How to Hunt and Investigate Linux Malware
Linux cyber threats may be less common than Windows ones, but they can be equally if not more damaging. Defending against these requires proactive efforts.
Eric Parker, a popular YouTube blogger and malware analyst, recently showed his approach to investigating and collecting intelligence on Linux malware.
Here is a recap of his video.
How to find Linux malware in Threat Intelligence Lookup
TI Lookup offers a centralized database of fresh IOCs, IOAs, and IOBs. It lets you search across threat data extracted from the latest malware and phishing samples analyzed by over 500,000 professionals and 15,000 companies around the globe in ANY.RUN’s Interactive Sandbox.
To start searching for Linux threats in TI Lookup, we can begin with the search query specifying the Ubuntu OS version used in the Interactive Sandbox.
Here is the query:
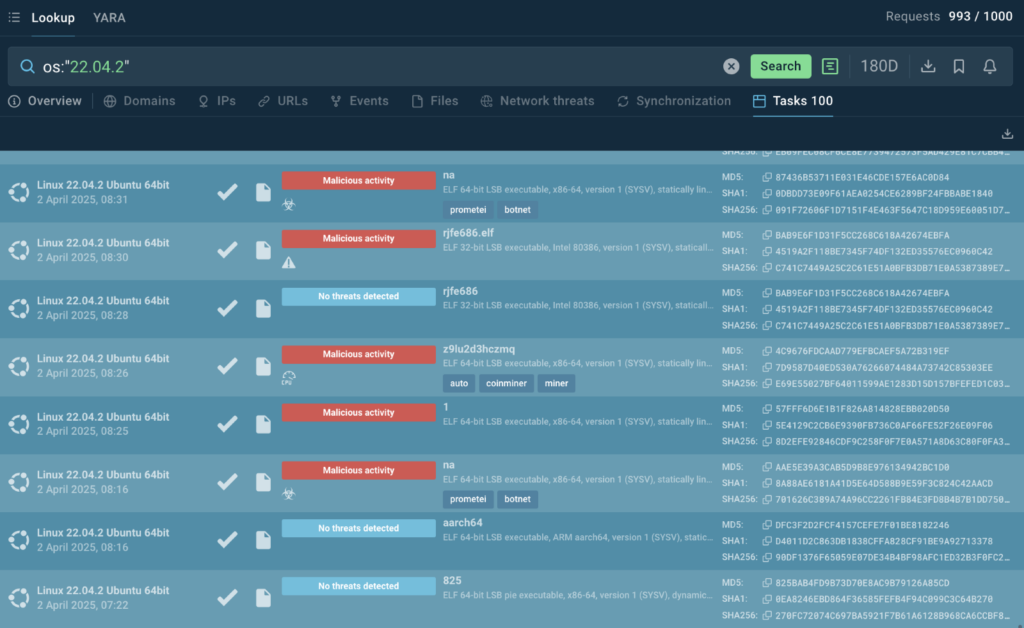
Among the results, we can see shell scripts, malware, and can get an idea of what indicators of compromise there are.
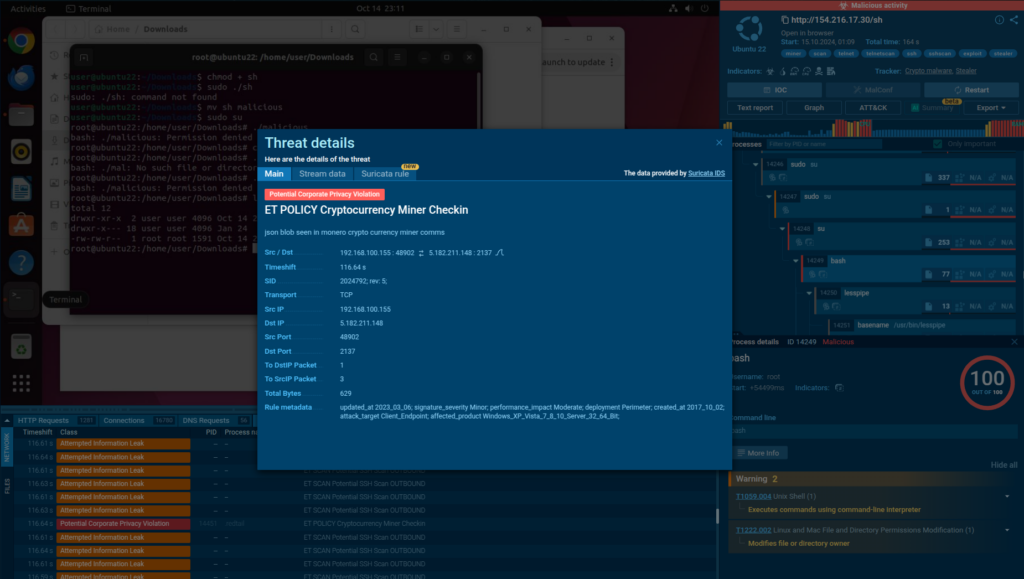
Example 1: XORbot
One of the files we found here is tagged XORbot. It’s a botnet primarily targeting Linux systems.

