Nothing’s new earbuds have a feature I wish was on my AirPods Pro – and they’re cheaper
The Nothing Ear 3 promise upgrades all-around, but there’s one major feature that’s very unique, but also on-brand.
Latest news – Read More
The Nothing Ear 3 promise upgrades all-around, but there’s one major feature that’s very unique, but also on-brand.
Latest news – Read More
A 19-year-old and an 18-year-old have been arrested and charged in the hack of London’s transport agency in 2024 — an attack attributed to the Scattered Spider cybercrime collective.
The Record from Recorded Future News – Read More
Palo Alto, California, 18th September 2025, CyberNewsWire
Hackread – Latest Cybersecurity, Hacking News, Tech, AI & Crypto – Read More
RevengeHotels has been targeting hotels in Brazil and Spanish-speaking regions with VenomRAT implants in 2025.
The post Threat Actor Infests Hotels With New RAT appeared first on SecurityWeek.
SecurityWeek – Read More
Hackers are posing as Empire podcast hosts, tricking crypto influencers and developers with fake interview invites to deliver macOS AMOS Stealer malware.
Hackread – Latest Cybersecurity, Hacking News, Tech, AI & Crypto – Read More
The high-end jewelry retailer is informing customers in the United States and Canada that hackers accessed information related to gift cards.
The post Tiffany Data Breach Impacts Thousands of Customers appeared first on SecurityWeek.
SecurityWeek – Read More
Experienced gamers are well aware of the risks of downloading games, mods, skins, and other gaming software from unofficial sources. However, infections can also originate from platforms users typically trust — developer websites and official stores.
In this post, we review several cases where attackers distributed malware through official gaming resources. We also explain how to protect your system, loot, and account — so you can keep playing on your favorite platforms without any nasty surprises.
In July 2025, Endgame Gear, a manufacturer of advanced mice aimed at esports players and seasoned gamers, reported a malware infection in its OP1w 4k v2 mouse-config utility. The Trojan remained on the company’s official site for almost two weeks, from June 26 to July 9, 2025.
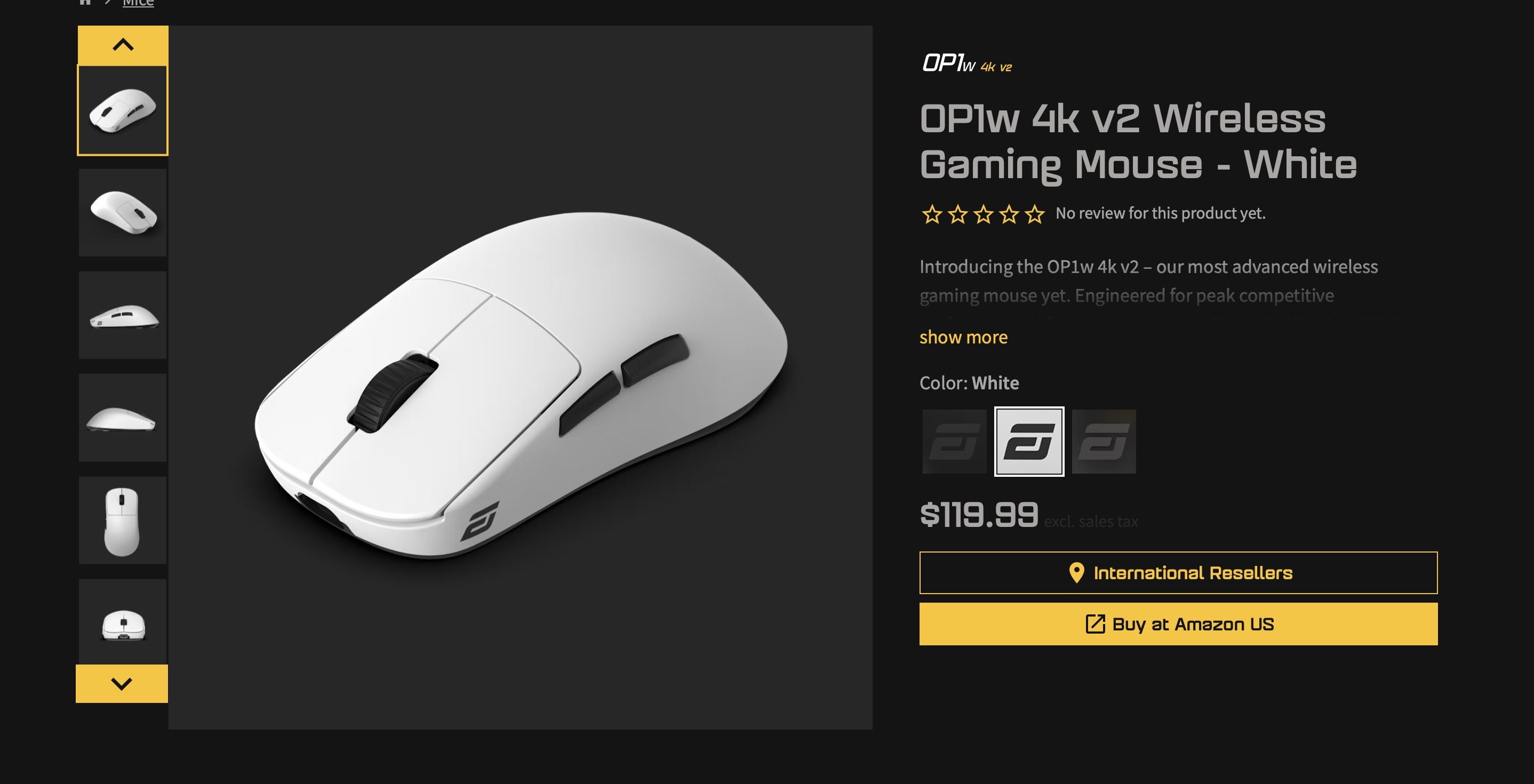
The official page for the Endgame Gear OP1w 4k v2 mouse hosted a malware-infected setup tool. Source
As a result, users who downloaded the utility from the product page during that period also received malware with it. Endgame Gear did not specify what the malicious payload was, but user-scan data suggests it was an XRed backdoor.
