I’ve tested dozens of robot vacuums, and these are my favorite Cyber Monday deals
These hand-picked Cyber Monday deals on robot vacuums are ending soon, so act fast and grab them before they’re gone.
Latest news – Read More
These hand-picked Cyber Monday deals on robot vacuums are ending soon, so act fast and grab them before they’re gone.
Latest news – Read More
The Debian project releases a new Live distribution that takes open-source very seriously.
Latest news – Read More
These Cyber Monday tablet deals from Apple, Samsung, Microsoft, and more are ending soon.
Latest news – Read More
November was a packed month for detection coverage. We rolled out new behavioral insights, broadened our visibility across multiple threat families, and strengthened rulesets at every layer. On top of that, our analysts uncovered and documented a new phishing wave targeting Italian organizations through malicious PDF attachments, now fully mapped in a dedicated TI report.
Let’s walk through the full set of improvements we delivered this month.
In November, we published several new TI Reports covering threats that are currently targeting companies around the world. The four of them are open to everyone:
We also wrote an extensive report exclusively for the TI Lookup Premium subscribers. It goes in-depth on a phishing campaign aimed specifically at Italian organizations across transportation, tourism, telecom, IT, and government sectors. The activity relies on PDF attachments disguised as official documents, each redirecting victims to counterfeit Microsoft login pages built to harvest corporate credentials.
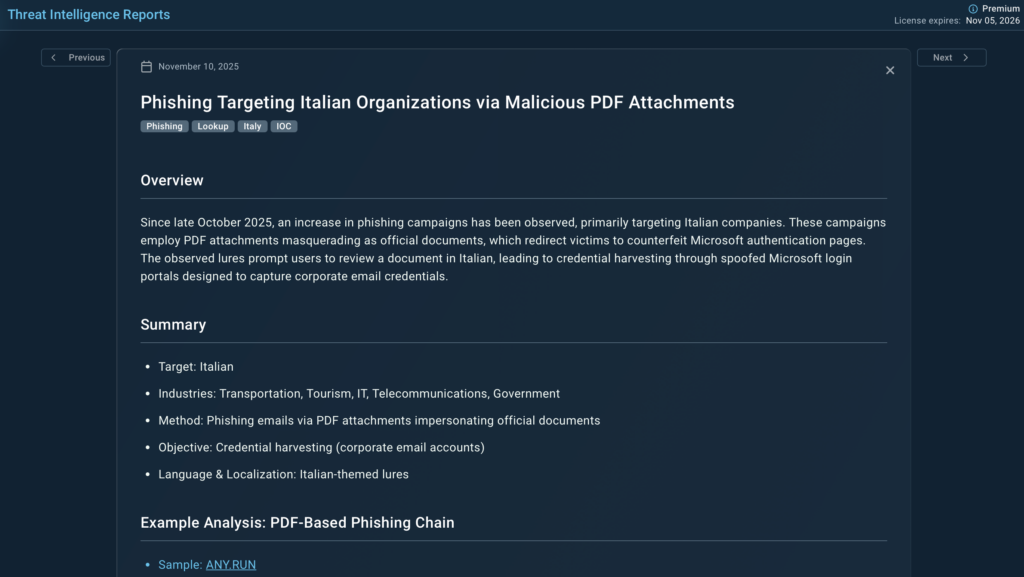
The report outlines:
We also included ready-to-use TI Lookup queries so analysts can surface related samples quickly, track the filename cluster, and follow the network infrastructure across recent public analysis sessions.