Let’s explore one of the samples.
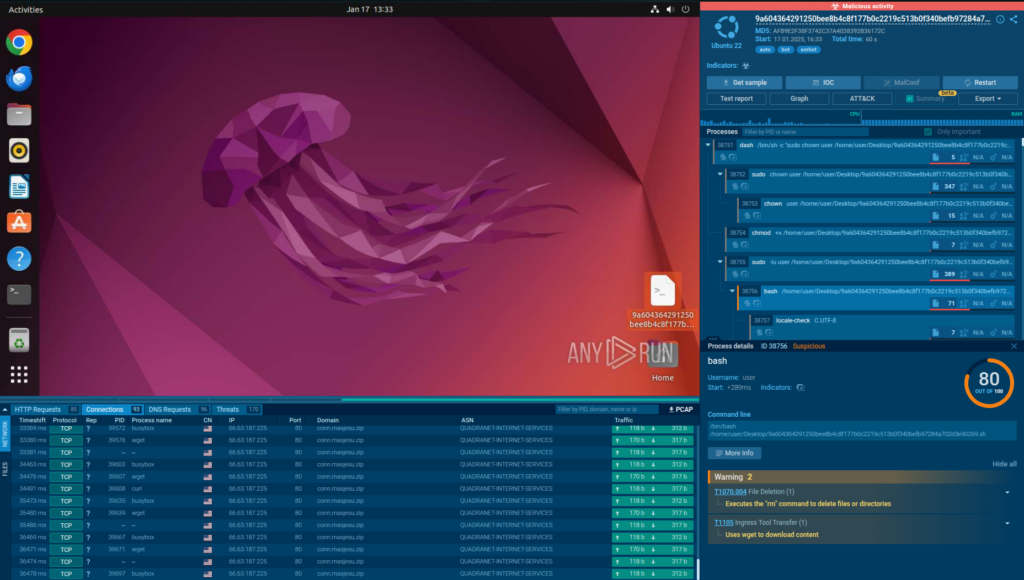
The sandbox instantly shows numerous connection requests made by the botnet.

The malware also modifies ownership on the system and downloads additional payloads.
Let’s move on to the next type of malicious software that you can find with TI Lookup, stealers.
