I tried this tiny 360° camera drone, and it could be a game-changer for creators
Insta360’s new Antigravity brand is launching a drone that records everything around it simultaneously in 8K.
Latest news – Read More
Insta360’s new Antigravity brand is launching a drone that records everything around it simultaneously in 8K.
Latest news – Read More
This VC funded Anthropic and Perplexity. Here are five predictions it makes for the year ahead in AI
Latest news – Read More
Cybersecurity researchers have disclosed a new Android trojan called PhantomCard that abuses near-field communication (NFC) to conduct relay attacks for facilitating fraudulent transactions in attacks targeting banking customers in Brazil.
“PhantomCard relays NFC data from a victim’s banking card to the fraudster’s device,” ThreatFabric said in a report. “PhantomCard is based on
The Hacker News – Read More
The new DDoS attack vector, which involves HTTP/2 implementation flaws, has been compared to Rapid Reset.
The post ‘MadeYouReset’ HTTP2 Vulnerability Enables Massive DDoS Attacks appeared first on SecurityWeek.
SecurityWeek – Read More
You check that the windows are shut before leaving home. Return to the kitchen to verify that the oven and stove were definitely turned off. Maybe even circle back again to confirm the front door was properly closed. These automatic safety checks give you peace of mind because you know the unlikely but potentially dangerous consequences of forgetting – a break-in, fire, or worse.
Your
The Hacker News – Read More
Editor’s note: The current article was originally published on March 11, 2024, and updated on August 14, 2025.
Security Operations Centers (SOCs) face an overwhelming volume of threat alerts, making it difficult to separate real threats from false positives without heavy resource use.
For teams already working with, or planning to adopt Filigran’s OpenCTI, ANY.RUN now offers powerful interoperability that bring real-time malware analysis and fresh threat intelligence directly into your existing workflows. This helps SOCs boost efficiency, cut response times, and act with confidence, all without replacing current tools.
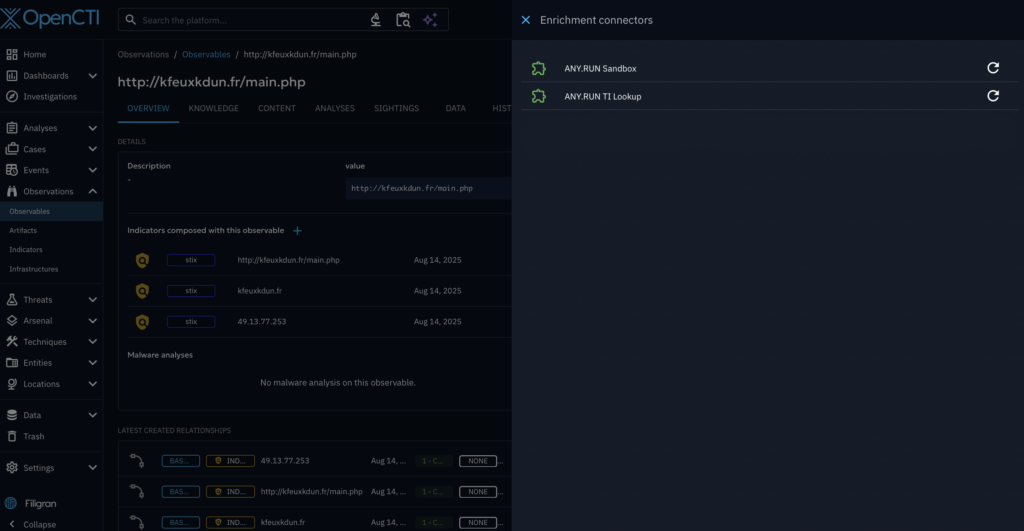
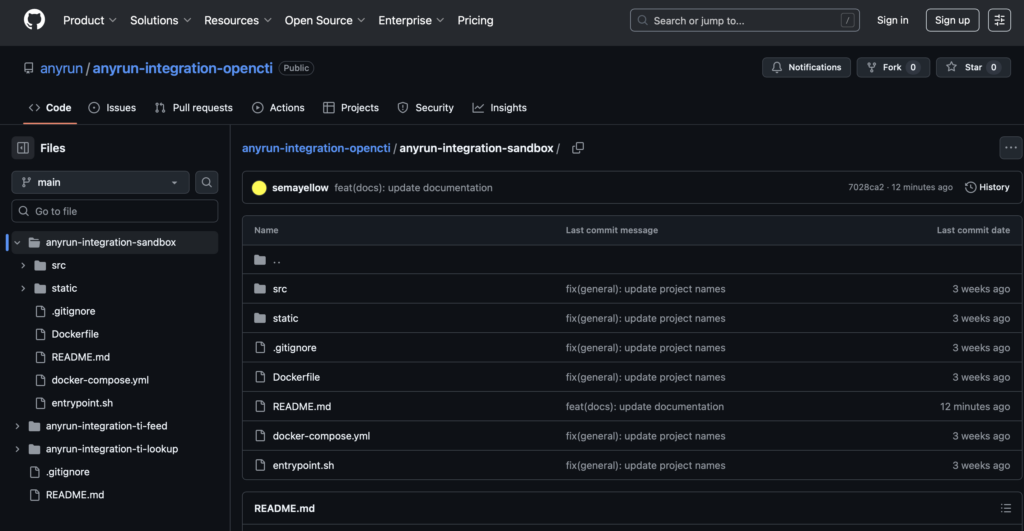
ANY.RUN now offers dedicated OpenCTI connectors for its main products, allowing SOC teams to use them with their existing security stack seamlessly. This means there is no need to change existing processes and tools, making interoperability simple for those already using OpenCTI.
