ANY.RUN Wins Trailblazing Threat Intelligence at the 2025 Top InfoSec Innovators Awards
Big news from the ANY.RUN team; we’ve just been named the 2025 “Trailblazing Threat Intelligence” winner at the Top InfoSec Innovators Awards!
This recognition means a lot to us because it celebrates what we care about most: helping analysts, SOC teams, and researchers access live, actionable threat intelligence that makes a real difference in investigations every day.
A Milestone That Reflects Our Mission
The Top InfoSec Innovator Awards celebrate cybersecurity companies that shape the future of the industry with new ideas and bold technology. Now in its 13th year, the program is known worldwide for spotlighting organizations that truly move the field forward.
Winning the Trailblazing Threat Intelligence award reinforces what drives us, transforming how teams investigate and respond to cyber threats through a connected, behavioral approach to intelligence.
For our users, this award reflects the impact they experience every day:
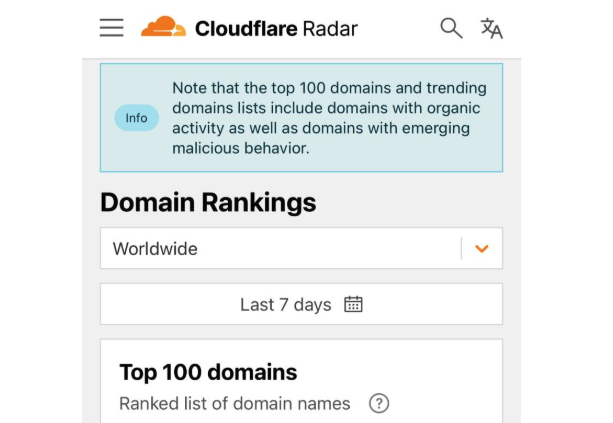
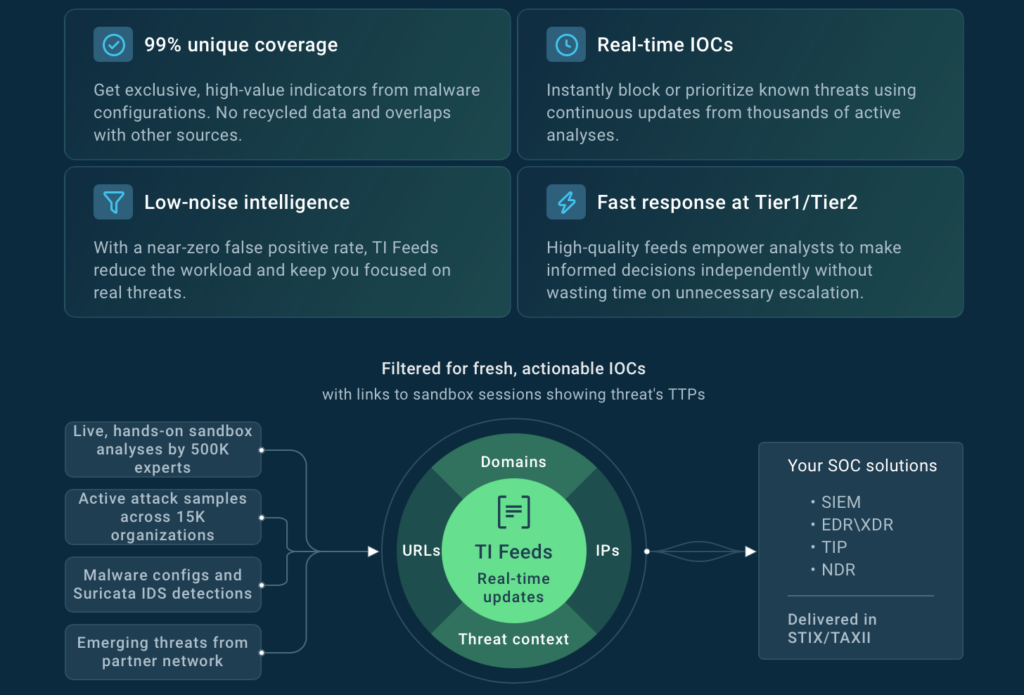
- Connected intelligence, powered by 15,000+ company data sources worldwide: ANY.RUN’s ecosystem gathers insights from thousands of live environments, helping teams detect threats that traditional feeds often miss.
