Payment Fraud Detection and Prevention: Here’s All To Know
Here are the most common and latest advancements in payment fraud strategies and payment fraud prevention tools for protecting your business.
Security | TechRepublic – Read More
Here are the most common and latest advancements in payment fraud strategies and payment fraud prevention tools for protecting your business.
Security | TechRepublic – Read More
The first-of-its-kind solution integrates with company codebases, enabling AI agents to work in-context and generate production-grade, front-end code in minutes.
Hackread – Latest Cybersecurity, Tech, AI, Crypto & Hacking News – Read More
Polices that forbid employees from divulging company details are worthless if the same information can be obtained from sources employees have no control over.
darkreading – Read More
Wake up to a new app on your iPhone after the iOS 18.4 update? You’re not the only one.
Latest stories for ZDNET in Security – Read More
The notorious cybercrime group Hunters International is dropping ransomware to focus on data theft and extortion.
The post Hunters International Ransomware Gang Rebranding, Shifting Focus appeared first on SecurityWeek.
SecurityWeek – Read More
Cybersecurity researcher Jeremiah Fowler uncovers a massive 47.8GB database with disturbing AI-generated content belonging to GenNomis.
Hackread – Latest Cybersecurity, Tech, AI, Crypto & Hacking News – Read More
Less than two dozen cybersecurity merger and acquisition (M&A) deals were announced in March 2025.
The post Cybersecurity M&A Roundup: 23 Deals Announced in March 2025 appeared first on SecurityWeek.
SecurityWeek – Read More
Two CVEs now exist for an actively exploited CrushFTP vulnerability and much of the security industry is using the ‘wrong one’.
The post Details Emerge on CVE Controversy Around Exploited CrushFTP Vulnerability appeared first on SecurityWeek.
SecurityWeek – Read More
GitHub has announced new capabilities to help organizations and developers keep secrets in their code protected.
The post 39 Million Secrets Leaked on GitHub in 2024 appeared first on SecurityWeek.
SecurityWeek – Read More
March was a productive and exciting month for the ANY.RUN team. We’ve been working hard to improve both our sandbox platform and Threat Intelligence services — all to help you detect threats faster and stay ahead of cybercriminals.
This month, we focused on expanding the environments available for malware analysis and making our threat detection even sharper. We also published fresh TI reports and introduced new signatures and rules to improve detection accuracy.
Let’s take a quick tour of what’s new in ANY.RUN.
It’s official! The update many security teams have been waiting for is here: ANY.RUN now offers Android OS in the Interactive Sandbox.
You can now investigate Android malware in a real ARM-based sandbox and see exactly how a suspicious APK file behaves in a mobile environment. This means no more guessing, no more blind spots, and no need for separate mobile analysis tools.
Read technical analysis of Salvador Stealer, a new Android banking malware
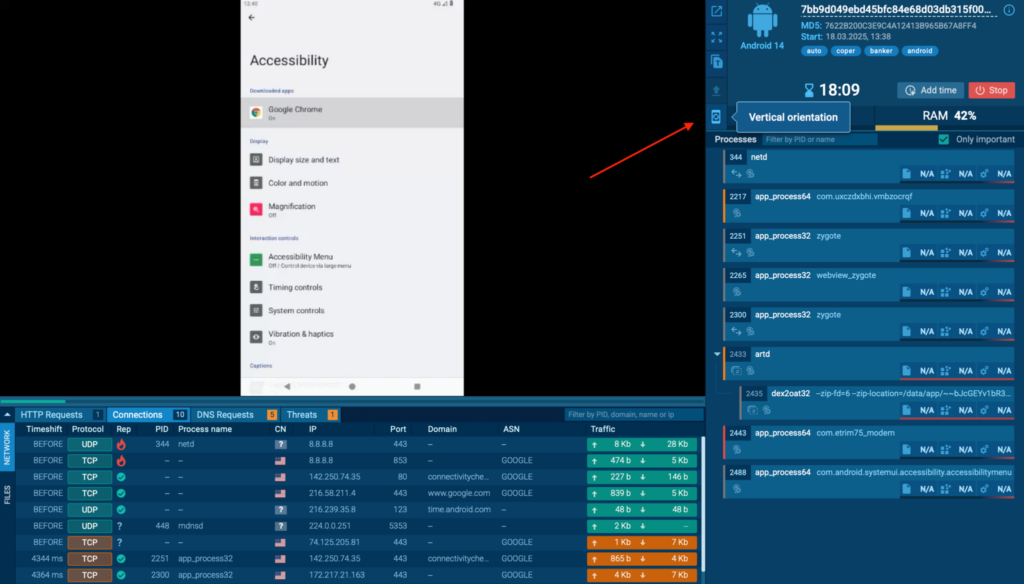
With this release, SOC teams, incident responders, and threat hunters can analyze Android threats faster and with greater accuracy, all within the familiar ANY.RUN interface.