XRed offers a wide range of capabilities for remote control of infected systems. These include a keylogger and enables attackers to access the command line, browse disks and folders, download and delete files, and take screenshots. XRed can also download additional modules and exfiltrate system data to remote servers.
It was gamers themselves who first noticed something was wrong with the OP1w 4k v2 configuration tool. They began discussing suspicious signs on Reddit nearly two weeks before Endgame Gear released an official statement. The key details that raised user suspicions were the size of the program — the infected version was 2.8MB instead of the usual 2.3MB — and the file signature, listed as “Synaptics Pointing Device Driver” instead of “Endgame Gear OP1w 4k v2 Configuration Tool”.
In its official statement on the incident, Endgame Gear clarified that users who downloaded the tool from the general downloads page (endgamegear.com/downloads), GitHub, or the company’s Discord channel are safe. The threat only affected gamers who downloaded software directly from the OP1w 4k v2 product page between June 26 and July 9, 2025. After that, the malware was removed from the company’s site.
The mouse manufacturer recommends the following steps for any potentially affected users:
In addition, users should change passwords for all important accounts, including financial services, email, and work-related logins.
In 2025, several cases were reported of malware being distributed through early-access games on Steam.
All three cases involved early-access titles — likely because Steam applies looser verification procedures for pre-release games. Let’s take a closer look at these three cases.
A few days after the beta release of PirateFi — the first game developed by a studio called Seaworth Interactive — one user reported on a Steam forum that his antivirus had prevented the game from launching. The security software detected the presence of Trojan.Win32.Lazzzy.gen malware, which the game attempted to install in the AppData/Temp directory after launch.

PirateFi promised players a pirate-themed survival sim, but in reality it stole browser cookies to hijack accounts. Source
The Trojan’s primary goal was to steal browser cookies. These cookies allowed the attackers to access victims’ accounts for financial services, social networks, and other online platforms. Several players who downloaded and ran the game reported that the criminals changed the passwords on their accounts and stole funds. PirateFi was pulled from Steam just four days after release. All users who had downloaded the game — fortunately, only around 800 people — received an official notification from the platform warning them of the malware on their devices.
