Your Roku devices are getting a big, free upgrade – including AI Voice
Enhancements are coming to Roku City screensaver, Roku Voice, Live TV Channels, the mobile app, and headphone mode. There’s also a new smart projector.
Latest news – Read More
Enhancements are coming to Roku City screensaver, Roku Voice, Live TV Channels, the mobile app, and headphone mode. There’s also a new smart projector.
Latest news – Read More
New York, USA, New York, 15th October 2025, CyberNewsWire
Hackread – Latest Cybersecurity, Hacking News, Tech, AI & Crypto – Read More
Once you start using QuickDAV, you’ll find this simple app indispensable for easy file transfers from any OS to Linux.
Latest news – Read More
Cybersecurity firm Sublime Security details a new credential phishing scam impersonating Google Careers to steal login details from Google Workspace and Microsoft 365 users.
Hackread – Latest Cybersecurity, Hacking News, Tech, AI & Crypto – Read More
Cybersecurity is not just about defense, it is about protecting profits. Organizations without modern threat intelligence (TI) face escalating breach costs, wasted resources, and operational inefficiencies that hit the bottom line.
Here is how actionable intel can help businesses cut costs, optimize workflows, and neutralize risks before they escalate.
When SOC analysts lack high-fidelity, context-rich threat intelligence, they are forced to manually investigate thousands of alerts, many of which turn out to be false positives. This relentless cycle wastes time, drains budgets, increases turnover, and leaves critical threats unaddressed.
Without automation and precise data, teams operate in a constant state of reactive chaos, where even minor incidents consume disproportionate resources.
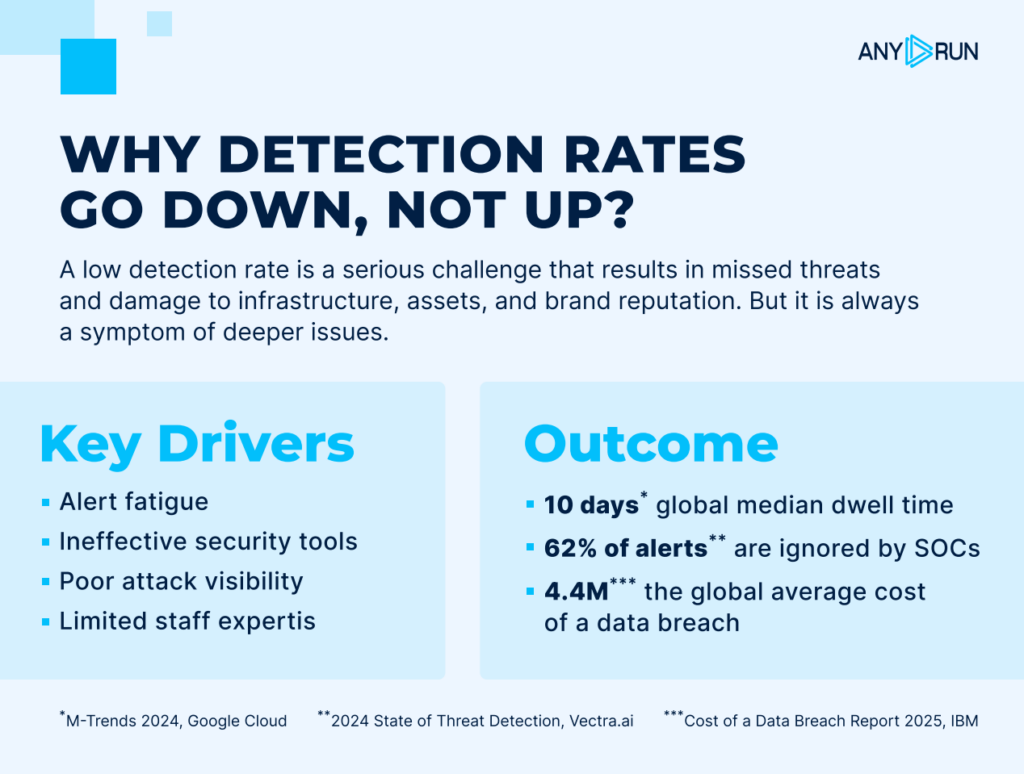
Cyberattacks exploit gaps in visibility and slow response times. Organizations relying on outdated or generic TI feeds often miss targeted, evasive threats until it is too late. By the time a breach is detected, the damage in terms of downtime, regulatory fines, and lost customer trust has already begun. The financial effects of a single incident can cripple budgets and erode market position for years.