And here’s the best part: Android OS support is available to all users, including Free Plan users.
Why it matters:
This update makes Android malware analysis easier, faster, and more accessible to everyone.

We’ve introduced a new pre-installed software set in the Windows 10 VMs: the Development Toolkit, designed specifically for advanced malware analysis.
With this update, users can now select the “Development” option when configuring their sandbox environment. This toolkit includes essential software like Python, Node.js, debuggers, decompilers, and reverse engineering tools, pre-installed and ready to use.
It’s ideal for analyzing complex threats like Python-based malware, Node.js-based samples, or malware that requires deeper debugging and inspection.
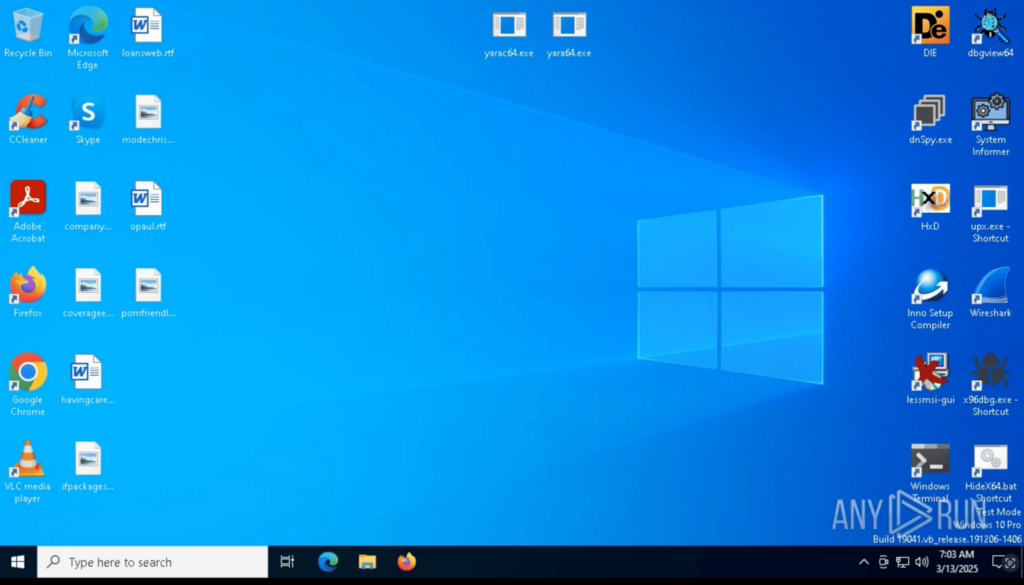
This set removes the need to manually install research tools, making your analysis sessions faster, smoother, and more efficient.
We’ve also boosted our threat detection and intelligence capabilities for more precise analysis.
In March, we expanded our network-based threat detection by adding 1,654 new Suricata rules. These rules enhance visibility over malicious domains, C2 infrastructure, and phishing campaigns.
Key updates include:
In March, we added a total of 64 new behavior-based detection signatures to improve malware visibility and detection accuracy. These signatures cover mutex findings, suspicious activity patterns, C2 communications, and detections for popular malware families.