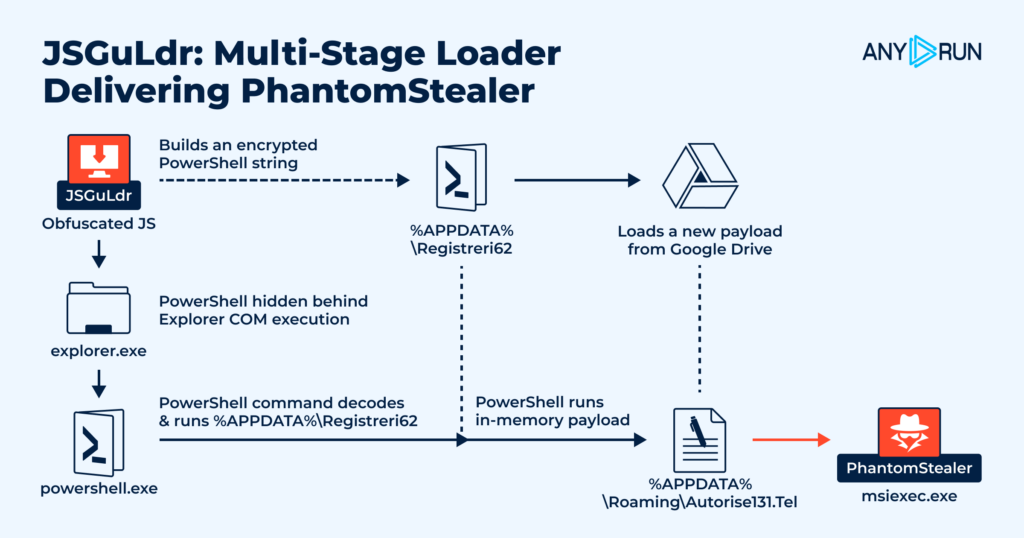
In November, we expanded the malicious behavior coverage of ANY.RUN’s Interactive Sandbox with 52 new signatures across ransomware families, loaders, post-exploitation tools, and suspicious PowerShell activity. These additions help analysts surface malicious behavior earlier, reduce repeated checks, and speed up root-cause discovery.
Here are the latest signatures added:
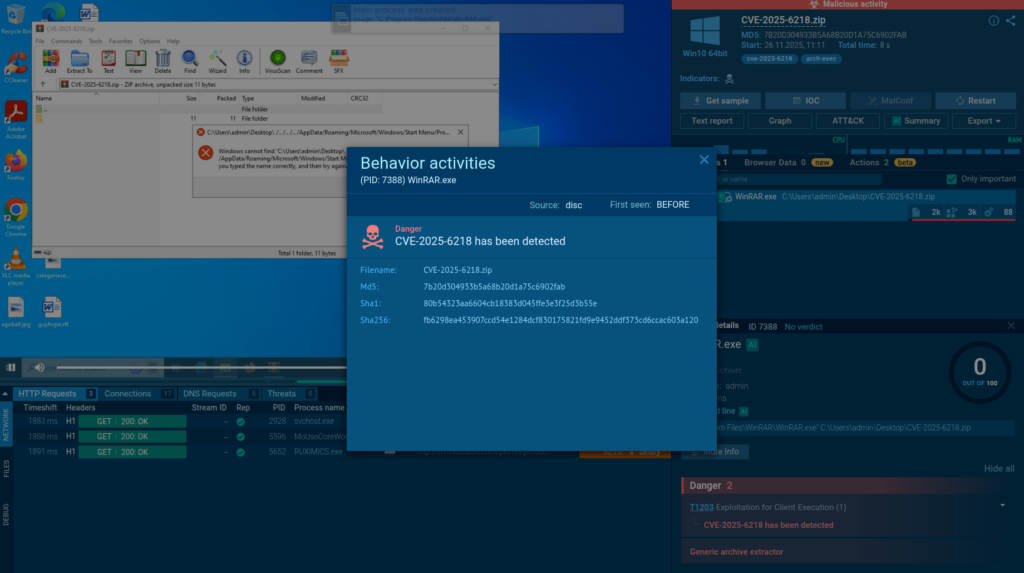
We added 9 YARA rules in November to improve early detection of ransomware, RAT families, and network-proxy tooling. These rules help analysts flag suspicious samples even before execution, making triage faster and more reliable.