Regulatory bodies do not accept “we didn’t see it coming” as an excuse. Without real-time, comprehensive TI, organizations struggle to detect, document, and mitigate threats in ways that satisfy auditors. The result is hefty fines, legal battles, and mandatory security overhauls that could have been avoided with proactive intelligence.
The financial impact of a cyberattack extends far beyond the immediate incident. Downtime, regulatory penalties, and reputational harm can accumulate into millions in losses even for a single event. Most organizations do not realize how many attacks slip through their defenses until it’s too late. The difference between a near-miss and a full-blown crisis often comes down to how quickly and accurately threats are identified.
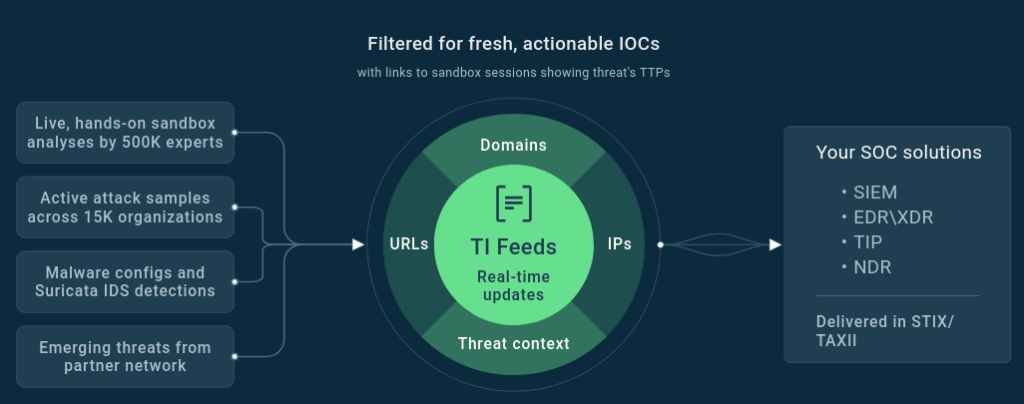
ANY.RUN’s Threat Intelligence Feeds provide actionable, real-time intelligence needed to block threats at the earliest stage. Instead of reacting to breaches after the fact, teams can neutralize risks before they execute, turning potential disasters into routine intercepts.
How ANY.RUN Helps:
SOC teams are overwhelmed by alert fatigue, with analysts spending hours each day chasing down irrelevant or duplicate threats. This becomes both a productivity issue and a financial drain, as organizations pay for overtime, burnout, and unnecessary tooling that does not address real risks. The problem compounds when teams lack the context to prioritize threats effectively, leading to misallocated resources and missed critical alerts.
ANY.RUN’s solutions filter out the noise, ensuring teams focus only on verified, high-impact threats. This shift saves time and redirects budgets from wasteful investigations to proactive and fast incident handling.
How ANY.RUN Helps:
Manual threat triage is one of the biggest hidden expenses in cybersecurity. Analysts stuck in repetitive, low-value tasks burn out and cost more in overtime and turnover. Delayed responses increase breach risks and force costly retraining.
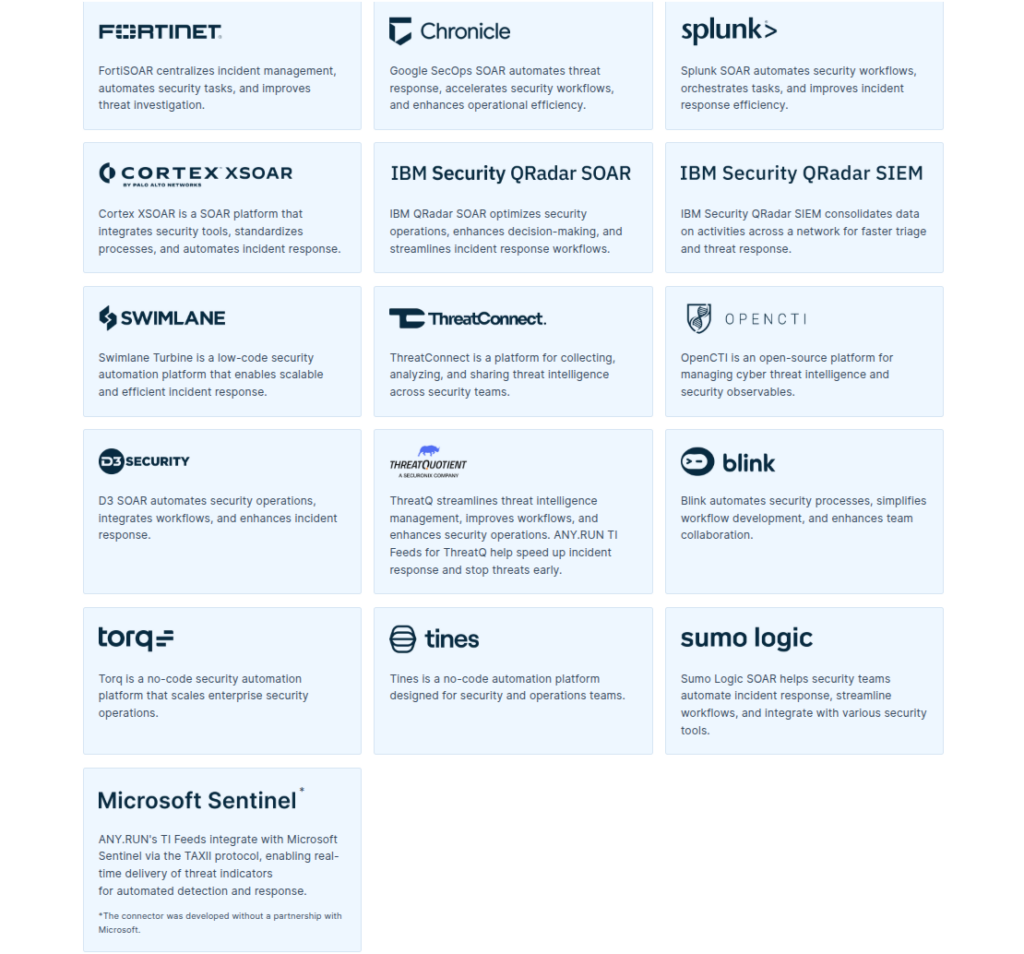
Thanks to plug-and-play integrations and API/SDK support, ANY.RUN’s TI solutions connect seamlessly with SOCs’ current software and enhance existing workflows. This reduces unnecessary escalations from Tier 1 to Tier 2 analysts, cutting labor costs and increasing the alert handling capacity without extra hiring.
