‘Gentlemen’ Ransomware Abuses Vulnerable Driver to Kill Security Gear
By weaponizing the ThrottleStop.sys driver, attackers are disrupting antivirus and endpoint detection and response (EDR) systems.
darkreading – Read More
By weaponizing the ThrottleStop.sys driver, attackers are disrupting antivirus and endpoint detection and response (EDR) systems.
darkreading – Read More
Sleep Scores are a welcome addition to Apple’s sleep-tracking tech. But there’s another feature that would help manage my stress.
Latest news – Read More
While Apple Intelligence updates weren’t the focus of the event, Apple still had new AI tricks up its sleeve.
Latest news – Read More
Amazon’s October Prime Day is likely coming soon. Here’s what we know so far.
Latest news – Read More
A series of corporate leaks show that Chinese technology companies function far more like their Western peers than one might imagine.
Security Latest – Read More
Google’s strongest security features are tucked behind a single toggle. Turn it on to protect yourself from theft, scams, spam, and more.
Latest news – Read More
The new model can generate three-minute-long tracks almost instantly. Here’s what it’ll cost you.
Latest news – Read More
Despite its recent code deletion disaster, the company is all in on its newest agent.
Latest news – Read More
In May 2025, the European Union levied financial sanctions on the owners of Stark Industries Solutions Ltd., a bulletproof hosting provider that materialized two weeks before Russia invaded Ukraine and quickly became a top source of Kremlin-linked cyberattacks and disinformation campaigns. But new findings show those sanctions have done little to stop Stark from simply rebranding and transferring their assets to other corporate entities controlled by its original hosting providers.

Image: Shutterstock.
Materializing just two weeks before Russia invaded Ukraine in 2022, Stark Industries Solutions became a frequent source of massive DDoS attacks, Russian-language proxy and VPN services, malware tied to Russia-backed hacking groups, and fake news. ISPs like Stark are called “bulletproof” providers when they cultivate a reputation for ignoring any abuse complaints or police inquiries about activity on their networks.
In May 2025, the European Union sanctioned one of Stark’s two main conduits to the larger Internet — Moldova-based PQ Hosting — as well as the company’s Moldovan owners Yuri and Ivan Neculiti. The EU said the Neculiti brothers and PQ Hosting were linked to Russia’s hybrid warfare efforts.
But a new report from Recorded Future finds that just prior to the sanctions being announced, Stark rebranded to the[.]hosting, under control of the Dutch entity WorkTitans BV (AS209847) on June 24, 2025. The Neculiti brothers reportedly got a heads up roughly 12 days before the sanctions were announced, when Moldovan and EU media reported on the forthcoming inclusion of the Neculiti brothers in the sanctions package.
In response, the Neculiti brothers moved much of Stark’s considerable address space and other resources over to a new company in Moldova called PQ Hosting Plus S.R.L., an entity reportedly connected to the Neculiti brothers thanks to the re-use of a phone number from the original PQ Hosting.
“Although the majority of associated infrastructure remains attributable to Stark Industries, these changes likely reflect an attempt to obfuscate ownership and sustain hosting services under new legal and network entities,” Recorded Future observed.
Neither the Recorded Future report nor the May 2025 sanctions from the EU mentioned a second critical pillar of Stark’s network that KrebsOnSecurity identified in a May 2024 profile on the notorious bulletproof hoster: The Netherlands-based hosting provider MIRhosting.
MIRhosting is operated by 38-year old Andrey Nesterenko, whose personal website says he is an accomplished concert pianist who began performing publicly at a young age. DomainTools says mirhosting[.]com is registered to Mr. Nesterenko and to Innovation IT Solutions Corp, which lists addresses in London and in Nesterenko’s stated hometown of Nizhny Novgorod, Russia.
