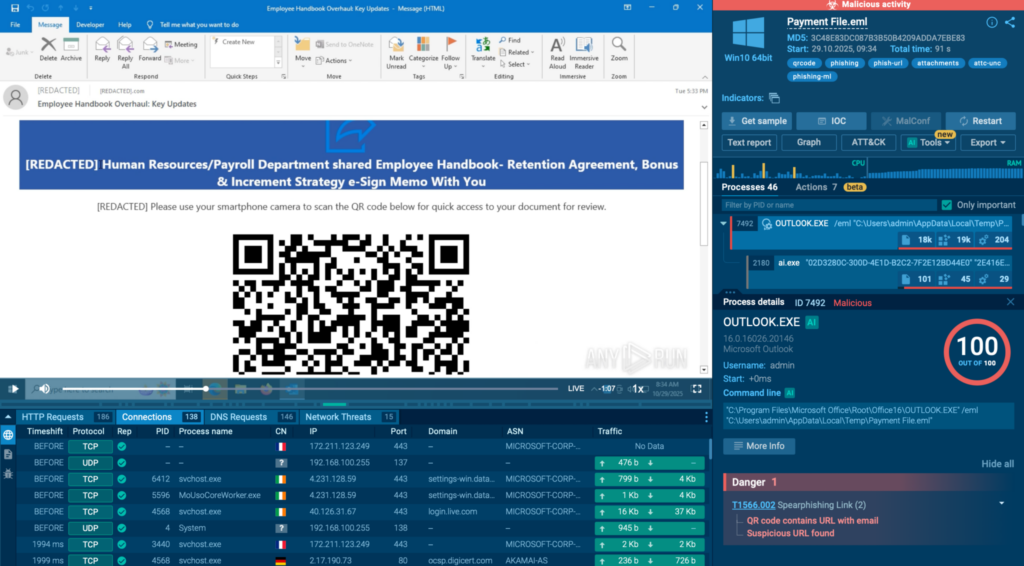
Overall phishing activity by uploads: 159,592
Phishkits:
Q4’s results align with our annual report’s conclusions: phishing is a prevalent type of cyber threat and Tycoon dominates in this category:
Key observations regarding APT activity in Q4 2025:
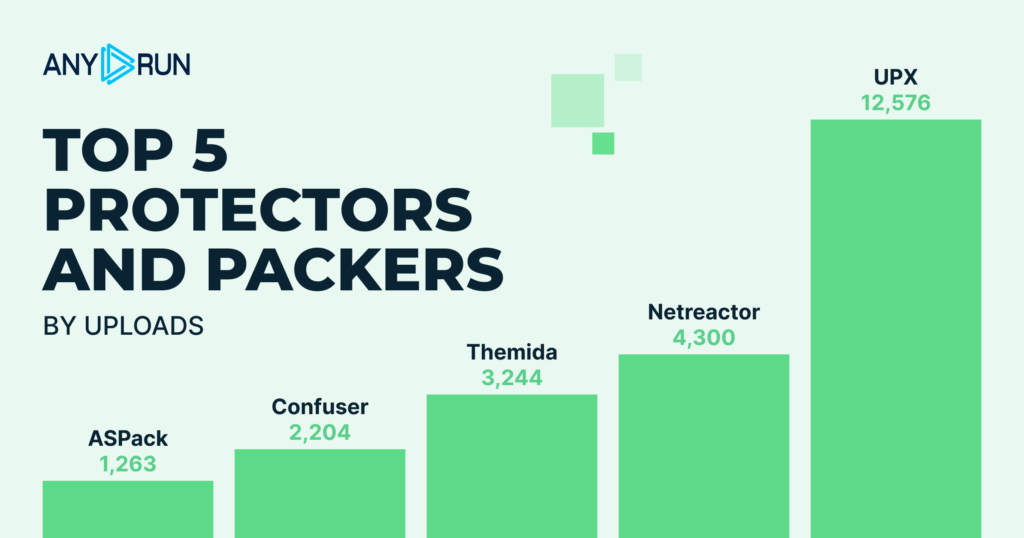
Top 5 most detected protectors and packers correspond with those of Q3. However, there are differences in terms of their intensity:
Q4 2025 shows a stable but evolving threat landscape. Key trends include persistent stealer activity, rising RATs and backdoors, and a dynamic phishing landscape. These insights underscore the importance of continuous monitoring and proactive threat analysis to stay ahead of emerging risks.
ANY.RUN develops solutions for malware analysis and threat hunting. Its interactive malware analysis sandbox is used by over 500,000 cybersecurity professionals worldwide. It enables detailed investigation of threats targeting Windows, Android, and Linux systems with hands-on analysis and instant visualization of malware behavior.
ANY.RUN’s threat intelligence solutions, including Threat Intelligence Lookup and Threat Intelligence Feeds, allow teams to quickly identify indicators of compromise, enrich alerts, and investigate incidents early on. As a result, analysts gain actionable insights, uncover hidden threats, and improve overall cybersecurity posture.
Start a 2-week ANY.RUN trial →
The post Malware Trends Q4 2025: Inside ANY.RUN’s Latest Threat Landscape Report appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More