In mid-March 2024, KrebsOnSecurity revealed that the founder of the personal data removal service Onerep also founded dozens of people-search companies. Shortly after that investigation was published, Mozilla said it would stop bundling Onerep with the Firefox browser and wind down its partnership with the company. But nearly a year later, Mozilla is still promoting it to Firefox users.
Mozilla offers Onerep to Firefox users on a subscription basis as part of Mozilla Monitor Plus. Launched in 2018 under the name Firefox Monitor, Mozilla Monitor also checks data from the website Have I Been Pwned? to let users know when their email addresses or password are leaked in data breaches.
The ink on that partnership agreement had barely dried before KrebsOnSecurity published a story showing that Onerep’s Belarusian CEO and founder Dimitiri Shelest launched dozens of people-search services since 2010, including a still-active data broker called Nuwber that sells background reports on people. This seemed to contradict Onerep’s stated motto, “We believe that no one should compromise personal online security and get a profit from it.”
Shelest released a lengthy statement (PDF) wherein he acknowledged maintaining an ownership stake in Nuwber, a consumer data broker he founded in 2015 — around the same time he started Onerep.
Onerep.com CEO and founder Dimitri Shelest, as pictured on the “about” page of onerep.com.
Shelest maintained that Nuwber has “zero cross-over or information-sharing with Onerep,” and said any other old domains that may be found and associated with his name are no longer being operated by him.
“I get it,” Shelest wrote. “My affiliation with a people search business may look odd from the outside. In truth, if I hadn’t taken that initial path with a deep dive into how people search sites work, Onerep wouldn’t have the best tech and team in the space. Still, I now appreciate that we did not make this more clear in the past and I’m aiming to do better in the future.”
When asked to comment on the findings, Mozilla said then that although customer data was never at risk, the outside financial interests and activities of Onerep’s CEO did not align with their values.
“We’re working now to solidify a transition plan that will provide customers with a seamless experience and will continue to put their interests first,” Mozilla said.
In October 2024, Mozilla published a statement saying the search for a different provider was taking longer than anticipated.
“While we continue to evaluate vendors, finding a technically excellent and values-aligned partner takes time,” Mozilla wrote. “While we continue this search, Onerep will remain the backend provider, ensuring that we can maintain uninterrupted services while we continue evaluating new potential partners that align more closely with Mozilla’s values and user expectations. We are conducting thorough diligence to find the right vendor.”
Asked for an update, Mozilla said the search for a replacement partner continues.
“The work’s ongoing but we haven’t found the right alternative yet,” Mozilla said in an emailed statement. “Our customers’ data remains safe, and since the product provides a lot of value to our subscribers, we’ll continue to offer it during this process.”
It’s a win-win for Mozilla that they’ve received accolades for their principled response while continuing to partner with Onerep almost a year later. But if it takes so long to find a suitable replacement, what does that say about the personal data removal industry itself?
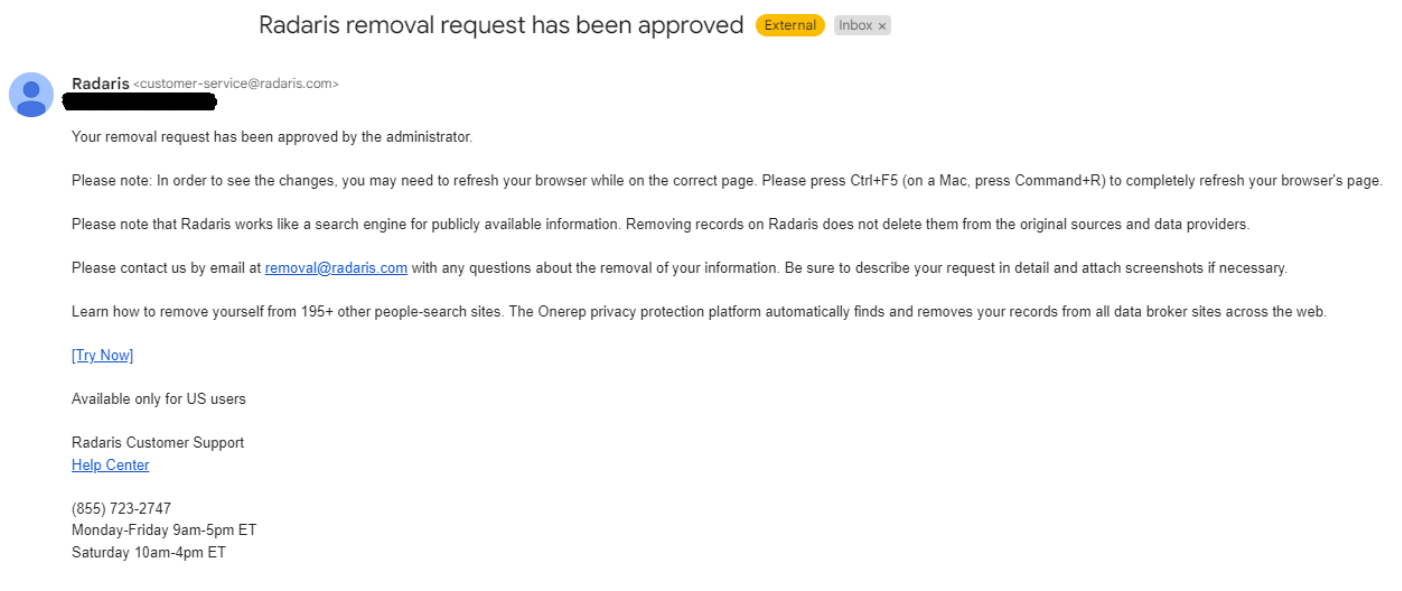
Onerep appears to be working in partnership with another problematic people-search service: Radaris, which has a history of ignoring opt-out requests or failing to honor them. A week before breaking the story about Onerep, KrebsOnSecurity published research showing the co-founders of Radaris were two native Russian brothers who’d built a vast network of affiliate marketing programs and consumer data broker services.