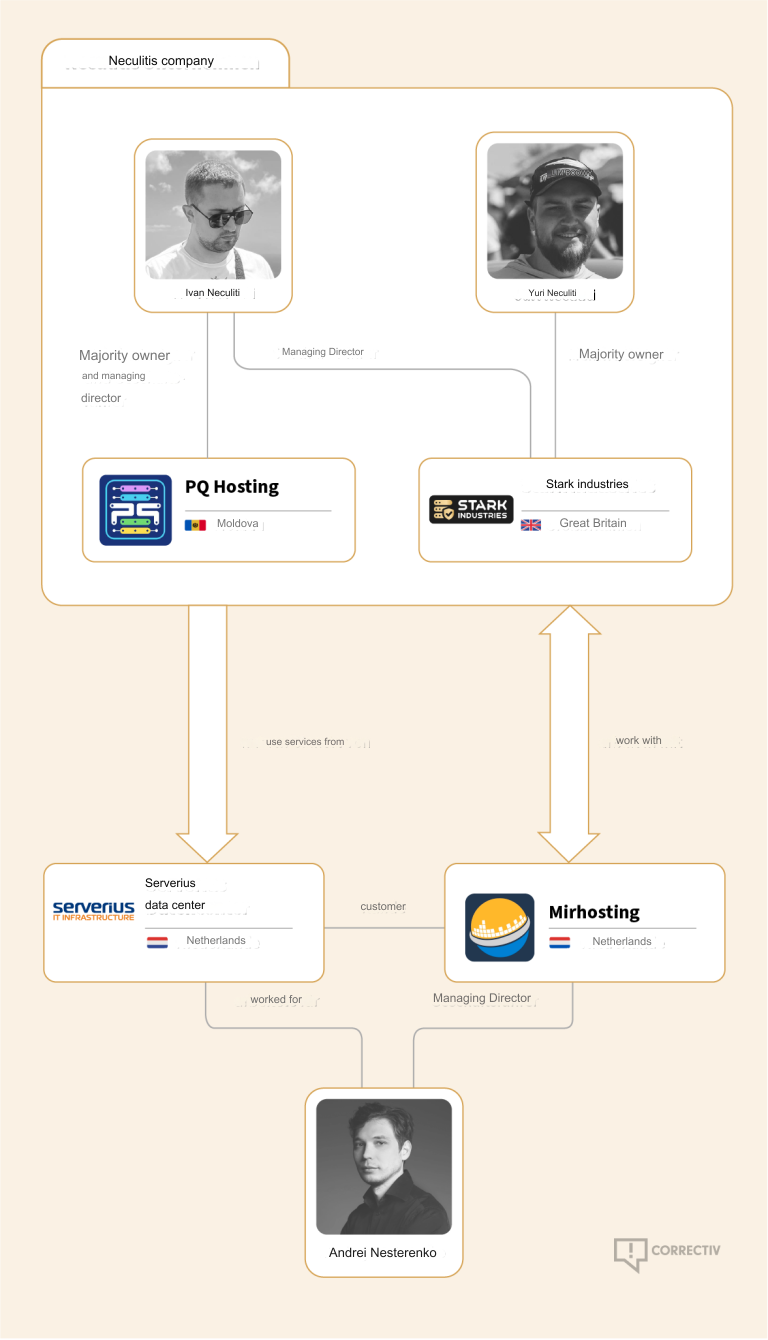
Image credit: correctiv.org.
According to the book Inside Cyber Warfare by Jeffrey Carr, Innovation IT Solutions Corp. was responsible for hosting StopGeorgia[.]ru, a hacktivist website for organizing cyberattacks against Georgia that appeared at the same time Russian forces invaded the former Soviet nation in 2008. That conflict was thought to be the first war ever fought in which a notable cyberattack and an actual military engagement happened simultaneously.
Mr. Nesterenko did not respond to requests for comment. In May 2024, Mr. Nesterenko said he couldn’t verify whether StopGeorgia was ever a customer because they didn’t keep records going back that far. But he maintained that Stark Industries Solutions Inc. was merely one client of many, and claimed MIRhosting had not received any actionable complaints about abuse on Stark.