Example 2: Linux Stealer
To find Linux stealers, we can simply combine the OS parameter with the threatName one. Here is the query we can submit to TI Lookup:
os:”22.04.2″ and threatName:”stealer”
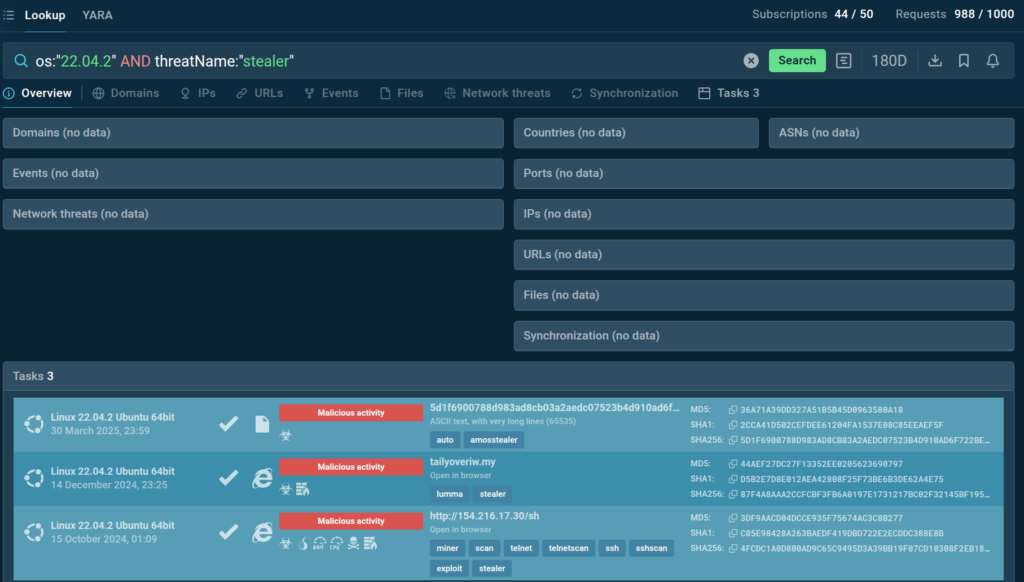
Although the list of stealer samples can hardly match that of Linux botnets, we can still find an interesting one to explore.
View analysis of Linux stealer
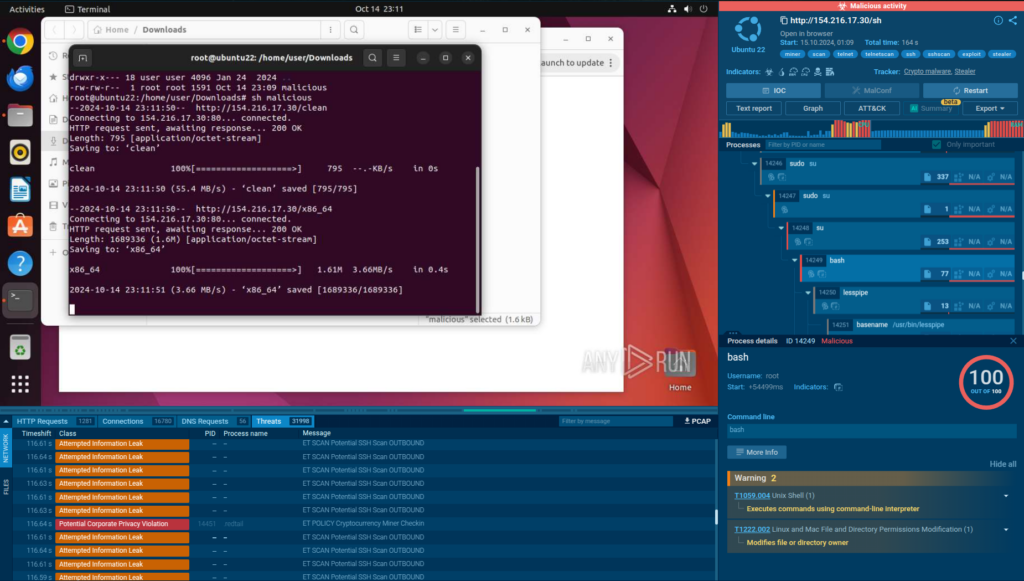
This one has an impressive list of malicious functionalities:
- It immediately begins to mine crypto using the system’s resources
- Joins a botnet and later can be used for conducting DDoS attacks
- Steals files and credentials from the potential victim
- Scans other Linux devices for vulnerabilities using Shodan
What Makes Linux Malware Different
The big thing you are probably starting to notice is that Linux malware is very different from Windows malware. It is not usually targeting a desktop user.
It’s not likely to have a campaign like email attachments or fake Fortnite swappers.
Those do very rarely exist, but because very few people use Linux as their primary desktop operating system, it’s much easier to target servers.
This puts at risk corporate infrastructure and makes it particularly important for companies to use proper tools for proactive security like ANY.RUN’s Threat Intelligence Lookup and Interactive Sandbox.
Reach out to us to learn how they can help your company.
