The brightest flashlights of 2025: We shine a spotlight on our top picks
We tested the brightest flashlights of 2025 for camping, hiking, and blackouts.
Latest news – Read More
We tested the brightest flashlights of 2025 for camping, hiking, and blackouts.
Latest news – Read More
The gen-AI adoption management platform will invest the funds in accelerating growth and product innovations.
The post Portal26 Raises $9 Million for Gen-AI Adoption Platform appeared first on SecurityWeek.
SecurityWeek – Read More
Iran is spying on American foreign policy influencers. But exactly which of its government’s APTs is responsible remains a mystery.
darkreading – Read More
Black Friday is weeks away, but AirPods sales are starting now. Here are the best ones to shop early.
Latest news – Read More
The United States on Tuesday imposed sanctions on a group of bankers, financial institutions and others accused of laundering money from cyber crime schemes — money the Treasury Department says helps pay for North Korea’s nuclear weapons program. Over the past three years, North Korean malware and social engineering schemes have diverted more than $3 […]
The post US Sanctions North Korean Bankers Accused of Laundering Stolen Cryptocurrency appeared first on SecurityWeek.
SecurityWeek – Read More
A critical vulnerability in Control Web Panel (CWP), tracked as CVE-2025-48703, allows remote, unauthenticated command execution.
The post CISA Warns of CWP Vulnerability Exploited in the Wild appeared first on SecurityWeek.
SecurityWeek – Read More
AI is able to automate less than 3% of the work now performed by independent contractors, a new study finds.
Latest news – Read More
ANY.RUN’s malware analysis and threat intelligence products are used by 15K SOCs and 500K analysts. Thanks to flexible API/SDK and read-made connectors, they seamlessly integrate with security teams’ existing software to expand threat coverage, reduce MTTR, and streamline performance.
Here’s how ANY.RUN’s solutions can transform your security.
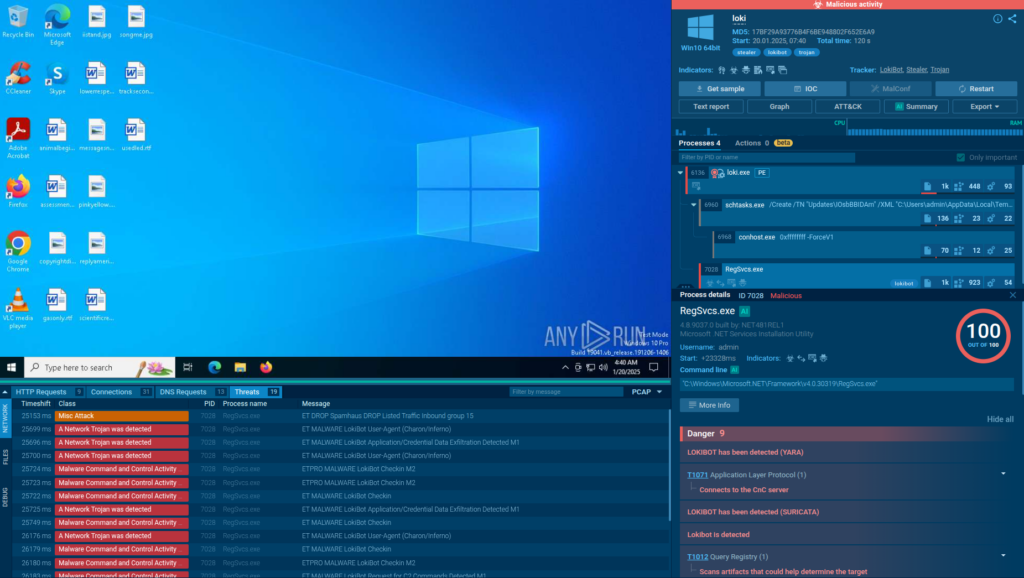
ANY.RUN’s Interactive Sandbox provides a real-time, cloud-based environment for detonating and analyzing suspicious files, URLs, and scripts across Windows, Linux, and Android systems. It lets analysts perform user actions like launching executables or opening links needed to trigger kill chains and force hidden payloads to reveal themselves, enabling faster detection and response.
The sandbox integrates with other solutions like SOAR platforms in an automated mode, which means it can fully detonate complex phishing and malware attacks on its own, including by solving CAPTCHAs and scanning QR codes.
The sandbox delivers immediate, actionable insights into the most evasive threats without risking production systems.
If your solution is not on the list, you can easily set up a custom integration using ANY.RUN’s API or Python-based SDK (see docs on GitHub or PyPi).