However, it appears that MIRhosting is once again the new home of Stark Industries, and that MIRhosting employees are managing both the[.]hosting and WorkTitans — the primary beneficiaries of Stark’s assets.
A copy of the incorporation documents for WorkTitans BV obtained from the Dutch Chamber of Commerce shows WorkTitans also does business under the names Misfits Media and and WT Hosting (considering Stark’s historical connection to Russian disinformation websites, “Misfits Media” is a bit on the nose).
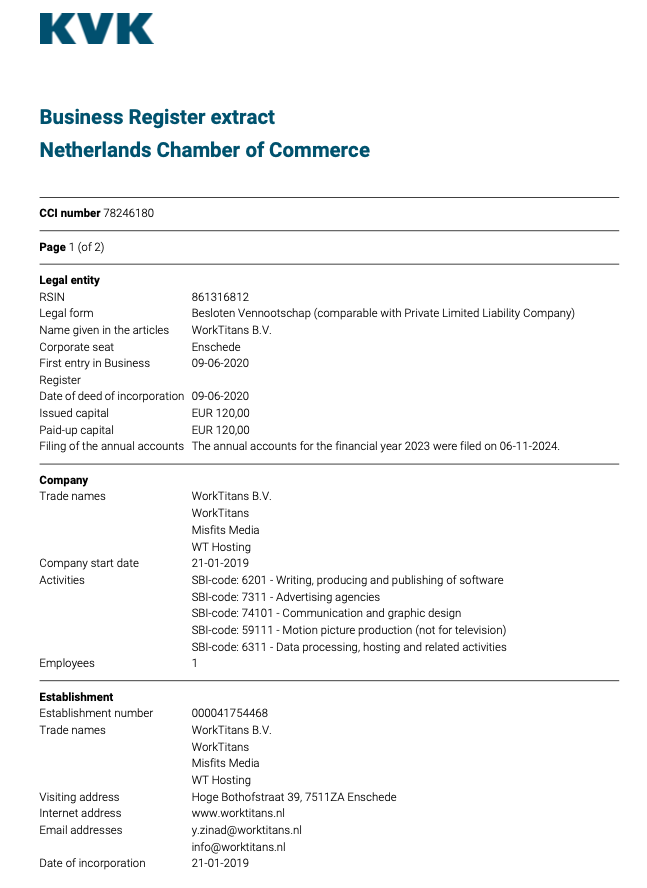
An incorporation document for WorkTitans B.V. from the Netherlands Chamber of Commerce.
The incorporation document says the company was formed in 2019 by a y.zinad@worktitans.nl. That email address corresponds to a LinkedIn account for a Youssef Zinad, who says their personal websites are worktitans[.]nl and custom-solution[.]nl. The profile also links to a website (etripleasims dot nl) that LinkedIn currently blocks as malicious. All of these websites are or were hosted at MIRhosting.
Although Mr. Zinad’s LinkedIn profile does not mention any employment at MIRhosting, virtually all of his LinkedIn posts over the past year have been reposts of advertisements for MIRhosting’s services.