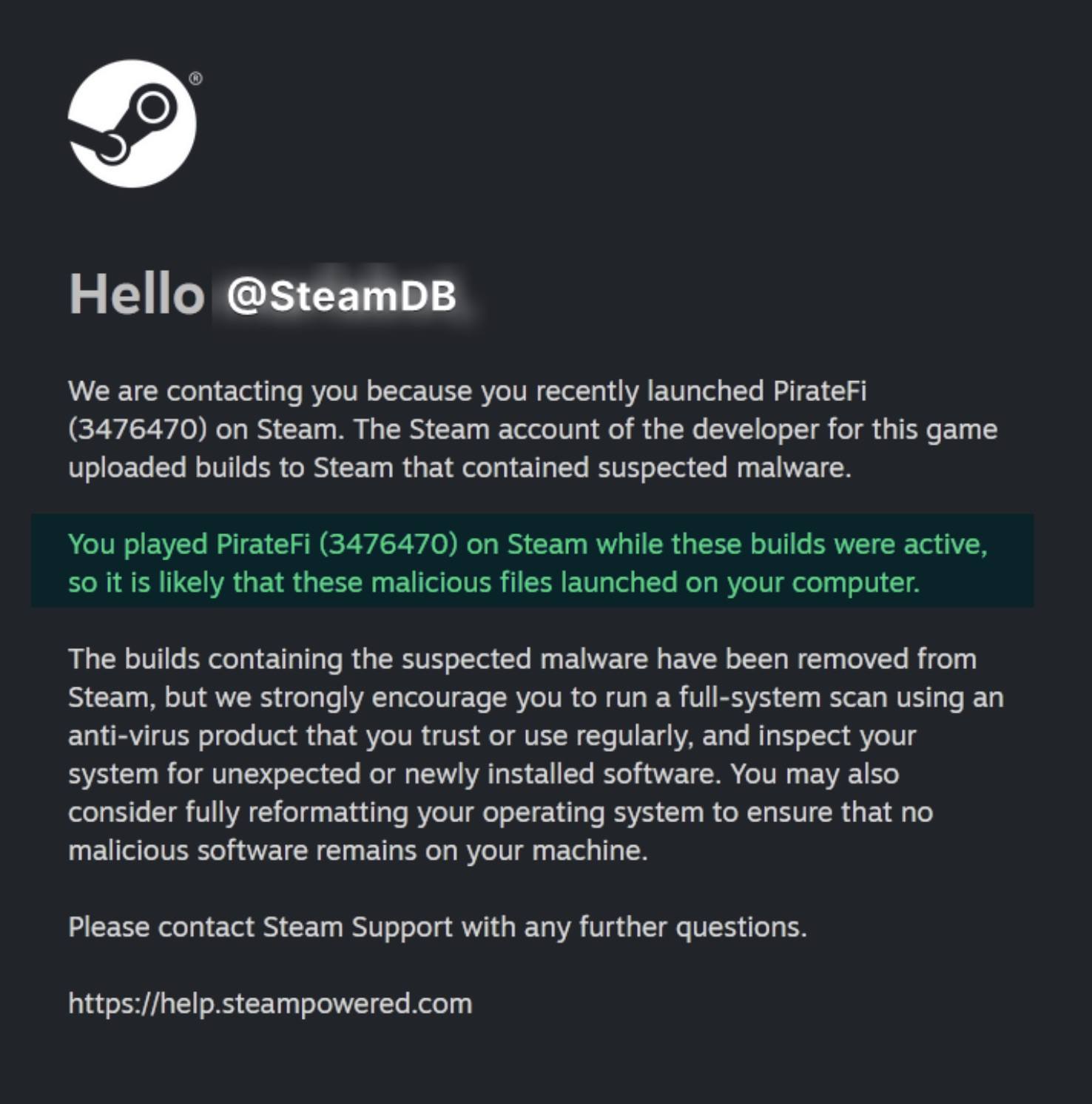
Steam users who downloaded the infected PirateFi game were warned of malware on their devices. Source
Just a month later, a similar situation occurred with another game — Sniper: Phantom’s Resolution by Sierra Six Studios. Once again, players were the first to suspect something was wrong: they noticed that the game’s description and screenshots were clearly copied from other projects. Another red flag was the developer’s offering a demo installer hosted on an external GitHub repository rather than through Steam.
