Photoshop’s biggest AI update yet just dropped – how to try all the new tools
Adobe has brought conversational editing and a host of other AI features to Photoshop. Here’s what’s new.
Latest news – Read More
Adobe has brought conversational editing and a host of other AI features to Photoshop. Here’s what’s new.
Latest news – Read More
Adobe’s new AI image model and Prompt to Edit tool aim to eliminate the pain of complex photo-editing tasks.
Latest news – Read More
Data allegedly stolen from the companies has been made available for download on the Cl0p ransomware leak website.
The post Industrial Giants Schneider Electric and Emerson Named as Victims of Oracle Hack appeared first on SecurityWeek.
SecurityWeek – Read More
Mass exploitation attacks are once again targeting WordPress websites, this time through serious vulnerabilities in two popular plugins,…
Hackread – Cybersecurity News, Data Breaches, Tech, AI, Crypto and More – Read More
The New Reality for Lean Security Teams
If you’re the first security or IT hire at a fast-growing startup, you’ve likely inherited a mandate that’s both simple and maddeningly complex: secure the business without slowing it down.
Most organizations using Google Workspace start with an environment built for collaboration, not resilience. Shared drives, permissive settings, and constant
The Hacker News – Read More
Walmart just revealed some of the Black Friday deals you’ll find this season. Here are the best ones live now on TVs, headphones, and more, and what’s coming.
Latest news – Read More
The zero-day exploitation of a now-patched security flaw in Google Chrome led to the distribution of an espionage-related tool from Italian information technology and services provider Memento Labs, according to new findings from Kaspersky.
The vulnerability in question is CVE-2025-2783 (CVSS score: 8.3), a case of sandbox escape which the company disclosed in March 2025 as having come under
The Hacker News – Read More
No SOC is perfect, but it’s possible to overcome frequent shortcomings and achieve measurable results by introducing one essential component of modern cybersecurity operations: threat intelligence.
Organizations using ANY.RUN’s TI solutions report the following results:
Quality, real-time threat intelligence helps SOCs tackle their toughest challenges. More on that below.
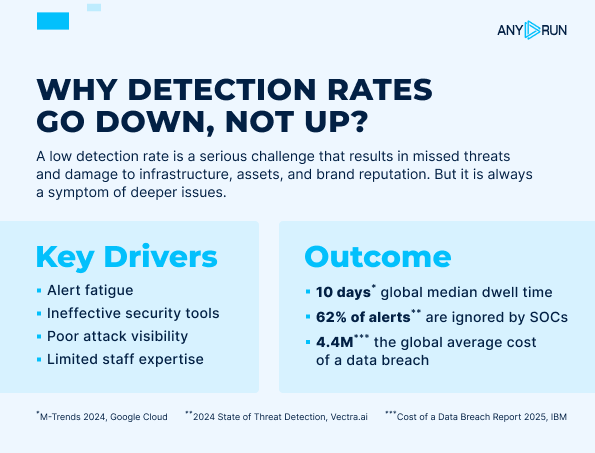
As attackers continuously refine their evasion tactics, low detection rates remain a key challenge for SOC teams. When even one missed threat can quickly escalate into serious operational and reputational risks, businesses can’t afford to overlook this metric.
