What is security hardening? | Kaspersky official blog
The past several years have seen a number of positive developments in global cybersecurity, with organizations worldwide making significant investments to bolster their defenses against cyberthreats. More sophisticated solutions, more guidelines available, and a more collaborative cybersecurity environment have all contributed toward a digital landscape enhancement. Yet, against the backdrop of these encouraging developments, a disparity in cyber-resilience between small and large organizations has been widening.
According to a recent World Economic Forum report, larger organizations are showing steady progress in improving their cyber-defenses, but their smaller counterparts are struggling to keep up. While many larger enterprises are equipped with cutting-edge security solutions and dedicated personnel, SMBs often lack the necessary resources, resulting in a yawning gap in their cyber-resilience. Given the context, small businesses have to use every opportunity to mitigate potential cybersecurity risks without extra resources, and that’s where security hardening can turn the tide and help avert potential threats by basically configuring organizations’ systems and networks in the right way.
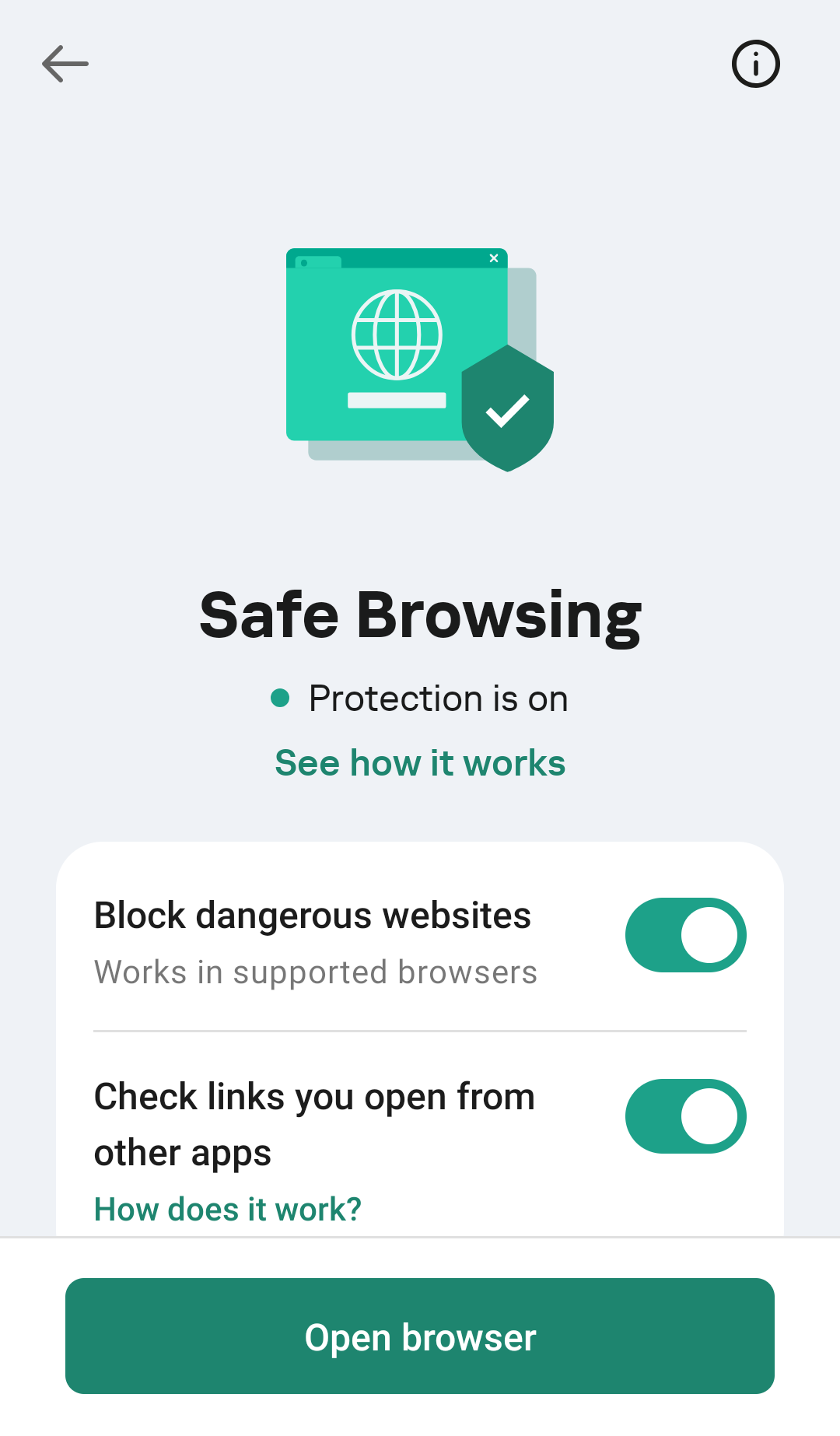
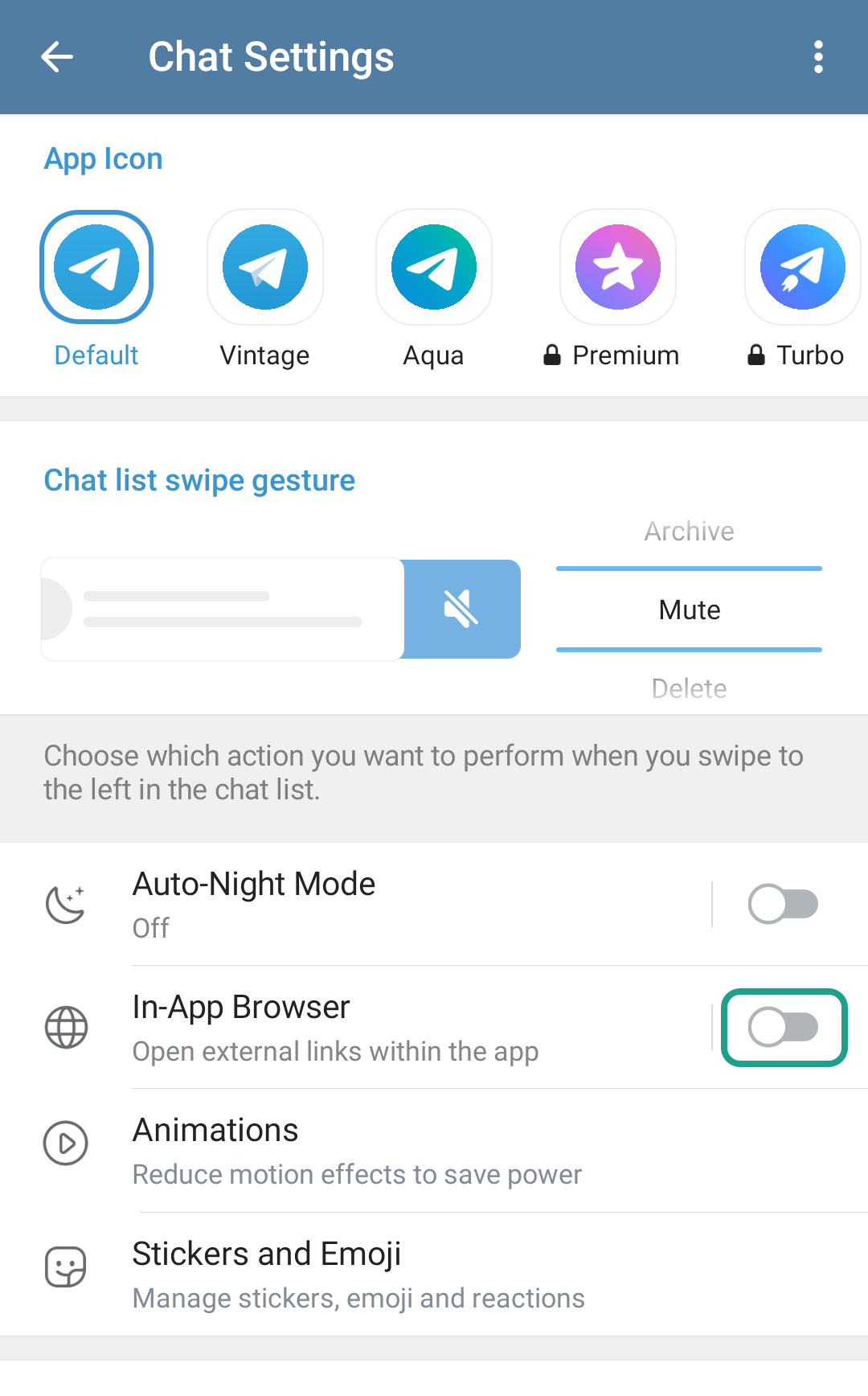
So what is security hardening? Security hardening is shorthand for a range of techniques and procedures that help protect digital infrastructure by reducing an attack surface — essentially turning the security of existing systems up to the maximum without necessarily resorting to extra protection solutions. In this article, we explore some of the must-have strategies that can help organizations — especially those with limited or no dedicated cybersecurity resources — to reduce exposure to potential attacks.