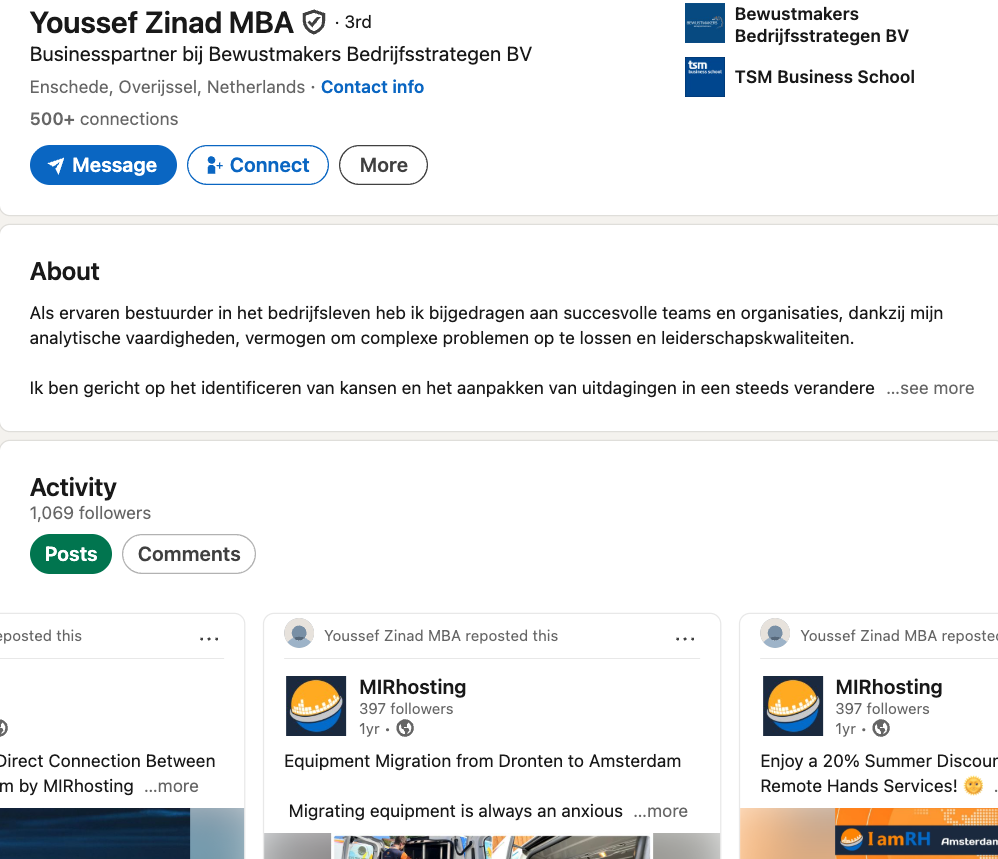
Mr. Zinad’s LinkedIn profile is full of posts for MIRhosting’s services.
A Google search for Youssef Zinad reveals multiple startup-tracking websites that list him as the founder of the[.]hosting, which censys.io finds is hosted by PQ Hosting Plus S.R.L.
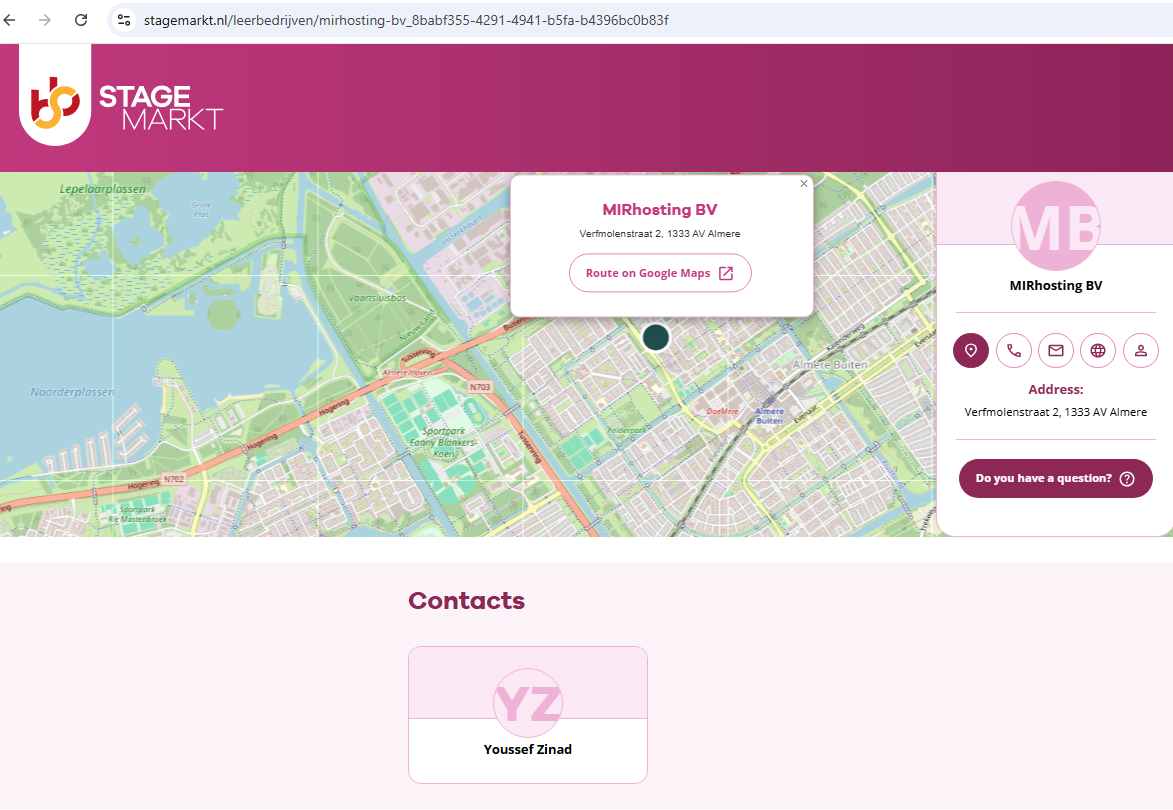
The Dutch Chamber of Commerce document says WorkTitans’ sole shareholder is a company in Almere, Netherlands called Fezzy B.V. Who runs Fezzy? The phone number listed in a Google search for Fezzy B.V. — 31651079755 — also was used to register a Facebook profile for a Youssef Zinad from the same town, according to the breach tracking service Constella Intelligence.
In a series of email exchanges leading up to KrebsOnSecurity’s May 2024 deep dive on Stark, Mr. Nesterenko included Mr. Zinad in the message thread (youssef@mirhosting.com), referring to him as part of the company’s legal team. The Dutch website stagemarkt[.]nl lists Youssef Zinad as an official contact for MIRhosting’s offices in Almere. Mr. Zinad did not respond to requests for comment.
Given the above, it is difficult to argue with the Recorded Future report on Stark’s rebranding, which concluded that “the EU’s sanctioning of Stark Industries was largely ineffective, as affiliated infrastructure remained operational and services were rapidly re-established under new branding, with no significant or lasting disruption.”
Krebs on Security – Read More

Welcome to this week’s edition of the Threat Source newsletter.