How ANY.RUN Helps:
Every minute counts during a cyber incident. Slow detection and response prolong downtime and amplify financial losses, from regulatory fines to customer churn. Organizations without real-time, context-rich TI often struggle to collect actionable insights, delaying critical decisions and letting attacks spread unchecked.
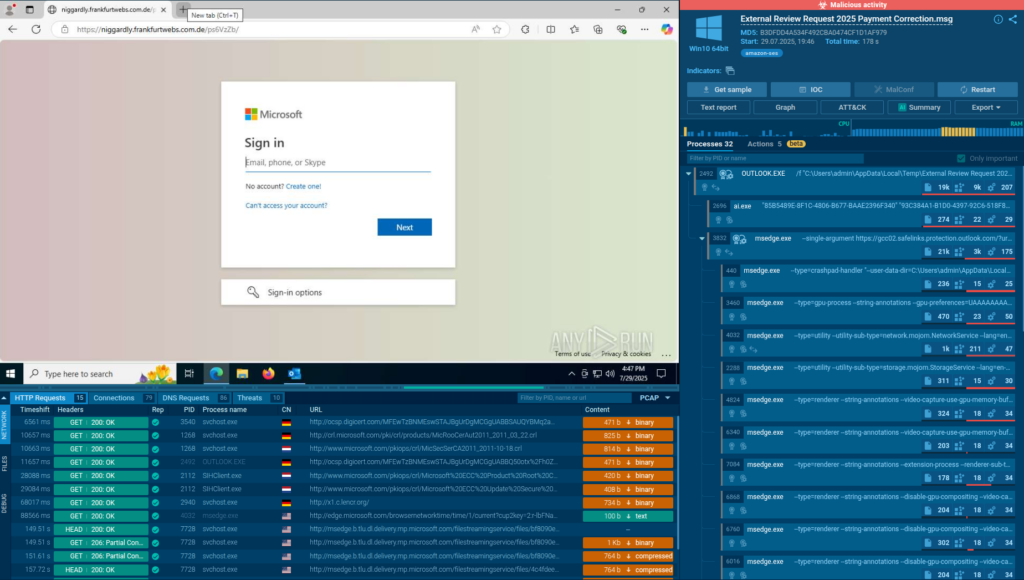
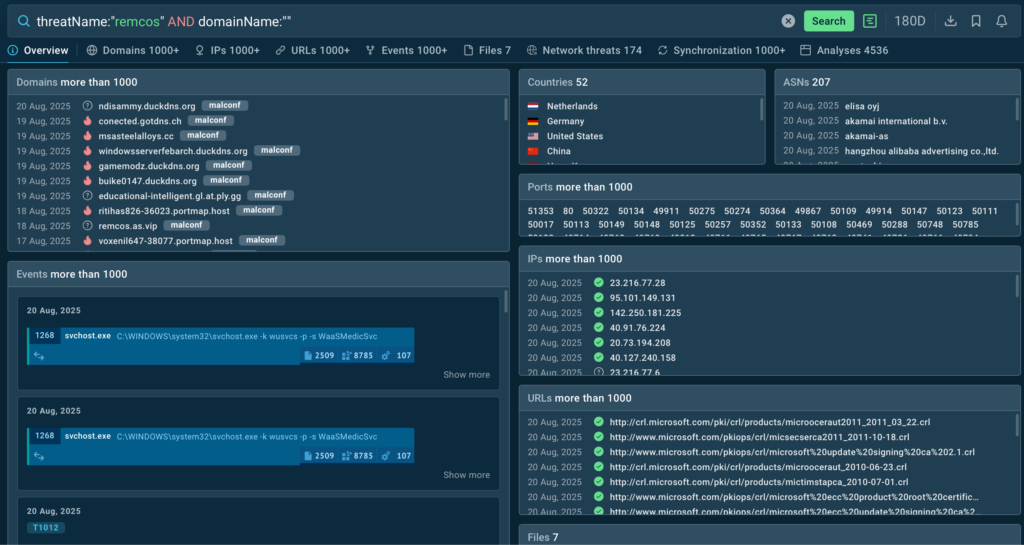
ANY.RUN’s TI Lookup provides instant, deep context, including a full attack view based on a single indicator, so teams can quickly understand the threat they are dealing with and respond decisively without guesswork. Faster responses limit damage, preserve revenue, and protect customer trust, turning potential crises into manageable events.
How ANY.RUN Helps:
Cyber threats evolve daily, but most TI feeds update weekly or monthly, leaving gaps that attackers exploit. Organizations stuck with static, generic IOCs are forced into reactive, costly fixes every time a new attack emerges. This approach poses a direct financial risk, increasing the likelihood of malware slipping through outdated defenses.
ANY.RUN’s TI Feeds update continuously with data from live investigations by 500,000 security analysts, ensuring defenses adapt automatically to new threats. TI Lookup’s MITRE ATT&CK integration helps teams anticipate attacker moves, turning security from a cost center into a strategic advantage.
How ANY.RUN Helps:
A transportation company faced constant cyber threats, especially through email phishing and malware attacks. Attackers frequently changed their infrastructure, making it hard to track and block threats in time. The security team struggled to manually monitor evolving attacks, which risked exposing sensitive communications and disrupting operations.
The company used ANY.RUN’s Threat Intelligence Lookup to automate threat tracking. They set up custom search queries for specific threats like geo-targeted attacks, CVEs, and phishing domains and subscribed to real-time updates. This allowed them to focus on active threats, convert new threat data into detection rules, and respond faster without manual searches.