Implementing strong authentication and authorization
The first fundamental is taking steps to reduce the risk of unauthorized access to a company’s systems and data. This requires the enforcement of a strict password policy that defines password length requirements, allowed characters, prohibited combinations, password expiration interval, etc. It should also include recommendations on the password storage method to rule out unsafe practices.
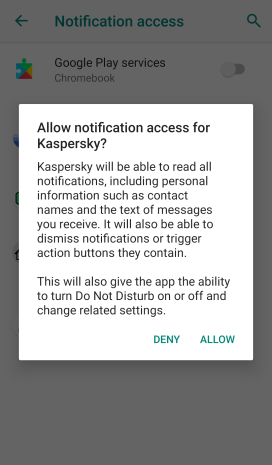
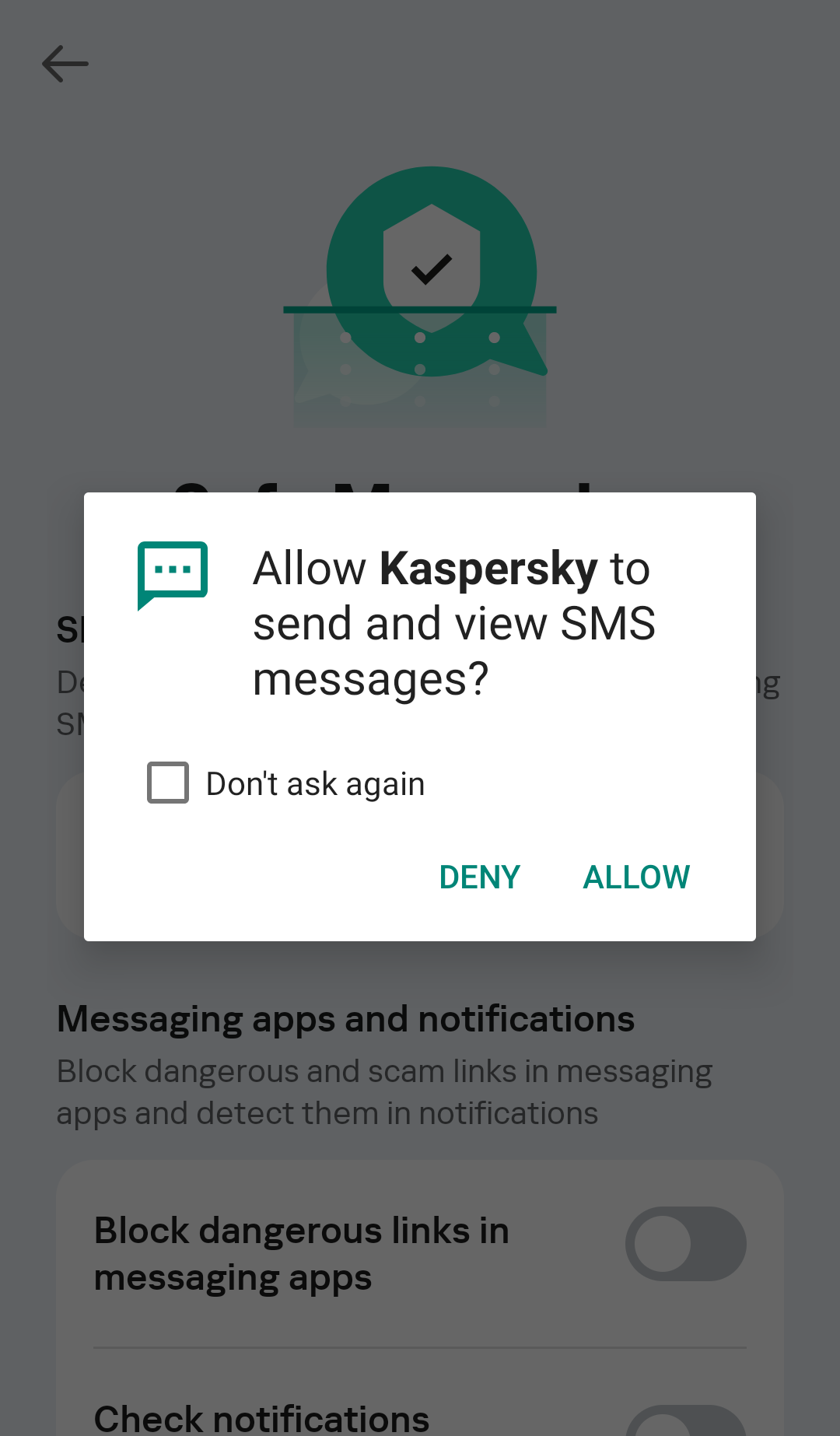
Another indispensable practice is the use of two-factor authentication, meaning that to access specific resources or data an employee has to verify their identity in two different ways. With two-factor authentication in place, even if attackers learn an employee’s password somehow, they still need to bypass the second factor, which gives an extra layer of protection.
