A former colleague of ours recently received a suspicious email notification from GetShared — a genuine service he was unfamiliar with. Being the paranoid cautious type that he is (he did work at Kaspersky, after all), he didn’t click the link but instead forwarded the notification straight to us. A closer look at the email message confirmed it was a scam. Indeed, our email security statistics suggest that GetShared has been gaining popularity with scammers. We explain how GetShared is used in attacks, why attackers use it, and how to stay safe.
What a GetShared attack looks like
The victim receives a normal, authentic email notification from GetShared informing them that someone has sent them a file. The message specifies the file name and extension. For example, in the attack targeting our ex-colleague’s employer, it was “DESIGN LOGO.rar”.
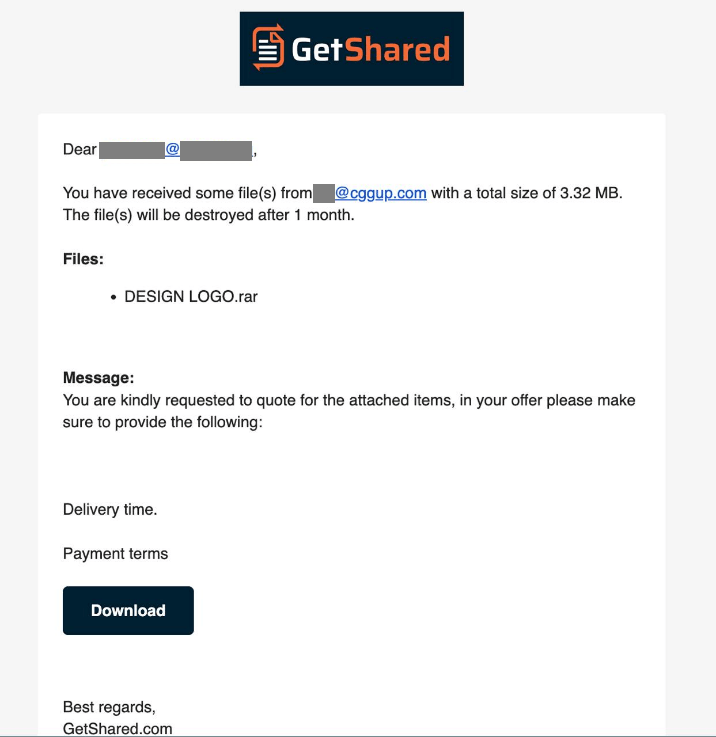
Sample scam email sent as a GetShared notification
The message that accompanies the link employs a classic phishing trick: scammers inquire about prices for items supposedly listed in the attachment. To add a veneer of legitimacy, they ask about delivery time and payment details.
Why malicious actors use GetShared and other third-party services
Security solutions filter out the vast majority of spam, phishing, scam emails, and malicious attachments at the email gateway level. A popular and effective tactic for scammers trying to bypass these defenses is to send emails through legitimate services like Google Calendar or Dropbox. These services, naturally, are uncomfortable being unwitting accomplices in cybercrimes, so they constantly improve their own countermeasures, tighten signup rules, and so on. Therefore, scammers keep looking for new services to exploit. GetShared — a free service for sending large files — turned out to be yet another exploitable tool.
Signs that something’s phishy
Let’s step back from this specific case and GetShared for a moment. Ask yourself: is it really normal practice to send a business inquiry as a note in some random third-party file-sharing service? Assuming a hypothetical client has a genuine business need to transmit a file — say, documents relating to an order — via an external service, they’d typically arrange it first through standard email correspondence before sending you a barrage of notifications. This is business etiquette 101.
When someone asks you to view a text document on a third-party service, there can only be three explanations:
- A security engine flags the document as spam, phishing, or scam.
- The document contains links to a scam, phishing, or malicious website.
- The document is infected, or the attachment is actually a malicious executable rather than a document.
In this particular instance, the service was used to distribute a text file containing a rather absurd request to get in touch with the malicious actors — they were trying to start a conversation to then develop the attack through social engineering.
Coming back to the email campaign we observed, this notification looks especially suspicious, primarily due to the glaring mismatch between the name of the file and the text accompanying it. The message hints at some list of goods, whereas the filename strongly suggests a design project.
Furthermore, take a close look at the sender’s address, which is stated clearly in the notification. A quick search for the domain name immediately reveals that this email address is likely used by scammers.
How to defend against such attacks
To protect your company from scam emails sent through GetShared or any other legitimate services, we recommend the following:
Kaspersky official blog –