Example 3: Mirai Botnet
Let’s take one more look at a common Linux botnet.
To find samples of Linux botnets, we submit the following search query to TI Lookup:
os:”22.04.2″ and threatName:”botnet”
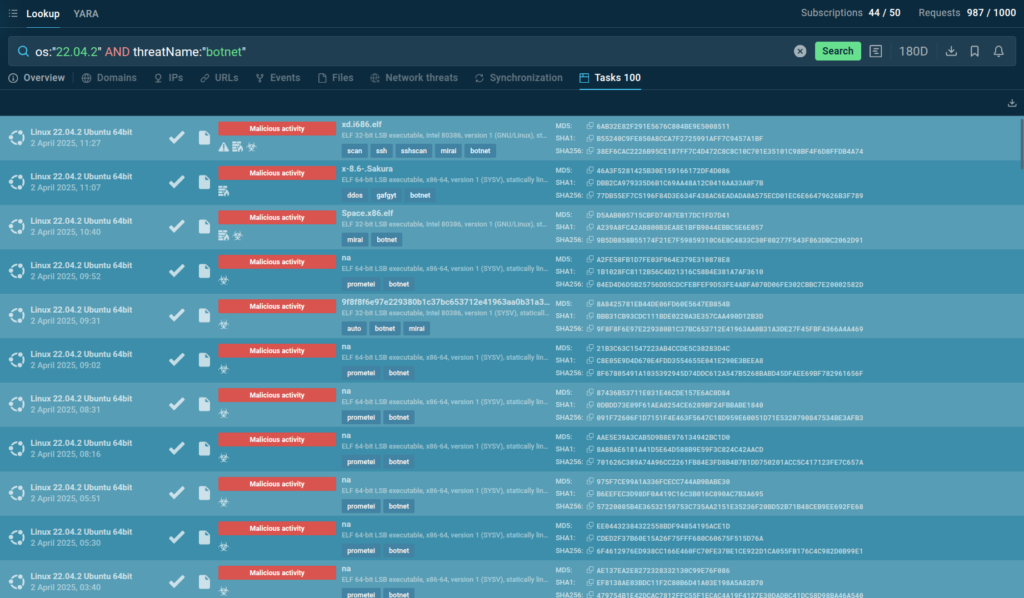
Let’s pick this sandbox session, which includes analysis of the Moobot version of Mirai.
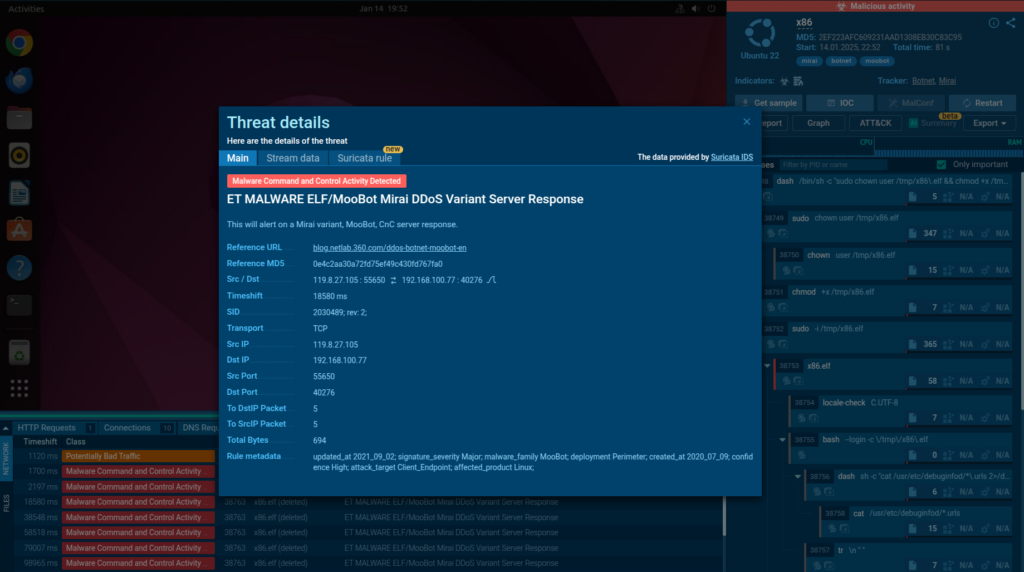
The infection starts with the download of x86.elf file, which is the process that seems to start, then it goes through and then it ultimately gets deleted, which is another stealthing technique.
