Efficient SOC: How to Detect and Solve Incidents Faster
SOCs face constant pressure. Heavy workloads, poor threat visibility, and disconnected tools introduce delays in detection and response, which may lead to financial loss and operational disruptions for the business.
ANY.RUN helps over 15K security teams to solve this challenge by empowering them to quickly detect, analyze, and understand threats, so they can respond faster and with confidence.
Here’s how your SOC can handle incidents efficiently and save up to 21 minutes per case.
Spot More Threats in Real Time
Many SOCs struggle with delayed detection due to static analysis tools and manual research that takes hours. By the time an attack is confirmed, it may have already spread across the network, increasing the cost and complexity of response.
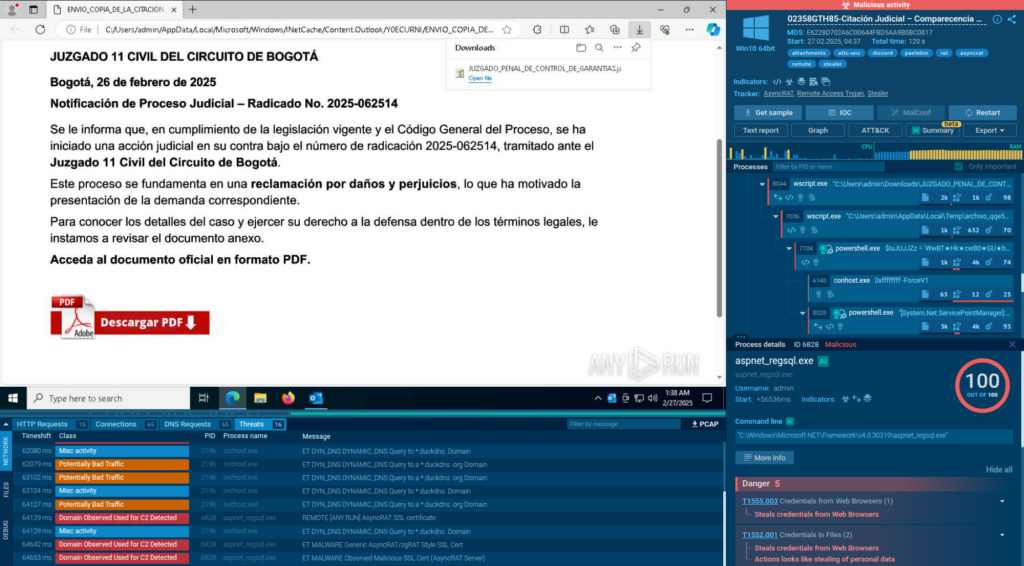
ANY.RUN’s Interactive Sandbox tackles this problem by providing a real-time virtual environment, allowing teams to observe malware behavior as it unfolds. Suspicious files, URLs, and scripts are detonated in cloud VMs, giving immediate insights into their actions, without risking production systems or waiting for the analysis to finish.
The result is fast knowledge of the threat and a clear understanding of the response steps needed to contain and mitigate it.
Results SOCs like yours achieve
- Faster MTTD: Get answers in minutes, not hours, with 88% of attacks visible within 60 seconds of analysis.
- Higher detection rate: See more with a 36% detection rate increase on average.
Identify Low-Detection Attacks with Speed and Ease
For cases with evasive threats, the sandbox equips SOC teams with the interactivity. It lets them identify attacks that beat the majority of standard detection systems by simulating user actions right inside the VM.
The common threats exposed with interactive analysis include:
- Multi-stage malware
- Payloads hidden in email attachments
- CAPTCHA-protected phishing pages
- Malicious links in QR codes
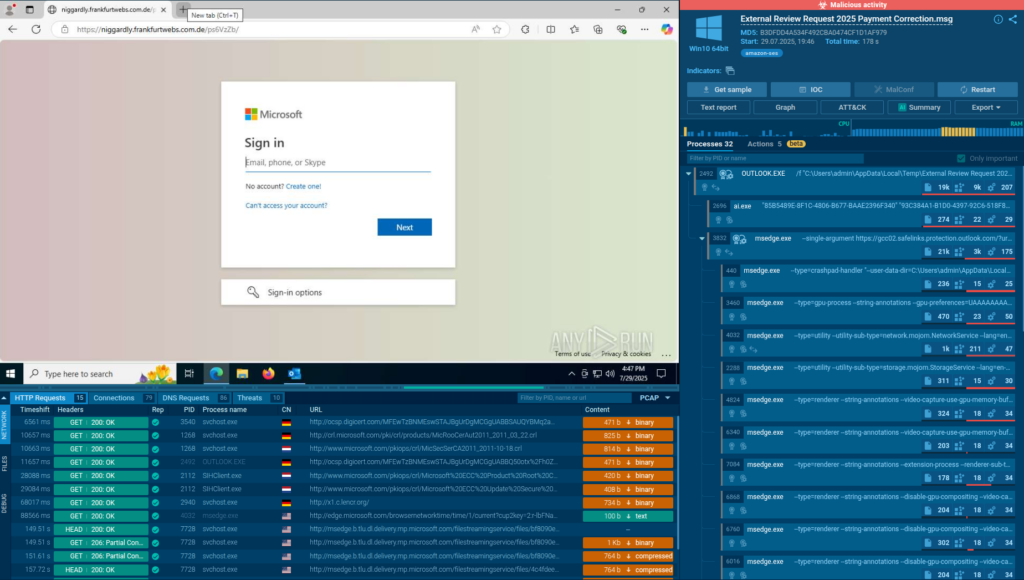
By opening, downloading, running, and performing other activities to trigger the attack chain, analysts can force threats to reveal themselves in seconds, cutting the time to the response stage.