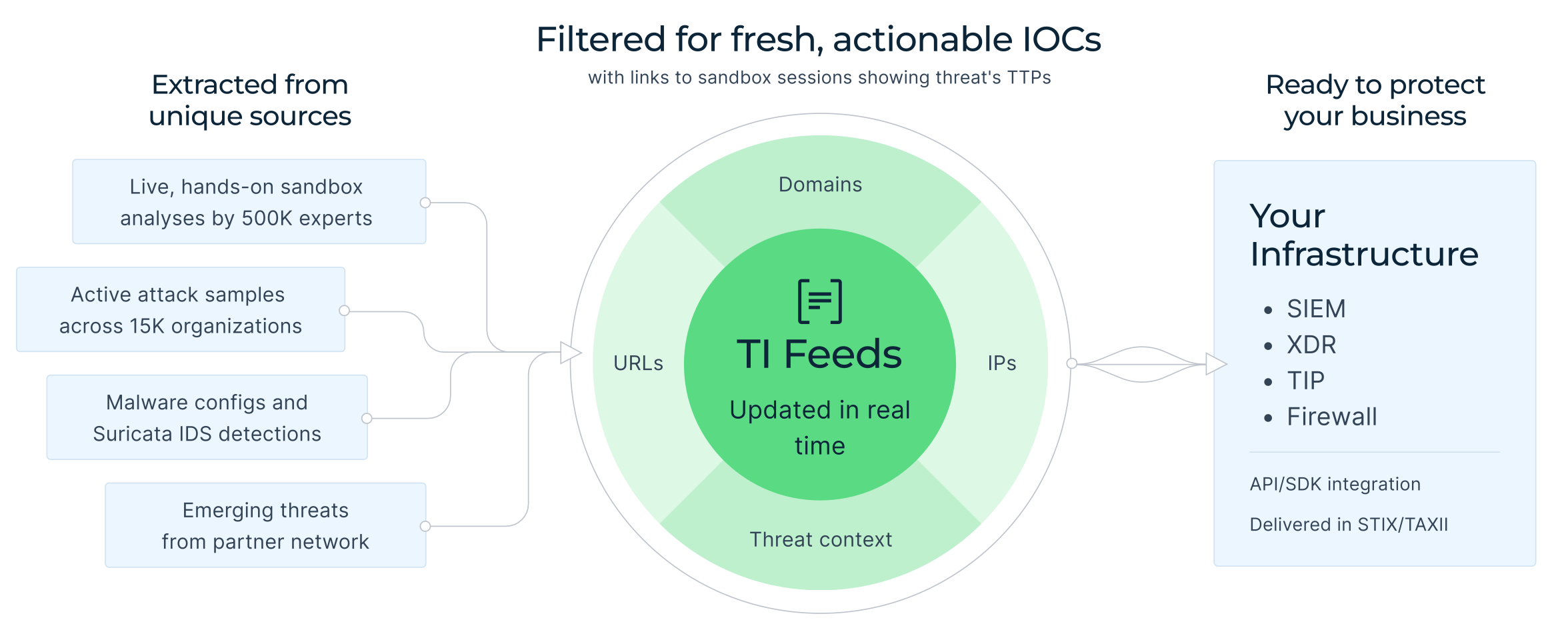
Solution: Threat intelligence is a powerful driver for early detection. This alone can radically boost your performance rates. How? Through expanded threat coverage, which is the key mission of Threat Intelligence Feeds.

By aggregating live attack data from 15,000+ organizations across industries and counties, TI Feeds highlights which malware is targeting real business right now. The result is 99% unique network IOCs that do not overlap with other sources and get carefully filtered to avoid false positives.
For your business, this means a wide, in-depth, and relevant visibility into the latest threats. That’s what drives the SOC team’s detections up and helps you remain one step ahead of attackers, mitigating the risk of costly disruptions.
Outcome:
The underlying reasons behind slow incident response often include a lack of automation and alert prioritization. But when incidents miss context, even the most efficient workflow might stall. Timely reaction becomes impossible when analysts have to go through disconnected alerts and bare IOCs.

Solution: Threat intelligence fueled with live context from ongoing malware investigations allows you to detect threats early on and cut response time dramatically. Each indicator from TI Feeds has a detailed sandbox report behind it. With it, you can see how malware behaves, what processes it affects, and what related IOCs there are.