If we watch a sandbox session replay – nothing visibly happens which is very common with this kind of malware: on the system that it is targeting, there wouldn’t even be a graphical user interface.
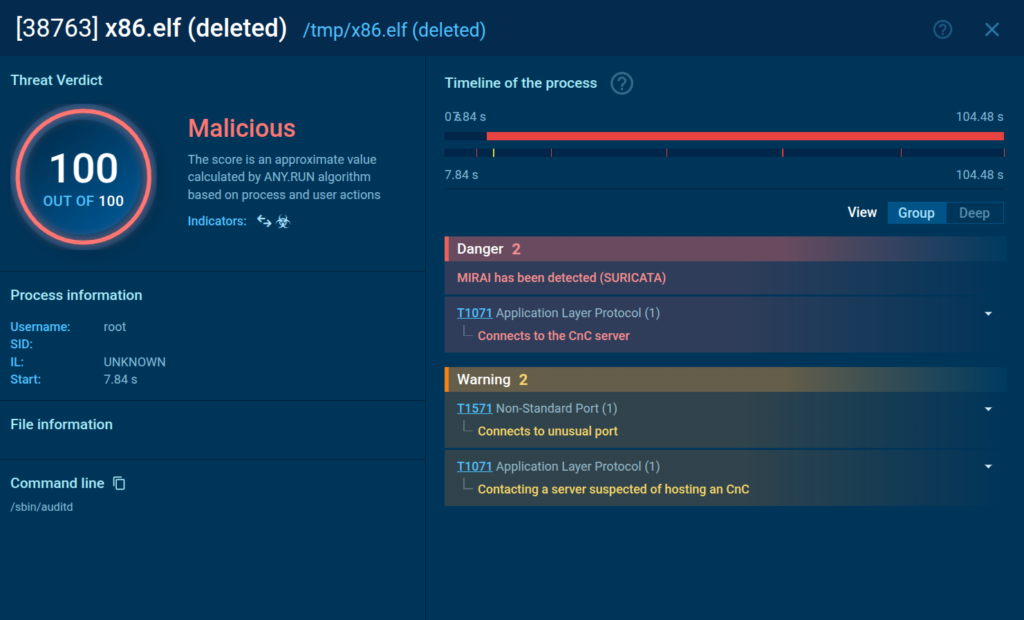
The only way you might be able to detect it is if you went through the processes, which can be done thanks to ANY.RUN’s real-time logging of all processes and system activities.

Secure Your Company Against Linux Threats
So how do you prevent Linux malware? The main thing is – watch out and make sure you don’t have a weak root password on your system.
To investigate and collect proactive intelligence on Linux threats that may target your infrastructure, use Threat Intelligence Lookup.
With TI Lookup, your company can streamline:
- Proactive Threat Identification: Search the database to proactively identify and update your defense based on the discovered intelligence.
- Faster Research: Accelerate threat research by quickly connecting isolated IOCs to specific threats or known malware campaigns.
- Real-Time Monitoring: Monitor evolving threats by receiving updates on new results related to your indicators of interest.
- Incident Forensics: Enhance forensic analysis of security incidents by searching for contextual information on existing artifacts.
- IOC, IOB, and IOA Collection: Discover additional indicators by searching the database for relevant threat information.
About ANY.RUN
ANY.RUN helps more than 500,000 cybersecurity professionals and 15,000 organizations worldwide. The Interactive Sandbox simplifies malware analysis of threats that target both Windows and Linux systems. The threat intelligence products, TI Lookup, YARA Search, and Feeds, help you find IOCs or files to learn more about the threats and respond to incidents faster.
Integrate ANY.RUN’s Threat Intelligence suite in your organization →
The post How to Hunt and Investigate Linux Malware appeared first on ANY.RUN’s Cybersecurity Blog.
ANY.RUN’s Cybersecurity Blog – Read More