Thanks to the ANY.RUN sandbox’s intuitive interface, most of the investigations can be done by junior analysts without assistance from senior professionals. This results in a continuous team-wide expertise growth and better decision-making.
Results SOCs like yours achieve
- Fewer missed threats: Find hidden attacks that most tools skip with up to 58% more threats identified overall.
- Efficient triage and response: Enable junior staff to handle more incidents on their own with 30% reduction in Tier 1 to Tier 2 escalations.
Automate Repetitive Work to Free Up Analysts
Alert fatigue ranks as number one challenge for SOC teams. It not only slows down response times but also increases the risk of human error, leaving gaps in defense.
ANY.RUN takes the brunt of the work off your team’s hands and automates critical aspects of threat analysis, including user simulations and malware detonation.
You get clear verdicts and actionable threat reports with IOCs and TTPs, enabling your team to make faster, more accurate decisions about the incident at hand.
Results SOCs like yours achieve
- No time wasted: Automation reduces manual effort, accelerating analysis and improving productivity across the team, with 94% of ANY.RUN users reporting faster triage.
- Lower costs: Save resources on routine tasks like checking suspicious files and URLs with 20% reduction in case load for Tier 1.
Connect Your Security Stack for Zero-Delay Workflow
Disconnected security tools create silos, forcing teams to lose time during switching between platforms and makes it harder to maintain a unified defense strategy.
ANY.RUN’s products: Interactive Sandbox, Threat Intelligence Lookup, and Threat Intelligence Feeds integrate seamlessly with popular TIPs, SIEMs, and SOAR platforms via API/SDK. These include Cortex XSOAR, QRadar SIEM & SOAR, OpenCTI, and others.
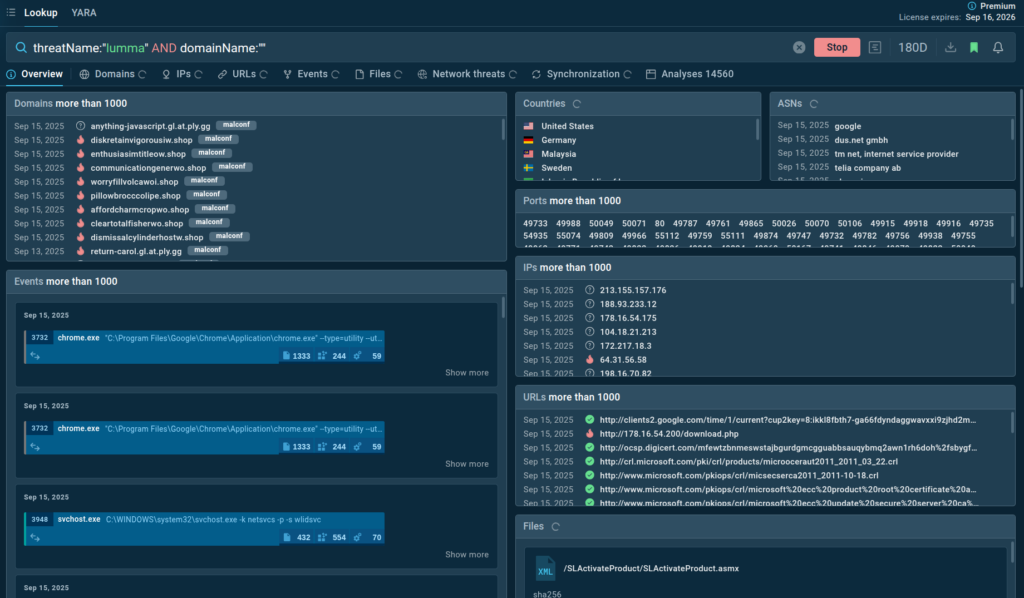
With a centralized incident control powered by ANY.RUN’s solutions, teams gain real-time alert enrichment, insights into threat behavior, and valuable context that guide containment and remediation efforts.
Results SOCs like yours achieve
- Productivity boost: With ANY.RUN’s products, teams reach up to 3x better performance, accelerating response times and fostering cross-team collaboration.
- Stronger security: Enrich proactive defense with 24x more IOCs using ANY.RUN’s TI solutions powered by data from 15K+ SOCs worldwide.
The Result: 21 Minutes Faster MTTR per Case
Organizations using ANY.RUN experience a unified, efficient workflow that cuts through noise and accelerates investigations. Real-time analysis, automation, and seamless integrations enable teams to reduce MTTR by 21 minutes per incident. This translates to:
- More threats handled with existing resources
- Faster alert triage and investigations
- Higher detection rates and wider threat coverage

For CISOs, the outcome is simpler, stronger security: fewer blind spots, lower costs, and a team equipped to stay ahead in an increasingly hostile threat landscape.
These results are evidenced by companies like Expertware, a leading IT consultancy and MSSP in the EU. With ANY.RUN, they achieved a 50% reduction in threat investigation and IOC extraction turnaround time.
By replacing time-consuming manual setups with interactive sandboxing, Expertware improved visibility into complex threats, streamlined collaboration across their SOC, and scaled operations without adding overhead.
About ANY.RUN
Designed to accelerate threat detection and improve response times, ANY.RUN equips teams with interactive malware analysis capabilities and real-time threat intelligence.
ANY.RUN’s cloud-based sandbox supports investigations across Windows, Linux, and Android environments. Combined with Threat Intelligence Lookup and Feeds, our solutions give security teams full behavioral visibility, context-rich IOCs, and automation-ready outputs, all with zero infrastructure overhead.
Ready to see how ANY.RUN’s services can power your SOC?
The post Efficient SOC: How to Detect and Solve Incidents Faster appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