- 24× more IOCs per incident for wider visibility: Live data from global attacks ensures comprehensive coverage of new malware and phishing campaigns, giving analysts the full picture behind each alert.
- 99% unique IOCs to cut noise and workload: In-depth behavioral intelligence filters out duplicates and low-value data, reducing Tier 1/Tier 2 investigation time and supporting faster, more confident decisions.
- 21 minutes faster MTTR per case: Real-time context for IOCs, IOAs, and IOBs provides the insight analysts need to prioritize critical alerts and accelerate incident resolution.
Connecting People and Data Through Innovative Threat Intelligence
We earned this recognition because innovation at ANY.RUN is built around real analyst needs. Instead of scattering data across multiple tools, we created an ecosystem where threat intelligence is connected, interactive, and human-centered.
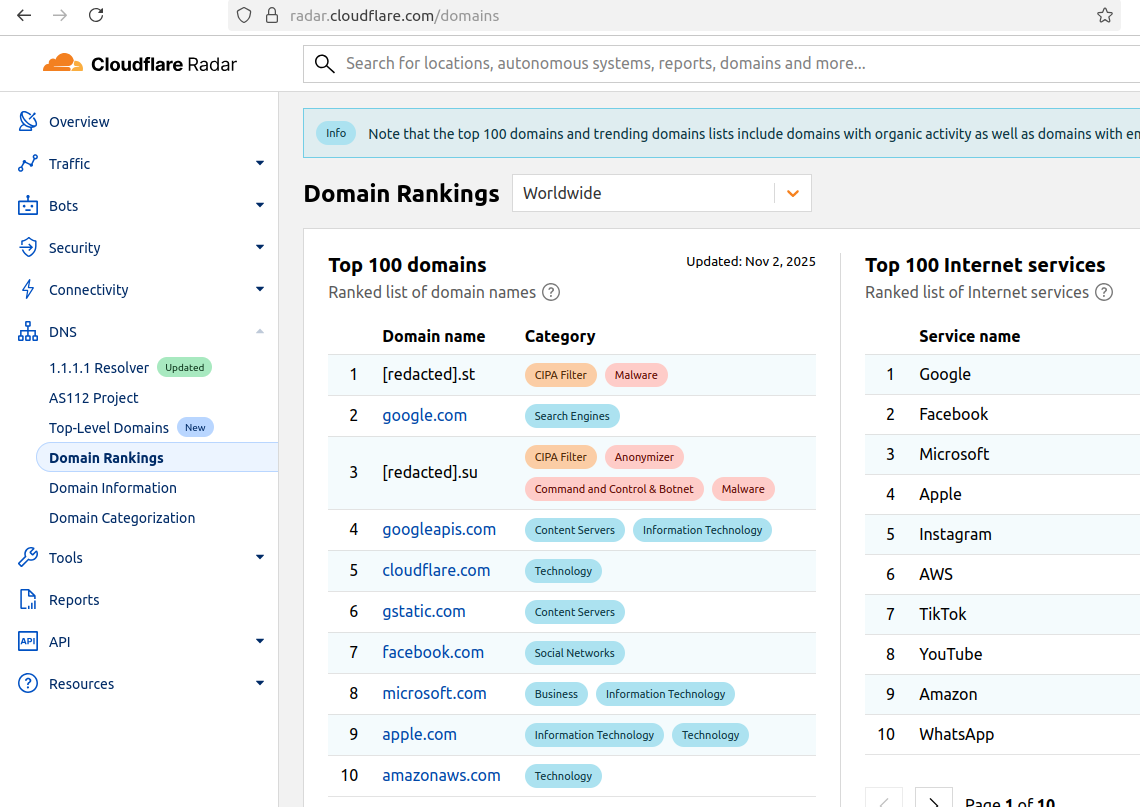
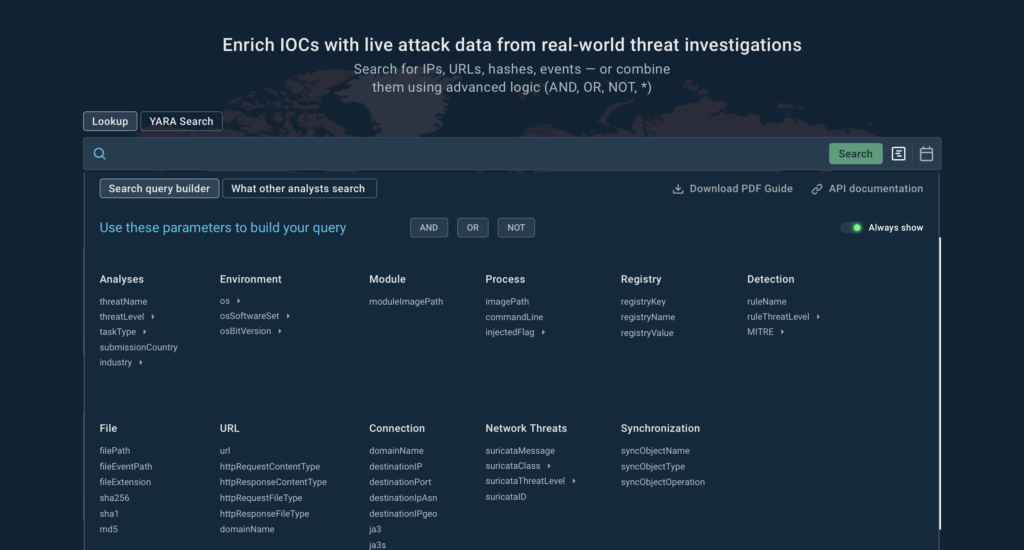
Our Threat Intelligence Lookup and Threat Intelligence Feeds bridge live malware behavior with verified indicators, giving teams instant context they can trust. Whether it’s uncovering hidden links between campaigns or enriching detections automatically, these solutions help analysts see more, decide faster, and collaborate better.
That’s what this award stands for: innovation that connects people and data to make threat intelligence more practical, powerful, and ready for what’s next.
Looking Ahead: Building the Future of Threat Intelligence