Highlights from this update include:
Additionally, behavior signatures were introduced to detect:
To further strengthen static detection and classification, we added 5 new YARA rules in March. These rules improve the identification of emerging malware families and suspicious behavior patterns.
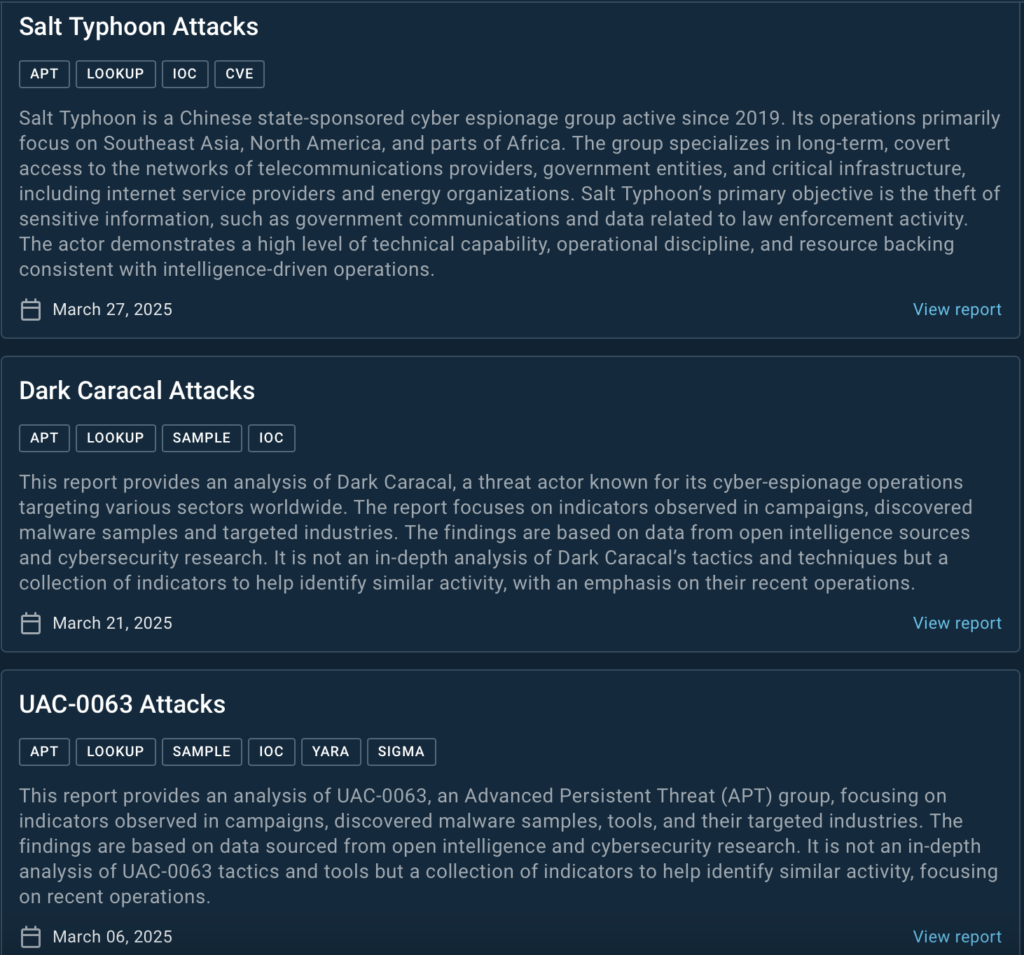
In March, we expanded our Threat Intelligence library with three new reports covering the latest activity of active APT groups. These reports provide valuable insights into real-world attacks, tools, and indicators to help security teams detect and respond to emerging threats.
Here’s what’s new:

ANY.RUN helps more than 500,000 cybersecurity professionals worldwide. Our interactive sandbox simplifies malware analysis of threats that target both Windows and Linux systems. Our threat intelligence products, TI Lookup, YARA Search, and Feeds, help you find IOCs or files to learn more about the threats and respond to incidents faster.
The post Release Notes: Android VM, Pre-Installed Dev Tools, TI Reports & Enhanced Detection appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More