Further examination of the installer’s code by Reddit users revealed suspicious software hidden inside. Like the creators of PirateFi, those behind Sniper: Phantom’s Resolution seemed to be after victims’ online accounts. Following user reports, both GitHub and Steam quickly removed the malicious game from their platforms.
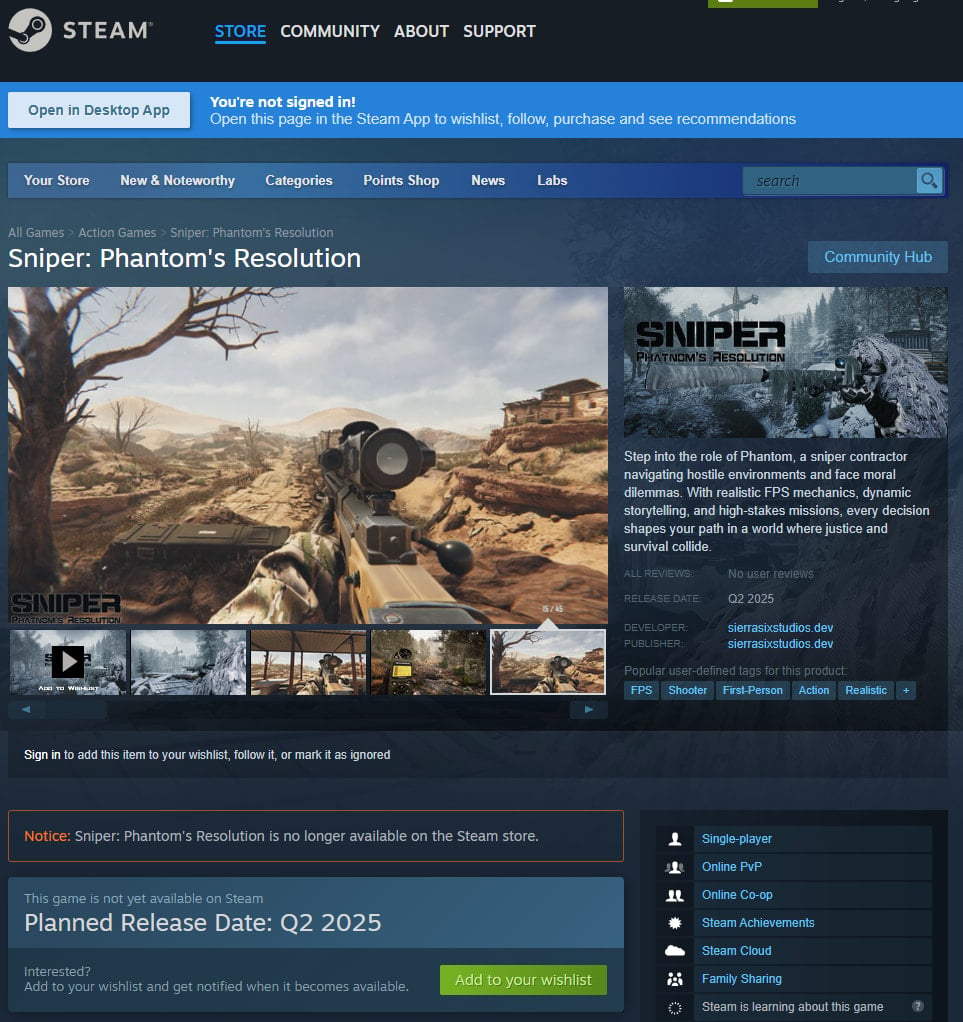
The game Sniper: Phantom’s Resolution was published on Steam with an installer containing malware, and was removed after user complaints. Source
The third case, involving a game called Chemia by Aether Forge Studios, was a little different: this time, it was a beta version of a legitimate game that was infected. Cybersecurity researchers believe the attack was carried out by the hacker group EncryptHub, also known as Larva-208.
It remains unclear how the attackers managed to inject malware into the game. However, players who launched the Chemia playtest unknowingly downloaded two infostealers to their devices. Both ran silently in the background without affecting gameplay, leaving gamers unaware their systems were compromised.