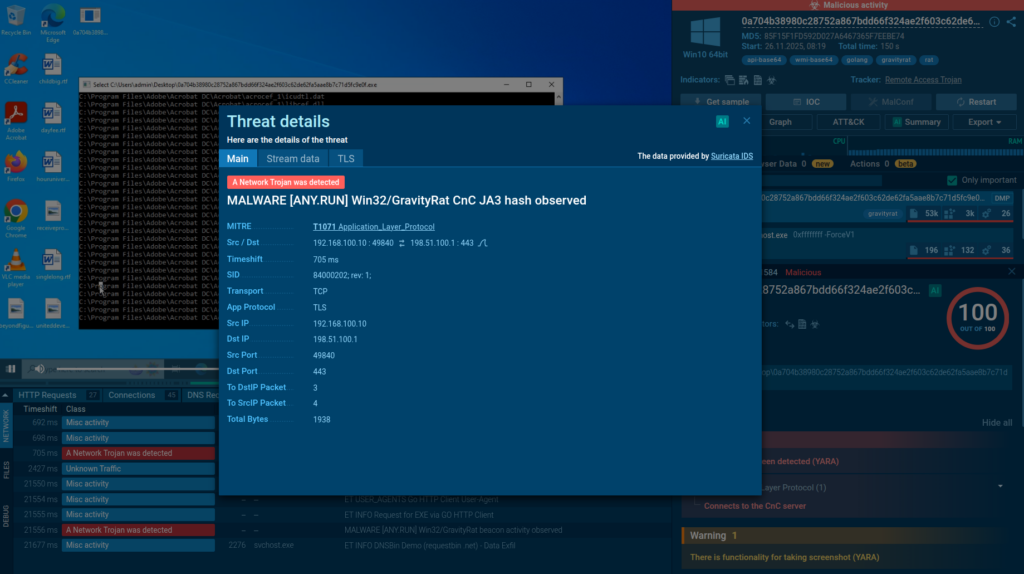
In November, we added 2,184 new Suricata rules, strengthening network-level detection for RAT traffic, stealer activity, and modern phishing techniques. These additions expand coverage for TLS fingerprinting and browser-based deception tactics.
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, is used by more than 500,000 analysts across 15,000 organizations worldwide. The service helps teams investigate threats in real time, follow full execution chains, and surface critical behavior within seconds.
Analysts can detonate samples, interact with them as they run, and immediately pivot into network traces, file system changes, registry activity, and memory artifacts. With continuously updated detection coverage, including new behavioralsignatures, YARA rules, Suricata rules, and TI insights, teams get faster answers and clearer visibility with less manual effort.
Whether you’re running day-to-day investigations, handling escalations, or tracking emerging campaigns, ANY.RUN gives SOC teams, DFIR analysts, MSSPs, and researchers a practical way to reduce uncertainty and make decisions with confidence.
Start your 14-day trial of ANY.RUN today →
The post Threat Coverage Digest: New Malware Reports and 5K+ Detection Rules appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
What generates the fastest profit for cybercriminals? Attacking systems that can help them access confidential information or finances directly. Therefore, it’s no surprise that entire groups of cybercriminals specialize in embedded systems: primarily ATMs full of cash, payment systems where transactions can be intercepted, medical equipment where personal data is processed and stored, and so on. All these devices often have less than an adequate level of security (both cyber and physical), making them a convenient target for attackers.
The classic challenge of protecting embedded systems running Windows is that their hardware typically becomes obsolete much slower than their software. These are often expensive devices that organizations won’t replace simply because the operating system has stopped receiving updates. The result is a high percentage of embedded devices with limited resources due to their narrow specialization, outdated software, and an operating system that’s no longer supported by manufacturer.
The end of support for Windows 10 is exacerbating this last issue. A multitude of devices that are perfectly capable of performing their primary functions for years to come will never be able to upgrade to Windows 11 — simply because they lack a TPM module.
The situation isn’t much better in the market for embedded Linux devices. Those built on x86 processors generally have newer hardware — but even that becomes outdated over time. Furthermore, many new embedded systems running Linux are based on the ARM architecture, which has its own specific requirements and challenges.
Because of these unique characteristics, standard endpoint security solutions are a poor fit. Protecting these devices requires a product equipped with technologies that can effectively counter modern threats targeting embedded systems. At the same time, it must be capable of running not only on modern hardware with the latest OS versions, but also on resource-constrained devices, and should be able to provide ideal stability in “unattended” mode, plus compatibility with specific embedded software. Ideally, it should be manageable from the same console as the rest of owner’s IT infrastructure, and support integration with corporate SIEM systems. As you’ve probably guessed, we’re talking about Kaspersky Embedded Systems Security.