Outcome:
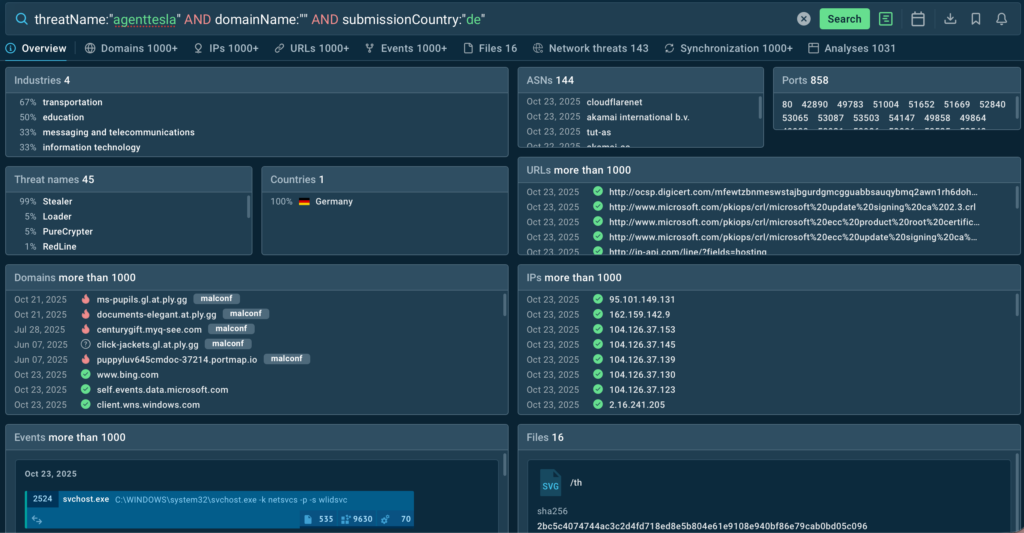
SOC teams must face massive amounts of data, and each unprocessed item awaiting manual investigation is a potential risk. That is why there’s a demand for solutions that work fast and support automated workflows.
Solution: Efficient TI solutions clear backlogs quickly and ensure that no threat is overlooked, including evasive or hidden threats that might act without showing themselves for months, leading to a system-wide disruption.
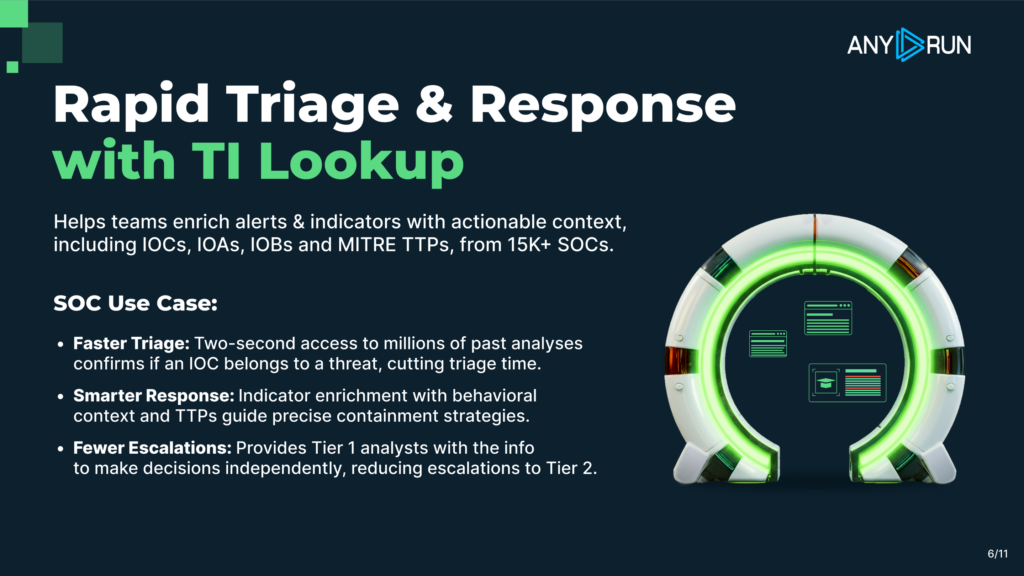
All it takes is one query to investigate a suspicious sample in Threat Intelligence Lookup to learn instantly if it poses danger. When the solution is integrated into your technology stack, this process becomes even smoother and can be scaled up without extra resources.
Outcome:
The human factor has a major impact on cybersecurity. Endless alerts lead to lower productivity of analysts. False positives and lack of ready-to-use threat data cause alert fatigue, a phenomenon that can snowball into serious compromise risks.