Available for ANY.RUN’s Enterprise plan users, it is designed to improve SOC metrics for incident detection and response, streamline routine tasks, reduce response times, and provide deep analytics.
You can connect any combination of these connectors based on their specific needs and licenses.
View documentation on GitHub →
This connectors ensure that accurate threat info is accessible in just a few clicks, significantly boosting SOC effectiveness.
ANY.RUN’s Interactive Sandbox is a cloud-based service that provides SOC teams with instant access to fully interactive Windows, Linux, and Android virtual machines for analyzing suspicious files and URLs.
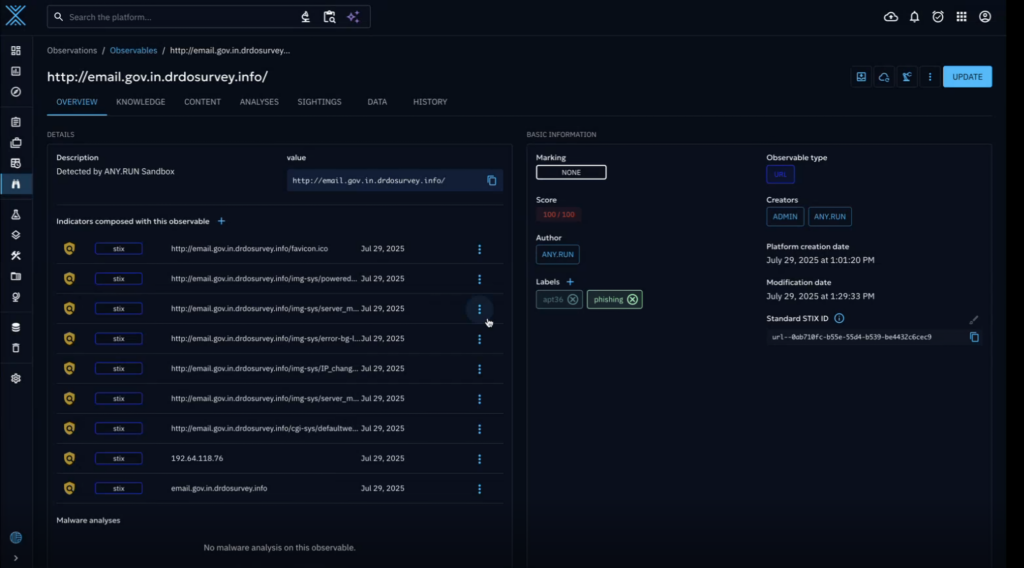
With the OpenCTI connector, SOC teams can:
Use documentation to set up the connector →
The connector leverages the Automated Interactivity feature. It allows for automated execution of user actions like archive extraction, CAPTCHA solution, and payload launching to trigger each stage of an attack and ensure complete detection of the most evasive threats.
The sandbox logs and marks malicious network traffic, processes, registry, and file modifications, providing immediate visibility into threat behavior.