I took a two-week vacation (thanks to Bill for covering my author shift last week) and made the deliberate choice to leave my laptop behind. No emails, IMs, no IT at all. Thank you, European work culture! It was a complete break.
Well, almost.
The weather didn’t always cooperate, so instead of freezing on a beach, I found myself catching up on TV — mostly news and a few series. But wherever I clicked, I just couldn’t escape the daily dose of AI. What can we do about invasive mosquitos? Ask AI. Government doesn’t move the needle? Ask AI. Want the weather forecast? AI, obviously. There are countless ads with people asking AI whether or not to wear a jacket “because it might rain.” Even with your favorite TV shows, gone are the days when the hoodied hacker sits in front of a black terminal with green text running a dangerous (haha) ping or nmap. Now, they’re writing lines like, “Did you try breaking the firewall with our latest AI algorithm, bro?”
Coming back to work and catching up on our industry news, I almost expected AI to be dominating the headlines. But it wasn’t, and neither was ransomware. Instead, they were all about breaches. Many — but not all — reports referenced compromised OAuth tokens linked to Salesloft’s Drift integration, with a notable number of high-profile victims. Sure, this isn’t a scientific or qualitative analysis (ransomware isn’t disappearing anytime soon), but the reporting and the headlines have definitely shifted from one to the other.