Lawyers for the Radaris co-founders threatened to sue KrebsOnSecurity unless that story was retracted in full, claiming the founders were in fact Ukrainian and that our reporting had defamed the brothers by associating them with the actions of Radaris. Instead, we published a follow-up investigation which showed that not only did the brothers from Russia create Radaris, for many years they issued press releases quoting a fictitious CEO seeking money from investors.
Several readers have shared emails they received from Radaris after attempting to remove their personal data, and those messages show Radaris has been promoting Onerep.
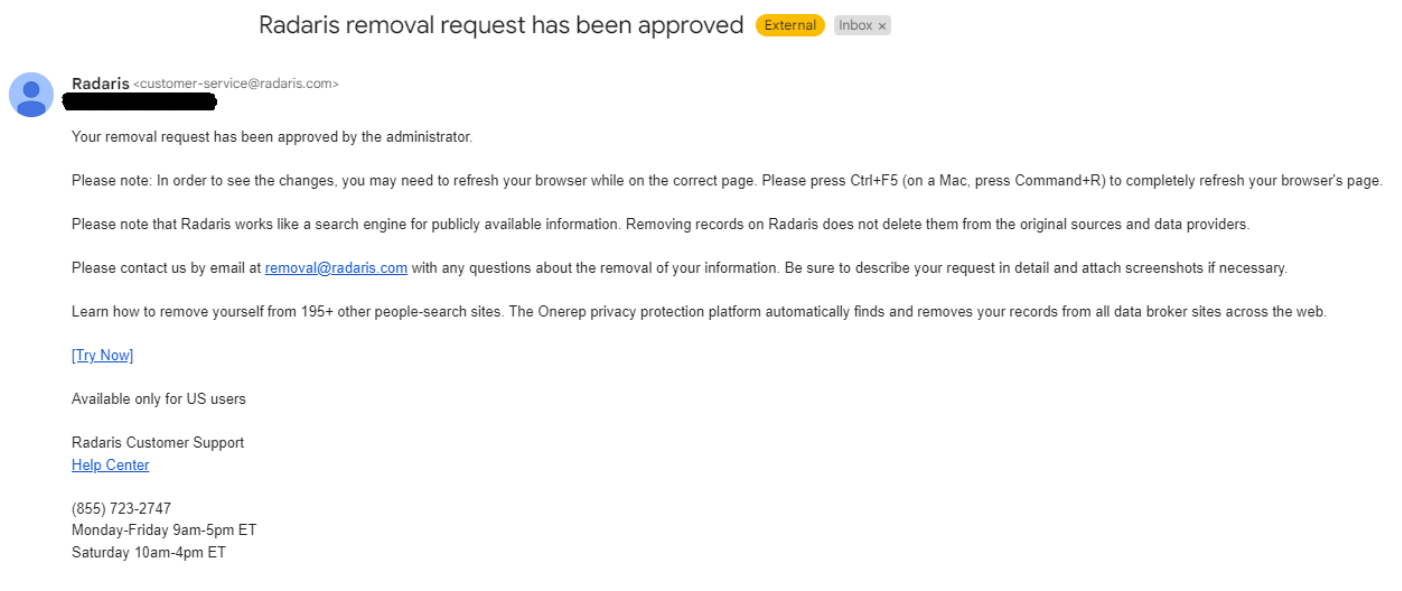
An email from Radaris promoting Onerep.
Krebs on Security –