CYREBRO’s AI-Native MDR Platform Earns Silver at the 2025 Globee Cybersecurity Awards
Tel Aviv, Israel, 12th March 2025, CyberNewsWire
Hackread – Latest Cybersecurity, Tech, AI, Crypto & Hacking News – Read More
Tel Aviv, Israel, 12th March 2025, CyberNewsWire
Hackread – Latest Cybersecurity, Tech, AI, Crypto & Hacking News – Read More
To truly become indispensable in the boardroom, CISOs need to meet the dual demands of defending against sophisticated adversaries while leading resilience strategies.
darkreading – Read More
Dragos case study reveals that Volt Typhoon hacked the US electric grid and stole information on OT systems.
The post China’s Volt Typhoon Hackers Dwelled in US Electric Grid for 300 Days appeared first on SecurityWeek.
SecurityWeek – Read More
San Jose, United States / California, 12th March 2025, CyberNewsWire
Hackread – Latest Cybersecurity, Tech, AI, Crypto & Hacking News – Read More
Strong and smart security operations teams are at the heart of any cybersecurity strategy, and today a startup that builds tooling to help keep them on their toes is announcing some funding on the back of a lot of growth. Pentera — which has built a system that launches simulations of network attacks to stress […]
© 2024 TechCrunch. All rights reserved. For personal use only.
Security News | TechCrunch – Read More
Artificial Intelligence (AI) becomes increasingly integrated into daily life, offering unprecedented advancements in automation, communication, and cybersecurity. However, as AI models grow more sophisticated, they also introduce new threats. Discussions about AGI (Artificial General Intelligence) and superintelligence often dominate public discourse, but immediate risks demand urgent attention.
This article explores three major AI threats: AI-powered phishing and malware generation, the misuse of AI for opinion shaping and unethical purposes, and unintended AI failures leading to harmful consequences. Understanding these risks and their countermeasures is crucial for AI safety and security.
Phishing has long been a major concern, but AI-driven automation has made it more effective than ever. Modern AI models generate hyper-personalized phishing emails, deepfake videos, and voice clones, making fraudulent messages more convincing and harder to detect.
A study of Cornell University analyzed AI-generated phishing emails and revealed how models like GPT-4 can evade traditional detection mechanisms. Despite machine learning-based detection tools, attackers continuously refine tactics to bypass defenses.
Some phishing campaigns now combine Open-Source Intelligence (OSINT) with LLMs to craft messages that exploit personal details. More advanced methods involve face spoofing, video generation, and voice cloning, creating a multi-modal attack strategy that achieves alarming success rates.
Beyond phishing, AI models can be manipulated to generate malware, write harmful scripts, or aid cybercriminal activities. Jailbreaking techniques exploit vulnerabilities in model alignment to bypass ethical safeguards.

AI providers often use test-time scaling, classifiers, and reinforcement learning reward models to guide inference outputs subtly. This raises ethical concerns about transparency and the risk of misinformation.
Companies such as OpenAI, Mistral, and DeepSeek have the power to align models in ways that reinforce corporate, investor, or political agendas. Concerns grow over their ability to shape public opinion.
In February 2025, researchers extracted DeepSeek’s system prompts, revealing that the model’s outputs could be manipulated to favor specific narratives. Techniques such as Bad Likert Judge and Crescendo demonstrated how alignment constraints could be bypassed.
AI-generated responses can steer users toward particular viewpoints, impacting public opinion and even electoral outcomes. Many users accept AI-generated information as fact, compounding the risk.
For example, the Skeleton Key technique documented by Microsoft instructs AI models to modify their behavior guidelines, effectively overriding ethical safeguards while adding disclaimers.
While many AI risks stem from malicious intent, some arise unintentionally due to flawed model design. Unintended consequences include providing harmful advice, generating dangerous content, or failing in critical applications.
AI companies may face lawsuits if their models inadvertently cause harm. Providers must implement robust safeguards, but balancing accessibility with security remains a challenge. Continuous monitoring and real-time anomaly detection are crucial.
Given these threats, researchers and AI companies are developing countermeasures:
In ANY.RUN’s Interactive Sandbox, for example, AI summaries help users better understand potential dangers involved in a particular task. Users can generate summaries of nearly any event within the virtual machine by clicking the AI button next to that event, or they can receive a summary of the entire task upon its completion.