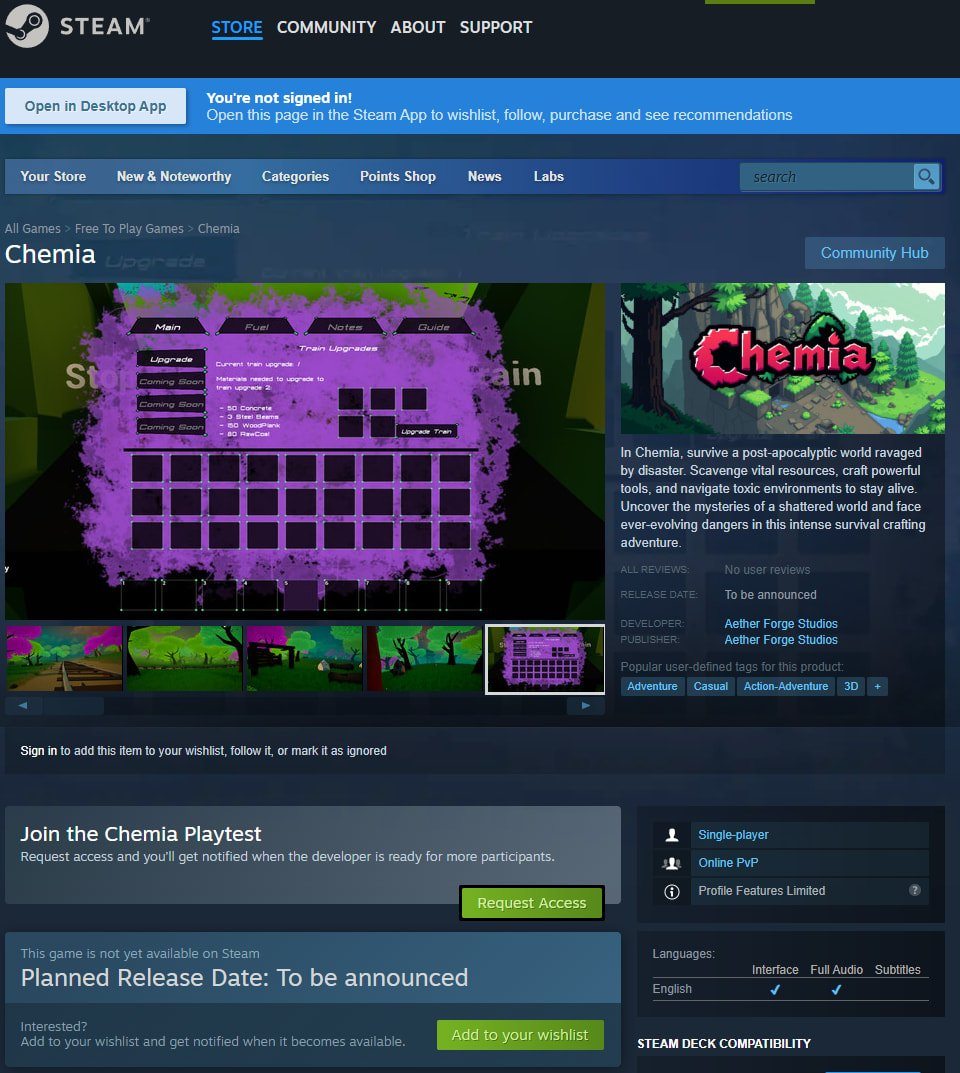
The Chemia playtest on Steam was distributed with infostealing malware that ran in the background, extracting data from browsers. Source
The attackers were targeting data stored in browsers, including saved passwords, autofill info, cookies, and cryptowallet details. At the time of writing, the game is no longer available on Steam. However, neither the platform nor the game’s developer has issued an official statement.
Sometimes dangers lurk not just on Steam, but also on developers’ official sites — including the biggest names. In 2018, about fifty thousand Minecraft players fell victim to attackers who uploaded malicious skins to the official Minecraft website. That platform has a fan-interaction system where any player can share skins they create with others — and that’s what the attackers exploited.

