What do you do when you need a program but can’t buy an official license yet? Correct answer: “Use the trial version” or “Find a free alternative.” Wrong answer: “Search online for a cracked version.”
Sketchy alternative sources are known to offer cracked versions of software, along with other goodies. After wading through sites stuffed with ads, you may get the program you want (usually minus the future updates and network functionality), but with a miner, stealer, or whatever else thrown in for good measure.
Based on real-world examples, we explain why you should avoid sites that offer instant downloads of in-demand programs.
Miner and stealer on SourceForge
SourceForge was once the largest site for all things open source, the forerunner of GitHub. But don’t think that SourceForge is dead – today it provides software hosting and distribution services. Its software portal hosts multiple projects, uploaded by anyone who wants to.
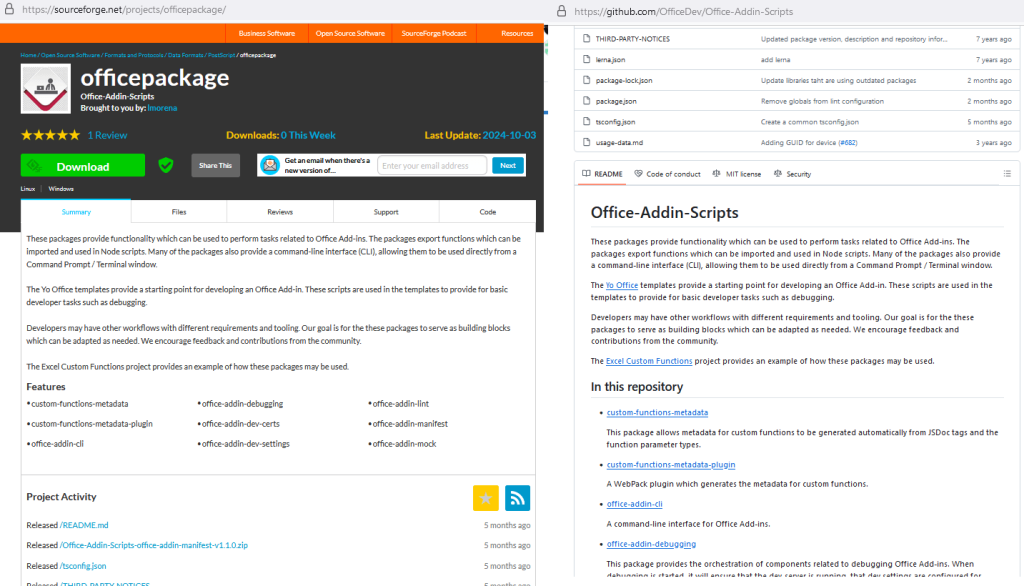
And, as with GitHub, it’s this cosmopolitanism that is a barrier to high-level security. Let’s take just one example: our experts found a project called officepackage on SourceForge. At first glance, it looks harmless: a clear description, no-nonsense name, even a positive review.
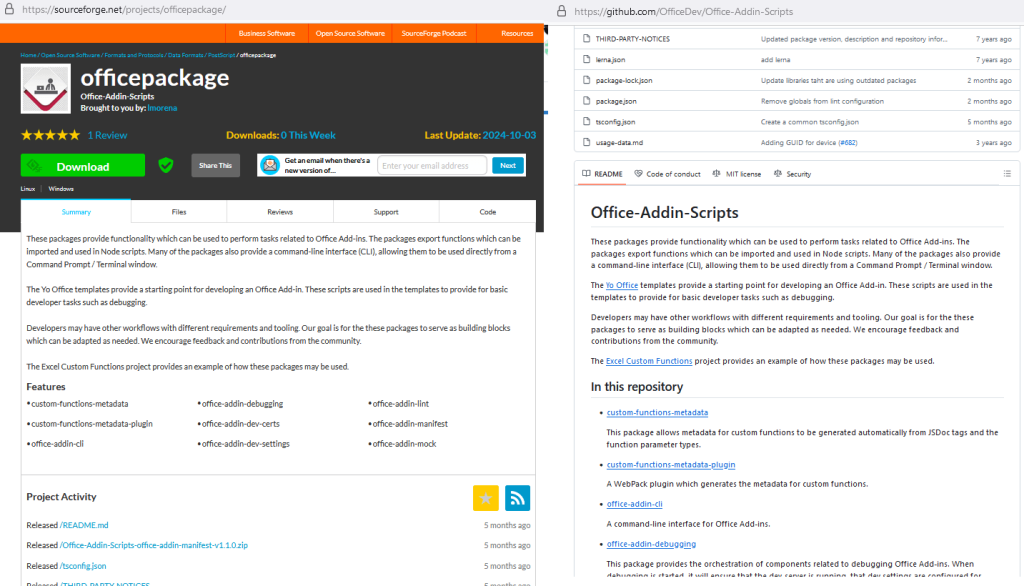
“Officepackage” page on SourceForge
But what if we told you that the description and files were copied outright from an unrelated project on GitHub? Alarm bells are already ringing. That said, no malware lands on your computer when you click the Download button – the project is apparently clean. Apparently, because the malicious payload was not distributed directly through the officepackage project, but through the web page associated with it. How is this possible?