Here’s a typical scenario of how you can use the connector in your SOC:
 Benefits the Interactive Sandbox in OpenCTI
Benefits the Interactive Sandbox in OpenCTI 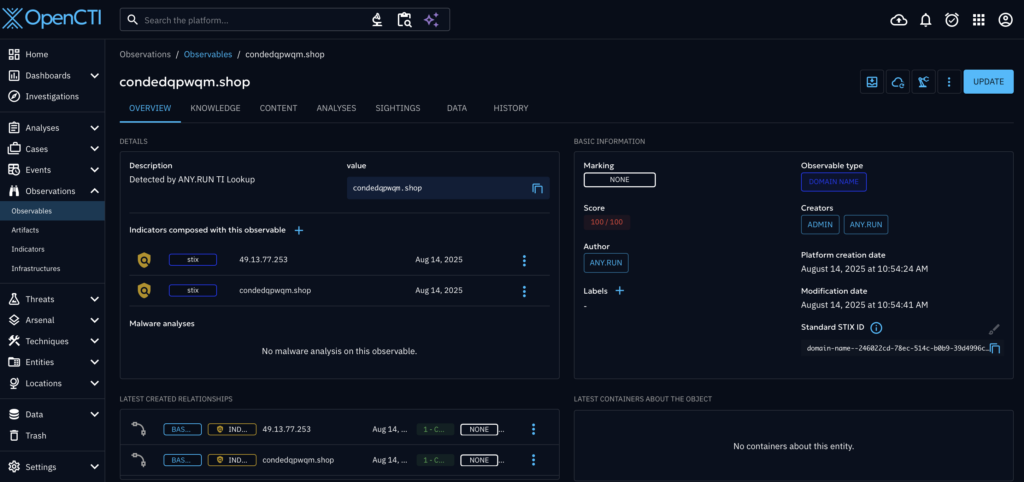
ANY.RUN’s Threat Intelligence Lookup provides a searchable database of fresh Indicators of Compromise (IOCs), Behavior (IOBs), and Action (IOAs). This data is extracted from live sandbox analyses of active malware and phishing attacks across 15,000 organizations, ensuring the indicators are fresh and available quickly after an attack.
With the OpenCTI connector, SOC teams can:
Use documentation to set up the connector →
Here’s a typical scenario of how you can use the connector in your SOC:
 benefits of TI Lookup in OpenCTI
benefits of TI Lookup in OpenCTI 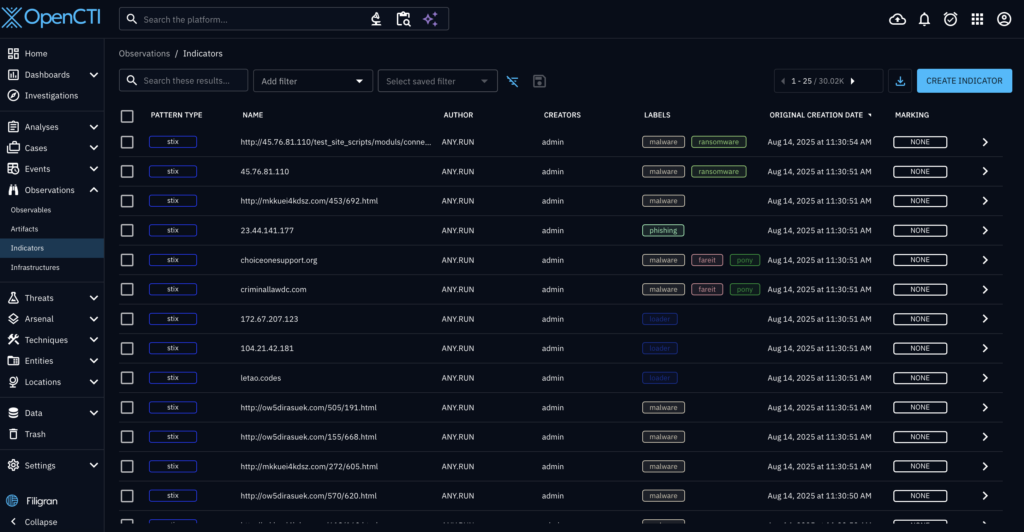
Threat Intelligence Feeds help MSSPs and SOCs fortify their security with filtered, high-fidelity indicators of compromise (IPs, domains, URLs) enriched with context from ANY.RUN’s Interactive Sandbox. Sourced from real-time sandbox investigations of active attacks across 15,000 organizations, ANY.RUN’s feeds are updated every two hours, allowing you to track threats as they emerge, develop, and spread to take critical security actions early.
With the OpenCTI connector, SOC teams can:
Use documentation to set up the connector →
Here’s a typical scenario of how you can use the connector in your SOC:
 Benefits of TI Feeds in OpenCTI
Benefits of TI Feeds in OpenCTIThe interoperability of ANY.RUN with OpenCTI provides significant user and business value, leading to measurable performance gains across the SOC.