We’ve talked repeatedly in this blog about the specific challenges of securing embedded systems, and our take on the same. However, Kaspersky Embedded Systems Security continues to evolve. In late November, we released a sweeping product update that enhances both the Windows and Linux versions.
Our experts have overhauled the solution’s codebase, adding a range of advanced threat detection and blocking mechanisms. The cornerstone of this update is a full-fledged behavioral analysis engine, which powers several technologies essential for modern device protection:
Another technology added to the updated Kaspersky Embedded Systems Security for Windows is BadUSB Attack Prevention. In a BadUSB attack, a malicious device that mimics a legitimate input peripheral — most often a keyboard — is connected to the target system. Through this device, the attacker can then cause all sorts of problems: input their own commands, intercept data entered from other devices (such as the login credentials of a service technician), cause denial of service, and more. This threat is especially relevant for embedded systems installed outside a company’s physical security perimeter. A BadUSB device plugged into the port of a standalone ATM in a remote rural area can go unnoticed for months and, unless blocked by a security solution, inflict significant damage.
We’ve also added our firewall to the solution. This allows administrators to control network access for specific applications via rules based on predefined trust levels for that software. Since an embedded device typically has a limited set of tasks, it makes sense to only permit network access for the applications that genuinely need it to function properly, while blocking all others. This not only makes life harder for attackers attempting to communicate with command-and-control (C&C) servers or exfiltrate data, but also reduces the risk of the system being used as a platform to attack the rest of the corporate infrastructure.
Finally, for administrator convenience, we’ve added a security status indicator, or a “traffic light”. This provides an at-a-glance assessment of how thoroughly each device is configured, showing whether all critical protection technologies are enabled, or if an administrator needs to review the settings and check the device’s security posture.
We’ve also significantly enhanced the new Kaspersky Embedded Systems Security for Linux. While most of the improvements boost the effectiveness of existing protection mechanisms, one fundamental change is our revamped application allowlist control system. It now uses certificate-based signing to streamline the process of updating the system and the applications required by the embedded device.
Unlike Windows, Linux systems don’t have a universal, ready-made certificate infrastructure that we could simply support. Therefore, at the request of one of our largest customers, we built our own. As a result, there’s no longer a need to regularly create and completely redeploy a full golden system image to every device — though, of course, you can continue to do this if your company needs it for any reason. Now, you simply need to sign a new application with your certificate, and the allowlist system in Kaspersky Embedded Systems Security will accept it and allow it to run without any further issues.
Another new technology in Kaspersky Embedded Systems Security for Linux is Web Threat Protection. The average usage model for embedded systems implies that it’s not the most useful feature on a device without a direct user. However, in practice, there are scenarios where embedded systems do use web protocols. For instance, some PoS devices require access to a corporate web-based CRM system, and the medical terminal can communicate in the same way with the internal portal that manages patient data. Such system could be compromised by attackers to perform a watering hole attack — infecting machines that connect to it. Furthermore, this protection is essential when using Kaspersky Embedded Systems Security on a regular computer with an outdated OS and no hope of updating it, rather than on an embedded system.
The next major product update is scheduled for the first quarter of 2026. In it, we plan to:
You can learn more about Kaspersky Embedded Systems Security on the official product page.
Kaspersky official blog – Read More
Your chance to take advantage of Black Friday deals on Apple devices is ending soon.
Latest news – Read More
Cybersecurity firm Cato Networks reveals HashJack, a new AI browser vulnerability using the ‘#’ symbol to hide malicious commands. Microsoft and Perplexity fixed the flaw, but Google’s Gemini remains at risk.
Hackread – Cybersecurity News, Data Breaches, Tech, AI, Crypto and More – Read More
Practicing good “operations security” is essential to staying safe online. Here’s a complete guide for teenagers (and anyone else) who wants to button up their digital lives.
Security Latest – Read More
Data exposure by top AI companies, the Akira ransomware haul, Operation Endgame against major malware families, and more of this month’s cybersecurity news
WeLiveSecurity – Read More
Black Friday is over, and we pulled the numbers on our top-selling products. Here’s what we found.
Latest news – Read More