The fact is that every project created on SourceForge gets its own domain name and hosting on sourceforge.io. So a project named officepackage is given a web page at officepackage.sourceforge[.]io. Such pages are easily indexed by search engines and rank high in search results. This is how attackers attract victims.
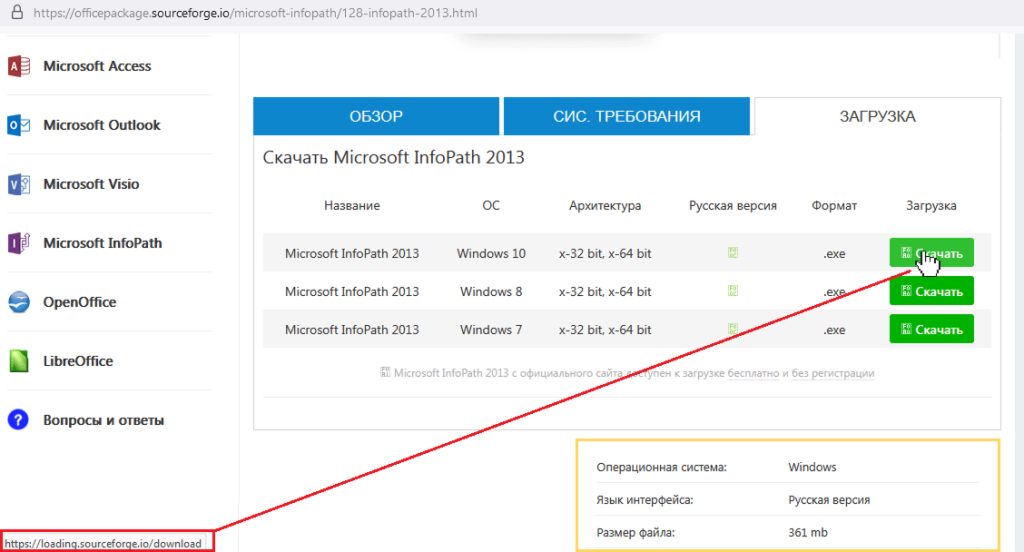
When visiting officepackage.sourceforge[.]io from a search engine brought users to a page offering downloads of almost any version of the Microsoft Office suite. But, as ever, the devil was in the detail: when you hovered over the Download button, the browser’s status bar showed a link to https[:]//loading.sourceforge[.]io/download. Spotted the trap? The new link has nothing to do with officepackage; loading is an entirely different project.
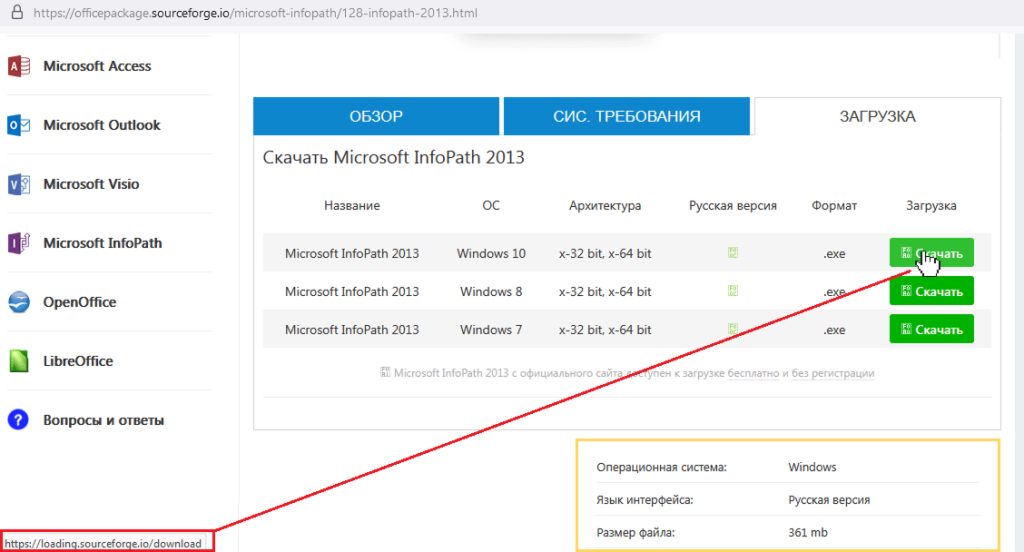
The “Download” button on the “officepackage” page of the SourceForge software portal leads to a completely different project
And after clicking, users were redirected not to the page of the loading project, but to another intermediary site with another Download button. And only after clicking this did the user, weary of surfing, finally receive a file – an archive named vinstaller.zip. Inside was another archive, and inside this second archive was a malicious Windows Installer.
At the heart of this evil nesting doll were two nasties: instead of Microsoft products, a miner and ClipBanker – malware for substituting crypto wallet addresses in the clipboard – were let loose on the victim’s device after running the installer. Details of the infection scheme can be found in the full version of the study on our Securelist blog.