And finally, organizations need to implement network access control measures to control users that enter the corporate network and also the level of access of these users. Configuring permissions within a corporate network following the least-privilege principle is a best practice, ensuring that users only have access to the systems needed to perform their tasks, and don’t have access to the entire environment. In an environment where employees have access only to the systems that they strictly need, in case of a potential breach attackers would have limited options for lateral movement within the network, which would minimize potential damage. Another useful tip is to regularly audit all accounts and their permissions, and revoking unnecessary ones – in case an employee is dismissed or moves to a different department.
Regularly updating software and timely patching vulnerabilities
Regular and prompt updates of operating systems, applications, and other software can help eliminate known vulnerabilities that can be used by attackers to compromise organizations’ networks. Software development is continually advancing, leading to two main challenges: a system can rapidly become outdated or even obsolete, and, more critically, it may become vulnerable to cyberattacks. Software developers address these issues by implementing new code distributed as part of updates. Software updates not only fix bugs or improve performance, but also might include patches of vulnerabilities detected during software operation. Сybercriminals never fail to grab the opportunity to exploit known vulnerabilities, with some of them exploited for years, which exposes the fact that years after the release of patches some organizations fail to install them.
Encrypting data
Encryption of data at rest (when data is stored, for example, on drives) as well as in transit (when data is moving between devices, such as within private networks or over the internet), protects the data from interception and unauthorized access. The two most effective data protection technologies are File and Folder Level Encryption (FLE) and Full Disk Encryption (FDE), which are used for tackling different tasks. The former protects critical data and restricts access to it, while the latter rules out the possibility of any data falling into the hands of third parties — even if a data storage device holding valuable information is lost or stolen.
Both FLE and FDE can be implemented on corporate computers with the help of built-in tools:
- BitLocker (Windows) or FileVault (macOS) for FDE.
- Encrypting File System (EFS) (Windows) or Disk Utility and FileVault (macOS) for FLE.
With data encryption in place, organizations can minimize the risk of confidential data being intercepted.
Implementation of backups and data backups
Backing up data is essential to ensure its integrity in case of a potential cyberattack, including with the use of ransomware or wipers. To guarantee a continuous backup process, one can schedule automatic backups to avoid time-wasting, with manual backups nevertheless still being an option.
When the process itself is set up, it’s necessary to check the integrity of backups regularly and perform practice runs resurrecting the server in a staging environment, and generally to make sure that if it becomes necessary, recovery will be possible. It should be noted that if a backup server is located inside the network perimeter, then in case of a potential attack, the backup will also be at risk of being destroyed by attackers. Therefore, it’s recommended to create several backups of critical data and diversify its storage, not neglecting data storage on physical devices. With data encryption in place, the risks of critical data loss and subsequent disruption of business processes are reduced.
Employee training
Last but not least, organizations have to adopt a systematic approach to cyber-education, carrying out regular assessments of the level of the cyber-literacy among staff, and implementing training to fill gaps in employees’ knowledge — making cybersecurity training a continual effort. Such training should include the basics of information security, best practices for data management, as well as typical attack scenarios used by cybercriminals — in particular social engineering techniques. Additionally, organizations can incorporate simulated phishing exercises to assess and reinforce both learning and monitoring employees’ proficiency from time to time to identify gaps in cyber-knowledge.
With nearly two-thirds of cyber-incidents caused by a human error, ongoing work to raise staff’s awareness of existing threats can help minimize the risks of attacks that exploit the human factor.
Altogether, the hardening techniques described above represent a strategy for reducing an organization’s attack surface. By implementing these security measures — ideally, together with the deployment of intrusion detection and prevention systems and installation of endpoint protection solutions — organizations can significantly minimize potential vulnerabilities. With this proactive approach, organizations can strengthen defenses against cyberthreats and also minimize risks of unauthorized access to their networks and systems.
Kaspersky official blog – Read More