This recognition fuels our drive to keep innovating.
In the coming months, we’re expanding our Threat Intelligence products with even deeper enrichment, new integrations for SIEM and SOAR platforms, and broader OS coverage.
But most importantly, we’ll keep growing together with our community; the analysts, researchers, and security teams who make ANY.RUN what it is today. Every sample executed, every IOC shared, every insight contributed helps make global defense stronger.
So, this win is yours as much as it is ours. 
See Why the Industry Calls It Trailblazing
Experience threat intelligence that helps analysts act 21 minutes faster per case and uncover 24× more IOCs per incident.
With behavior-driven data and real-world context, ANY.RUN turns every investigation into clear, actionable insight.
Book a live demo and see how connected intelligence can sharpen your team’s response.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, makes advanced investigation fast, visual, and accessible.
The service processes millions of analysis sessions and is trusted by 15,000+ organizations and over 500,000 cybersecurity professionals worldwide.
Teams using ANY.RUN report tangible gains; up to 3× higher SOC efficiency, 90% faster detection of unknown threats, and a 60% reduction in false positives thanks to real-time interactivity and behavior-based analysis.
Explore ANY.RUN’s capabilities with a 14-day trial
The post ANY.RUN Wins Trailblazing Threat Intelligence at the 2025 Top InfoSec Innovators Awards appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More