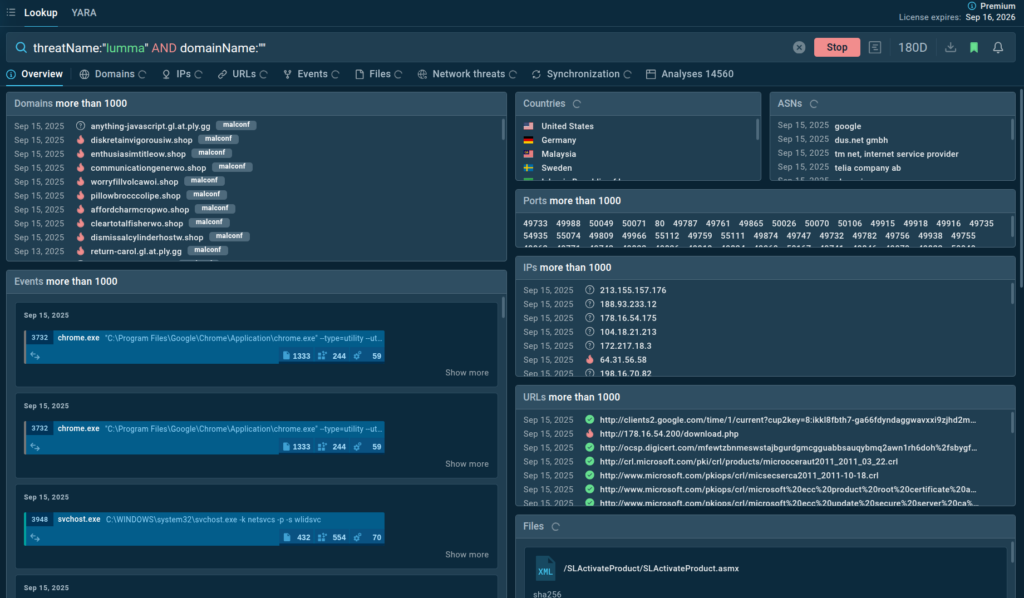
Threat Intelligence Feeds deliver real-time, high-confidence malicious indicators (IPs, domains, URLs) supplied in STIX/TAXII. The indicators are sourced from analyses of the latest malware and phishing attacks performed by 15,000 organizations and 500,000 analysts in ANY.RUN’s Interactive Sandbox.
Thanks to being powered by one of the largest malware analysis communities, these feeds provide 99% unique IOCs, not found in other sources, that are updated in real time.
As a result, they give SOCs up-to-date visibility into threats almost as soon as they emerge. With TI Feeds, security teams can:
If your solution is not on the list, you can easily set up a custom integration using ANY.RUN’s API or Python-based SDK (see docs on GitHub or PyPi).
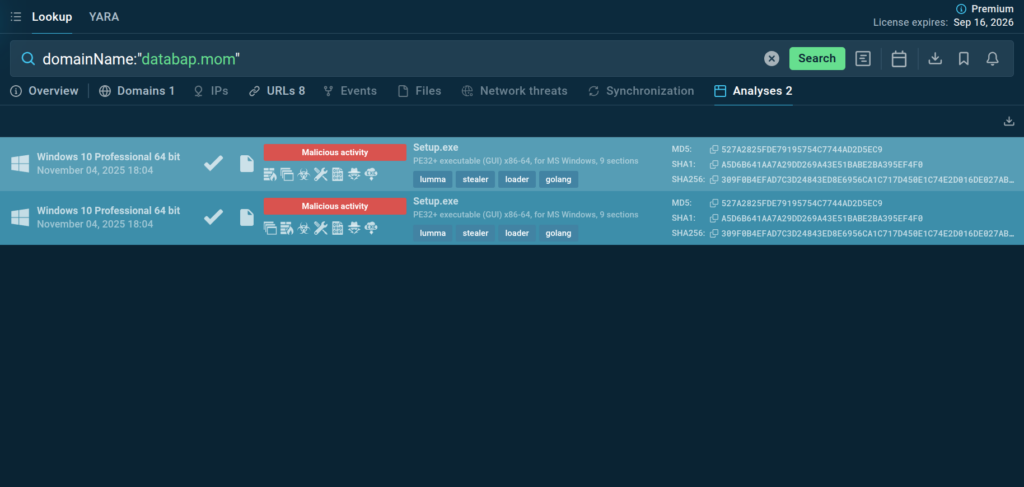
Threat Intelligence Lookup is a powerful solution designed to streamline and accelerate malware investigations, from proactive monitoring to incident response.
SOC teams can use it to quickly get actionable context for over 40 different types of Indicators of Compromise (IOCs), Attack (IOAs), and Behavior (IOBs), from an IP address and a domain to a mutex and a process name.
Each indicator in TI Lookup’s database is linked to a sandbox session, where it was observed, providing analysts with a complete view of the attack, including its TTPs.
If your solution is not on the list, you can easily set up a custom integration using ANY.RUN’s API or Python-based SDK (see docs on GitHub or PyPi).
Whether you want to uncover hidden threats in seconds, catch emerging attacks, or enrich alerts with actionable context, ANY.RUN equips your SOC with the visibility, speed, and efficiency needed to stay ahead.
With flexible API/SDK and ready-made connectors for leading platforms, implementation is smooth, and the impact is immediate: faster MTTR, higher detection rates, and a stronger defense posture.
Feel free to reach out to us about integrating ANY.RUN’s products in your SOC at support@any.run.
Trusted by over 500,000 cybersecurity professionals and 15,000+ organizations in finance, healthcare, manufacturing, and other critical industries, ANY.RUN helps security teams investigate threats faster and with greater accuracy.
Our Interactive Sandbox accelerates incident response by allowing you to analyze suspicious files in real time, watch behavior as it unfolds, and make confident, well-informed decisions.
Our Threat Intelligence Lookup and Threat Intelligence Feeds strengthen detection by providing the context your team needs to anticipate and stop today’s most advanced attacks.
Ready to see the difference?
Start your 14-day trial of ANY.RUN today →
The post Unified Security for Fast Response: All ANY.RUN Integrations for SIEM, SOAR, EDR, and More appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added two security flaws impacting Gladinet and Control Web Panel (CWP) to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild.
The vulnerabilities in question are listed below –
CVE-2025-11371 (CVSS score: 7.5) – A vulnerability in files or directories accessible to
The Hacker News – Read More
Whether you’re new to password managers or ready to switch to a different solution, these five recommendations include something for every user.
Latest news – Read More