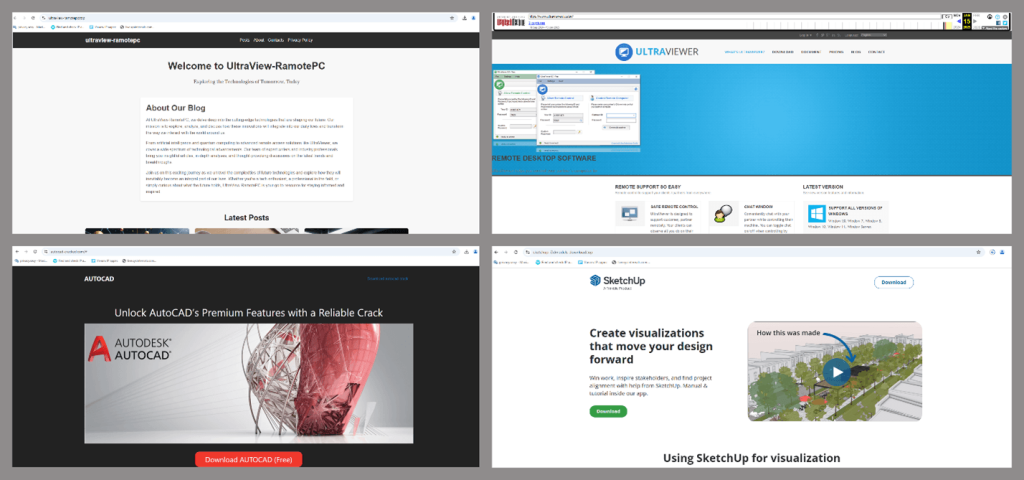
Malicious TookPS installer disguised as legitimate software
Cybercriminals do not limit themselves to SourceForge and GitHub. In another recent case unearthed by our experts, attackers were found distributing the malicious TookPS downloader, already familiar to us from the fake DeepSeek and Grok clients, through fake websites offering free downloads of specialized software. We discovered a whole series of such sites offering users cracked versions of UltraViewer, AutoCAD, SketchUp and other popular professional software, meaning that the attack was not only aimed at home users, but also at professional freelancers and organizations. Other malicious files detected included the names Ableton.exe and QuickenApp.exe, purported versions of the popular music creation and money management applications.
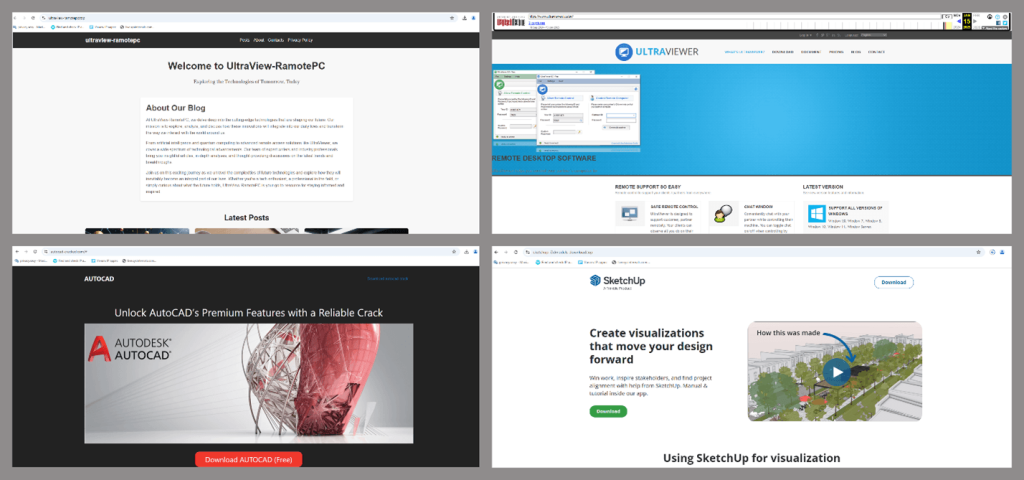
Fake pages distributing TookPS
By circuitous means, the installer downloaded two backdoors to the victim’s device: Backdoor.Win32.TeviRat and Backdoor.Win32.Lapmon. See another Securelist post to find out exactly how the malware was delivered to the victim’s device. The malware gave the attackers full access to the victim’s computer.
How to protect yourself
First, do not download pirated software. Under any circumstances. Ever. A cracked program may be temptingly free and instantly available, but the price you pay will be measured not in money, but in data – your data. And no, that doesn’t mean family photos and chats with friends. Cybercriminals are after your crypto wallets, payment card details, account passwords – and even your computer’s resources for cryptocurrency mining.
Here’s a list of rules we recommend for anyone who uses SourceForge, GitHub and other software portals.
- If you can’t buy the full version of an application, use alternatives or trial versions, not cracked software. You might not get the full functionality, but at least your device is guaranteed to be safe.
- Only download programs from trusted sources. As SourceForge and GitHub practice shows, even then you should proceed with caution and scan all downloaded files with an antivirus.
- Protect your cryptocurrency and banking data with reliable tools. Treat virtual wallets with the same reverence as physical ones.
Further reading in support of not downloading pirated software:
Kaspersky official blog –