The Minecraft skins that could reformat hard drives and delete system programs. Source
The malware was spread via PNG skin files, and was capable of deleting programs, formatting hard drives, and destroying backup data. One peculiar detail was that some victims received bizarre messages with titles such as:
The malicious code’s specifics make experts believe that professional cybercriminals were likely not behind the attack. Still, the Minecraft case clearly demonstrated the vulnerability of content-sharing mechanisms on gaming platforms.
Installing games, mods, skins, and other gaming software from official sources is, of course, safer than pirating them from shady ones. However, as we’ve shown in this post, even legitimate sites require vigilance.
Many gamers may be skeptical about this last tip, as it’s a common belief in the gaming community that antivirus software slows down games. That may have been true years ago, but tests these days show that the latest security solutions cause no measurable drops in performance.
Moreover, Kaspersky Premium even includes a dedicated gaming mode. It turns on automatically when a game launches, postponing database updates, notifications, and routine scans until the session ends — thus minimizing system resource usage.
How else do attackers target gamers? Check out our selection of articles on this topic:
Kaspersky official blog – Read More
In the current cycle, Bitcoin has anchored most of the capital inflow. In 2025, 66% of investors selected…
Hackread – Latest Cybersecurity, Hacking News, Tech, AI & Crypto – Read More
Scammers are now using “SMS blasters” to send out up to 100,000 texts per hour to phones that are tricked into thinking the devices are cell towers. Your wireless carrier is powerless to stop them.
Security Latest – Read More

Welcome to another episode of Humans of Talos, our ongoing video interview series that celebrates the people powering Cisco’s threat intelligence efforts. In each episode, we dive deep into the personal journeys, motivations and lessons learned from the team members who help keep the internet safe.
This time, we sit down with Alex Ryan, a seasoned Incident Commander from Cisco Talos Incident Response. Read (or watch) on to hear her candid reflections on the emotional intensity of incident response, the critical role of a supportive team in preventing burnout, and invaluable advice for aspiring cybersecurity professionals.
Amy Ciminnisi: Alex, you were recently on the Beers with Talos podcast, and during that, we learned that you have two liberal arts degrees, but you found yourself really loving how machines and systems worked, and then you work your way through the cybersecurity ranks. I’d love to know: What brought you to Talos?
Alex Ryan: During my career inside companies doing incident response, vulnerability management, and risk management, Talos Intelligence was often one of my sources. I often looked at intelligence from vendors who were using their own datasets to generate the finished intelligence, rather than those who just took whatever intelligence was already out there, re-mashed it, and enriched it a bit. I have a lot of respect for Talos from using them as a source for guiding how I would do incident response and prioritize my defenses and things like that. When the opportunity came up to join Cisco Talos Incident Response as an Incident Commander, it was that reputation (and having used their material for so long which showed that there was really good quality people and research being done) that put this job at the top of my list of choices.
AC: You have a very difficult job as an Incident Commander, acting as the point person in situations where people are possibly going through the worst days of their careers. What’s something about your day-to-day role that people might be surprised by or interested in?
AR: Incident response is a very high pressure situation to be in. You need to exude quiet confidence and build a trust relationships quickly with your customer. But on the back end, things can be chaotic: trying to get access to machines, trying to find the right machines. “Do we have the right IOCs?” “What is this thing? Let me reverse engineer it.” Trying to distill all of that activity into larger topics and give progress to the customer on it is critical.
It’s also high risk for the business being impacted. I think that there was a statistic at one point that about 70% of small to medium businesses that paid the ransom after being compromised went out of business within a year, because the ransom was such a financial hit that they just couldn’t absorb that kind of impact. So while the customer is trying to not freak out, I’m trying to exude quiet confidence while managing the forensics analysis activity. Trying to balance all of that is quite difficult, so incident response has a very high burnout rate.
After I came back from raising my children, it took me about two years to detox completely from incident response. I was really high strung, and I had no chill. Zero chill. I had to learn how to say no and how to prioritize my family over this hero complex that I was having at work. I would say I’m a much more well-rounded person now, and perhaps I’m better at my job because of that.
Want to see more? Watch the full interview, and don’t forget to subscribe to our YouTube channel for future episodes of Humans of Talos!
Cisco Talos Blog – Read More