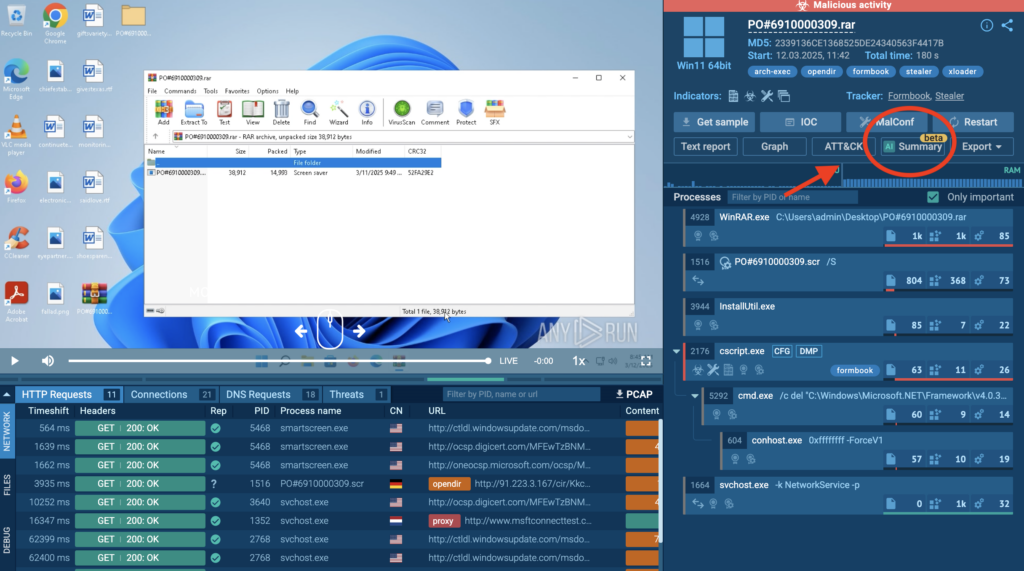
View the analysis in the sandbox
AI also powers automated interactivity in the Sandbox: it helps to automatically perform tasks like handling CAPTCHAs, clicking specific buttons, and more.
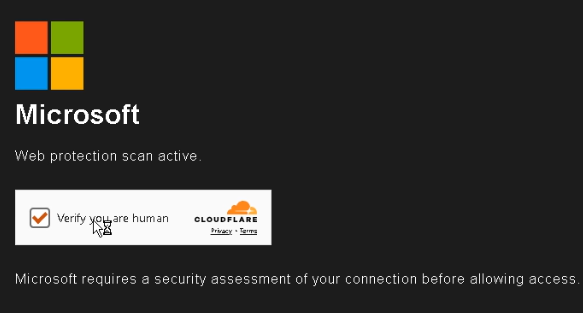
View the analysis in the sandbox
The rapid evolution of AI presents both unprecedented opportunities and serious security risks. AI-driven phishing, jailbreaking, opinion manipulation, and unintended harmful outputs demand continuous vigilance.
While defensive measures such as AI red teaming, dynamic safeguards, and transparency initiatives help mitigate these threats, the challenge remains a constant arms race between attackers and defenders. For businesses, it is the challenge to keep balance between embracing new horizons AI opens and obviating the hazards it poses.
Leverage TI Lookup for threat discovery, research, detection and response!
50 search queries for test: contact us now.
ANY.RUN helps more than 500,000 cybersecurity professionals worldwide. Our interactive sandbox simplifies malware analysis of threats that target both Windows and Linux systems. Our threat intelligence products, TI Lookup, YARA Search, and Feeds, help you find IOCs or files to learn more about the threats and respond to incidents faster.
The post AI Safety: Key Threats and Solutions appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
API attacks are constantly on the rise, with a recent alarming study showing that 59% of organizations give…
Hackread – Latest Cybersecurity, Tech, AI, Crypto & Hacking News – Read More
Hackers used compromised credentials to access PowerSchool’s PowerSource portal months before the December 2024 data breach.
The post PowerSchool Portal Compromised Months Before Massive Data Breach appeared first on SecurityWeek.
SecurityWeek – Read More
Microsoft on Tuesday patched a zero-day vulnerability in the Windows Win32 kernel that has been exploited since March 2023.
The post Newly Patched Windows Zero-Day Exploited for Two Years appeared first on SecurityWeek.
SecurityWeek – Read More
Microsoft’s March 2025 Patch Tuesday fixes six actively exploited zero-day vulnerabilities, including critical RCE and privilege escalation flaws. Learn how these vulnerabilities impact Windows systems and why immediate patching is essential.
Hackread – Latest Cybersecurity, Tech, AI, Crypto & Hacking News – Read More