Solution: ANY.RUN delivers clean, reliable threat intelligence retrieved directly from malware analysts, not from third-party sources. This means that every IOC is verified and supplied in real time, allowing to decrease escalations between tiers and empower analysts to conduct proactive hunting and research.
Outcome:
Enterprises often hesitate to adopt new solutions in fear that they might disrupt the established workflow and demand major changes in current operations.
Solution: It’s key to consider the possibility of smooth integration that leaves you with a unified, sustainable defense system rather than several standalone services. Threat intelligence should strengthen your ecosystem, not conflict with it.
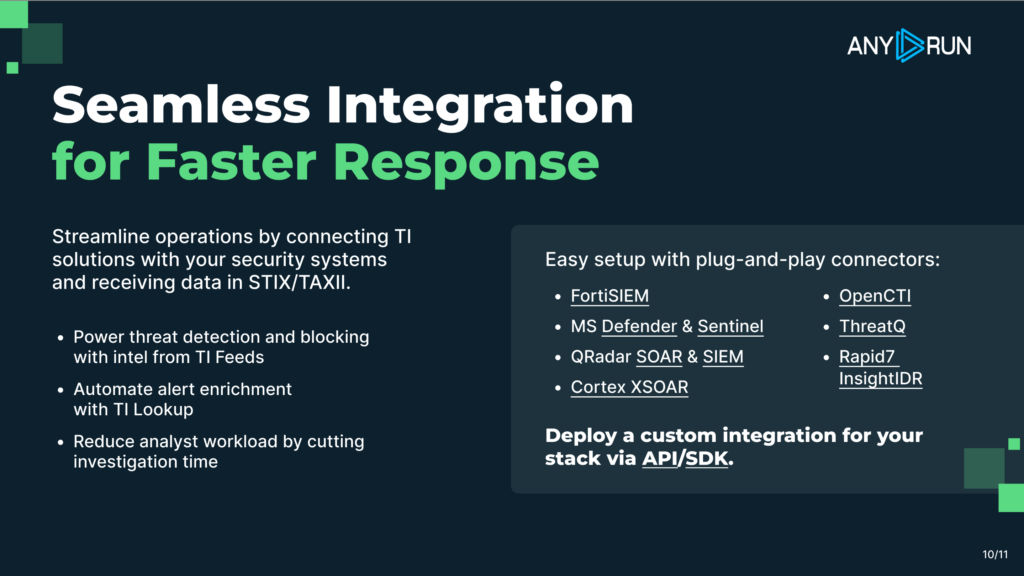
ANY.RUN’s TI Lookup and TI Feeds come with a wide range of integrations and connectors from renowned vendors, as well as the possibility for custom integrations through STIX/TAXII & API/SDK.
Outcome:
Making threat intelligence a part of your workflow brings integrity and sustainability to the entire infrastructure. You can transform common SOC challenges into opportunities for faster detection, smarter response, and overall cybersecurity resilience.
Built for modern SOC workflows, ANY.RUN enables teams to detect threats faster and respond with confidence. Our Interactive Sandbox delivers real-time malware analysis and contextual threat intelligence for rapid, informed decisions.
Compatible with Windows, Linux, and Android, the cloud sandbox provides in-depth behavioral analysis without local configuration. Integrated TI Lookup and TI Feeds supply enriched IOCs and automation-ready intelligence, no infrastructure maintenance required.
Experience it with a 14-day trial →
The post 5 SOC Challenges and How Threat Intelligence Solves Them appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
The USS Gerald R. Ford is a $13 billion aircraft carrier sailing to the Caribbean with nuclear propulsion, an electromagnetic plane launcher, and 90 aircraft onboard.
Security Latest – Read More
A European embassy located in the Indian capital of New Delhi, as well as multiple organizations in Sri Lanka, Pakistan, and Bangladesh, have emerged as the target of a new campaign orchestrated by a threat actor known as SideWinder in September 2025.
The activity “reveals a notable evolution in SideWinder’s TTPs, particularly the adoption of a novel PDF and ClickOnce-based infection chain, in
The Hacker News – Read More