Trusted by over 500,000 cybersecurity professionals and 15,000+ organizations in finance, healthcare, manufacturing, and other critical industries, ANY.RUN helps security teams investigate threats faster and with greater accuracy.
Our Interactive Sandbox accelerates incident response by allowing you to analyze suspicious files in real time, watch behavior as it unfolds, and make confident, well-informed decisions.
Our Threat Intelligence Lookup and Threat Intelligence Feeds strengthen detection by providing the context your team needs to anticipate and stop today’s most advanced attacks.
Ready to see the difference? Start your 14-day trial of ANY.RUN today →
The post ANY.RUN & OpenCTI: Transform SOC for Maximum Performance appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
The breach of the US Courts records system came to light more than a month after the attack was discovered. Details about what was exposed—and who’s responsible—remain unclear.
Security Latest – Read More
For a small-form-factor PC that still delivers impressive performance, the Geekom IT15 is a great choice.
Latest news – Read More
Zimperium’s zLabs team uncovers a critical security flaw in the popular Android rooting tool, KernelSU v0.5.7. Learn how…
Hackread – Latest Cybersecurity, Hacking News, Tech, AI & Crypto – Read More
Artificial intelligence is already trying its hand as a travel agent: just ask a chatbot about your chosen destination, and in a couple of seconds you’ll get a full sightseeing itinerary, a list of hotels with good reviews, and even visa tips. And with the help of an AI agent, you can even buy tickets without having to trawl through endless airline websites and flight aggregators. Sounds like a traveler’s dream, but there are downsides. In this post, we look at what to pay attention to when planning a vacation with ChatGPT or another AI assistant.
A Kaspersky study reveals that just 28% of AI users trust artificial intelligence to plan their vacations, (with 96% of that 28% being satisfied with such AI assistance). Note that chatbots possess no knowledge of their own, but learn from input texts and data, and then formulate the most fitting answer to a question. And AI isn’t immune to serving up inaccurate, outdated, or downright false information. Sure, some chatbots already have an internet search function built in, but infallible fact-checking is still a long way off.
In March 2025, Mark Pollard of Australia was due to fly to Chile to give a lecture. But he was turned away at the check-in desk for not having a visa. Mark had duly consulted ChatGPT about the visa requirements of various Latin American countries, and had blindly trusted its response. As of 2019, however, Australian citizens need a visa to visit Chile, but this information was apparently unknown to the neural network. In another case, AI advised a journalist to visit museums that had been wiped out by a forest fire.
Sometimes, even professionals on duty are led astray by bad AI. In 2024, staff at Manila airport tried to stop a passenger boarding a UK-bound flight: she was a UK citizen, but only had her US passport on her at the time. As it turns out, that isn’t grounds to deny boarding a flight to England, but the staff had been misinformed by Google AI Overviews. It took a call to the embassy to resolve the situation.
If you don’t want AI to send you to a closed restaurant or a non-existent landmark, then check the information in real time. Just be aware — and beware — that connecting to public Wi-Fi is always a gamble, with the security of your devices and data at stake. When abroad, it’s much safer to use mobile internet. There’s no need to buy a physical SIM card — just use an eSIM.
Most popular Ais, like ChatGPT and Gemini, process and store all user requests. Which means that in the event of a bug or major leak, outsiders could find out too much about you: travel dates, schedule, budget, and traveling companions. So only share with neural networks data that you wouldn’t mind the whole world knowing.
Many companies these days offer AI agents — digital assistants that can autonomously perform tasks on your behalf. For example, you can ask an AI agent to book a tour, and email your colleagues about your upcoming vacation (please don’t give AI agents access to work chats and email!). Once instructed, the AI agent either launches a virtual machine or captures your computer screen and connects to third-party services.
The problem is that you risk giving the neural network not only your personal data, but also the freedom to perform unwanted actions on websites. Recall that AI agents are vulnerable to prompt injection attacks — hidden commands that attackers plant on phishing pages and hacked websites. Spotting these on your own is near impossible: prompt injections are usually embedded in a website’s metadata or visual elements.
For now at least, the safest way to plan vacation travel is to do your own research and buy everything you need yourself — using AI only as an auxiliary tool. And to minimize the risks associated with prompt injections, use a reliable security solution that blocks all attempts to infect your device with malware.
What else to read before your trip:
Kaspersky official blog – Read More