Threat intelligence solutions like ANY.RUN’s TI Feeds and TI Lookup both improve security and deliver measurable cost savings, resource optimization, and risk reduction. By automating triage, eliminating false positives, and accelerating response, businesses can:
ANY.RUN is built to help security teams detect threats faster and respond with greater confidence. Our Interactive Sandbox delivers real-time malware analysis and threat intelligence, giving analysts the clarity they need when it matters most.
With support for Windows, Linux, and Android environments, our cloud-based sandbox enables deep behavioral analysis without the need for complex setup. Paired with Threat Intelligence Lookup and TI Feeds, ANY.RUN provides rich context, actionable IOCs, and automation-ready outputs, all with zero infrastructure burden.
The post 5 Ways Threat Intelligence Saves Businesses Money and Resources appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
According to a new report by cybersecurity firm Symantec, the hackers gained access to the Russian company’s software build and code-repository systems between January and May 2025 — suggesting the breach may have been an attempted software supply-chain attack aimed at the firm’s customers.
The Record from Recorded Future News – Read More
As problems with household water become more detectable and prevalent, many are moving beyond just handheld filters for drinking water.
Latest news – Read More
DT Research’s 323MD rugged tablet has an anti-microbial keyboard and IP65 water and dust resistance.
Latest news – Read More
National Cyber Security Centre reckons the rise is due to the UK’s increasing dependence on digital systems and a sharp increase in ransomware activity.
The post ‘A Call to Arms’ as UK Faces 50% Surge in Major Cyberattacks appeared first on TechRepublic.
Security Archives – TechRepublic – Read More
Fortinet and Ivanti have announced their October 2025 Patch Tuesday updates, which patch many vulnerabilities across their products.
The post High-Severity Vulnerabilities Patched by Fortinet and Ivanti appeared first on SecurityWeek.
SecurityWeek – Read More