Looking past the buzzwords and catchphrases, the headlines really boiled down to two main themes: supply chain and identity attacks. In a SaaS world, I think it’s time to rethink their definitions and priority levels.
Why? First, supply chain attacks aren’t limited to hardware or software anymore. We need to consider the datapath (or where data possibly is processed) as a key part of the supply chain.
Second, identity attacks don’t just target users; interconnected applications are increasingly at risk, too. I’m not saying we can ignore the users, especially with current reporting that it started with access through a GitHub account or software vulnerabilities in our “classic” applications, but we absolutely need to broaden our focus. Last week’s headlines made that clear.
Cisco Talos’ latest blog post details the Cyber Threat Intelligence Capability Maturity Model (CTI-CMM), a framework that helps organizations assess and enhance their cyber threat intelligence programs across 11 key domains. By outlining clear maturity levels and improvement cycles, CTI-CMM can help your team benchmark your current capabilities and develop a strategy for continuous (and practical) growth.
Understanding and improving your CTI program’s maturity can help your organization better anticipate, detect, and respond to cyber threats, no matter your budget or staffing level. It also makes the security investments you do have more effective, and ensure your team’s efforts are aligned with business priorities.
Check out the CTI-CMM framework to assess where your organization stands, identify gaps and opportunities, and create a roadmap to practical improvements for your organization.
Huge NPM supply chain attack goes out with whimper
A supply chain attack involving multiple NPM packages had the potential to be one of the most impactful security incidents in recent memory, but such fears seemingly have proved unrealized. (Dark Reading)
Swiss Re warns of rate deterioration in cyber insurance
Increased competition among insurers has led to a third consecutive year of reduced rates, according to the report, as the available supply of cyber coverage has exceeded current demand. (Cybersecurity Dive)
Critical SAP vulnerability actively exploited by hackers
A critical security flaw has been found in several SAP products, and could allow a malicious actor to gain administrator-level control. (HackRead)
No gains, just pains: 1.6M fitness phone call recordings exposed
Sensitive info from hundreds of thousands of gym customers and staff was left sitting in an unencrypted, non-password protected database. Audio recordings spanned from 2020 to 2025. (The Register)
US offers $10M reward for Ukrainian ransomware operator
Volodymyr Tymoshchuk allegedly hit hundreds of organizations with the LockerGoga, MegaCortex, and Nefilim ransomware families. According to an indictment, the intrusions caused hundreds of millions of dollars in losses. (Security Week)
China accuses Dior’s Shanghai branch of illegal data transfer
China’s public security authority alleges that Dior’s Shanghai branch has transferred customers’ personal data to its headquarters in France illegally, leading to a data leak in May. (Reuters)
SHA 256: 41f14d86bcaf8e949160ee2731802523e0c76fea87adf00ee7fe9567c3cec610
MD5: 85bbddc502f7b10871621fd460243fbc
VirusTotal: https://www.virustotal.com/gui/file/41f14d86bcaf8e949160ee2731802523e0c76fea87adf00ee7fe9567c3cec610/details
Typical Filename: N/A
Claimed Product: Self-extracting archive
Detection Name: Win.Worm.Bitmin-9847045-0
SHA 256: 9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507
MD5: 2915b3f8b703eb744fc54c81f4a9c67f
VirusTotal: https://www.virustotal.com/gui/file/9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507
Typical Filename: VID001.exe
Claimed Product: N/A
Detection Name: Win.Worm.Coinminer::1201
SHA 256: c67b03c0a91eaefffd2f2c79b5c26a2648b8d3c19a22cadf35453455ff08ead0
MD5: 8c69830a50fb85d8a794fa46643493b2
VirusTotal: https://www.virustotal.com/gui/file/c67b03c0a91eaefffd2f2c79b5c26a2648b8d3c19a22cadf35453455ff08ead0
Typical Filename: AAct.exe
Claimed Product: N/A
Detection Name: PUA.Win.Dropper.Generic::1201
Cisco Talos Blog – Read More